Ransomware Attackers turn to Google Ads after Dream Market Take Down
The ransomware supply chain faced disruption this week after a prominent dark market place was likely seized by law enforcement. In a sequence of events similar to the xDedic seizure, the email addresses and communications between ransomware distributors and victims all but stopped as ransomware operators hurried to delete and disconnect accounts linked to Dream Market. Dream Market was the last remaining major dark market for illicit goods that had originally sprung up after Silk Road was dismantled by law enforcement. The other three were AlphaBay, Hansa Market, and RAMP which were seized and closed by US, European and Russian authorities in mid 2017.
Dream Market Likely Seized by Law Enforcement, Users Rush to Cover Their Tracks
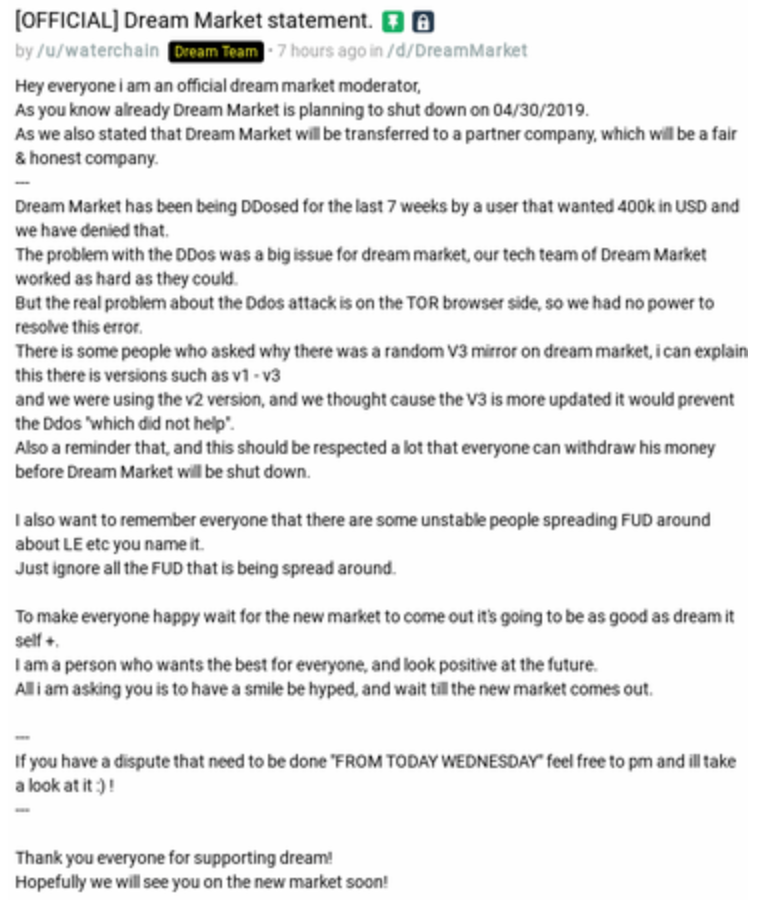
The announcement by Dream Market was made on the same day as FBI, Europol, and DEA officials announced dozens of arrests across a coordinated effort to staunch drug trafficking on the dark web. The announcements sent dark market users rushing to cover their tracks, and the security community speculating if law enforcement had actually been running the site in order to glean as much incriminating evidence as possible.
The reaction by Dream Market users, many of whom may be involved in Ransomware, is similar to the Hansa Market seizure in June 2017. When Hansa Market was seized, it was quietly run by Dutch police for a full month. The Dutch police collected troves of evidence on the sites users. The xDedic take down in January of 2019 spurred similar theories that law enforcement seized user account credentials to gain access to other incriminating email accounts and fully capture evidence of dark market participants. After the xDedic takedown, there was a similar lull in ransomware communications across some variants.
Ransomware Distributors Get Creative to Salvage Disrupted Ransom Extortions
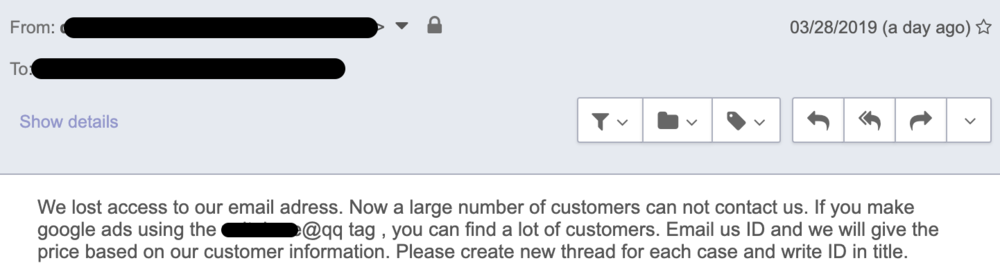
The abandonment of email addresses left both distributors of ransomware and their victims in a communications lurch after scores of active extortion negotiations went silent. In an attempt to recover ransom payments, some ransomware operators proactively reached out to ransomware incident response firms with messages like the one below:
Email from Dharma Ransomware Group requesting help sourcing prior victims
In this example, the contact (from a Dharma distribution group that previously used the a @qq.com’ handle) suggests that Google Ads be purchased on their previous email address in order to attract the abandoned ransomware victims that may be searching online for help. A quick Google search shows that no firm that received this message has taken this group up on their offer.
Six-Year History of Dream Market Comes to an End
Dream Market had a relatively long span of operations between April 2013 and April 2019. It was the last of the four main dark-markets that had sprung up after the collapse of SilkRoad, which was seized and shut down by US law enforcement in 2013. It is not uncommon for marketplaces to close abruptly if the moderators (who often act as escrow agents for buyers and sellers) choose to exit with the balance of goods and currency held for settlement. In the absence of Dream Market, sites such as T•chka and Wall Street Market will likely become the go-to dark web destinations for buying illegal goods and services, including malware and stolen data.
In further announcements, the Dream Market team attributed the shutdown to a planned migration of the site’s users base to a new venue because of prolonged DDoS attack on the TOR site. The DDoS attack had been ongoing and the single actor was demanding a $400,000 ransom demand that the site’s operators did not want to meet.
If history repeats itself, the activity that flowed through Dreamwill likely reconstitute on alternative sites. While the recovery of dark market activity may seem disheartening for victims of ransomware, or to individuals that may have lost loved ones to an overdose on drugs purchased from these sites, it is important to recognize that these takedowns act as a major deterrent to the proliferation of illicit activity. Additionally, arrests of ransomware distributors can often lead to the recovery of servers and software that can be used to build free decryption tools for past victims.
*** This is a Security Bloggers Network syndicated blog from Blog | Latest Ransomware News and Trends | Coveware authored by Bill Siegel. Read the original post at: https://www.coveware.com/blog/dream-market-take-down-causes-ransomware-communication-chaos