Stuck Between a Data Breach and a Ransom
2020 will be remembered for a whole host of reasons. Campfire stories will be told to grandchildren of when we all had to wear face masks, stand 2 meters apart and were not allowed to hug or shake hands. For those who hunt cybercriminals and attempt to shine a light on notoriously shady hacking operations, the blurring of the lines between what constitutes a ransomware attack and data breach will be the chosen campfire horror story, starting with the Maze ransomware. The gang behind the malware’s distribution saw an opportunity it could not ignore when forcing victims to pay the ransom. Ingenious in its simplicity and dastardly in the extra stress it would cause business leaders, the gang threatened to release stolen data if the initial ransom demanded to decrypt encrypted files was not paid promptly. Soon, these threats became reality.
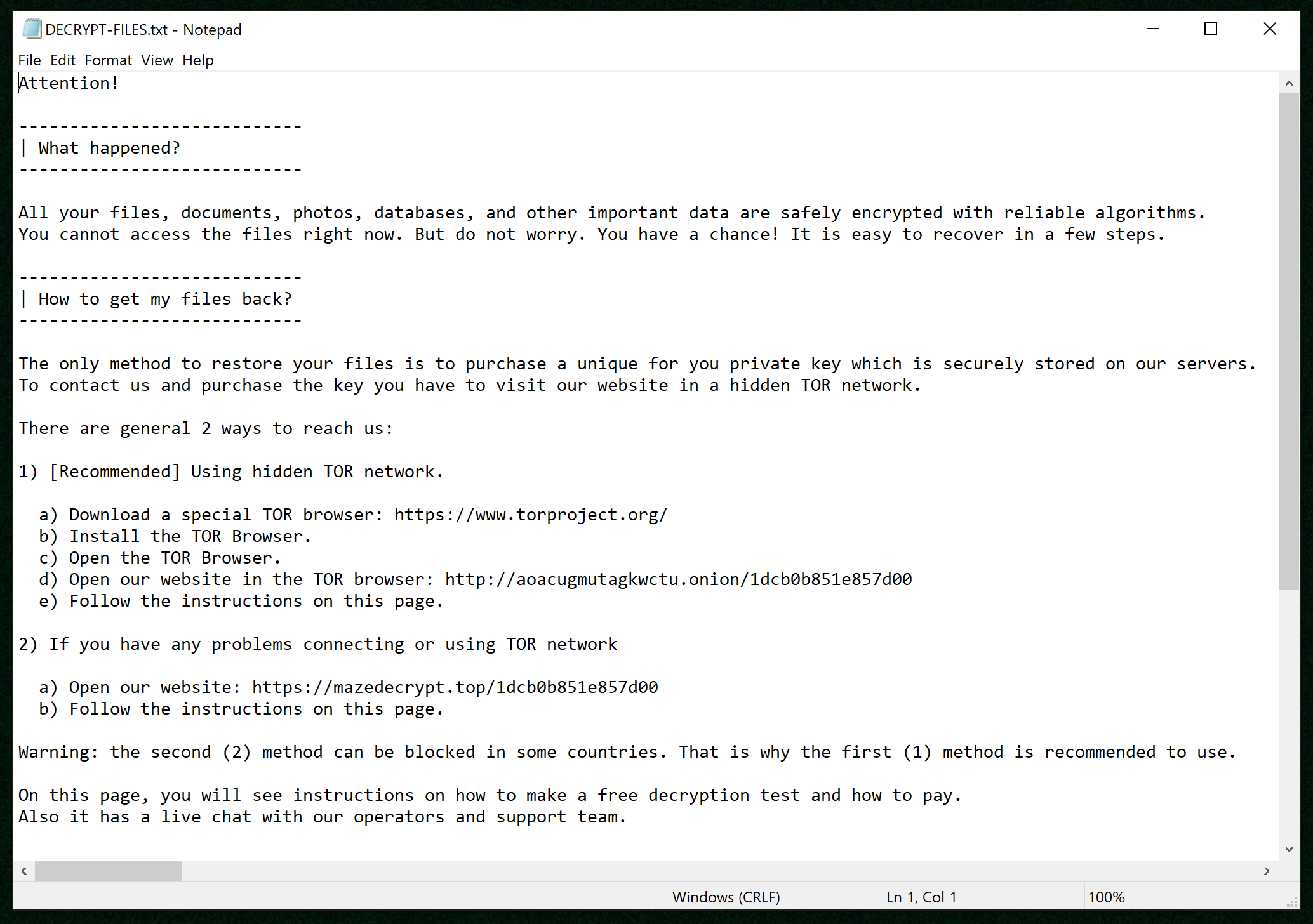
Maze Blurring the Lines
While some were still feeling the hangover of New Year ’s Eve parties and others were writing out their resolutions, news broke that one of the victims of Maze was suing the ransomware operators, referred to as “John Doe” in filed legal papers, for illegally accessing the company’s network, encrypting files and publishing data when the ransom wasn’t paid. The company, Southwire, fell victim to a Maze attack in December 2019. The ransomware gang, before encrypting vital files needed to operate at an acceptable level, stole 120GB of data and proceeded to encrypt 878 devices.
The company did as is often advised and did not pay the ransom, which resulted in the ransomware gang publishing a section of the stolen data, showing that it would make good on its threats. The ransom amount initially was set at 850 bitcoins—approximately $6 million USD at the time, a staggering amount when compared to the several hundred demanded in the malware’s infancy. However, in an age of human-operated ransomware that is determined to tackle massive corporations, millions now are demanded with the amount dependent on how well-off the company is perceived to be.
By the end of January, the gang was releasing the data of multiple victims in an effort to extort payment from its victims. Given the extra pressure now faced by businesses to pay the debate to pay or not to pay again resurfaced now in a higher gear. By not only threatening but actually releasing stolen data, what was once treated as a ransomware incident is now also a data breach. If that data contains information protected by numerous data privacy laws, such as GDPR or PCI DSS, the company may be further fined due to non-compliance if the data was not properly managed. It has been argued that a ransomware attack amounts to a data breach regardless of whether data is released to the public; however, these arguments have become purely academic in the face of current realities.
This pattern has continued with the latest development in the Maze saga, as the gang seems to have teamed up with the gang behind Ragnar Locker. The partnership involves the shared use of the data-leaking platform created by those behind Maze. This would be the second gang to partner with Maze, the first being LockBit. The current partnership seems to be driven by the sharing of intel that can help future operations become more effective at turning targets into victims. As to what exactly Maze gets from the partnership, as it seems to be the main contributor and is sharing its data-leaking platform, it may be that the gang gets a share of the other’s profits for providing the platform as a service. As more ransomware gangs struggle to successfully target the biggest game out there, cooperation between gangs may be the next troubling trend that will shape the threat landscape. The sharing of resources, intelligence and ultimately victims will make ransomware more difficult to combat if this is indeed the case.
Sodinokibi’s Quick Adoption
It was not long after Maze started publishing stolen data that other big names followed. One of those was Sodinokibi—also called REvil by several security firms and media houses—which published data appearing on a well-known Russian hacker forum. Approximately 337MB was dumped to show that the gang was willing to make good on a threat it made earlier soon after Maze began dumping data. Around the same time, the ransomware gang had snagged two high-profile victims in Travelex and CDH Investments, and the threats may well have been intended for those organizations as they both had publicly stated that they would not be paying the ransom. Also in January, a report revealed that ransom costs had nearly doubled in the fourth quarter of 2019. According to the report:
“In Q4 of 2019, the average ransom payment increased by 104% to $84,116, up from $41,198 in Q3 of 2019. While the median ransomware payment in Q4 was $41,179, the doubling of the average reflects the diversity of the threat actors that are actively attacking companies. Some variants such as Ryuk and Sodinokibi have moved into the large enterprise space and are focusing their attacks on large companies where they can attempt to extort the organization for a seven-figure payout. For instance, Ryuk ransom payments reached a new high of $780,000 for impacted enterprises. On the other end of the spectrum, smaller ransomware-as-a-service variants such as Dharma, Snatch, and Netwalker continue to blanket the small business space with a high number of attacks, but with demands as low as $1,500.”
The good news is that ransomware has been thin on the ground and incredibly hard to find.
The same firm published a follow-up report detailing the cost associated with ransomware for the first quarter of 2020, which again had risen, another 33% over the previous quarter, according to the report:
“In Q1 2020, the average enterprise ransom payment increased to $111,605, up 33% from Q4 of 2019. Ransomware distributors increasingly targeted large enterprises and were successful in forcing ransom payments for the safe recovery of data. Large enterprise ransom payments are the minority by volume, but the size of the payments dramatically pulled up the average ransom payment. The median ransom payment remained relatively stable at $44,021, up only slightly from the Q4 2019 median of $41,179. The stability of the median reflects the fact that most ransom payments were modest relative to the average.”
In both reports, Sodinokibi featured heavily as one of the main agitators contributing to the spike in ransomware costs. A key point discussed in the reports was the ransomware gangs that were also making use of what the report describes as data exfiltration and what this article refers to as data theft. Surprisingly, Maze was the only ransomware that was seen to decrease in data exfiltration attempts while others, including Sodinokibi, increased attempts to steal data. One such attack by Sodinokibi that made international headlines was the successful data exfiltration and encryption of the U.S. legal firm Grubman Shire Meiselas & Sacks. The firm represents John Mellencamp, Elton John, David Letterman, Robert DeNiro, Christina Aguilera, Barbra Streisand, Bruce Springsteen and Madonna to name a few, as well as numerous high-profile corporate entities.
The gang claims to have stolen 756GB worth of data from the law firm, and even threatened to release information discovered in the attack belonging to U.S. President Donald Trump; however, it is unclear whether the law firm represents Trump in any of his private or public ventures. To prove that the gang did indeed have sensitive data on celebrities, it published a small amount of data pertaining to Christina Aguilera and Madonna. The announcement was made via its blog, ironically titled, “Happy Blog.” Such announcements certainly applied increased pressure to the law firm’s decision-makers regarding whether to pay the ransom. The initial ransom demanded was $21 million USD, which would double if it wasn’t paid promptly.
To the Highest Bidder
The latest development in this saga involves the Sodinokibi gang creating an eBay-like auction site to sell the stolen data. The gang claimed to have already sold the data pertaining to Trump for $1 million USD and was looking to find buyers for the data pertaining to Madonna. This inspired the gang to offer a bidding service to make it easier for those looking to gain information that could be used for blackmail, identity theft or a whole host of other nefarious activities.
The auction site was added to its blog at the start of June. Reports from the time reported that the gang was auctioning information belonging to two companies—a U.S. food distributor and a Canadian agricultural company. The food distributor’s data started bids at $100,000 USD but the lot could be had for $200,000 USD. The Canadian data had a similar bid and sale structure—his time bids started at $50,000 USD and bought once-off for $100,000. The auction site even had a list of rules bidders had to agree to before participating:
“To bid on an auction, you must register for each auction separately. After registration, you will need to make a deposit of 10% of the starting price. At the end of the auction the amount will be refunded (except for blockchain commission). If you have not paid your bid on the winning auction, you will lose your deposit. This is to ensure that none of the bidders make fake bids. All computational operations are performed in the cryptocurrency Monero (XMR). By clicking Continue you confirm that you agree to the terms above. You will be given a username/password and details of deposit payment.”
Conclusion
With ransomware operators looking to diversify their portfolios by making money off of stolen data via auctions, the threat posed to organizations has increased significantly. Already, prestigious law firms and Fortune 500 companies have fallen victim to ransomware incidents; now the attackers have another option available to them to profit from their illegal activities. Not only are Maze and Sodinokibi releasing and auctioning off stolen data; currently, Ako, Clop, DoppelPaymer, Mespinoza, Nefilim, Nemty, NetWalker, Ragnar Locker, Sekhmet and Snatch also have adopted similar tactics.
For the victims, the question of whether to pay adds complexity. It is clear some organizations do pay the ransom: Now faced with the added potential cost of fines for non-compliance with regulations, the need to pay the ransom has raised the stakes beyond tolerable levels. However, despite the pressures faced by decision-makers, the advice is still not to pay the ransom. Not only do ransoms fund criminal enterprises, but paying also opens the organization to exploitation from other ransomware and malware gangs working with the original perpetrator.
In an interview with Bleeping Computer, a representative for the FBI summed up this view neatly:
“The FBI encourages victims to not pay a hacker’s extortion demands. The payment of extortion demands encourages continued criminal activity, leads to other victimizations, and can be used to facilitate additional serious crimes. Furthermore, paying a ransom does not guarantee the victim will regain access to their data. The best approach is to focus on defense in depth and have several layers of security as there is no single method to prevent compromise or exploitation.”