Voice of Practitioners: The State of Secrets in AppSec

The risks associated with secrets sprawl in application security (AppSec) are immense. Hard-coded secrets, such as API keys and configuration variables, are the gateway to a company's most valuable asset: its data. Despite this, many organizations still rely on manual code reviews to protect themselves from secrets being hard-coded in source code, despite being notoriously inefficient and ineffective.
To shed light on this issue, GitGuardian commissioned Sapio Research to conduct a study on the perceptions and practices of 507 IT and security decision-makers in the US and UK. The study, entitled "Voice of Practitioners: The State of Secrets in AppSec," provides valuable insights into the risks posed by secrets sprawl and the measures taken to mitigate them in large enterprises.
The study reveals that senior management in large organizations is acutely aware of the risks associated with hard-coded secrets. A significant 75% of respondents reported having experienced a past leak, and 94% plan to improve their secrets management practices in the next 12-18 months. Interestingly, more than half of the respondents identified "source code and repositories" as key risk points within their software supply chains, with 47% specifically citing hard-coded secrets.
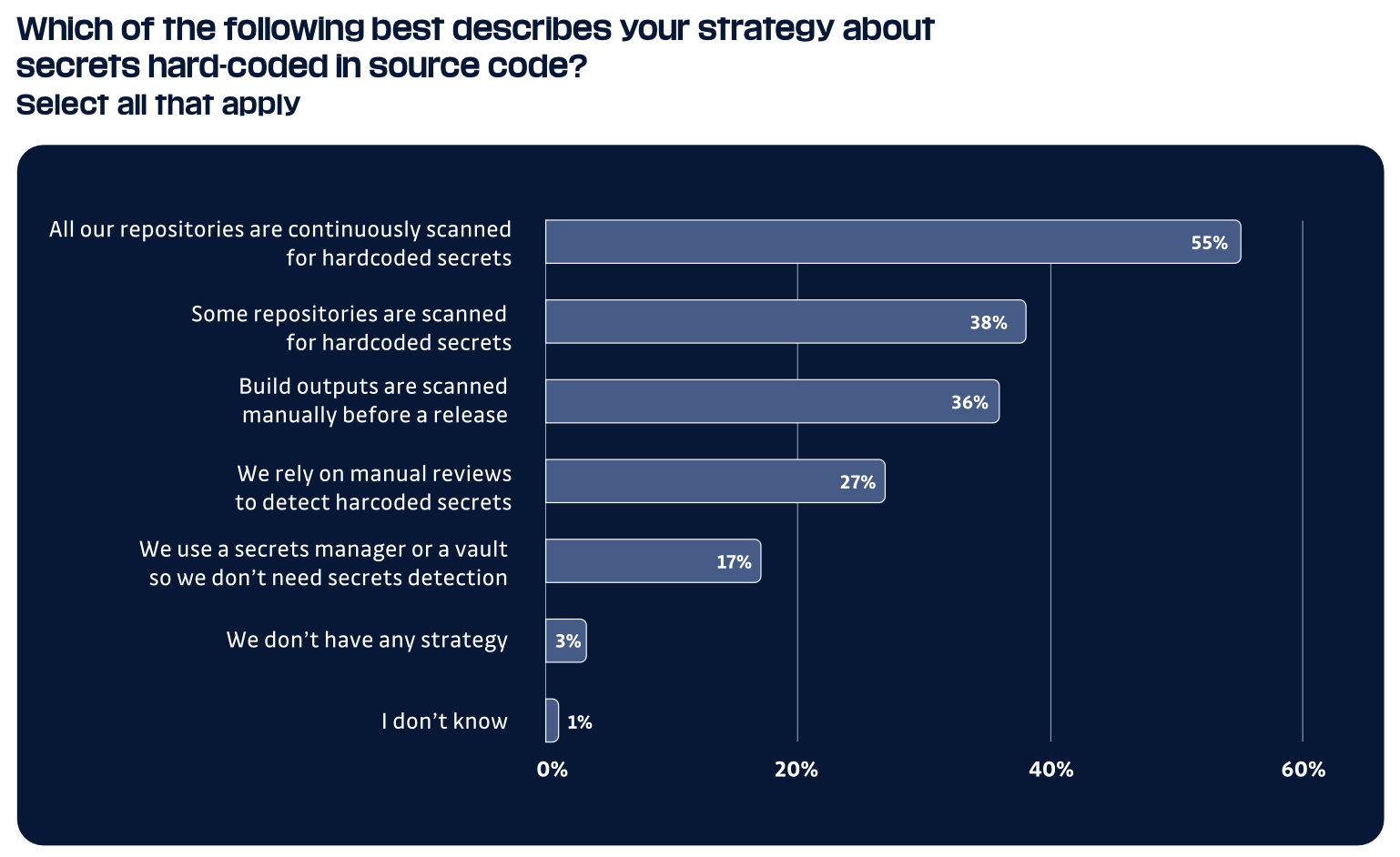
Despite this increased awareness, the study also highlights significant disparities in risk reduction strategies across the industry. For example, a concerning 27% of respondents revealed that they rely on manual code reviews, which are inefficient, to protect themselves from secret leaks.
The study emphasizes the need for organizations to adopt a more proactive approach to security, leveraging automated tools and processes to identify and remediate vulnerabilities quickly and efficiently. By automating the triage and assignment processes, organizations can accelerate their security orchestration, improve their security posture, and free up valuable resources to focus on other critical tasks.
In addition to the poll results, the study delves into the common pain points experienced by large organizations as they grapple with an accumulating backlog of vulnerabilities. In 2022, GitGuardian partnered with a large-scale enterprise to help scale its leak prevention efforts using a multifaceted approach. With 7,500 developers and over 50,000 monitored sources, this enterprise required a solution that was both robust and scalable.
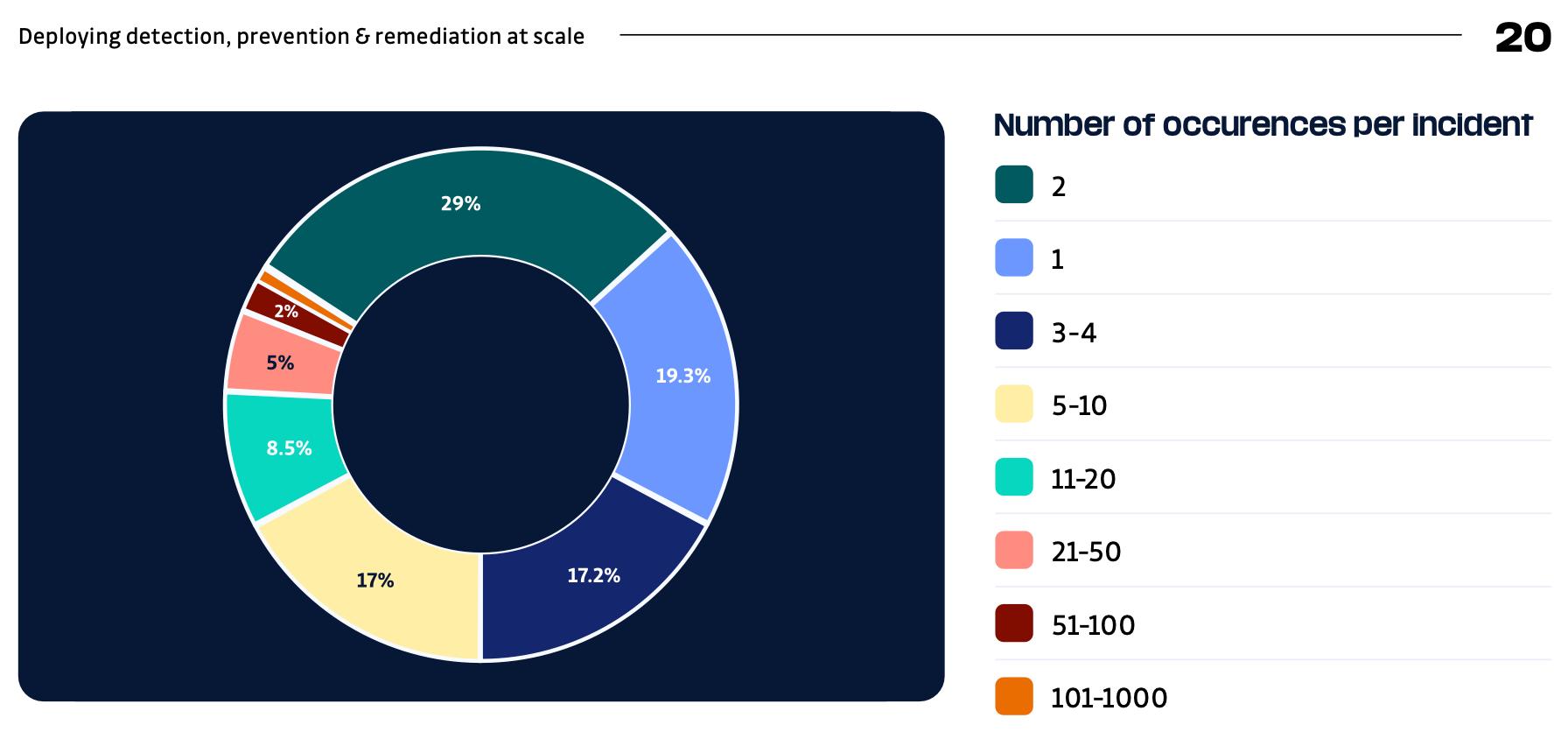
The results of this successful deployment provide valuable insights into the best way to grow an application security strategy in large enterprises.
Overall, the study highlights the importance of a holistic secrets strategy in AppSec and provides valuable insights into the best practices for reducing the risks associated with secrets sprawl. While secrets sprawl is a problem most companies experience, it's not a hard one to solve. There are tools available today that natively integrate into developer workflows for managing, orchestrating, and rotating secrets.
To learn more about the state of secrets in AppSec and how to mitigate risks in your organization, download the Voice of Practitioners study.
In addition, GitGuardian is hosting a webinar on May 25, 2023, at 5 PM CEST, discussing the results of the study with a panel of guest speakers we picked for their expertise in secrets management and developer-led security!

The webinar will provide an opportunity to learn more about the study's findings and ask questions about the best practices for reducing the risk of secrets sprawl in AppSec. Save your seat now!
*** This is a Security Bloggers Network syndicated blog from GitGuardian Blog - Automated Secrets Detection authored by Thomas Segura. Read the original post at: https://blog.gitguardian.com/voice-of-practitioners-the-state-of-secrets-in-appsec/




