Tech Support Scams and What They Mean
Since 2008, tech support scams have been raking in millions of dollars annually, with victims often paying several hundred dollars in the false belief that the person on the other end is helping them to prevent a far greater danger from infecting their computer. Driven by advances in technology and software that allow for a third party to control the victim’s computer remotely, tech support scams are incredibly profitable. However, before the scammer gains access to the computer remotely, the scam begins with the use of older, more humble technology: an email or a phone call.
The good news is that today people are falling for these scams in far fewer numbers, as awareness of such scams has increased and tech giants have collaborated to prevent the scams. However, they do still exist, still catching victims off-guard. According to research published in 2018, those living in India were most likely to be caught out by a tech support scam, while in the U.S. those residing in California, Florida, Texas and New York were most likely to fall victim.
How Scammers Operate
One of the best methods of protection against a tech support scam is knowing how they operate. The majority of these scams begin with a phone call or an email from a supposed tech support agent requesting they receive a call back to solve a fake problem. In one popular tactic, the scammer pretends to be a Windows support agent. Another method exploits web page features, creating a page that opens full-screen and cannot be closed easily. The web page states that the computer is infected with several pieces of malware and the user needs to contact the number provided.
Regardless of the scammers’ chosen method—be it a phone call, email or a web page that fails to close—the main aim is to get in contact with potential victims. Then the next phase of the scam begins: trying to gain the potential victim’s trust by being a supposedly legitimate agent for a company. Several tactics are used to accomplish this, from simply providing a fake agent number to the victim to using Windows tools to convince them that there is indeed a problem with their computer.
The use of Windows Event Viewer has become a popular tactic used to convince the victim that their computer is infected. Event Viewer operates as a system monitor, tracking the performance and activity of the computer. This includes showing errors, which often are used to provide the evidence of a system under attack. In reality, generating errors is normal for computers. In other cases, scammers have gone so far to direct the user to a link or email attachment that will download a piece of malware in an attempt to prove their legitimacy.
Remote Access
The above tactics are an insidious use of social engineering and exploiting people’s lack of technical know-how. If the scammer is successful, the scammer them tries to gain remote access to the target computer. Legitimate remote access software often is abused by scammers, who convince the victim to download the program and allow the scammer, who they believe to be a tech support agent, remote access to the computer.
Once this occurs, the scammer can install malware such as ransomware, adware packages to generate ad revenue, keyloggers or banking trojans to steal online banking credentials. To add insult to injury, the scammer then demands payment for their service once they have “protected” the victim from further attacks, demanding anywhere between $100 USD and $600 USD.
Payment can also be done in several ways. In the past, scammers would ask for the victim’s credit card information, which put the credit card at risk for future fraudulent purchases. But a crackdown by credit card companies and the inclusion of newer payment verification methods have forced scammers to move away from demanding payment directly. In one case, the scammer demanded that the victim purchase Google Play Store cards preloaded with the requested amount.
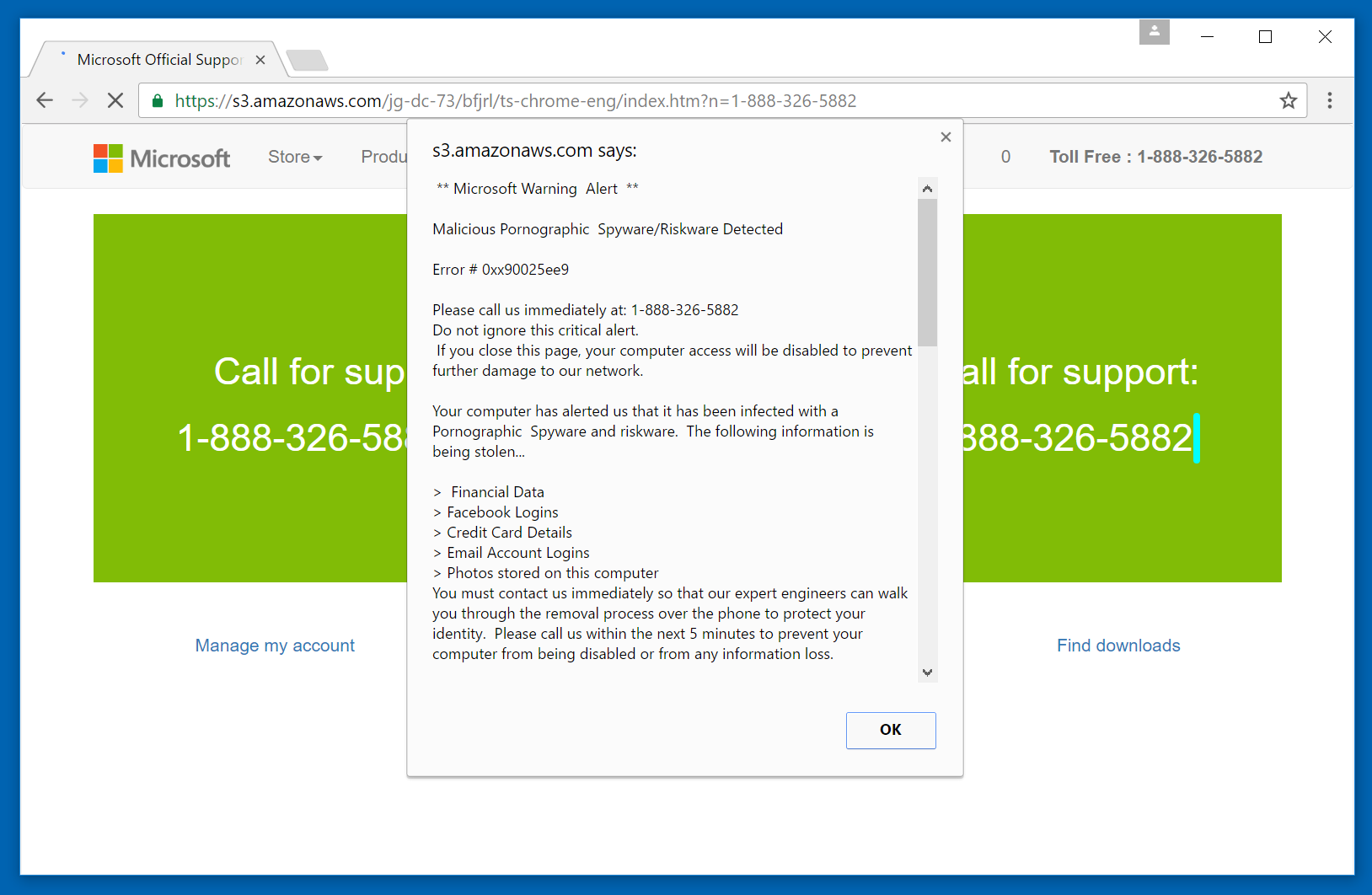
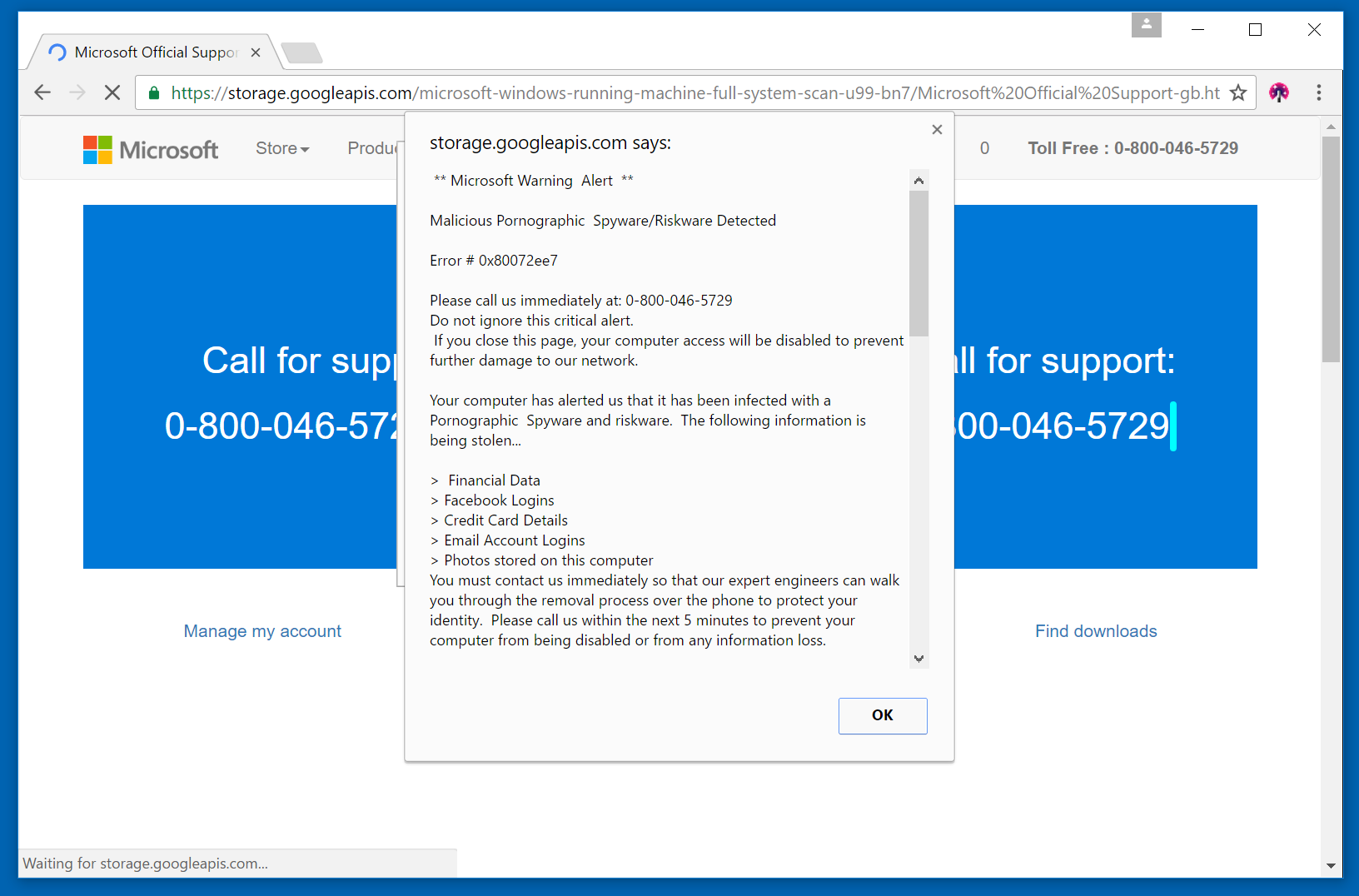
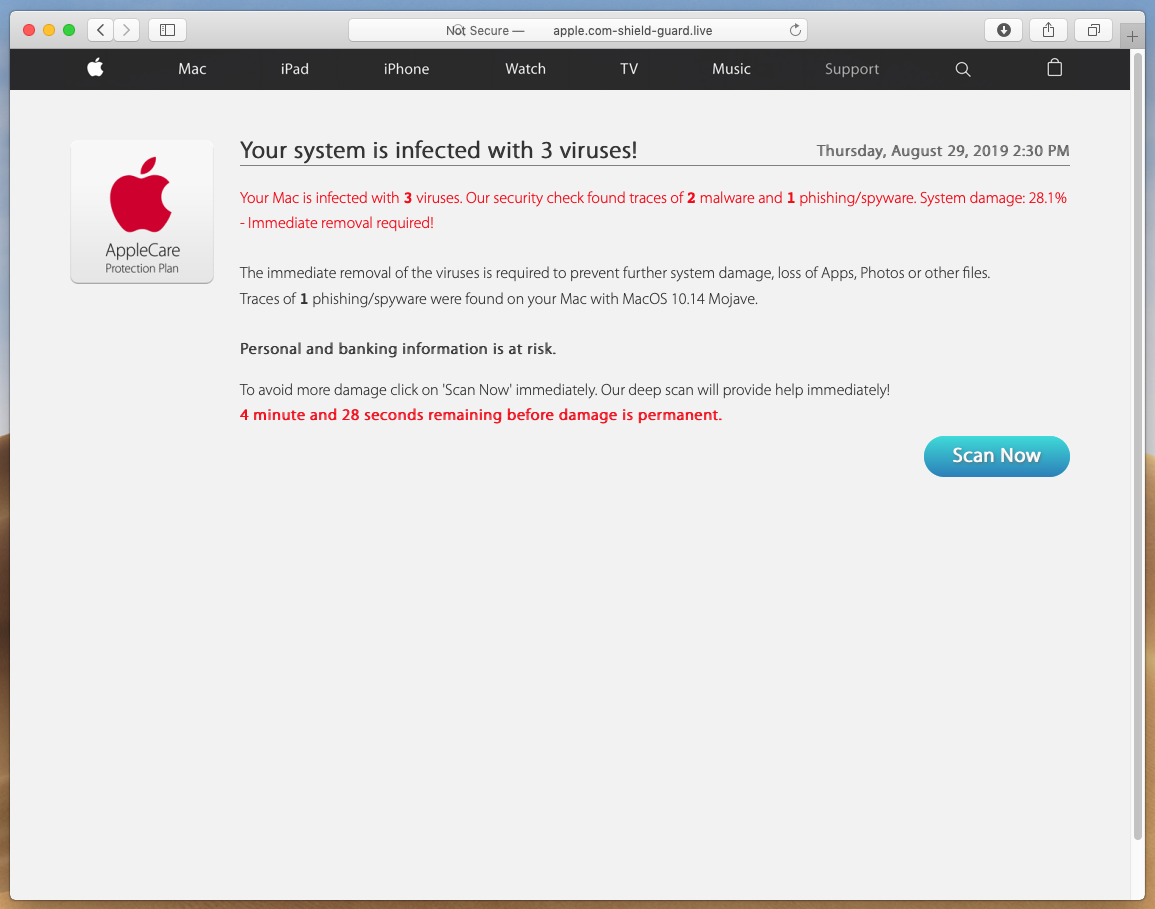
Here are screenshots of some popular tech support scam pop-ups in 2019.
Example 1 – “Pornographic virus alert”:
Example 2 – “Microsoft warning alert”:
Example 3 – “Your system is infected with 3 viruses” (Mac):
Real-World Case
Earlier it was mentioned that those residing in India are more likely to fall for such a scam. This statement, although backed by statistical data, can be interpreted in a number of ways. However, it should not be interpreted that such a scam is a geographical or cultural problem. The problem is indeed global, as illustrated by the recent discovery of a scam targeting people residing in the United Kingdom.
Security researchers discovered that scammers were targeting mainly elderly and vulnerable people using BT, a British telecoms and internet service provider. One woman fell foul to the scam and lost up to 34,000 GBP. Like with many other tech support scams, the person on the other end of the line pretended to be an employee of BT. The scammers, in this case, had access to both names and numbers of BT customers—information that could have resulted from a data breach and would normally not be available publicly. This allowed the scammers to be far more targeted in their approach, making the scam in general far more dangerous.
Those behind the scam adopted several tactics to defraud their victims. One such tactic is known as an overpayment scheme, in which the scammer tells the victim they have overpaid an amount for services. The scammer deliberately transfers an amount into the victim’s account and asks for the victim to transfer the amount allegedly overpaid. Then the scammer cancels the original transaction, netting the original transaction and the “overpaid” amount.
Other scammers resorted to tried-and-tested tech support tactics. Often the scams were initiated by a robocall claiming to be from BT and that they should call back the number provided. To get the BT customer to call back, the scammer raises the apparent stakes by claiming that the customer’s internet service will be cut off if they do not call back. From here, the scammer can demand amounts for tech services rendered or, like in the example above, use other methods to defraud the elderly and vulnerable. In these cases, the scammer would ask the victim to download TeamViewer, a legitimate remote access software, to gain remote access. From there the victim’s computer opens up a wealth of opportunities to the scammer.
How to Spot a Tech Support Scam
One of the first telltale signs of a tech support scam is an unsolicited phone call or email. Legitimate tech support agents do not contact customers in this way. Recipients should simply hang up or not respond. Those needing support can search the web for the correct number—legitimate companies will have their numbers registered and customers can check the company contact details via official correspondence.
In addition, users should know what software is being installed on their computer. When in doubt, leave it out. However, this may more difficult to adhere to, as tech support scammers use legitimate software to gain remote access.
Those who believe they have been scammed should contact their local law enforcement agency to report a crime. By reporting the incident, victims can help law enforcement catch those responsible and hopefully bring them to justice. Divulged credit card information or any other personal financial information also should be reported to the victim’s financial institution, so the card can be cancelled to prevent future fraud or identity theft. Recovering a stolen identity can be a nightmare at the best of times.