The Internet of Things (IoT) and Digitally Stored PII: Avoidable or Inevitable?
The Internet of Things (IoT) is rapidly showing up in all facets of daily life and collecting personally identifiable information (PII) in massive quantities. From smart home thermostats to one-click purchasing, IoT devices collect PII to personalize experiences for consumers. In an increasingly digital and connected world, unprecedented immersion into environments of convenience, knowledge, and accessibility has become the norm. While these are exciting times, it is imperative to consistently manage personal and professional vulnerabilities surrounding IoT and digitally stored PII. As the Spider-Man canon advises, “With great power comes great responsibility,” and it is critical to explore and weigh the risks of convenience against safety and security.
Everything is Connected
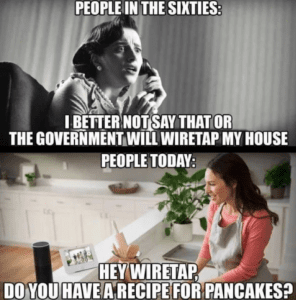
In a bygone era, interesting facts were pulled off the shelf from the appropriate book of a grandparent’s encyclopedia set. The fact that voice-controlled devices can now answer all the important questions of the universe, is an all-out gamechanger.
As illustrated in the Libelium Smart World infographic, IoT has the potential to have a positive impact on a grand scale. Transportation infrastructure, environmental hazard detection, and monitoring food supply safety could improve quality of life, business efficiency, and profitability for millions of people.
The darker side of IoT and digitally stored PII warns of in-home violations via hacked baby monitors, compromised appliances initiating malicious global email attacks, and life-threatening access to implanted pacemakers. While some companies claim to “ensure” encryption and promise not to share user information, the use of a genealogy site to capture a serial killer has already set a precedent for using consumer information in unexpected and unintended ways. There is a delicate balance between championing innovation and cultivating risk awareness.
How IoT can turn ugly
It often feels like life operates at break-neck speed, so conveniences afforded by IoT and digitally stored PII, such as one-click ordering and dash buttons, are a welcome respite. However, enter in a phone porting scam, where someone steals another person’s mobile number, and suddenly a malicious actor has incredibly easy and damaging access to saved retail sites, purchase history, payment methods, and home address. All this information provides enough material to launch a sophisticated social engineering attack and open attack vectors to the intended target’s network of family, friends, and colleagues.
Threat Mitigation
Manufacturing and purchases of IoT products and services aren’t going anywhere but up. The boom of available products has exploded in recent years and is on track to multiply exponentially year over year. There isn’t a regulated standard for monitoring such a boom so the onus of safety and security falls on the shoulders of individual users. Taking calculated risks is highly subjective and personal, so it’s up to each person to research and educate themselves on how IoT and digitally stored PII fits into, and affects, their lives. Seek out expert advice on privacy control strategies, such as former government computer crime investigator Michael Bazzell’s interviews and book. Be an informed consumer and use purchasing power to support companies and products that take security seriously. Monitor accounts and devices regularly to detect anything unusual. Implement best practices for good cyber hygiene like having robust passwords and not using the same password for multiple devices or accounts.
Feeling Comfortable with Digital Connection
As IoT and online actions involving PII move in the direction of becoming unavoidable, it’s helpful to focus on practical actions anyone can take to avoid digital anxiety. Here are some steps that may help:
- Read the Terms of Service:
“But no one reads these!” The amount of permissions and access outlined in some are quite surprising; take a look in order to make more informed decisions.
- Set up “dummy” accounts with fake information:
When signing up for something online, there will often be prompts to connect the new platform with an existing email or social media account. Create an anonymous email address or false social media profile to fulfill the set-up parameters. This can shield personal information from a high quantity of apps and aggregations.
- Use pre-paid credit cards:
When making a one-time purchase or participating in a “free trial,” using a pre-paid credit card will remove the risk of using personal credit on multiple sites. It is even possible to use an expired or empty pre-paid credit card on free trials so when the introductory period ends, and it starts to charge the card on file, it is not a useable account.
- Put IoT Devices (like smart security cameras) on their own network that utilizes a separate firewall, so the main network is walled off.
- Monitor cell phone apps and access:
Is the Wi-Fi connection secure? Is the Bluetooth connection necessary? Does the location feature connect with apps to send alerts when near a certain business that happens to have a sale? Yes, this happens and, yes, it is creepy!
- Unplug devices not being used so they aren’t always “listening.” Choose specific rooms where devices exist but don’t have access to sensitive conversations.
Investigate and Be Informed:
- Know what data exists, where you can delete it, and what information you own.
- Think through possibilities and probabilities. Anything that is put on the internet never truly goes away and terms, conditions, and laws change.
- DNA testing companies are all the rage. In fact, one just partnered with a pharmaceutical company. Could this data be used against people?
Many companies digitally store extremely personal data such as race, ethnicity, hormone levels, fertility statistics, allergies, and DNA. Every company has different privacy policies which are each open to changing guidelines, hacking, subpoenas, human error, and malicious actors. Awareness and determining personal risk allowance, as they pertain to IoT and digitally stored PII, are key to making decisions about what, when, where, and how information is shared.
This is the direction our world is headed so now is a great opportunity to become properly educated and prepared to handle the new reality of increasingly ubiquitous IoT and digitally stored PII. Making it a habit to think about, and take, security precautions whenever possible can offer peace of mind
Sources:
https://www.forbes.com/sites/jacobmorgan/2014/05/13/simple-explanation-internet-things-that-anyone-can-understand/#655027f91d09
https://www.social-engineer.org/general-blog/identity-thieves-phishing-and-pilfering-your-pii/
https://quoteinvestigator.com/2015/07/23/great-power/
https://arstechnica.com/information-technology/2017/11/rethinking-our-approach-toward-personal-threat-models-in-an-iot-world/
http://www.libelium.com/libelium-smart-world-infographic-smart-cities-internet-of-things/
https://www.npr.org/sections/thetwo-way/2018/06/05/617196788/s-c-mom-says-baby-monitor-was-hacked-experts-say-many-devices-are-vulnerable
https://www.infoworld.com/article/2930366/internet-of-things/welcome-to-the-smart-home-of-horror.html#slide8
https://thehackernews.com/2017/08/pacemakers-hacking.html
http://time.com/5256835/how-did-golden-state-killer-genealogy-websites-online-dna-police/
https://www.digitaltrends.com/home/what-is-an-amazon-dash-button/
https://www.social-engineer.com/your-phones-betrayal/
https://www.csoonline.com/article/2124681/social-engineering/what-is-social-engineering.html
https://www.forbes.com/sites/louiscolumbus/2018/06/06/10-charts-that-will-challenge-your-perspective-of-iots-growth/#56ea8943ecce
https://www.intel.com/content/www/us/en/internet-of-things/infographics/guide-to-iot.html
https://www.forbes.com/sites/bernardmarr/2015/10/27/17-mind-blowing-internet-of-things-facts-everyone-should-read/#33a9e9b03505
https://www.social-engineer.org/podcast/ep-103-how-to-be-a-good-parent-with-michael-bazzell/
https://security.berkeley.edu/resources/best-practices-how-to-articles/top-10-secure-computing-tips
https://digitalguardian.com/blog/what-cyber-hygiene-definition-cyber-hygiene-benefits-best-practices-and-more
https://www.tomsguide.com/us/how-to-secure-alexa,news-26881.html
http://www.pharmtech.com/gsk-23andme-partner-genetic-drug-development
The post The Internet of Things (IoT) and Digitally Stored PII: Avoidable or Inevitable? appeared first on Security Through Education.
*** This is a Security Bloggers Network syndicated blog from Security Through Education authored by SEORG. Read the original post at: https://www.social-engineer.org/general-blog/the-internet-of-things-iot-and-digitally-stored-pii%E2%80%AFavoidable-or-inevitable%E2%80%AF/



