What Makes a Password Weak or Strong?
In today’s digital age, passwords serve as the first line of defense in securing our online accounts. Yet, despite the increasing awareness of cybersecurity threats, many individuals and organizations still fall victim to password-sourced breaches.
One of the key reasons behind this is the prevalence of weak passwords.
In this article, we’ll delve into the crucial differences between weak and strong passwords. We will also provide practical tips on how to bolster your online security.
WEAK PASSWORDS
Understanding Weak Passwords
Weak passwords are characterized by their vulnerability to various types of attacks, such as brute force attacks, credentials stuffing, and dictionary attacks. These passwords are considered weak because they often lack complexity and are easily guessable or susceptible to automated cracking methods.
Here are some characteristics of weak passwords:
Short Length: Weak passwords are typically short, often consisting of fewer than eight characters. Short passwords provide fewer combinations, making them easier to crack.
- Sample: simpsons
Lack of Complexity: Weak passwords often lack complexity, containing only lowercase letters or common words without any special characters, numbers, or a mix of uppercase and lowercase letters.
- Sample: simpsonfamily
Personal Information or User Name: Attackers often use easily obtainable personal information such as birthdates, names of family members, or pet names as passwords, making them susceptible to targeted attacks. Also, putting your user name in your password is a big mistake.
- HomerSimpson
Repeated Characters or Patterns: Passwords that consist of repeated characters (e.g., “111111”) or simple patterns (e.g., “abcd1234”) are considered weak because they are easy to guess or crack using automated tools.
- Simpson123
Business or Site Name: Passwords that contain the name of the site or business that the password accesses.
- Sample: For example, if you worked at Google, having a password with Google in the name. Or to log into your Amazon account, having Amazon in the password.
Using Leetspeak Paired with Short Passwords: Leet (or “1337”), also referred to as leetspeak, is often used in passwords and they are just modified spellings that use numeric or character replacements in ways similar to numbers. Often the letter “I” will be replaced by the number “1” or an exclamation point “!” while the letter O will be replaced by the number 0. Attackers know these common leetspeak substitutions so a short password is easy to crack, even with leetspeak.
- Sample: H0merS!mpson
Using Previously Exposed Passwords: If your password has already been exposed in a data breach or leak, do not continue to use it for other accounts. Reusing exposed passwords or credentials puts your account at significant risk.
Passwords varied with just 1-2 characters: Similar passwords, or variations of an old, exposed password with just 1 or 2 character changes should not be used. Attackers will often use small variations of your old passwords to get into your account.
STRONG PASSWORDS
Identifying Strong Passwords
Strong passwords are designed to withstand various types of attacks, significantly reducing the risk of unauthorized access to your accounts.
Here are some key characteristics of strong passwords:
Length: This is one of the most important factors. Strong passwords are long, typically containing 16 characters or more. The longer the password, the more difficult it is to crack, as it increases the number of possible combinations. This is why passphrases are often recommended (4-5 unrelated words that have meaning to you.)
- Sample of lengthy password: CloudyMeatballsMockingbirdHouse
Randomness: Strong passwords are not based on easily guessable patterns or personal information. Instead, they are random combinations of characters that are unrelated to your personal life or easily guessable information.
- Sample of random password: CloudyMeatballsMockingbirdHouse (same as above)
Complexity: You can also incorporate a mix of uppercase and lowercase letters, numbers, and special characters (e.g., !, @, #, $, %). This complexity adds an extra layer of security, making it harder for attackers to guess or crack the password.
- Sample of complexity with long password: Cl0udy!Me4tballs*Moc%ingbirdHous3# (riff on the one above)
Unique for Each Account: Using the same password for multiple accounts increases the risk of a security breach. If one site is breached, every other account where you use that same password is also at risk. Strong passwords are unique for each account, reducing the impact of a breach on other accounts. Read more about the password reuse issue.
Tips for Creating Strong Passwords
Now that we understand the characteristics of strong passwords, here are some tips to help you create and manage them effectively:
Use Passphrases: Consider using passphrases instead of passwords. Passphrases are longer and easier to remember, making them both strong and user-friendly. 4-5 longer unrelated words work well.
- Sample of passphrase: “L0veMount4in*Sapphir3P1zzaRoku)” is a strong passphrase.
Avoid Common Words and Patterns: Steer clear of using common dictionary words, phrases, or patterns that are easily guessable or susceptible to dictionary attacks. And please, don’t put the word password in your password. Learn more about common passwords.
- Sample of common words and patterns: PasswordsSuck123
Consider a Password Manager: Consider using a reputable password manager to generate and store strong, unique passwords for each of your accounts. Password managers offer secure storage and auto-fill features, reducing the burden of memorizing multiple passwords. But make sure your master password is truly unique.
Enable Multi-Factor Authentication (MFA): Supplement your passwords with an extra layer of security by enabling multi-factor authentication wherever possible. MFA requires a second form of verification, such as a code sent to your phone, making it significantly harder for attackers to gain unauthorized access to your accounts. But remember, even with MFA, you still need to have a strong password.
CONCLUSION
In conclusion, the importance of strong passwords in safeguarding our online accounts cannot be overstated. By understanding the characteristics of weak vs. strong passwords, along with following best practices for password creation and management, you can significantly enhance our cybersecurity posture and protect ourselves from potential threats. Remember, a strong unique password is your first line of defense in the ever-evolving landscape of cybersecurity.
TEST IT OUT
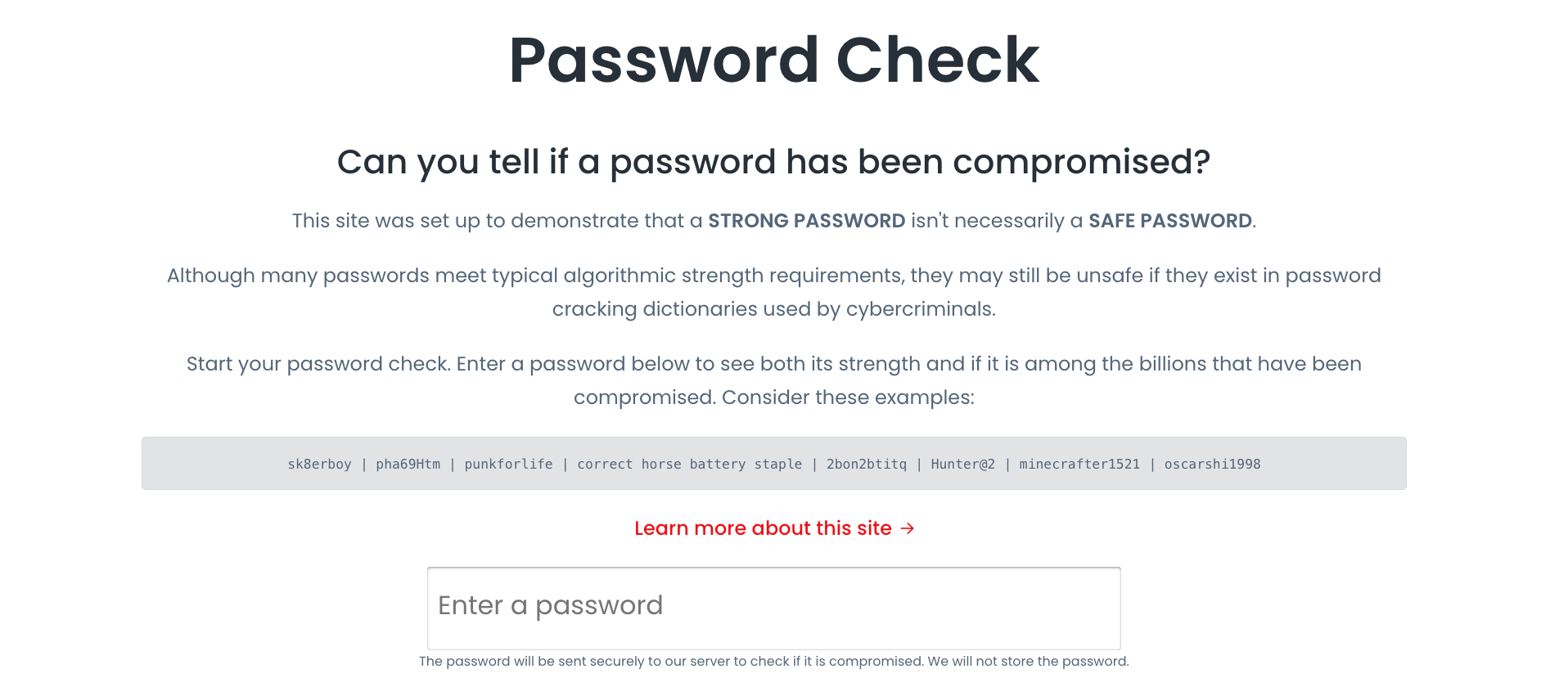
You can check a sample password at our secure site here:
Test out variations of passphrases and passwords to come up with a secure password for each site. Stay safe!
The post What Makes a Password Weak or Strong? appeared first on Enzoic.
*** This is a Security Bloggers Network syndicated blog from Blog | Enzoic authored by Enzoic. Read the original post at: https://www.enzoic.com/blog/what-makes-a-password-weak-or-strong/