Device-Centricity
Oh, network-centered security. What a brilliant idea. Let’s put all our faith in the network and forget about those pesky little devices that connect to it. Who needs to worry about laptops, tablets, and smartphones, anyway? They’re just small, insignificant pieces of technology that have absolutely no bearing on our security. Device-centricity? Maybe it’s a fad.
Let’s face it, the network is the most important thing when it comes to security. Who cares if your employees are connecting from home, the office, a coffee shop, or an airport? As long as the network is secure, everything is fine. After all, hackers would never be interested in attacking individual devices, would they?
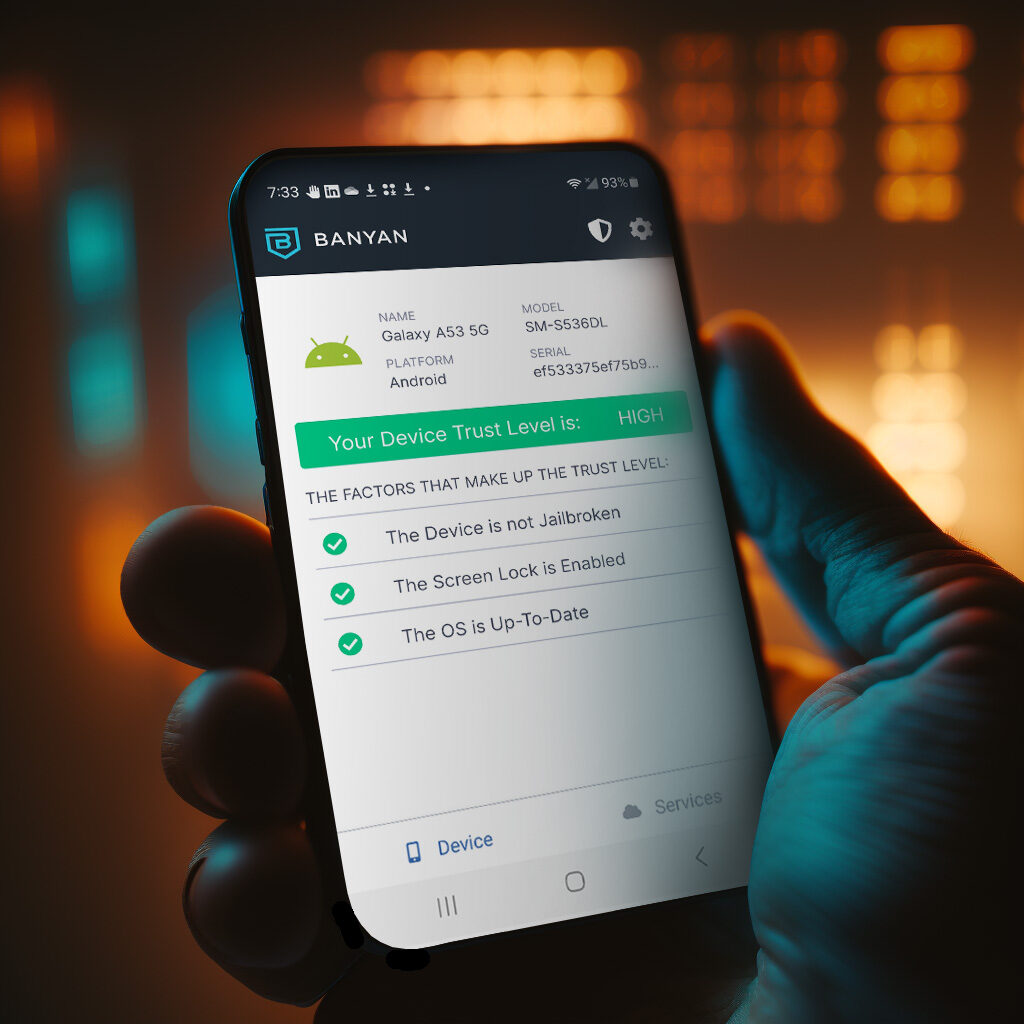
But wait, what if one of those devices is compromised? What if someone steals an employee’s laptop or gains access to their smartphone? Oh, I know, let’s just blame the network for that too. It’s clearly the network’s fault for not being secure enough to protect those devices. So what if the devices themselves have security features like posture verification and user verification? We can just ignore those and focus solely on the network.
And let’s not forget about the joys of network-centered security when it comes to mobile devices. Why bother securing those pesky little things when we can just assume that the network will take care of everything? Who cares if an employee loses their phone or accidentally connects to an unsecured Wi-Fi network? It’s not like those devices contain sensitive information or anything. Device trust – what’s that?
Clearly, device-centric security is just a waste of time. We should all be focusing on the network and ignoring those silly little devices that connect to it. I mean, who needs a holistic approach to security when we can just blame the network for everything? It’s so much simpler that way.
Oh, and let’s not forget about the joys of intelligent routing. Because clearly, the network is capable of determining which devices are secure and which ones aren’t. Why bother with individual device security when we can just rely on the network to make all the decisions for us? It’s not like the network has ever made a mistake before, right?
In conclusion, device-centric security is a complete waste of time. Let’s just focus on the network and ignore all those insignificant little devices that connect to it. After all, what could possibly go wrong?
The post Device-Centricity first appeared on Banyan Security.
*** This is a Security Bloggers Network syndicated blog from Banyan Security authored by Colin Rand. Read the original post at: https://www.banyansecurity.io/blog/device-centricity-chat-gpt/?utm_source=rss&utm_medium=rss&utm_campaign=device-centricity-chat-gpt

