Browser Push Notifications: Useful Feature Exploited by Deceptive Marketers
Pop-ups and browser lockers have given way to irritating and potentially destructive push notifications
For many of us, when we hear the word “malware,” the first thing that comes to mind would be visions of emptied bank accounts, encrypted files or webcams turned on to track your every move. The psycho-analytical wordplay game reveals malware at its worst; however, malware’s ability to exploit useful features presents a less-threatening but far more irritating side of the filthy coin.
One of these irritating features increasingly exploitated by cybercriminals and deceptive marketers is browser push notifications, sometimes referred website push notifications. Previously, deceptive marketers used pop-ups to redirect users to websites they invariably did not want to go to—at worst, they were used as a vehicle for drive-by downloads. Now, browser notifications are being abused.
To the average user, the difference between a pop-up and a browser notification may seem irrelevant. They both do a very similar thing—inform the user—and both can be irritating. There is a difference between the two, and that difference has become important in how anti-virus packages and pop-up blockers filter and stop the former. The Mozilla Developer documents, an authority on web development, defines a pop-up as:
“A popup is a dialog that’s associated with a toolbar button or address bar button…When the user clicks the button, the popup is shown. When the user clicks anywhere outside the popup, the popup is closed.”
While its defines a browser notification as:
“The Notifications API lets a web page or app send notifications that are displayed outside the page at the system level; this lets web apps send information to a user even if the application is idle or in the background…Typically, system notifications refer to the operating system’s standard notification mechanism: think for example of how a typical desktop system or mobile device broadcasts notifications.”
The average user would still probably see them as the same. The difference can be summarized as follows: Browser notifications display the message out of the browser window, often appearing as a system message such as those used to inform users of updates, for example. Pop-up blockers can block the website from posting pop-up through the browser window. Many browsers now have such a feature due to the constant abuse of pop-ups by cybercriminals and less savory marketers. They can’t perform the same service for browser notifications. All is not lost, though; browser notifications can be blocked. More on this later.
Abusing a Potentially Useful Feature
It is important to remember that browser notifications need the user to consent to their use. This comes in the form of that little box that appears on the left of the screen when visiting a site. The little box asks if the website in question can send notifications. If agreed to, that website can send notifications outside of the browser via the operating systems messaging broadcast system.
Here is where the unscrupulous marketer takes advantage of the feature. Rather than asking for the user’s permission to send notifications, the message box asking for permission will ask for the user’s permission to play a video, for example. If clicked, the user is redirected to another website to watch the video, they believe. This could be used to redirect the user multiple times to multiple websites until they stop or finally lose any semblance of sanity. All the while, for every website the user clicks on the “allow” button, the user has granted the marketer the permission to send notifications, thus opening the door (or window) for abuse.
Here’s an example showing a deceptive pop-up ad that asks to allow notifications:
The marketer could abuse this for website clicks to generate ad revenue, as a simple example. While not being the earth-shattering realization that your bank account has been cleaned out by a hacker deploying a banking trojan, such notifications are incredibly irritating, just like when abuse of the pop-up feature was popular. However, abusing browser notifications can be for more sinister reasons.
Here is another example of a pop-up trying to trick internet users into allowing website push notifications:
A real-world example of such abuse can be seen when websites are used to feed users unreliable ordamaging content via a website with a browser notification. If the user allows notifications, they are redirected to other potentially damaging websites. Often the simple act of allowing notifications will give the attacker the opportunity the chance to install unwanted applications such as adware or allow the attacker access to personal information and sensitive data.
The Emergence of Push Locker
Push locker is built upon the premise made infamous by browser lockers, wherein the browser is bombarded with a series of alerts informing the user that the browser is locked. The constant barrage of alerts, pop-ups or notifications makes browsing other web pages impossible. This adds to the myth that the browser is indeed blocked, when the truth is far different. In these attacks, the victim is often redirected to a screen that states the browser has been locked and the victim needs to call for tech support. That is where the tech support scam begins.
Push lockers work in an incredibly similar way: A user will visit a site, where the notification to allow push notifications will pop up asking for permission. Through some manipulation of the browser notification API, when the user clicks “not now” or “never,” the user is then redirected to another website, often a sub-domain of the original the user landed on, and the process continues. This locks the users into a cycle of redirects and notifications.
These are incredibly irritating and can easily be weaponized to do far more sinister operations. In one example discovered by researchers, the attack kept the victim locked into a cycle of an ongoing consent page cycle—the typical modus operandi of the push locker but for one difference: While the victim is locked on the consent page, another piece of malware is working behind the scenes. That malware is a cryptominer, utilizing the victim’s CPU to mine cryptocurrency. Those who eventually consented were redirected to another webpage with an offer that was difficult to refuse. Again, on the offer page the cryptominer was installed in the background. This meant that the unlucky victim could not evade the cryptominer in any safe way.
The speed at which researchers have been encountering push lockers has increased dramatically since the start of 2019. The technique could be used to hide the download of far more malicious and financially devastating pieces of malware. There is good news, however, and users are not completely defenseless.
Blocking Notifications
Browsers enable users to disable or block these notifications. Notifications look different on each browser, which means users need to do a bit of research to figure out how to block them. Further, users can block notifications altogether, or the user can add specific domains to a blocked list.
Example of deceptive push notification ad on Windows computer:
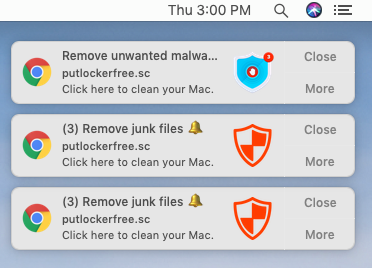
Example of deceptive push notifications ads on a Mac computer:
There are several excellent guides online explaining how to do this on different browsers. Knowing how to block notifications is one way to defend yourself from such an attack. Also important is how you conduct yourself online. Like with pop-up ads, the attack more than often relies on getting the user’s attention. Offers too good to be true, fake news articles designed to elicit a response and the like are effective social engineering tactics known to get people to click on risky links or allow notifications that, in the long term, will prove to be unwanted.
Any new technology that allows marketers to sell products more effectively and target their audience with greater certainty inevitably will be subverted. New attacks will be devised to exploit the technology. While the technology may change, one thing that remains the same is the ways in which attackers get users to click. “If it’s too good to be true, it probably isn’t,” and other clichés may sound trite and overused, but they’re necessary in helping people think twice before clicking on something they shouldn’t.
Combating cyber scams involves understanding the technology used by attackers as well as how attackers often appeal to our base desires to get us to click on a link or allow browser notifications. Whereas in the past con men would carry out scams in person, today the internet allows scams to be carried out anywhere and with anonymity. The tactics used to hook users has not changed, however, and there needs to be a better approach to teaching users the signs of a scam. Often security firms are focused on developing technology to prevent attacks and scams, but little is done to correct the failings we as humans exhibit at one time or another.