When Organizations Take a Risk-First Approach to IT Compliance, They’re Better at Avoiding Security Incidents
Cybersecurity and IT risk management professionals know that staying on top of security is a constant battle. Cyber attackers evolve their methods at a frenetic pace, there are more stringent data privacy regulations in place than ever before, and today’s technology buyers are highly sensitized to the fact that their software vendors and service providers’ security flaws can leave their valuable data exposed. When organizations fail to implement effective IT risk management measures, they often pay a dear price.
According to Hyperproof’s 2021 IT Compliance Benchmark survey — completed by 1,029 IT compliance professionals in December 2020, 61 percent of all surveyed tech companies have experienced a data breach or a privacy violation within the past three years. The average loss from a single incident was $5.96 million. When organizations experience an incident, the loss doesn’t just come from the monetary penalty they incur for non-compliance. There are a variety of costs, including: Operational costs, such as lost sales; higher operating costs; investigations and litigation costs; reputational damage; and lost customer loyalty.
Although the majority of surveyed organizations suffered some losses from data breaches and compliance violations, there was a small group of outliers that didn’t experience any. In fact, organizations that took an integrated approach to IT risk management (and made effort to tie their risk and compliance activities together) did a much better job of avoiding security lapses than organizations that view their compliance function as the function that enforces rules and regulations (and conducted risk management and compliance activities in silos). Additionally, the group that made an effort to align their risk management and compliance activities were able to meet their IT compliance obligations more efficiently — by saving time on administrative work — than the group that viewed their compliance function and risk management function as two disparate functions.
Below, we’ll take a close look at how these outlier organizations in our study achieved superior IT risk management outcomes.
Two Distinct Approaches to IT Compliance
For years, industry analyst firms like Gartner and various GRC advisory firms have championed the value of taking an integrated approach to managing IT risks (also known as “risk-first” approach). This represents a departure from the “compliance-first” or “audit-first” approach (still quite pervasive today), where an organization opts to define its security policies and internal controls based on what they have to do to fulfill regulatory requirements.
The main criticism of the compliance-first approach is that organizations often get a false sense of security once they’ve met regulatory requirements (e.g. gotten a SOC 2 report). And they end up spending more time and money than they need to, because they unintentionally complete the same activities multiple times when they try to meet compliance objectives and mitigate risks.
The premise of taking an integrated approach is that each organization focuses on its unique set of risks first; addressing compliance requirements becomes just a portion of a holistic risk management approach. The risk management process starts with a risk assessment. An organization then creates security policies and internal controls tailored to the results of their risk assessments. Then, controls are mapped to “standard” controls in IT compliance frameworks to minimize duplicative efforts. The compliance program’s focus is about ensuring that keys controls are functioning effectively and as designed—not simply ticking off boxes outlined in regulations.

In our 2021 IT Compliance Benchmark survey, we asked respondents what they see as the purpose of their compliance function — is compliance a separate function or a part of a holistic risk management program? We wanted to see whether companies that take a holistic approach experience superior business outcomes compared to those that view their compliance function solely as the function that enforces adherence to rules and regulations. For example, do organizations that take an integrated approach experience compliance lapses at a lower rate?
To find out, we asked respondents this question: Which statement best reflects how your organization views the purpose of the compliance function? Select one.
- My organization views compliance as the function that enforces regulations/industry standards
- We believe that having a solid compliance program helps us mitigate risks; but risk management and compliance activities are typically conducted separately, in response to separate events
- My organization has an integrated view on how to manage our unique set of risks—our risk and compliance activities are tied together and aligned
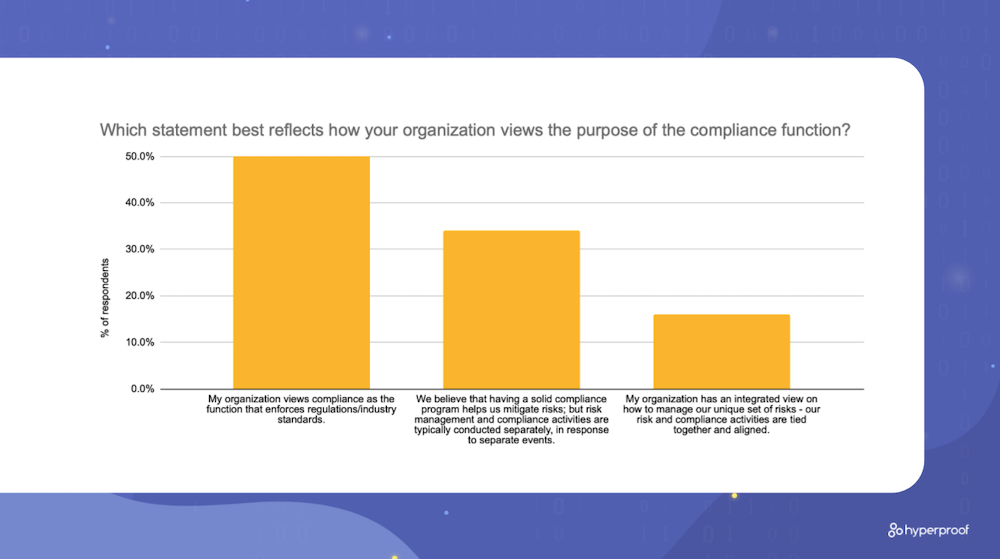
We found that half of all respondents’ organizations view compliance as the function that enforces regulations and industry standards. Over a third of respondents (34%) believe that having a solid compliance program helps them mitigate risks, but day-to-day risk management and compliance activities are typically conducted separately in response to separate events. Only 16% of all respondents take an integrated approach and have aligned their risk and compliance activities. These organizations that take an integrated view tend to embed risk responsibilities into compliance personnels’ jobs.
Study Results

In this survey, we asked respondents whether their organization has experienced a compliance lapse such as a privacy violation or a data breach in the past 3 years. As a group, organizations who take an integrated approach do a much better job at avoiding compliance lapses (e.g., privacy violation, data breach) than 1) those who believe the compliance function’s purpose is to enforce rules and 2) those who believe that compliance program helps with risk mitigation but conduct risk and compliance activities in silos. The differences we found are statistically significant.
While 61% of survey respondents overall reported their organization has experienced a compliance violation in the last three years, only 40% of those who take an integrated view of risk management and compliance activities experienced a compliance violation. On the other hand, 71% of all respondents who view the compliance function as the enforcer of rules have experienced a compliance violation in the past 3 years. Of those who believe that compliance programs help mitigate risk but still manage activities in silos, 58% reported a compliance violation.

Additionally, we found that organizations that manage IT risks in an integrated approach spend less time on administrative activities compared to organizations that view compliance as a policing function.
The average organization that takes an integrated view spent 39% of their total time on administrative tasks, while the average organization that viewed compliance as the policing function spent 50% of their total time on administrative tasks!
This finding led us to ask: How do these organizations save time and get their work done more efficiently? What do they do differently from those who view the compliance function as the enforcer or rules?
The Differentiated Practices of Integrated Organizations

What we found is that organizations that manage IT risks in an integrated approach focus on a set of practices that 1) help them understand their current security posture and identify gaps and 2) get work done more efficiently than the rest.
1. Integrated organizations have a more accurate view of their existing risks and how well these risks are being managed in the present.
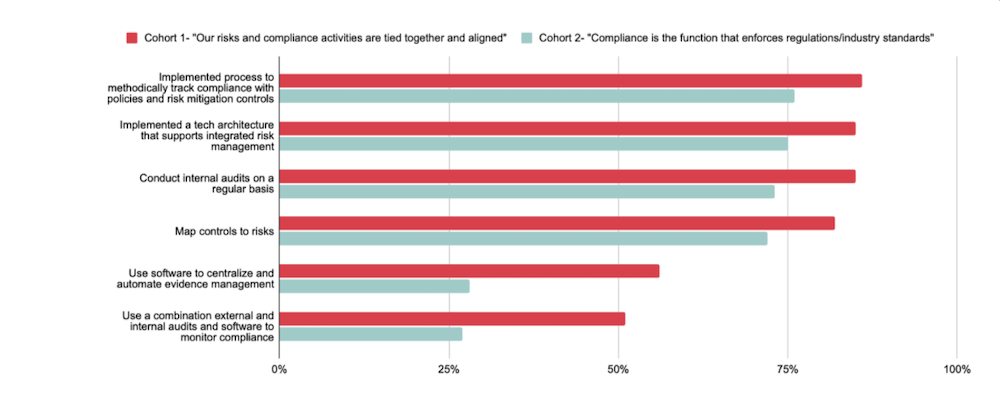
Integrated organizations adopted the following practices at greater rates compared to organizations who view the compliance function as the function that enforces the rules. These differences are statistically significant.
- They map controls to risks: 82% of respondents from integrated organizations have mapped internal controls to the risks they’re meant to mitigate, vs. 72% of those who view compliance as a policing function.
- They conduct internal audits: 85% of respondents from integrated organizations conduct internal audits on a regular basis, vs. 73% of respondents who view compliance as a policing function.
- They use multiple methods to monitor controls and gauge controls effectiveness (including external audits, internal audits and software) at nearly twice the rate of those who view compliance as a policing function (51% vs. 27%).
- They embrace process: 86% of respondents from integrated organizations have implemented processes to methodically track compliance with policies and risk mitigation controls, compared to 76% of respondents who view compliance as a policing function.
2. Integrated organizations are better at using technology to gain efficiencies in their IT risk management workflows
Integrated organizations adopted the following practices at greater rates compared to organizations who view the compliance function as the function that enforces the rules. These differences are statistically significant.
- They have tech that supports integrated risk management: 85% of respondents from integrated organizations reported having a technology architecture that supports integrated risk management, vs. 75% of respondents who view compliance as a policing function.
- They expedite evidence management work flows with software: They use software to centralize and automate the collection of evidence (for control testing and IT compliance audits) at twice the rate of those who view compliance as a policing function (56% versus 28%).
Want to Get Additional Insights and Benchmarks To Inform Your IT Compliance Strategy?
You can access additional benchmarks and the complete 2021 IT Compliance Benchmark Report here.
How Hyperproof Supports Integrated IT Risk Management

Hyperproof’s compliance operations platform can help your security assurance/compliance team manage your information security compliance work consistently and efficiently, and you’ll be able to easily gauge how well existing risks are managed and identify areas for improvement. Hyperproof’s key capabilities include:
- Record-Keeping: Hyperproof serves as the single source of truth for all of your risks and compliance activities. Hyperproof can be where you house all infosec compliance requirements and standard frameworks (e.g. SOC 2, ISO 27001, PCI, etc.), controls universe, and evidence. Evidence retrieval is easy with Hyperproof, and your organization will be well-prepared for a spot audit at any time. If you choose, you can also use Hyperproof’s Risk Register to keep track of your risks. Risks can be mapped back to existing controls — allowing you to understand how well your existing risks are managed.
- Project management: You can use Hyperproof to determine your scope of work and what needs to be done to meet compliance frameworks’ requirements (e.g., what controls need to be created), identify owners and contributors to the work, create timelines, and assign tasks. Equally important, Hyperproof will help you identify existing controls you can leverage to meet requirements for new compliance frameworks.
- Workflow optimization and automation: Cut the time your team spends on manual tasks by up to 70 percent and free up time to work on the most impactful activities. With Hyperproof, you can improve productivity by automating manual tasks (e.g., collect evidence automatically, set automated reminders for others to submit evidence) and remove friction points from collaborative processes.
- Reporting and monitoring: Hyperproof makes it easy for everyone within your organization to get on the same page about what the current state of your compliance efforts are and where improvements are needed. With real time analytics, your team knows exactly where they should spend their time and energy. Potential problems, such as outdated controls, are identified early before they metastasize into costly incidents.
To learn more about Hyperproof, sign up for a personalized demo.
The post When Organizations Take a Risk-First Approach to IT Compliance, They’re Better at Avoiding Security Incidents appeared first on Hyperproof.
*** This is a Security Bloggers Network syndicated blog from Hyperproof authored by Jingcong Zhao. Read the original post at: https://hyperproof.io/resource/risk-first-approach-to-compliance/





