Start Menu Search Video
In this video I demonstrate that text typed into the Windows 10 start menu gets sent to Microsoft and how
that traffic can be intercepted, decrypted and parsed.
What Was Sent?
The XML files shown in the video were sent by Cortana’s “SmartSearch” app to
As shown in the video, the POST’ed keystrokes can be found inside requestInfo XML tags that have a “RawQuery” key.
The following tcpdump and grep commands can be used to list the RawQuery data sent to Bing in these HTTP/2 requests:
Running that command on the PolarProxy PCAP file from the video gives the following output:
key=”RawQuery” value=”no”
key=”RawQuery” value=”not”
key=”RawQuery” value=”note”
key=”RawQuery” value=”notep”
key=”RawQuery” value=”notepa”
key=”RawQuery” value=”notepad”
key=”RawQuery” value=”s”
key=”RawQuery” value=”se”
key=”RawQuery” value=”sea”
key=”RawQuery” value=”sear”
key=”RawQuery” value=”searc”
key=”RawQuery” value=”search”
key=”RawQuery” value=”search ..”
key=”RawQuery” value=”search ..e”
key=”RawQuery” value=”search ..er”
key=”RawQuery” value=”search ..e”
key=”RawQuery” value=”search ..”
key=”RawQuery” value=”search”
key=”RawQuery” value=”search p”
key=”RawQuery” value=”search per”
key=”RawQuery” value=”search perm”
key=”RawQuery” value=”search permi”
key=”RawQuery” value=”p”
key=”RawQuery” value=”pr”
key=”RawQuery” value=”pri”
key=”RawQuery” value=”priv”
key=”RawQuery” value=”priva”
key=”RawQuery” value=”privac”
key=”RawQuery” value=”privacy”
The same data also gets sent in the query string variable “qry” of GET requests for
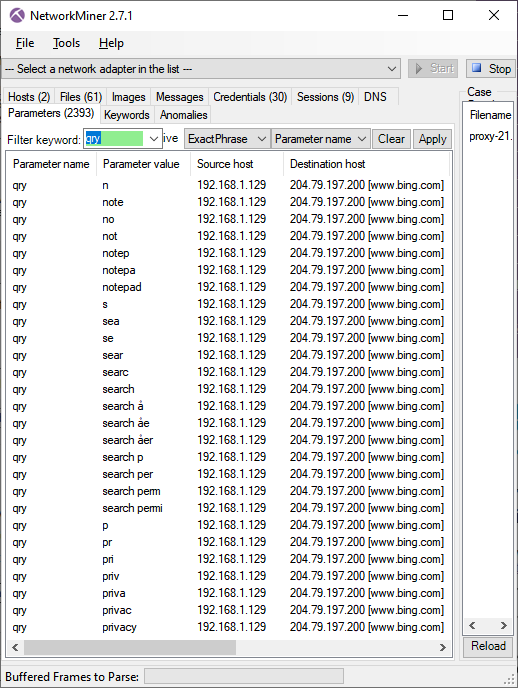
Image: NetworkMiner’s Parameters tab with filter “qry” on “Parameter name” column
How to Intercept, Decrypt and Decode HTTPS Traffic
The following section presents the technical details regarding my setup,
so that others can reproduce and verify these findings.
My first step was to install PolarProxy on a Linux machine on the local network.
PolarProxy is a TLS proxy, which can intercept and decrypt TLS traffic.
This TLS proxy is primarily designed to decrypt traffic from malware and hackers,
but can also be used to decrypt legitimate traffic when needed.
PolarProxy was configured to listen for incoming TLS connections on TCP port 443
and output PCAP data with the decrypted traffic as if it had been transmitted over TCP 80.
The decrypted traffic was accessible as a real-time stream through a
PCAP-over-IP service running on port 57012.
Here’s the full command that was used to start PolarProxy:
In the video I showed the Windows 10 client’s modified hosts file, which included an entry for www.bing.com pointing to the PolarProxy machine.
What was not shown in the video though, is that PolarProxy’s own CA certificate had been added to the Win10 machine’s list of trusted root CA’s,
as explained in the “Trusting the PolarProxy root CA” section of the PolarProxy installation instructions.
With these two changes in place all HTTPS requests for www.bing.com from the Win10 PC got diverted through the PolarProxy TLS inspection service,
which then decrypted and re-encrypted the traffic before forwarding it to Bing.
The decrypted Bing requests could be accessed either locally on the Linux machine,
or remotely using the PCAP-over-IP service on TCP port 57012.
I used NetworkMiner to read the live PCAP stream with decrypted traffic from port 57012 and extract all files being sent and received in real-time.
Is it Possible to Disable the Cortana Search?
When Ars Technica reporters asked Microsoft back in 2015
if there was any way to disable this communication, Microsoft replied with the following statement:
As part of delivering Windows 10 as a service, updates may be delivered to provide ongoing new features to Bing search, such as new visual layouts, styles and search code.
No query or search usage data is sent to Microsoft, in accordance with the customer’s chosen privacy settings.
There are plenty of how-to guides online with instructions on how the Cortana search feature can be disabled.
Most of these guides suggest disabling the AllowCortana setting in group policies or in the registry.
We’ve tried several of the settings suggested in these how-to guides, but none of them seem to prevent Windows from sending keystrokes to Bing.
If you know how to successfully disable Cortana’s Bing searches,
then please feel free to reach out to us so that we can update this blog post.
UPDATE 210928 – How to Actually Disable Cortana Search
Twitter user @GeorgeProfonde3 reached out
to suggest a fix that might prevent the start menu from sending data to Bing.
We have now verified this fix and we’re happy to announce that it works (at least for us).
- Start regedit
-
Open the following registry key:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search - Ensure that the value for CortanaConsent is set to 0
- Create a new DWORD registry value called “BingSearchEnabled” with value 0
You should no longer see any connections to www.bing.com when interacting with the start menu after implementing this fix.
We’re still not sure how to disable the cortana search traffic using Group Policies though.
 Share on Facebook
Share on Facebook  Tweet
Tweet  Submit to reddit.com
Submit to reddit.com
*** This is a Security Bloggers Network syndicated blog from NETRESEC Network Security Blog authored by Erik Hjelmvik. Read the original post at: https://www.netresec.com/?page=Blog&month=2021-09&post=Start-Menu-Search-Video

