CWE-77
Improper Neutralization of Special Elements used in a Command (‘Command Injection’)
CWE-77 refers to command injection, a vulnerability that allows malicious parties to control parts of the application by providing input that influences how the application behaves. In short, the attacker could control how the app behaves, compromising the app itself and potentially its data as well.
Why command injection vulnerabilities are problematic
Command injection vulnerabilities allow attackers to perform actions they would otherwise not be able to perform. This potentially allows them to modify the behavior of the application, as well as gain access to sensitive data.
Variations, such as command-line injections or operating system (OS) injections, are commonly found, but there are additional ways that command injections can occur as well.
How command injection attacks occur
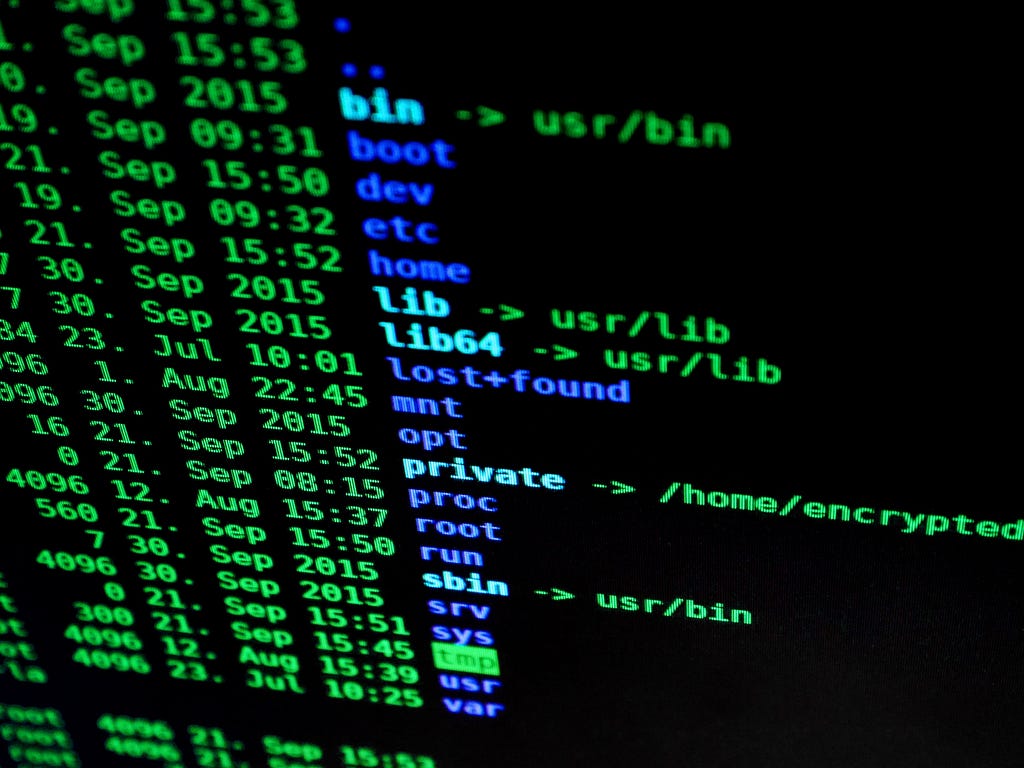
Command injection attacks occur when user-provided input is accepted and used as part of a command executed by the application. For example, the user input might be used to find a file. The input is appended to a command that looks for a file and returns the content to the user. Without proper sanitization, users could modify this behavior (e.g., append a command to delete the folder contents).
This ability offers a malicious party the means to do something they would not otherwise be able to (either because they lack the proper authorization or ability to do so directly). Furthermore, the way that the programming language is structured may allow attackers to string together and execute multiple commands, all at once.
Mitigating command injection vulnerabilities
Any instance where user input is accepted and used without proper sanitization could lead to a command injection vulnerability. As such, sanitization and allowlisting are simple strategies that can help.
However, it can be difficult to allowlist the accepted values properly; the best mitigation strategies include using libraries to implement the desired functionality. Additionally, limiting the scope of the command (e.g., set permissions so that users cannot access/modify/open privileged files) can help.
TL;DR
Command injections are a general class of vulnerabilities primarily arising due to unsanitized user input that’s then used in a command executed by the application. Sanitization of user input, allowlist, implementing functions with libraries, and securing privileged files are all methods of mitigating the risk of command injections.
CWE-77 was originally published in ShiftLeft Blog on Medium, where people are continuing the conversation by highlighting and responding to this story.
*** This is a Security Bloggers Network syndicated blog from ShiftLeft Blog - Medium authored by Katie Horne. Read the original post at: https://blog.shiftleft.io/cwe-77-bf222588a521?source=rss----86a4f941c7da---4




