Why the Global Video Game Market is a Bellwether for Other Businesses
The video game market has come a long way since Pong became a new hobby for many casual gamers around the world. Video game console unveilings and gaming title releases like Call of Duty are now cultural events with global, online gaming player populations, professional eSports teams, and subscription plans. While COVID-19 caused an increase in gaming, the game industry has shown no signs of slowing down anytime soon.
While key players like Activision, Microsoft, Nintendo, and Sony have remained constant in the games market over the years, there are seemingly new entries into the video game market each year that explode in popularity, including PC games, and mobile gaming on tablets and smartphones. The lucrative sums of money spent in the global video game market have given rise to increased cybercrime. A study of 10,000 gamers around the world found that 33% of respondents have been hacked within the past two years. As a result of these hacks, 46% of gamers stated that they lost items or currency.
Gamers losing their hard-earned digital assets aside, cyberattacks on in-game economies harm the user experience and the principle of fair play and can also cause revenue loss for organizations and game developers, among others.
Arkose Labs sought to uncover the true nature of the threats facing gamers, and the video game market as a whole, in its quarterly report. The report, Gaming Industry Threats Leveling Up: Fraud Farms and Bot Attacks Among Leading Dangers shows that these cyberattacks not only point to a growing problem within the global video game market, but can also serve as a key predictor of what’s to come in other industries as well.
Why the gaming market and gamers are being targeted by fraudsters
The gaming market itself is ripe for exploitation by financially motivated bad actors and cybercriminals. Attackers target gaming companies because they are lucrative—small monetary amounts, but with massive volume. According to a survey conducted earlier this year, the average gamer spends around $76 per month buying goods on gaming platforms, adding up to $58,000 over a lifetime. It is estimated that in 2022, more than 3 billion gamers exist around the world, which presents a large attack surface that is connected to the internet.
Additionally, internet gaming sites are often used by a younger community whose online login credentials are less likely to have been part of a data breach from other major websites. Cybercriminals seek to take control of high-value gaming accounts to gain items which they can resell in the real world, for real dollars. When an online account is taken over, the entire balance is transferred to an attacker-owned account, and the attacker cashes out. There are markets in these gaming worlds where consumers (and attackers) can convert the gaming currency into cash.
The holidays in particular present increased opportunities for fraudsters and cybercriminals looking to target student gamers that are spending more time at home on the internet playing multiplayer games. New game titles or consoles are often released into the video game market during this time as well.
Understanding three common cybersecurity threats facing the video game market
Cybercriminals and fraudsters seek to maximize profits with minimal investment and usually look for the path of least resistance when it comes to their attacks. All of this helps them to realize a greater return on investment, oftentimes this is enabled by malicious bots. Arkose Labs’ quarterly report analyzed 8 billion online sessions from the world’s biggest gaming companies across the U.S., U.K., Australia, and Singapore between November 2021 and October 2022 and found the following types of traffic:
- Basic bots
- Intelligent bots
- Fraud farms
- Legit traffic
Basic bots, intelligent bots, and fraud farms enable fraudsters to strike with credential stuffing incursions, account takeovers, man-in-the-middle (MITM) phishing attacks, and fake new account registrations.
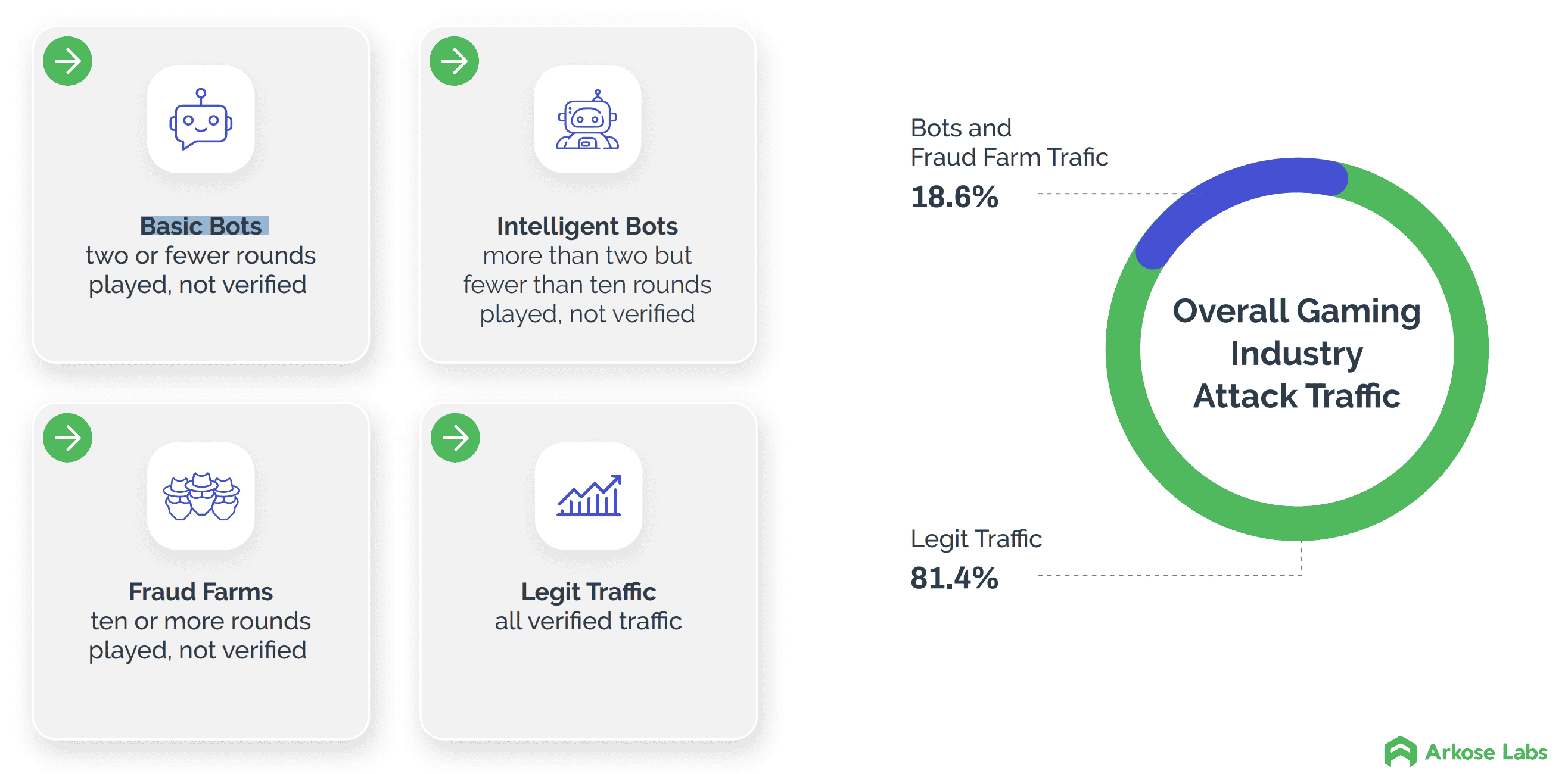
Basic bots were the most commonly used attack type followed by intelligent bots and fraud farms. Basic bots provide attackers with a highly scalable option with the volume that they need to make financial gains. Additionally, bots provide a lower barrier to entry for use as they can be purchased from online marketplaces ready for malicious purposes, including stealing and capturing login credentials, browser fingerprints, and cookies.
For additional information and data points related to these attacks, read Arkose Labs’ Q4 2022 Report Gaming Industry Threats Leveling Up: Fraud Farms and Bot Attacks Among Leading Dangers today.
Want to understand cybersecurity threats facing your industry? Look to the gaming market
Many industries work in security silos. But Brett Johnson, Arkose Labs’ Chief Criminal Officer, says banks, retail merchants, and other businesses should look to the attacks in the gaming space to predict what is coming their way. Now, we’re seeing criminals consider where they can use automated attacks (bot-based attacks) in other verticals.
“Pay attention to the gaming industry. That is the playground, the proving ground for most automated types of attacks. Because the dollar amounts are not very high on the returns, criminals are looking for automated ways to commit the types of fraud that manual humans are doing in other verticals. Once those automated ways are proven effective in that testing ground, then they’ll start deploying them in other verticals.”
While video gaming and the gaming industry also gets the headlines, as more traditional businesses enter the metaverse, even those not involved in online games, it will be critical for them to rethink their security strategies. The fraudsters of the future will operate within the metaverse, targeting tech-savvy consumers using increasingly sophisticated tactics. Attack types will shift too. Synthetic account attacks—which might typically involve a fraud attempt using a mixture of real stolen PII data and fabricated data—are more common in the metaverse.
Why Arkose Labs makes attacks more difficult and costly for fraudsters
Arkose Labs focuses on making attacks more difficult and costly for fraudsters and cybercriminals alike, dismantling their economic incentive by challenging them to clear enforcement tests at scale. To complete the attack, fraudsters must spend more time and invest in additional resources and machine learning.
We protect global video gaming companies from evolving attacks; block automated activity aimed at monetizing stolen data; and secure the in-game experience from match-fixing. Arkose Labs unique detection and mitigation platform analyzes data from user sessions to determine the context, behavior, and past reputation of every request. We classify traffic based on its risk profile and present suspicious traffic with enforcement challenges to differentiate between true users and fraudsters.
Here’s how we give businesses like yours the advantage:
- Account takeovers:We keep customers safe by eliminating large-scale attacks on user accounts.
- User-centric authentication: We make challenges easy for good users by creating gaming-inspired CAPTCHAs
- Easy implementation: We gain instant results by working to deploy rapidly.
Want to learn more about threats facing the video gaming industry and how it can apply to your business? Read Arkose Labs’ Q4 2022 Report: Gaming Industry Threats Leveling Up: Fraud Farms and Bot Attacks Among Leading Dangers.
For more information on how Arkose Labs can help your organization beat malicious bot activity, including credential testing, credential stuffing, and account enumeration attacks, book a demo with us today.
*** This is a Security Bloggers Network syndicated blog from Arkose Labs authored by Steve James. Read the original post at: https://www.arkoselabs.com/blog/why-gaming-market-is-the-bellwether-for-other-businesses/



