How to use Acunetix software composition analysis
Software composition analysis (SCA) is an important part of application security testing. Today’s web applications deliver rich functionality through the use of multiple open-source components. Like all software, open-source components are subject to vulnerabilities, and each component will have a development path typically tracked with version numbers. SCA is the process of analyzing an application’s source code to identify open-source components and their version numbers, and comparing this list with a master database that contains known components with version numbers and vulnerability exposures.
Scanning a target with SCA functionality
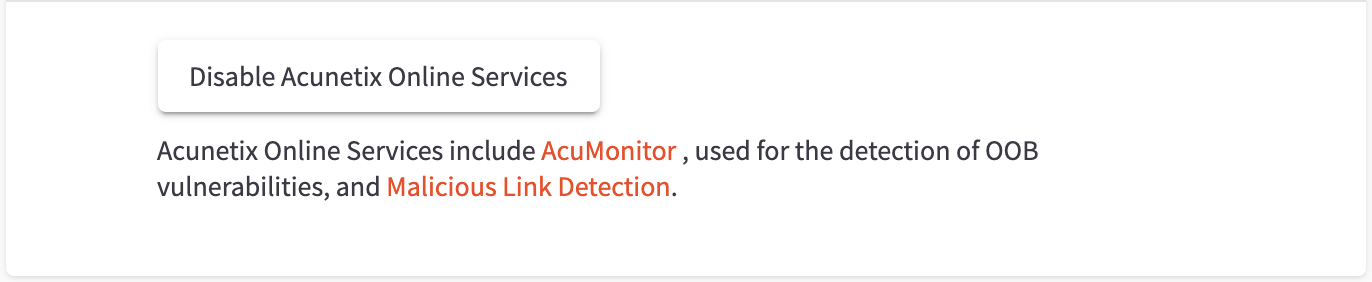
Acunetix provides an SCA server with a master database of open-source components as part of Acunetix Online Services. You must ensure that Acunetix Online Services are enabled for your Acunetix installation before SCA analysis can occur; go to your profile page to check this:
You also need to have the AcuSensor agent installed on your server. When an application is scanned with Acunetix, the AcuSensor agent deployed to the application will analyze the application, create an inventory of components being used, and submit the inventory to the SCA server for comparison. The SCA server will then respond to Acunetix if it finds any components with known vulnerabilities.
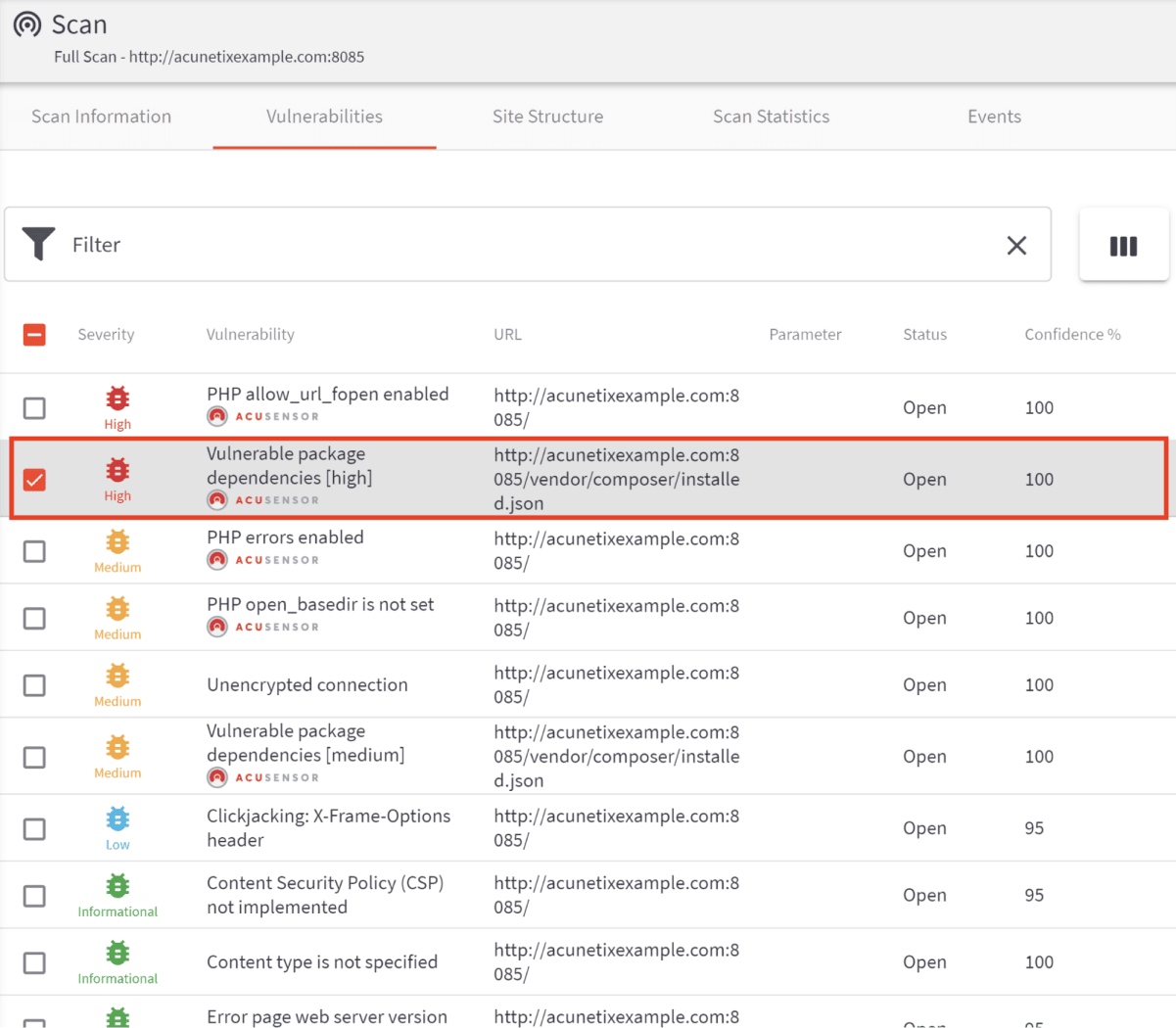
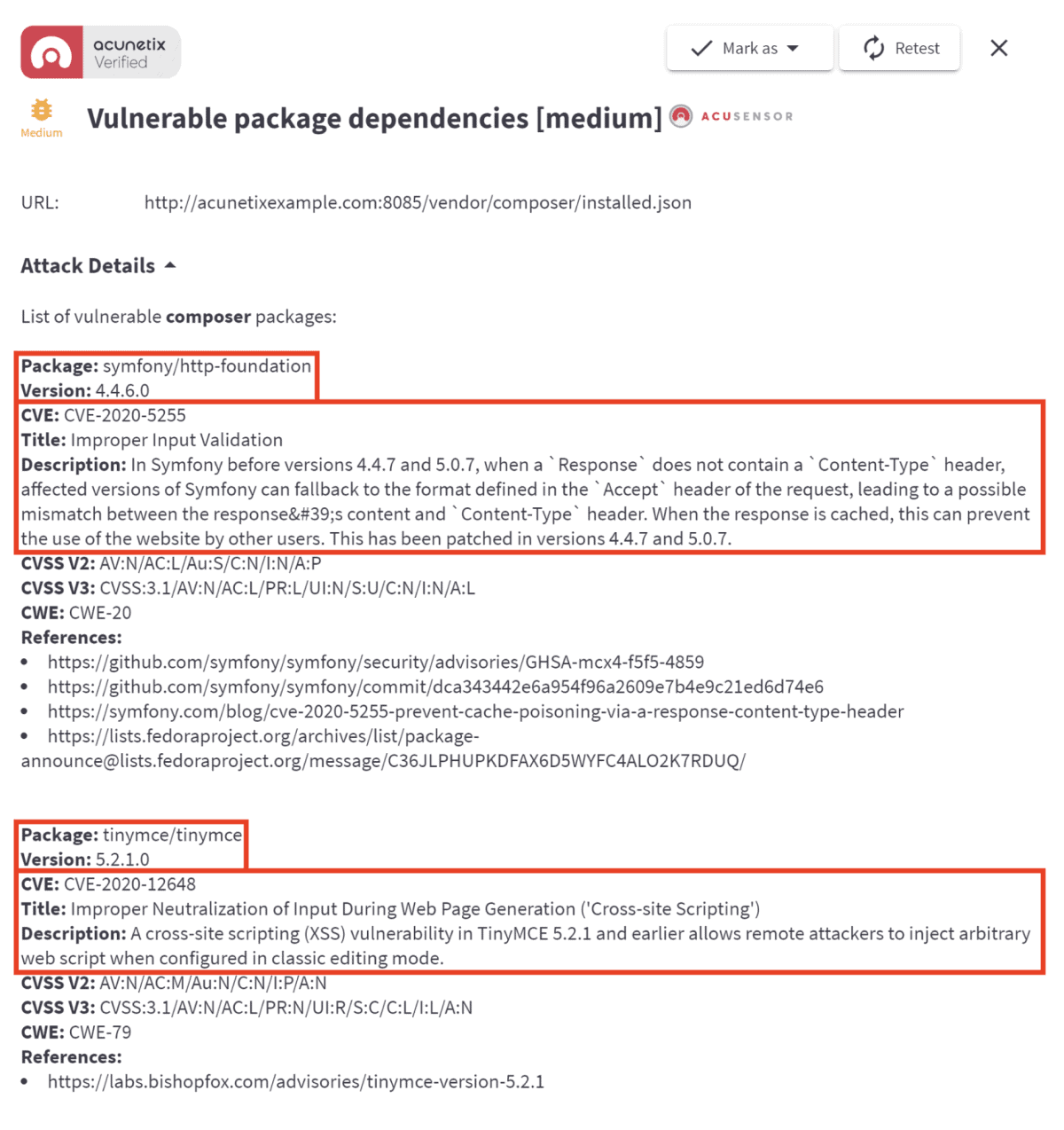
When reviewing the scan results, you can see that the SCA functionality has discovered vulnerable packages being used:
You can also expand the discovered vulnerability to get a detailed description of the vulnerable package:
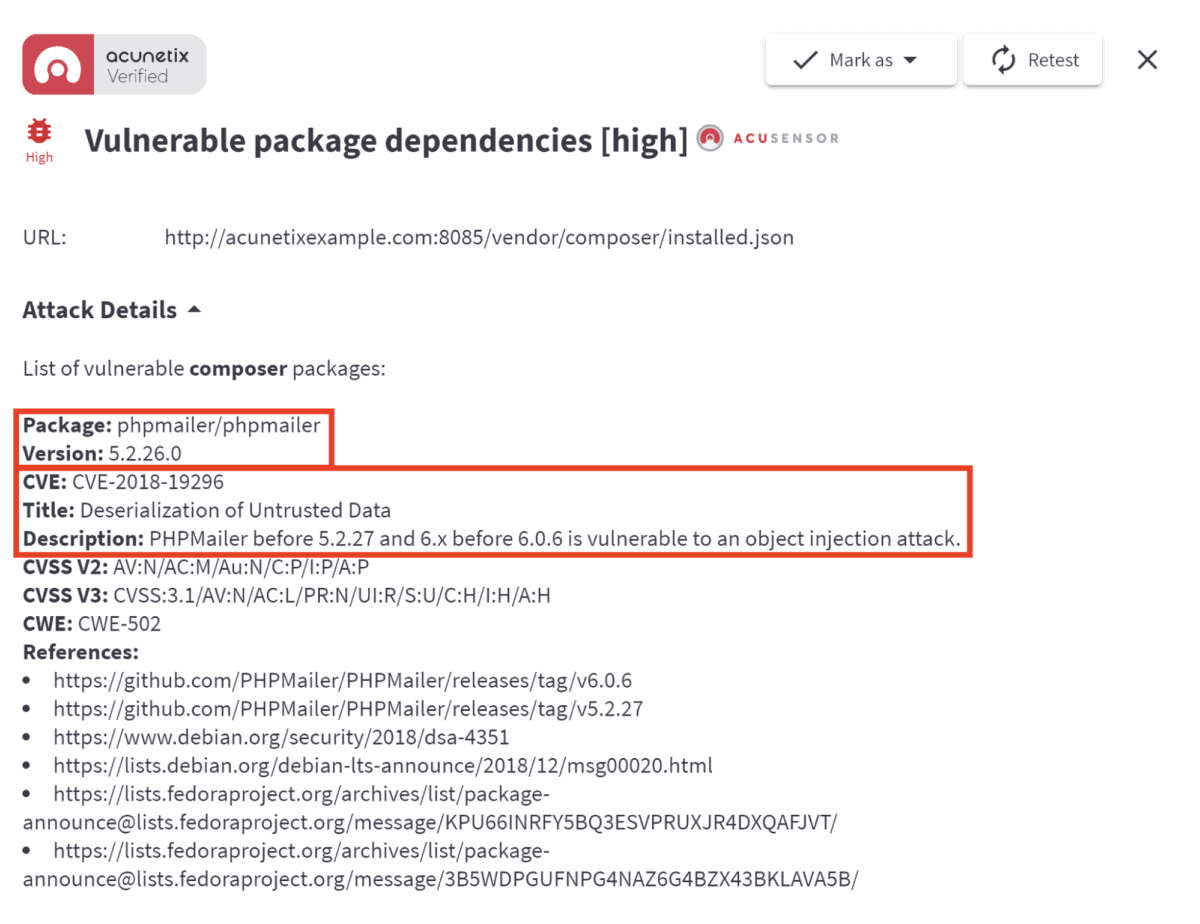
If multiple vulnerable packages of the same severity level are found, the detailed description will be shown for each vulnerable package:
Remediation hints
The detailed description gives us valuable pointers for eventual remediation. In the first example quoted above, the version reads:
Version: 5.2.26.0
and the description reads:
Description: PHPMailer before 5.2.27 and 6.x before 6.0.6 is vulnerable to an object injection attack.
This clearly indicates which version numbers of the open-source component in question are vulnerable, as well as the specific version number found in your web application. You can therefore use a version of the component that has resolved the vulnerability. In this case, you would most likely be best served by upgrading the PHPMailer component to at least version 6.0.6 (or version 5.2.27 if you require some legacy functionality of behavior that is not present in version 6.0.6).
Stay secure
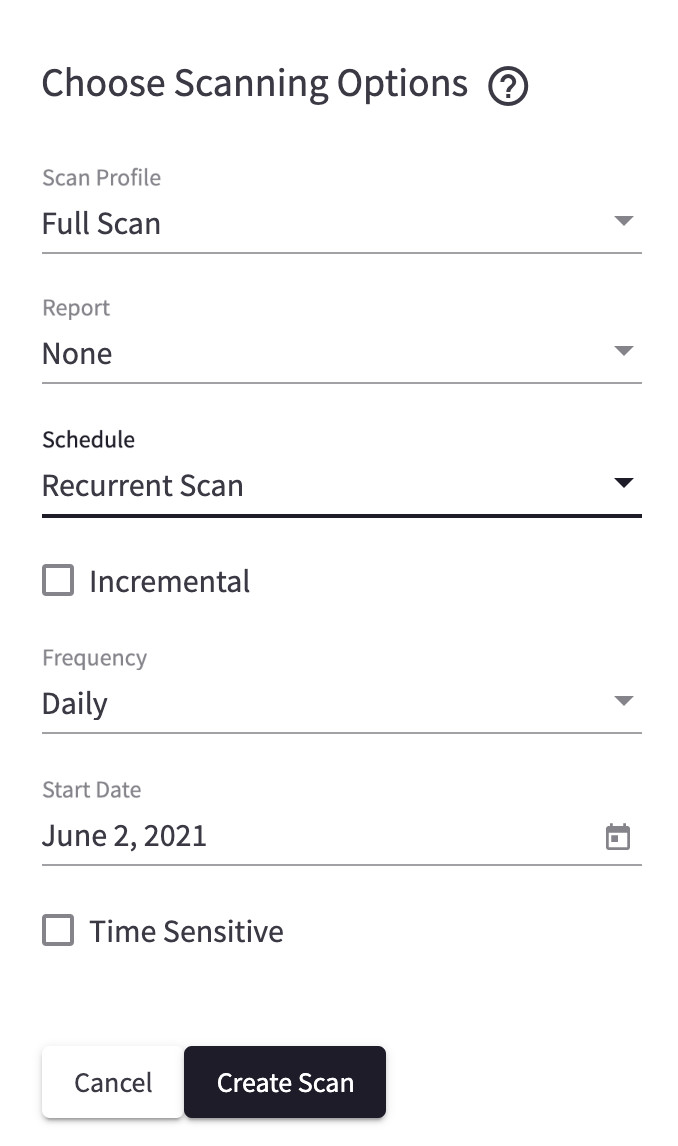
Keep in mind that performing a one-time scan on your target is not sufficient, even if your web application is in code freeze. As time goes by, new vulnerabilities are discovered, resulting in the need to remain vigilant.
Vulnerability scanning should be an integral part of your SDLC (software development life cycle).
One simple way to help you to keep your web applications safe is to set up a recurrent scan. Any vulnerabilities discovered during any of the scheduled scans will be reported via email for you to take action and remediate.
Get the latest content on web security
in your inbox each week.
*** This is a Security Bloggers Network syndicated blog from Web Security Blog – Acunetix authored by Kevin Attard Compagno. Read the original post at: http://feedproxy.google.com/~r/acunetixwebapplicationsecurityblog/~3/nwvUP1Y8S4M/





