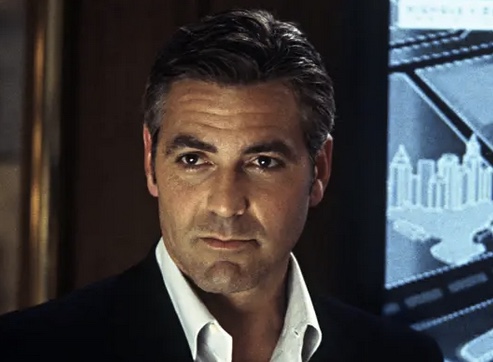
The Danny Ocean of Social Engineer’s
It’s pitch black. A car speeds through the desert with no headlights, desperately trying to outpace the armed guards in the vehicles behind. A sharp left turn takes the car barreling in a new direction, out of grasp of the guards. “STOP!” yells the passenger. The driver slams on the breaks just in time to avoid plummeting down the cliff only inches ahead. This story, along with others of being arrested, evading armed guards (on foot, this time), and slipping in back doors unnoticed were my introduction into the world of social engineering. Professional Social Engineer’s (SEs) became, in my mind; confident, bold people who were not riddled with anxiety over their tasks. Think Danny Ocean.
There’s A Color Wheel of SE’s
These stories were great, but how could this be the career path I venture down when the thought of one vishing call makes me nervous? I wasn’t sure that I had the ability to wade into a field like this. These thoughts weren’t fully stemming from Impostor Syndrome (although I have experienced plenty of that), but rather from a self-analysis of how I respond to stressful situations. I didn’t know if my personality or communication style would be the best fit for the industry.
At DEF CON 27 I came to understand that my perception of the “typical” social engineer was skewed. As I met person after person, I realized something quite simple; each of them was different. It’s a basic truth we all know, but I had forgotten to apply it within the industry itself. I came to realize that there was no one kind of person who worked in this field; it attracted all sorts. There were people who experienced anxiety over the same aspects of the job as I do, in addition to those “Danny Ocean” personalities.
What I saw reminded me of a color wheel. Everyone was varied; some bold, some soft, some a blend of the extremes. What they each shared was simple: Every “color” complimented some aspect of the industry in its own way. As I got to know certain individuals better, I was intrigued by how they were able to change their “color”, or skill set, depending on the job they were doing. As I paid attention to how they managed this color shift, I started taking note of how I could apply their techniques.

Learn Your Color
Before you can apply other’s techniques and strengths, you first need to identify your own. With the help of my mentors I came to understand that what we may view as personal weaknesses can be turned into our greatest strengths.
I asked my teammates what qualities they once saw in themselves as weaknesses, but now view as strengths. One response that stood out was “being harmless.” They said “being perceived as harmless, or not someone to be taken seriously, is a blatant weakness in social situations and even in careers. But when you can manifest that in an in-person engagement, or even on a call…It’s super handy.”
If you hold this image up against the Danny Ocean image of social engineers, it may appear quite different. However, this response stood out because this trait is something the rest of us on the team have only ever seen as a strength in this person. This demonstrated to me the need to be honest in your self-assessment. Step back and stop viewing traits as weaknesses or strengths. Instead, think about how you can channel your natural traits into the backbone of your tasks.
Expand Your Color Palette
Once you have learned and honed your personal skill set; how should you go about expanding it? Let’s use vishing to see how we can do this. Vishing is defined as “the practice of eliciting information or attempting to influence action via the telephone.” Here at Social-Engineer, LLC, we use Vishing as a Service® (VaaS)® to train our client’s employees in their security protocols. We use a variety of pretexts, or the reason we give for calling. This allows us ample opportunity to try out new techniques and step outside of our box.
I am almost always nervous when trying out a new pretext or calling a new client. Instead of fighting this feeling, I try to channel my nerves into my pretext. For example, I might say that I’m an intern and need help. Using an assistance theme like this allows me to ask questions, sound nervous, and request help without raising suspicion. It also allows me to play to the target’s ego; who doesn’t feel good while helping and teaching a new hire?
I work with an amazing team, and we often share tips and tricks we use on our vishing calls. By listening to some of their calls, I slowly started incorporating various techniques as I felt comfortable. Some people on the team naturally sound sure of themselves, knowledgeable, and calm. This makes them very good with authority pretexts. By mimicking their cadence, I was able to learn how to channel that persona in my own calls. Once you build up a repertoire of techniques, you will be able to shift from one persona to the next based on the needs of the moment.
The Human Hacking Conference 2021
Shameless plug alert! If you are interested in learning more about vishing and the techniques used, join us at The Human Hacking Conference 2021! I, alongside my self-proclaimed vishing opposite, Curt Klump, will be teaching a special Vishing WorkshopTrack where you will learn all our insider tips and tricks.
Incorporate New Techniques
Just before typing these words I was on a vishing call where I was able to use the aforementioned techniques. I made my call while planning to use my soft, help-seeking voice. When the man picked up, though, he sounded very authoritative. There was something in me saying that he wouldn’t respond to my usual approach.
Switching up my plan, I mimicked his cadence. I tried to sound authoritative, making sure I spoke clearly and not too fast. I also limited word whiskers (saying “um,” “you know,” etc.) and did not apologize when he was unable to find my ID in the employee database. When I went for the flag (the piece of information our client had deemed sensitive), he questioned me and refused to provide it, saying I should have access to that information already. I gave some excuse about the program I was using not allowing me to access the information while having an open ticket. While I was still making up this excuse (and trying to sound like I knew exactly what I was talking about), he put me on speaker and walked away to a different computer to see if what I was saying was true.
It wasn’t, of course. The whole time he was trying to verify what I said, he was speaking about the “new security training” they were going through and how he wasn’t supposed to give out information. After a minute, he figured out a workaround for me and told me the solution. Without trying his solution, I again asked for the flag. I wanted to see if he would stick to his guns or cave to the authority pretext. Without a second’s hesitation, he provided the information I had requested.
Stories to Share
So, whether you’re a Danny Ocean of social engineer’s; cool, calm, and collected… or more of a Linus, like me; shaky, faking it till you make it… the social engineering field IS for you. Take time to learn your strengths. More importantly, take a good look at what you consider to be your weaknesses. Reach out to those around you for a fresh perspective. Your “weaknesses” may end up being your greatest strengths.
Don’t be afraid to step outside of your box. If you’re comfortable with one approach, try something different! This industry is full of all different kinds of people, each with skills and stories to share. Learn from those around you and try out their favorite techniques as you learn. Slowly but surely; you will have a plethora of colors on your palette!
Wrtitten by: Shelby Dacko
Sources
https://www.social-engineer.com/about/
https://www.social-engineer.com/overcome-the-impostor-syndrome%e2%80%af/
https://www.varonis.com/blog/working-in-cybersecurity/
https://www.social-engineer.com/my-first-onsite-social-engineering-engagement-pretenders-assemble/
https://www.social-engineer.com/services/vishing-service/
https://www.humanhackingconference.com/
https://www.humanhackingconference.com/trainers/curt-klump/
Image
https://i.pinimg.com/originals/37/22/ff/3722ffb3cef0c077cfd29e7b7ee6fcf6.jpg
http://www.artgraphica.net/free-art-lessons/watercolor/watercolor-color-wheel.html
The post The Danny Ocean of Social Engineer’s appeared first on Security Through Education.
*** This is a Security Bloggers Network syndicated blog from Security Through Education authored by SEORG. Read the original post at: https://www.social-engineer.org/newsletter/the-danny-ocean-of-social-engineers/?utm_source=rss&utm_medium=rss&utm_campaign=the-danny-ocean-of-social-engineers