Bots Breaking Bad: Stolen Pharmacy Accounts Up for Sale
By Kasada Threat Research Team
Using Bots to Steal Pharmacy Accounts and Resell Prescriptions
For the first time, Kasada threat intelligence observed the use of credential stuffing to attack pharmacies, steal customer accounts, and exploit the distribution of prescribed medications. Accounts stolen by bots provide access to active prescriptions, which are then resold illegally on a secondary marketplace for profit.
This activity is both illegal and dangerous. It puts medications in the hands of people who don’t have a prescription from a doctor and enables substance abuse. It also takes prescribed medications away from the people who need them legitimately.
The Evolution of Bots: From Sneakers to Pharmacies
It’s been well publicized that scalper bots “skip the digital line” and purchase in-demand items such as sneakers, gaming consoles, and NFTs. More recently, people have realized that the same bots can be repurposed to score any item or service wherever demand outpaces supply, such as baby formula, semiconductor chips, and even COVID-19 vaccine appointments.
Malicious bots facilitate billions of dollars in online fraud, in part by automating login processes to test stolen user credentials and perform account takeover (ATO). Stolen accounts obtained from credential stuffing attacks are exploited by making fraudulent transactions and depleting stored value. Using bots to commit ATO has been pervasive for a long time in industries such as Retail, Media & Entertainment, and Financial Services.
With regards to pharmacies, we’ve also seen scalper bots jump ahead of others to book services, such as COVID-19 vaccine appointments. Now what’s come to light is a new trend of pharmacy accounts being stolen with bots in order to purchase and resell controlled substances. We observed the first instance of this in the beginning of April 2022.
Real World Evidence – Tens of Thousands of Stolen Accounts, 5x Increase
Kasada researchers have discovered tens of thousands of stolen online pharmacy accounts that are now available for sale on secondary marketplaces. The trend is accelerating – over the past 60 days, the number of stolen accounts we’ve observed available for sale has increased by 5x.
As seen below, the sellers offer access to legitimate prescriptions for controlled and highly addictive substances, such as Adderall and Oxycodone. The price for a stolen account ranges from what one would normally pay with an insurance co-payment to several hundred dollars. The marketplaces offer stolen accounts from physical and online-only pharmacies, many of which are from the top 10 U.S. pharmacies. The pharmacy names and sellers have been intentionally redacted. Based on the overall rating, buyers of these stolen accounts rate their transactions positively.
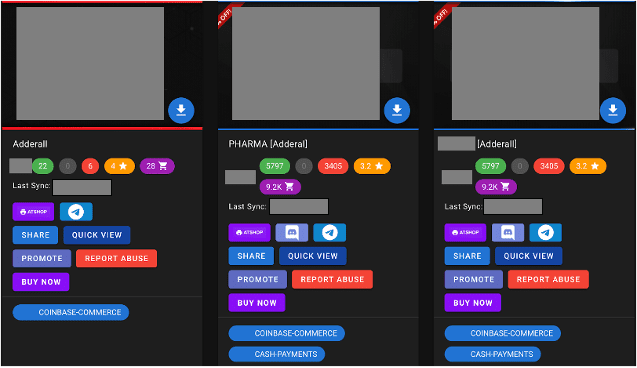
Example: Stolen Accounts for Adderall
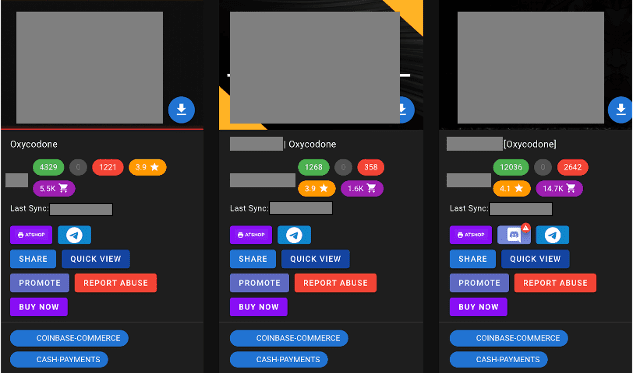
Example: Stolen Accounts for Oxycodone
How Fraudsters Commit Account Takeovers (ATO) to Sell Stolen Prescriptions
- Credential Stuffing to Conduct ATO Attacks – Automated account cracking tools, including OpenBullet2, are loaded with bots and configurations similar to those used for scalping. These tools perform a credential stuffing attack on a pharmacy’s website or mobile app. By stuffing stolen usernames and passwords, the attacker can exploit the fact that consumers reuse the same credentials on different websites. A small percentage of the stolen credentials “work” and allow the attacker to successfully takeover accounts (performing ATO) with legitimate login credentials.
- Data Extraction – Once an account is taken over, the attacker automates the process of extracting the prescriptions and other information associated with the account. Data linked to the account includes customer information, such as name, birth date, phone number, and the payment source on file.
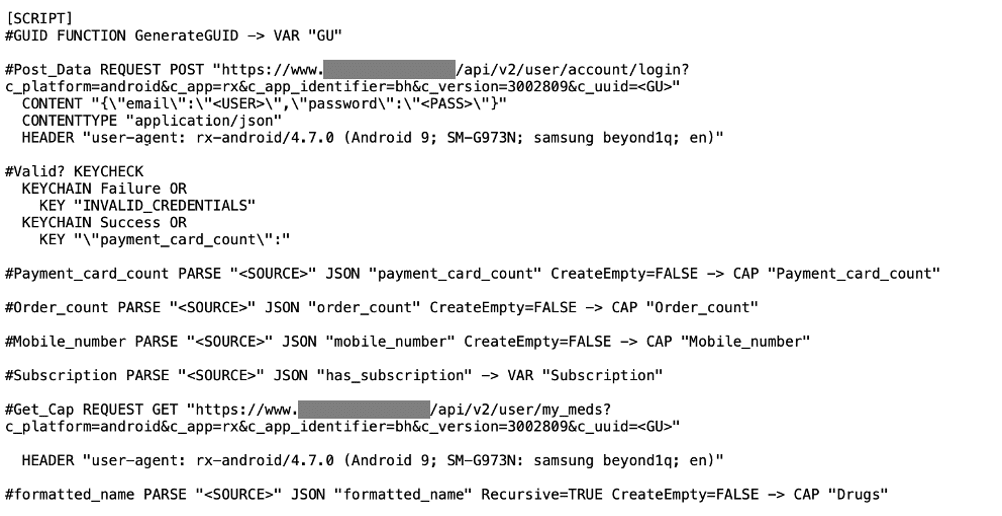
A simple script used to automate the extraction of personally identifiable information and prescription data from cracked pharmacy accounts, using POST/GET requests and parsing of JSON objects.
- Storefront Integration – The extracted information is integrated with eCommerce marketplaces that can be found across the corners of the Internet. It’s notable that these acts of online fraud aren’t restricted to the dark web, but are on the Internet for anyone to find. Stolen accounts are put up for sale using a non-identifiable seller profile. Shoppers can choose the pharmacy and medication of their choice, accepting a range of payment methods, including cash transfer and crypto. The sellers typically offer a guarantee such that if the account doesn’t work, they will provide a new account at the same pharmacy at no additional charge.
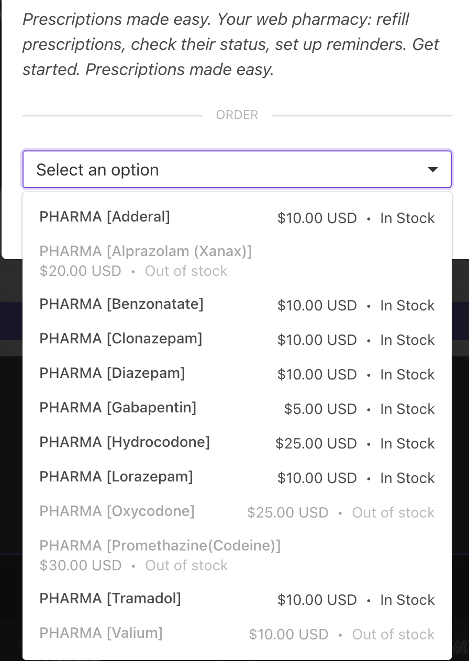
These online marketplaces offer a range of stolen accounts to provide access to a variety of addictive and controlled substances. In addition to painkillers and amphetamines, other medications, including cough suppressants, anti-seizure, anti-anxiety are readily available for purchase.
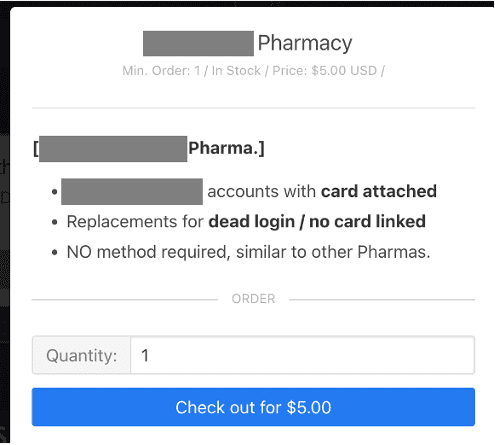
Purchases of stolen accounts come with a guarantee. If the login or card on file doesn’t work, the provider will replace it with a new account.
- Using a Stolen Pharmacy Account – Once an account is purchased on the secondary market, the purchaser is free to use the account to obtain the medication at the specified pharmacy. This can be done using online ordering (use the credit card associated with the account and reroute the shipping address). Alternatively, the purchaser can visit a pharmacy to pick up the prescription using the information lifted from within the account to pass authorization checks, such as birthdate. What’s done with these pharmaceuticals after purchasing? Likely a combination of two activities that create a dangerous – and difficult to trace – impact on our society. The purchaser can consume them, or resell them for a premium, furthering the underground economy for stolen pharmaceuticals and widening the access of controlled substances to those who shouldn’t be taking them.
Where There’s a Will There’s a Way… What to Expect Next
This is one of the most egregious and dangerous uses of bots we’ve ever observed.
It’s easy to see how the illegal sale of stolen pharmacy accounts can be a profitable venture. Not to mention very dangerous – by enabling medications to be put into the hands of people who don’t have a prescription.
With free, open source tools widely available to automatically crack accounts, a bot operator can monetize this illegal activity with very little effort. Based on the volume of marketplace transactions we’ve observed within the past 30 days, we estimate a single operator can make in excess of $25,000 per month selling stolen pharmacy accounts.
Currently, the bots which use pre-built configurations leveraging residential proxy networks to crack accounts aren’t nearly as sophisticated as what Kasada has seen in other industries like Retail and Financial Services. But as more light is shed on the problem and more security defenses are put in place, we expect the bot sophistication will inevitably rise and continue conducting these illegal, profitable operations.
Most recently, Kasada has been observing the use of solver services within OpenBullet2 configurations. This allows attackers to commit ATO by tricking most of the “leading” anti-bot detection systems by presenting valid tokens (not Kasada). It’s plausible the same will be done in the future to successfully crack online pharmacy accounts if current methods stop working well.
The Latest Threat Intelligence on Automated Threats, Credential Stuffing, and ATOs
Request a threat intelligence briefing personalized to your business. You will learn the latest methods being used to conduct and combat automated fraud along with specific threat intel on your organization. We’re here to help.
*** This is a Security Bloggers Network syndicated blog from Kasada authored by Kasada. Read the original post at: https://www.kasada.io/bots-breaking-bad-stolen-accounts-pharmacy/



