Home » Security Bloggers Network » IronNet’s December Threat Intelligence Brief
IronNet’s December Threat Intelligence Brief
As we look back on November, we have much to report on, such as an FBI email hoax, where attackers abused insecure code in the Law Enforcement Enterprise Portal (LEEP) to send thousands of illicit emails about fake cyberattacks using the federal agency’s email address (eims@ic[.]fbi[.]gov). Additionally, the Digital Forensics and Incident Response (DFIR) reported on the continued exploitation of the Proxyshell vulnerabilities on the Microsoft Exchange servers.
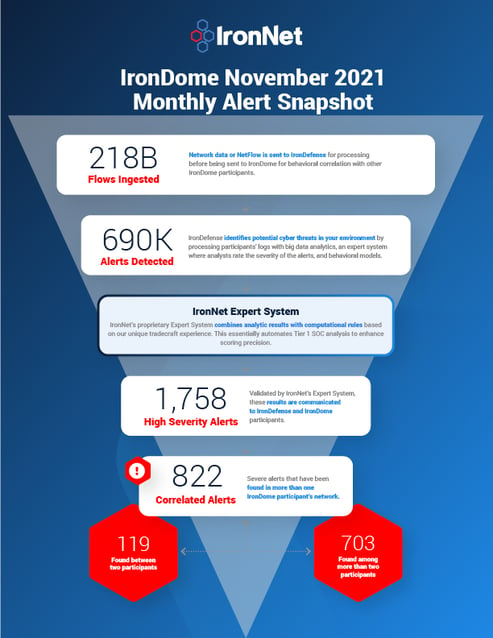
At IronNet, we look to behavioral analytics to detect such unknown threats on enterprise networks before adversaries succeed at their end-game: exploitation or exfiltration. When it comes to ransomware attacks and other types of attack campaigns, early detection is critical. First, we do the threat detection groundwork needed to spot abnormal network activity across our customers’ networks. Second, our IronDefense NDR expert system scores these alerts, prioritizing the most interesting events to help cut down on alert fatigue. Finally, we take a Collective Defense approach to crowdsourced threat sharing in real time.
The December IronNet Threat Intelligence Brief
This ability to analyze and correlate seemingly unrelated instances is critical for identifying sophisticated attackers who leverage varying infrastructures to hide their activity from existing cyber defenses. As reported in the December Threat Intelligence Brief, our analysts review alerts from millions of data flows that are ingested and processed with big data analytics. We apply ratings to the alerts (benign/suspicious/malicious) and immediately share them with IronDome Collective Defense participants.
Here is a snapshot of what we discovered across the IronDome communities in November, showing 822 correlated alerts across IronDome participant environments:
Given the unique cross-sector visibility and Collective Defense capabilities of IronDome, we are able to highlight the most frequent behaviors each month, in turn enabling us to track trends over time. For November, the most frequent behavior analytics were External Scanning (2911), DNS Tunneling (672), and C2 Rendevous (DGA) (299).
Analysis of IOCs
In addition to correlated alerts, significant IronDome community findings revealed 541 Indicators of Compromise (IoC) that may pose risk to IronDome participant environments. For example, we analyzed the malicious domain linethesebrother[.]top, one of nearly 2,000 malicious domains flagged as phishing by multiple vendors.
All the IoCs we analyzed are used to trigger alerts that are mapped to the Cyber Kill Chain to identify the stage and progression of the threat. They can be used to create detection rules for network, endpoint, or other security tools currently deployed to mitigate cyber risk in each IronDome participant’s environment.
See the December Threat Intelligence Brief for the full list of recent IoCs.
The bigger picture of Collective Defense
Every month, IronNet’s expert threat analysts create threat intelligence rules (TIRs) based on significant community findings from IronDome, malware analysis, threat research, or other methods to ensure timely detection of malicious behavior targeting an enterprise or other IronDome community participants.
In November, we created 11,674 threat intel rules of our 286,789 created to date. Some examples of this month’s research related to indicators associated with malware delivery domains for Gafgyt, AgentTesla, Woreflint, and Dridex malware, as well as IoCs surrounding the state-sponsored North Korean TA406 threat group.
This combination of behavior-driven and IoC signature-based detection, alert ranking, and sharing ensures IronDome participants have the broadest view of threats facing their enterprise.
FBI email hoax
As I mentioned, the FBI was the victim of a recent email hoax. Threat actors abused insecure code in LEEP, an online portal that state and local law enforcement use to register and set up accounts. Once a confirmation code was generated, the threat actor, identified as “pompompurin,” could edit the POST request and change the subject and text parameters of the email before sending the hoax to thousands of email addresses. The main motivation of this campaign was to discredit Vinny Troia, the founder of the dark web intelligence companies Shadowbyte and NightLion. No personally identifiable information (PII) or data was compromised.
You can see the latest industry news in the full brief or check out IronNet’s threat intelligence web page.
*** This is a Security Bloggers Network syndicated blog from IronNet Blog authored by Anthony Grenga. Read the original post at: https://www.ironnet.com/blog/december-ironnet-threat-intelligence-brief

.jpeg?width=185&name=Blank%20Print%20Document%20(1).jpeg)