Russian Spear Phishing Campaign Hits Ukraine
Ukrainian cyber security agencies have warned that their government and private organizations are being targeted by a massive spear phishing campaign launched by Russian threat actors.
The Ukrainian secret service has called this the work of ‘special services of Russian Federation’. It is noteworthy that this is the third cyber attack coming from the Russian side to target Ukrainian organizations this year.
Take a Moment to Stay Tuned Forever
Subscribe to get weekly cyber security updates!
The Sequence of the Attack
It is believed that the spear phishing campaign started in early June. Alerts were released by the Ukrainian Secret Service, Ukrainian Cyber Police, and CERT Ukraine regarding the same.
The attackers impersonated the Kyiv Patrol Police Department. They have sent out fraudulent emails that warn the recipients of their failure to pay taxes.
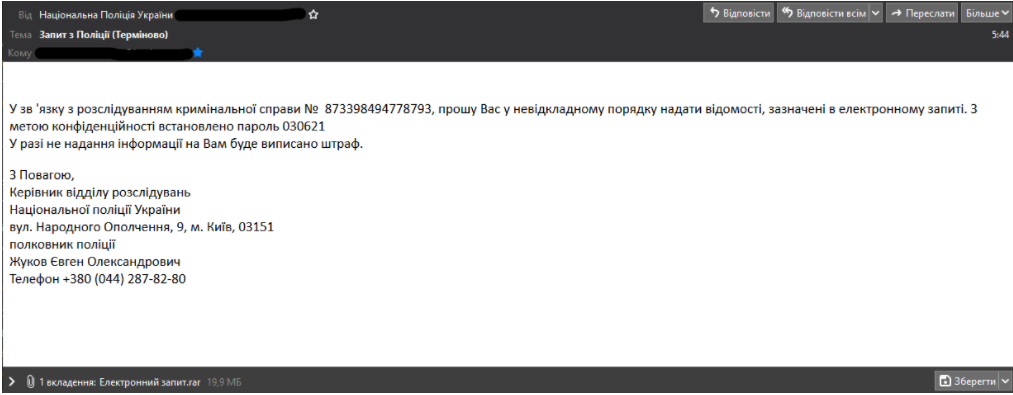
The people who received the emails reported that they were urged to download a RAR archive (included in the email). On decompression, this drops a fake pdf file, which in reality is a double extension EXE file (filename.pdf.exe).
Victims unknowingly installed a modified version of a remote access software named RemoteUtilities that would ping back to remote command and control servers present in Russia, Germany, and the Netherlands.
CERT officials have said that these attacks used tactics similar to those used in the attacks carried out in January and March.
Ever since tensions boiled after changes in the geopolitical situation of Russia and Ukraine in 2014, Ukraine has been a target of many cyber attacks. Moreover, they have attributed many of these attacks to the Kremlin.
Turn Your Employees Into A Cyber Threat Shield
Make your employees proactive against prevailing cyber attacks with ThreatCop!
The post Russian Spear Phishing Campaign Hits Ukraine appeared first on Kratikal Blogs.
*** This is a Security Bloggers Network syndicated blog from Kratikal Blogs authored by Rishi Khemani. Read the original post at: https://www.kratikal.com/blog/russian-spear-phishing-campaign-hits-ukraine/





