A step by step guide toSilent SMS Attacks and Security
Cellular attacks are more common than most users of mobile connectivity think. Fueled by the COVID-19 pandemic and the growing number of connected IoT devices, there have been 4.83 million attacks in 2020. This is a fifteen percent increase when compared to 2019. And those are just the attacks detected.
The most worrying types of cellular threats are those you cannot detect even after an attack was executed. Among these threats are Silent SMS attacks. As the name suggests, silent SMS (also known as “stealth SMS,” “stealth ping”, or “Short Message Type 0”) attacks are just that – attacks that sound no alarms on the target devices or at the networks.
How exactly do they work? And how can MNOs and users defend against them in 2021 and beyond?
What are silent SMS attacks?
Silent SMS is a message of Type 0 that is acknowledged by the recipient device but does not contain any content. Messages of these types do not show on the screen display nor alert the user.
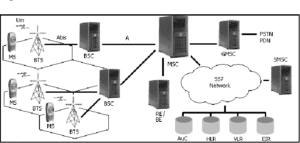
The SS7 (Signaling System No. 7) protocols are fundamental in cellular communication networks. Unfortunately, SS7 has numerous vulnerabilities that a malefactor can take advantage of to launch attacks. These include location tracking, SMS interception, and other types of signaling attacks.
One of the more interesting attacks is the Silent SMS Denial of Service (DoS) attack. During a normal DoS attack, a network is flooded with excess traffic rendering its computer resources unreachable to users. The same idea can be applied to mobile devices. A device can be flooded with silent SMS messages without the victim knowing it’s even happening. The messages flooding the target device will abnormally consume the battery while preventing the device from receiving calls.
Location information and tracking is another widespread target for malefactors exploiting SS7 protocol vulnerabilities. To determine the location of the target mobile device, a silent SMS could be sent to that device to force it to update the current (typically the nearest) serving base station onto the cellular network.
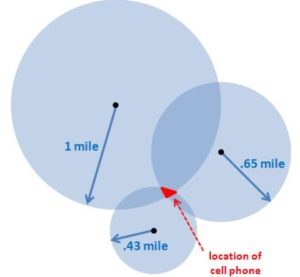
Like in a Silent SMS DoS attack, the device user will not be alerted about receiving any message. However, unlike a DoS attack, there are no visible symptoms noticeable of an attack taking place. Therefore, the victim will be completely unaware that they are being tracked.
The SIM card is another major target as well because they utilize Wireless Internet Browsers (WIB) that are not always properly secured. Telecommunications companies use Over the Air technology to talk to WIBs so that they can manage SIM cards.
Essentially, malefactors can send a silent SMS that contains instructions for the WIB. Once received on the victim’s device, the instructions are executed. At this point, there are several things that the malefactor can do, such as get location data, start a call, send an SMS, or even launch an internet browser with a specific URL.
Who is performing Silent SMS attacks?
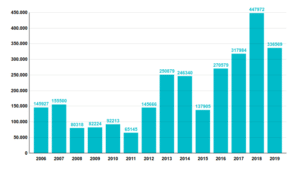
Though it has been reportedly used by authorities and governments so far, the lowering costs of equipment and broadband access has made this attack vector accessible even to malefactors with minimal technical knowledge.
Usage of sending Silent SMS by police is on the rise. For example, in Germany, police sent 138,000 messages in 2015. In 2018, the amount sent had tripled, and it is not openly stated why there has been a sudden increase.
Who is at risk of a Silent SMS attack?
For most users, having their location tracked or losing wireless access due to a DoS attack is not critical. However, when it comes to triangulating the location of mission-critical mobile IoT devices (like vehicles) or disabling communication with persons who must stay in touch at all times? It’s enterprises and governments who are at risk from attackers.
For enterprises, attacks will most likely result in monetary losses, whereas, for governments, national defense is at stake. They also need to consider the damage that could be done if an attacker can install malware on the device using Wireless Internet Browsers’ vulnerabilities on SIM cards.
Why are silent SMS attacks so dangerous?
Cellular attacks exploiting the SS7 protocol are nothing new. However, considering the covert nature of silent SMS attacks, they are tough to detect before it is too late. This makes silent SMS attacks a compliance nightmare. A breach cannot be detected and, as such, cannot be reported in a compliant manner. Invisible DoS attacks, OTA malware, and unauthorized location tracking can be risky if not devastating.
Not only are SS7 attacks nearly impossible to detect when the attack is occurring, but from a forensics standpoint, they leave virtually no traces. The forensic investigator has little to no data to extract from the victim’s device for analysis. Of course, this is unless the victim has an application installed on their device that is specifically designed to detect and intercept silent SMS messages.
At the cellular network level, the investigator may be able to analyze the traffic and potentially detect the unusually high amount of messages sent. Unfortunately, the investigator needs to have the victim’s device in hand to verify an attack occurs in real-time.
What you can do to protect yourself
The only way to effectively detect and thwart such attacks is on the mobile network level. This requires the use of MNO tools and technologies that aim to “plug” the security holes created by the antiquated SS7 protocol still in use today.
Today, much of the defense against silent SMS attacks is left to users and IT administrators in enterprises who (sadly) lack the tools to protect against silent SMS attacks. For telecommunications companies in 2021, this means looking at SS7 protection from a global approach. This, in turn, demands putting in place the proper solutions and security tools to protect their networks and subscriber devices from these attacks.
Keep Silent SMS away from your organization
FirstPoint’s cellular security solutions give airtight protection from malicious SMS.
The post A step by step guide to</br>Silent SMS Attacks and Security appeared first on FirstPoint.
*** This is a Security Bloggers Network syndicated blog from Blog – FirstPoint authored by Adam Weinberg. Read the original post at: https://www.firstpoint-mg.com/blog/step-by-step-silent-sms-attacks/



