Reading Mandiant M-Trends 2023
The famous Mandiant 2023 M-Trends (NOT G-Trends, mind you…) report is out, and here are some of the things that I found to be surprising and NOT surprising 🙂
SURPRISING
- “Mandiant experts note a decrease in the percentage of global intrusions involving ransomware between 2021 and 2022. In 2022, 18% of intrusions involved ransomware compared to 23% in 2021” [A.C. — wow, ransomware is finally declining! Good news?!]
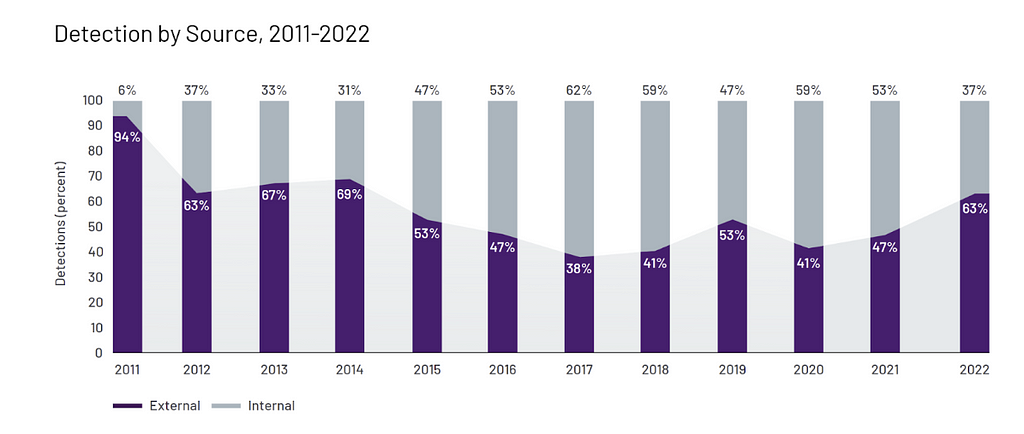
- “Organizations were notified of breaches by external entities in 63% of incidents compared to 47% in M-Trends 2022, which brings the global detection rates closer to what defenders experienced in 2014”
- “Mandiant observed threat actors leverage data available in underground cybercrime markets, clever social engineering schemes, and even bribes to carry out intrusions and account takeovers. Furthermore, these adversaries demonstrated a willingness to get personal with their targets, bullying and threatening many of them.”
NOT SURPRISING
- “Global median dwell time continued to improve year over year, with organizations detecting incidents in just over two weeks in 2022. This is the shortest global median dwell time from all M-Trends reporting periods”
- “Mandiant observed more destructive cyber attacks in Ukraine during the first four months of 2022 than in comparison to the previous eight years.”
- “Exploits remained the most leveraged initial infection vector used by adversaries, at 32 percent. Phishing returned as the second most utilized vector, representing 22 percent of intrusions as compared to 12 percent in 2021.”
- “Of all threat groups observed in 2022, Mandiant assessed that 48% of these threat groups to have financially motivated operations, 18% with espionage related motivations and 9% with other motivations like, destructive operations, hacktivism, and being a nuisance”
Related posts:
- Google Cybersecurity Action Team Threat Horizons Report #6 Is Out!
- Google Cybersecurity Action Team Threat Horizons Report #5 Is Out!
- Google Cybersecurity Action Team Threat Horizons Report #4 Is Out!
- Google Cybersecurity Action Team Threat Horizons Report #3 Is Out!
- Google Cybersecurity Action Team Threat Horizons Report #2 Is Out!
- Illicit coin mining, ransomware, APTs target cloud users in first Google
Reading Mandiant M-Trends 2023 was originally published in Anton on Security on Medium, where people are continuing the conversation by highlighting and responding to this story.
*** This is a Security Bloggers Network syndicated blog from Stories by Anton Chuvakin on Medium authored by Anton Chuvakin. Read the original post at: https://medium.com/anton-on-security/reading-mandiant-m-trends-2023-f315c62c8a8b?source=rss-11065c9e943e------2

