Ransomware Evolution: GandCrab v5.1 New Exploit Kit Distribution and TOR Site Features
Last fall, Bitdefender coordinated with law enforcement to release a free decryption tool GandCrab Version 5.0-5.0.3. For victims, the release of the free decryptor was a welcome relief. The action demonstrated how public and private organizations can collaborate to help victims of ransomware.
Unfortunately, the developers of GandCrab released version 5.0.4 about 24 hours after the Bitdefender tool was made public. The most recent version, GandCrab v5.1, comes with a variety of distribution changes and UX updates to the GandCrab TOR site, which we expound upon below.
GandCrab v5.1 Distributed in a Variety of new Exploit Kits; More Ransom IDs Left Behind
The primary attack vector for ransomware remains RDP ports, but GandCrab has a diverse array of distribution methods. While RDP-based ransomware attacks remain popular, automated attacks using exploit kits such as Fallout EK, Emotet, or credential stealers like Vidar have been linked to GandCrab infections as well.
The use of these broadly available toolkits has coincided with the increase in the average size of GandCrab ransoms, and with new patterns in the number of ransom ID’s per infection.
Prior to the exploit kits gaining popularity, a single attack would typically have one or two unique IDs (file extensions). Each ID had its own TOR page, with a ransom amount scaled to the perceived value of the underlying machine. Since the more automated exploit kits have gained popularity, the number of unique IDs in a single infection has skyrocketed. Some victims have dozens of ID’s to contend with. Each ID tends to have the same ransom amount, indicating a ‘spray and pray’ methodology vs a more surgical attack.
GandCrab v5.1 TOR Site – Core Features Unchanged
The GandCrab TOR site has always been relatively well designed as compared to other types of ransomware TOR sites, such as Nozelesn and SamSam. A working TOR payment site requires active management, and neglect can have negative consequences.
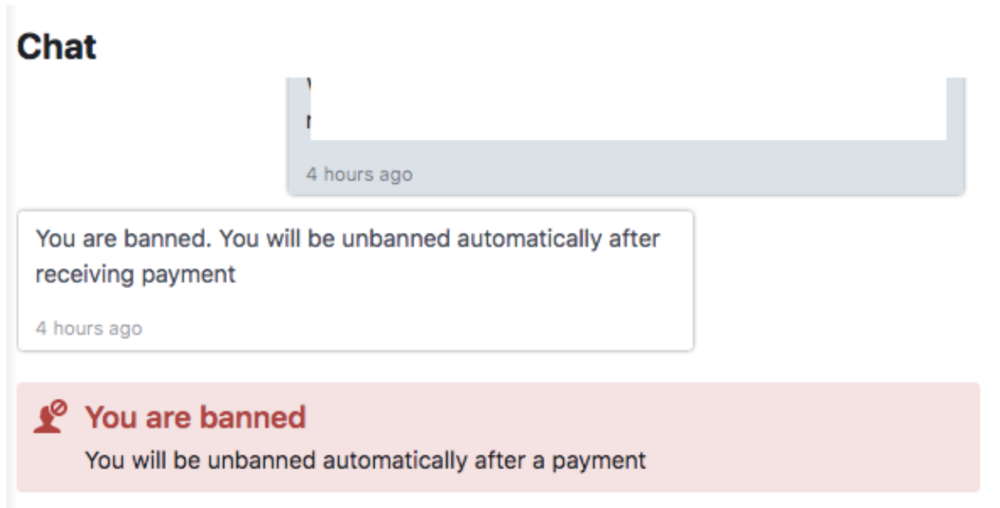
On the GandCrab 5.1 TOR site, the chat support is remarkably well staffed. In our own conversations, it is rare to wait more than 30 minutes without a response, regardless of time of day. They assist in troubleshooting and are not misleading. They also have little patience for rude or aggressive language. Some victims were banned from chat support until paying the ransom after they wrote some colorful language in the chat.
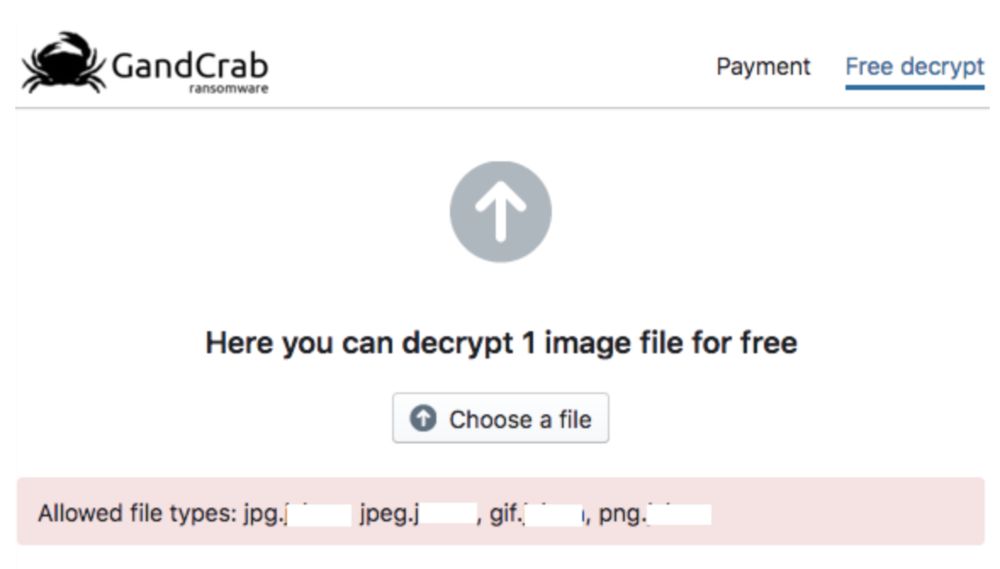
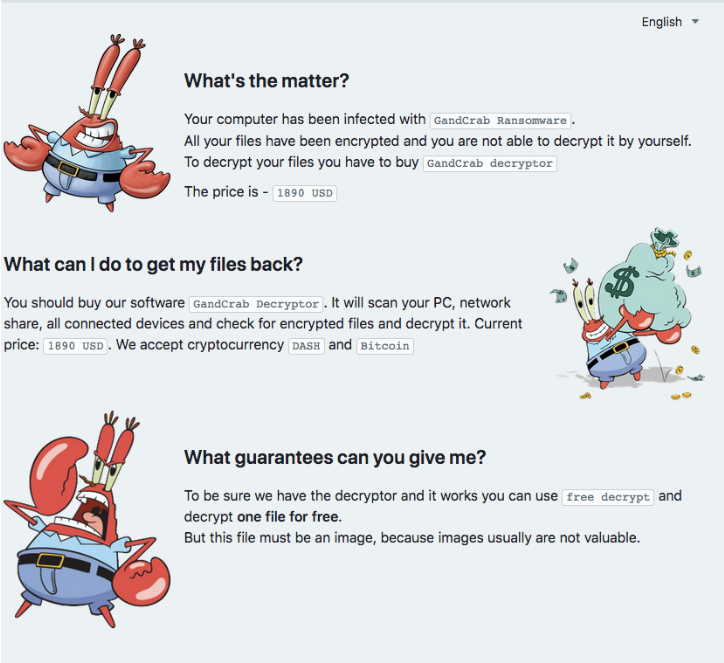
In addition to chat support, the automated test decryption feature remains bug-free. Victims of an attack are able to upload a small image for proof of decryption. The site will offer the decrypted file back via download. We imagine considerably development went into making this feature robust. File restrictions ensure no files of value are decrypted for free.
Enablement Features for Dishonest Data Recovery Firms Persist
As previously documented, the GandCrab TOR site has features that enable dishonest data recovery companies. The features allow a data recovery firm to hide the actual cost of the ransom from the victim, along with their chats with GandCrab support.
The first feature is a discount code. The discount code can be requested over chat, but it is only activated for subsequent infections to avoid discounting each victim that requests one. The discount code is entered on new GandCrab pages, as shown below:
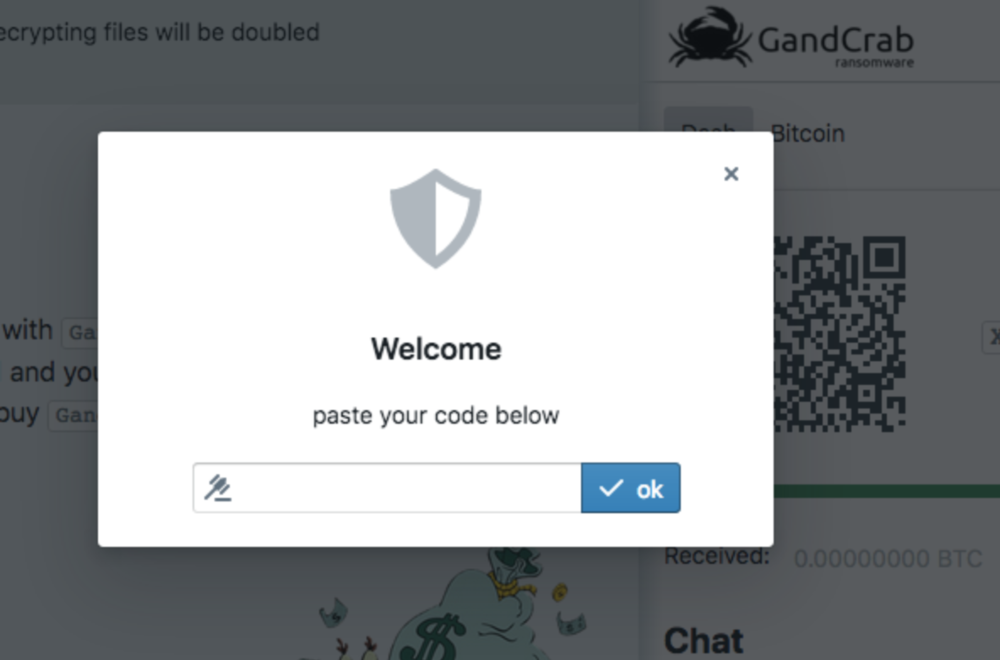
After entering the code, the applicable discount is displayed and the USD ransom amount on the payment pages is automatically adjusted. Discounts range from 5-20% depending on the size of the ransom. For full disclosure, Coveware possesses a discount code and passes all discounts on to clients without offset.
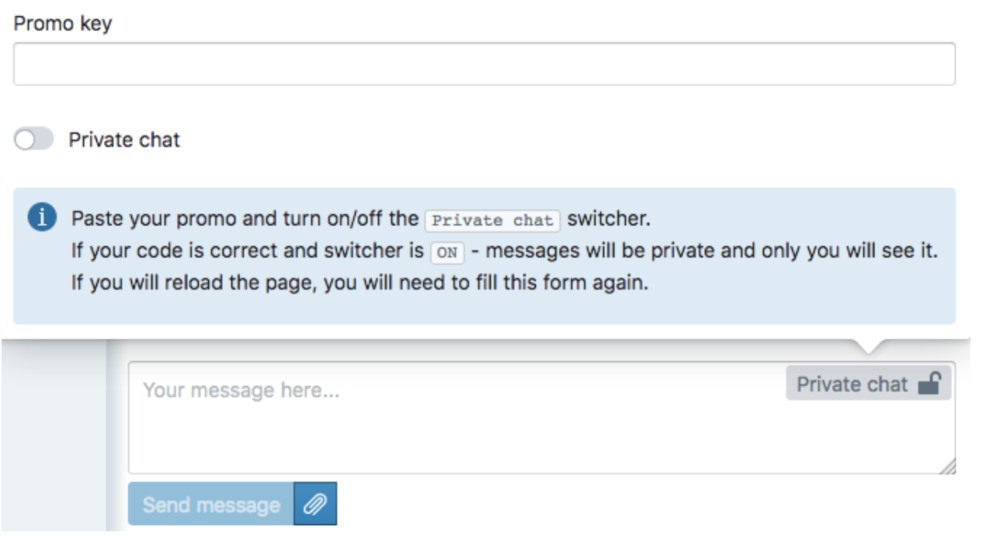
The second feature is a private chat that can be enabled via the same ‘discount’ code. The image below shows how a user with a code can enable a private chat hidden from any other visitor on the TOR site. This is useful for dishonest data recovery companies that lie about the cost of decrypting files to their clients.
GandCrab 5.1 Developers Invest in New Graphics, Sound Effects
In addition to the new distribution and infection patterns, the GandCrab developers invested some time into their UX. The GandCrab v5.1 TOR site features new crab cartoon graphics. The graphics give the impression that the developers feel their ransomware is little more a prank, rather than a serious existential attack on a business or a person’s data.
There is also a hidden feature behind the GandCrab logo. When clicked, the screen toggles between a light and dark color scheme. The embedded sound effects that play when the colors change are sourced from ‘Night Stalker,’ a character from the video game Dota 2. Again, the developers give the impression that their ransomware is a game with inconsequential real-world effects.
GandCrab v5.1 Ransomware Payment
The payment process remains straight forward and paying in Dash remains cheaper than Bitcoin as the developers are able to lower their bitcoin mixing costs.
The wallet address for each page is unique (only used once), and is rigged to trigger an updated screen on the TOR site once the correct amount of coins hits the wallet. The page provides guidance on how to view the number of blockchain confirmations required before the decryptor is released so that victims who pay understand the wait time.
GandCrab v5.1 Decryption Tool is Still the Slowest
One area that did not receive any enhancement from the GandCrab developers is the throughput of the decryption tool. Among ransomware decryption tools, it remains the slowest. Large backup drives can often take several days to decrypt. However, the decryption instructions provided have been updated to reflect ways to point the decryptor at specific drives.
GandCrab 5.0.4+ Still No Public Decryption Tool
While Bitdefender released a free decrypter for GandCrab 5.0-5.0.3, GandCrab V5.1+ is currently not publically decryptable.
As always, paying a ransom should be the absolute last resort. Victims are encouraged to seek any alternative plausible versus paying. Saving a full copy of an encrypted machines data is recommended as a first step. Please review our more comprehensive guide for responding to a ransomware attack, or contact us if you are in need of immediate assistance.
*** This is a Security Bloggers Network syndicated blog from Blog | Latest Ransomware News and Trends | Coveware authored by Bill Siegel. Read the original post at: https://www.coveware.com/blog/2019/2/4/gandcrab-51

