The Changing Landscape of Automated Attacks on Web and Mobile Apps
In recent years, we have witnessed an unprecedented surge in automated attacks targeting online businesses. These attacks are aimed at validating stolen payment card details, scraping content, taking over accounts and sometimes even slowing down the target website.
In the last post, I had highlighted how competitors could be behind some of these attacks. Now, to dig deeper into the presence of bad bots across industries, recently we conducted quarterlong research, the findings of the study are covered in a report aptly titled “The Big, Bad Bot Problem Q3 2018.”
The research revealed that the latest breed of bad bots leverages cutting-edge technologies including machine learning and robotic process automation (RPA) to masquerade as genuine users and attack online businesses. The report that is based on the analysis of traffic on thousands of anonymized domains during Q2 and Q3 2018 unveils that cyberattackers target businesses across industries. However, a few industries are considerably more affected by bad bots than others. Travel (20.1 percent), e-commerce (18.3 percent) and real estate (13.7 percent) have the highest percentage of bad bot traffic.
Let’s take a closer look at the presence of bad bots in these industries:
Travel
Travel portals witnessed a dramatic increase in bad bot traffic during September 2018. Nearly 50 percent of the total traffic consisted of bad bots in the last month of Q3.
E-commerce
Automated attacks are inconsistent on e-commerce firms. On average, 25.74 percent of traffic was bad bots on e-commerce firms during Q2 and Q3. One of the reasons for this inconsistency is seasonal spikes in automated activity on e-commerce websites during festive seasons when there is a greater economic incentive for each successful account takeover.
Commonly Used OS and Browsers by Bad Bots
The next answer that we were looking for during the research is, how these attacks are executed across industries and what tools does an attacker use? We found that these cyberattackers are not limited to using one tool. They use a combination of tools (such as proxy IPs, multiple UAs, programmatic/sequential requests) to disguise the identity of bots, evade detection and perform sophisticated automated attacks. Bots masquerade as genuine users by using widely used browsers and devices.
Commonly Used Operating Systems
In Q2 and Q3, Windows continued to be the most popular operating system used by bad bots. 80.2 percent of bad bots used Windows OS as their user agent to commit attacks in Q2 and Q3.
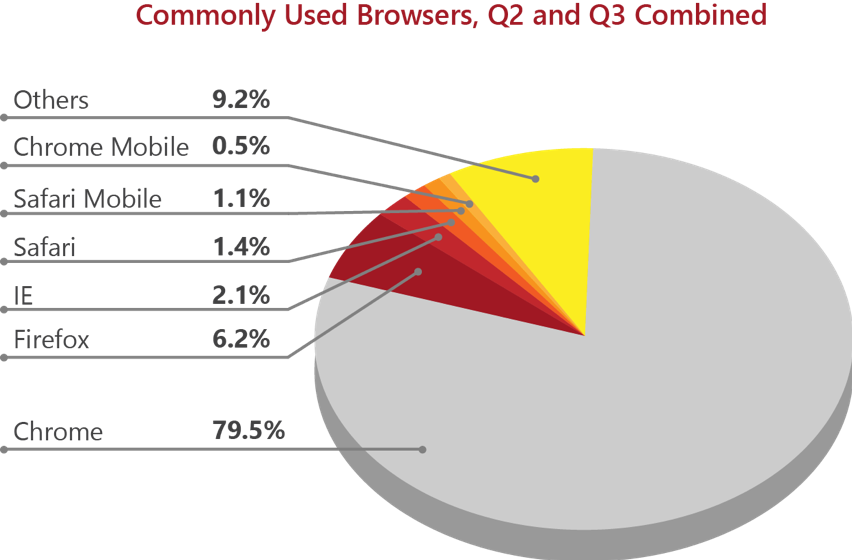
Commonly Used Browsers
Chrome, Firefox and IE are the most commonly used user agents to execute attacks. Chrome is the first choice for bot herders. 79.5 percent of bad bots used Chrome as their user agent to attack online businesses in Q2 and Q3 combined.
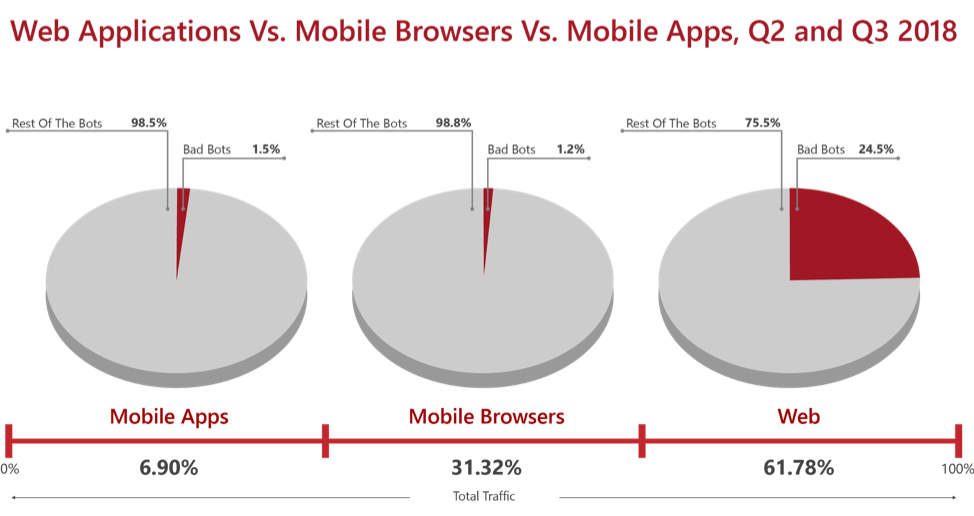
Most Exploited Attack Surfaces
Attackers use these user agents along with various other components of their “exploit kit” to intrude into an online business’s internet infrastructure. Web applications are the first target for cyberattackers; however, there is a shift in this trend. We observed that attacks on mobile apps have increased in recent months.
 Where Bad Bots Originate
Where Bad Bots Originate
Most of the bad bots detected during our study originated from Russia, followed by Germany and the Netherlands.
Prevention Measures to Combat Security Breaches by Bad Bots
The risk posed by bad bots requires dedicated measures to avert sophisticated automated attacks. There are various solutions that claim to eliminate bad bots. In recent years, however, bots have started to mimic human behavior, hence the risk of categorizing genuine users as invalid traffic is mounting. Bot management solutions need to take an optimized approach that blocks all types of bad bot traffic without impacting genuine user experience. This requires that various factors be considered, including domain-specific user behavior and implementation of measures such as challenge-authentication response to validate a visitor’s identity before categorizing the visitor as genuine or invalid traffic.