Over the past year, COVID-19 fundamentally transformed how people live and work, how companies interact with customers, how customers shop and buy, and how physical and digital supply chains function. As the economic importance of digital innovation accelerated during the global pandemic, so too did the number of cyber-attacks aimed at exploiting software supply chains.
And yet, much has stayed the same. Top performing companies like Apple, Goldman Sachs, and Amazon — and more recently, Zoom, Peloton, and Wayfair have mastered three key competitive advantages: knowing how to use open source and third-party innovation at scale, integrating security and risk controls into multiple phases of the software supply chain, and releasing higher quality code faster than their competitors.
After a year of research that involved studying 100,000 production applications and 4,000,000 component migrations made by developers and operational supply, demand and security trends associated with the Java (Maven Central), JavaScript (npmjs), Python (PyPI), and .Net (nuget) ecosystems, we’re excited to share the 2021 State of the Software Supply Chain report.
Here’s what we learned this year:
Open Source Supply, Demand, and Security Vulnerabilities have all Exploded:
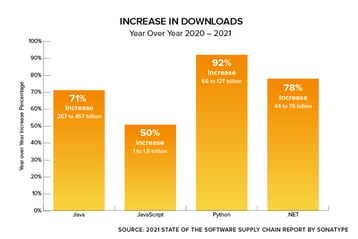
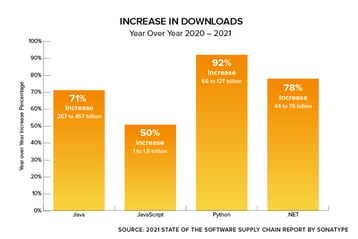
- Supply increased 20%. The top four open source ecosystems now contain a combined 37,451,682 different versions of components.
- Demand increased 73%. In 2021 developers around the world will download more than 2.2 trillion open source packages from the top four ecosystems.
- Open Source attacks increased 650%. In 2021 the world witnessed an exponential increase in software supply chain attacks aimed at exploiting weaknesses in upstream open source ecosystems.
- Production apps utilize only 6% of available open source projects. Despite a huge available supply of open source projects, utilization is concentrated in a surprisingly small number of popular projects.
- Popular open source projects are more vulnerable. 29% of popular (Read more...)