Patch Tuesday: December 2021
On Tuesday, December 14, 2021, Microsoft released its monthly set of software security patches. This month, Microsoft has patched 67 software vulnerabilities in total, including seven critical issues and a zero-day vulnerability being exploited in the wild.
Zero-day vulnerabilities are those that have been publicly disclosed but don’t yet have a patch. Hence, they pose a greater security risk since your vulnerable systems are exposed until a patch becomes available. You should act quickly to apply patches to the zero-days in this month’s release.
The tools affected by this month’s vulnerabilities include Microsoft Office, Microsoft Windows Codecs Library, Visual Studio Code, Windows Kernel, Windows Update Stack and Azure Bot Framework SDK.
The critical bugs in this month’s Patch Tuesday release are:
| ID | Affected Product(s) | Impact | Rating |
|---|---|---|---|
| CVE-2021-43215 | Internet Storage Name Service (iSNS) protocol | Server Memory Corruption Vulnerability Can Lead to Remote Code Execution | Critical |
| CVE-2021-43905 | Microsoft Office app | Remote Code Execution Vulnerability | Critical |
| CVE-2021-43233 | Remote Desktop Client | Remote Code Execution Vulnerability | Critical |
| CVE-2021-43883 | Windows Installer | Elevation of Privilege Vulnerability | Important |
| CVE-2021-43240 | NTFS Set Short Name | Elevation of Privilege Vulnerability | Important |
| CVE-2021-41333 | Windows Print Spooler | Elevation of Privilege Vulnerability | Important |
| CVE-2021-43890 | Windows AppX Installer | Spoofing Vulnerability | Important |
The December 2021 Security Update Release Notes can be found here.
We recommend all critical patches be deployed as soon as possible, but no later than 30 days after release. For detailed information on all 67 vulnerabilities, please visit Microsoft’s Security Update Guide page.
All About Patch Tuesday
Any individual that has spent time on a personal computer knows what an update or patch is. A patch is a set of changes or updates done to a computer program or application — everything from the operating system (OS) to business apps and browsers. This is mostly done to fix a software bug or error or to provide new features and enhancements. Patching of software is important since security patches address software vulnerabilities that cybercriminals might exploit to gain unauthorized access to your device and your data.
What Is Patch Tuesday?
Microsoft Patch Tuesday is the second Tuesday of every month on which Microsoft releases security-related updates for its Windows OS, browsers and business applications. The other updates, not related to security, are released on the fourth Tuesday of every month. Sometimes, Microsoft releases an out-of-band (OOB) update for an emergency security issue that is not published specifically on the second Tuesday, but could be published on any day of the month.
When Did Patch Tuesday Begin?
Patch Tuesday was introduced by Microsoft in October 2003 to mainly reduce the cost of distributing patches. Tuesday was specifically chosen as the optimal day of the week so as to allow users to apply patches over the week. Monday was left free to address any issues that arose over the preceding weekend.
Severity Rating System for Vulnerabilities
To help customers understand the importance of applying a particular patch, Microsoft has published a severity rating system that rates each vulnerability according to the worst theoretical outcome should that vulnerability be exploited.
| Rating | Description |
|---|---|
| Critical | It is recommended that critical updates are applied quickly. A vulnerability is rated critical when its exploitation could allow code execution without user interaction. |
| Important | A vulnerability that could result in the compromise of confidentiality and integrity of user data. Microsoft recommends that customers apply important updates at the earliest opportunity. |
| Moderate | A vulnerability that is mitigated to a significant degree by certain factors such as default configuration, auditing and authentication requirements. Microsoft recommends that customers consider applying the security update. |
| Low | A vulnerability that is extremely difficult to exploit or has minimal impact. |
Why is Patching Needed?
Patching is required to remediate software vulnerabilities that can be exploited by hackers. It helps prevent security breaches, data theft, data loss and violation of compliance regulations. Timely deployment of patches is a critical part of a business’ IT security strategy.
How do I check my Edition, Version and OS Build on Windows 10?
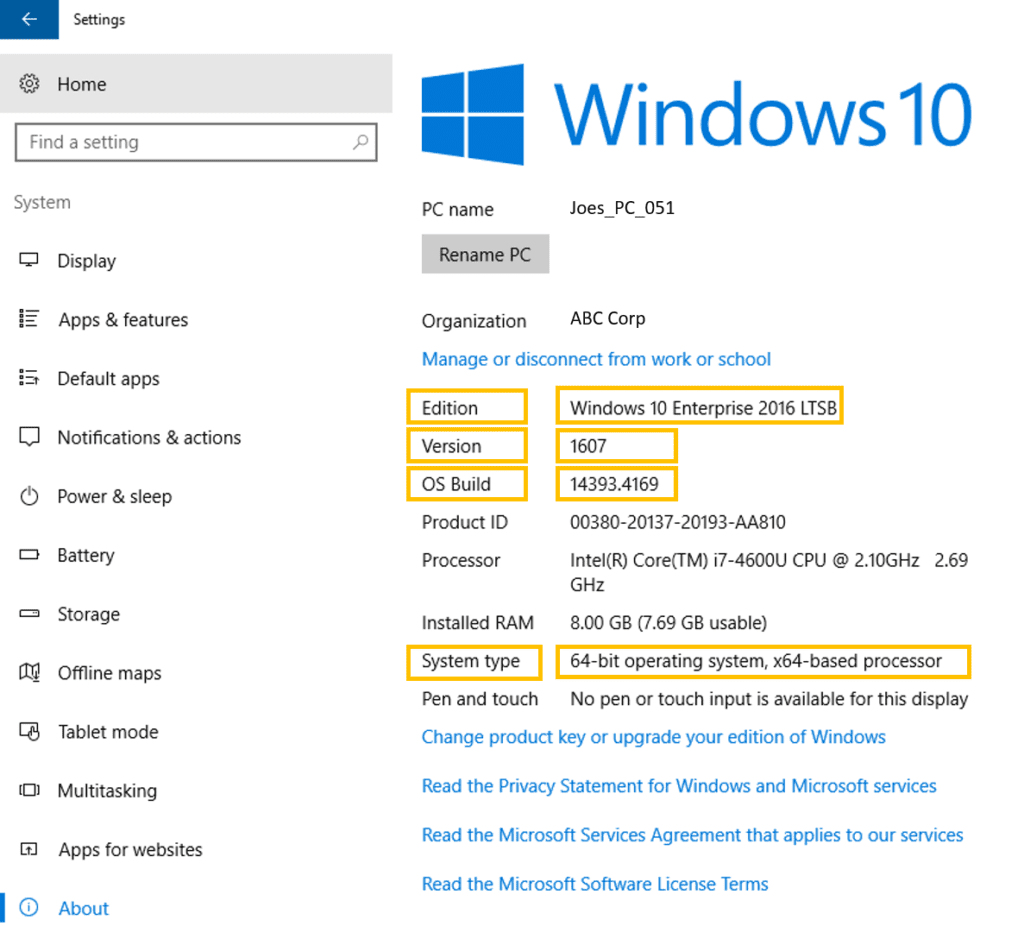
Login to your computer and select the start button.
Go to Settings > System > About
Open the About settings. Depending on the version of Windows 10 you have, you can see System Type (32-bit or 64-bit), Edition, Version and OS Build on the same page (see screenshot below) or under Device specifications > System type and Windows specifications.
How can users check which patches they have gotten?
If the user is using a Windows-based personal computer:
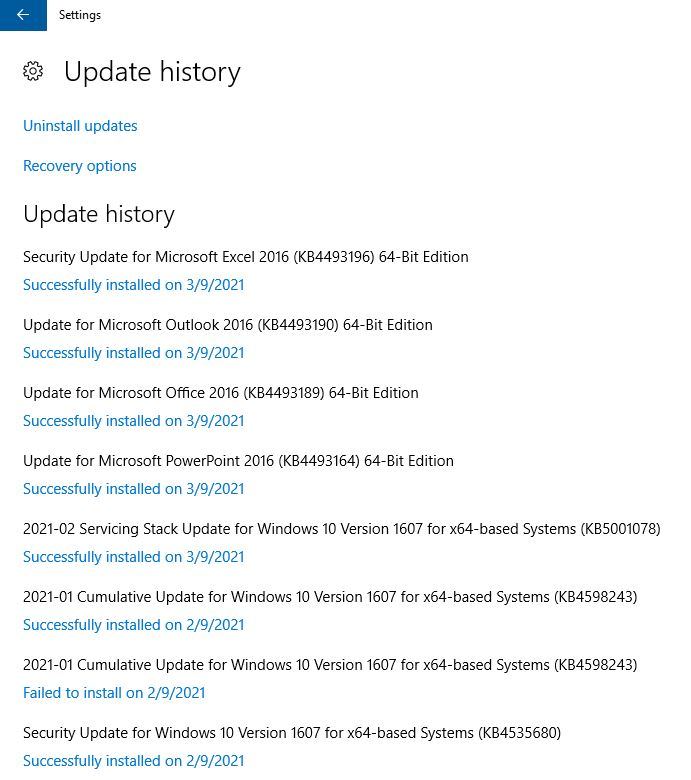
Click on Search>Windows Update Settings> View update history. Here you can see the versions of the software installed on your computer. If you’d like to check for any missing updates, click on “Check for updates.”
Are Microsoft patches cumulative?
Patch Tuesday updates, which are Windows security updates are cumulative and are released on the second Tuesday of each month. Cumulative updates mean if you miss an update one month, it’s rolled into the patch for the next month.
What is the difference between a patch and an update?
General software updates are feature based updates, to enhance the functionality of the software, while Patch Tuesday patches are specifically for security fixes.
Are updates only released on Patch Tuesday?
No. Feature updates that improve the capabilities or functionalities of a software are released twice a year, during spring and fall, also known as “semi-annual” releases.
Windows security improvements are released on “Patch Tuesday” meaning on the second Tuesday of each month.
Occasionally, when there is a high-risk security vulnerability discovered, Microsoft releases an out-of-band patch, in between Patch Tuesdays, that should be applied immediately.
What is Exploit Wednesday?
Patch Tuesday: November 2021 Updates
The day following the release of the security updates on Patch Tuesday is called the Exploit Wednesday, as hackers become more active on these days, preying on unpatched vulnerabilities. Hence, it is recommended to install a patch as soon as possible to reduce the risk of security breaches.
On Tuesday, November 9, 2021, Microsoft released its monthly set of software security patches. This month, Microsoft has patched 55 software vulnerabilities in total, including six zero-day vulnerabilities and six critical vulnerabilities.
The six zero-day vulnerabilities are tracked as CVE-2021-42292 (actively exploited) , CVE-2021-42321 (actively exploited), CVE-2021-38631, CVE-2021-43208 ,CVE-2021-43209 and CVE-2021-41371.
Zero-day vulnerabilities are those that have been publicly disclosed but don’t yet have a patch. Hence, they pose a greater security risk since your vulnerable systems are exposed until a patch becomes available. You should act quickly to apply the patches to the zero-days in this month’s release.
The tools affected by this month’s vulnerabilities include Chromium-based Edge browser, Microsoft Azure, Microsoft Office, Visual Studio, Windows Kernel, Exchange Server and Windows Defender.
The critical bugs in this month’s Patch Tuesday release are:
| ID | Affected Product(s) | Impact | Rating |
|---|---|---|---|
| CVE-2021-3711 | Visual Studio | OpenSSL: CVE-2021-3711 SM2 Decryption Buffer Overflow | Critical |
| CVE-2021-42298 | Windows Defender | Microsoft Defender Remote Code Execution Vulnerability | Critical |
| CVE-2021-42316 | Microsoft Dynamics | Microsoft Dynamics 365 (on-premises) Remote Code Execution Vulnerability | Critical |
| CVE-2021-38666 | Windows RDP | Remote Desktop Client Remote Code Execution Vulnerability | Critical |
| CVE-2021-42279 | Windows Scripting | Chakra Scripting Engine Memory Corruption Vulnerability | Critical |
| CVE-2021-26443 | Windows Virtual Machine Bus | Microsoft Virtual Machine Bus (VMBus) Remote Code Execution Vulnerability | Critical |
The November 2021 Security Update Release Notes can be found here.
Patch Tuesday: October 2021 Updates
On Tuesday, October 12, 2021, Microsoft released its monthly set of software security patches. This month, Microsoft has patched 74 software vulnerabilities in total, including four zero-day vulnerabilities and three critical vulnerabilities.
The four zero-day vulnerabilities are tracked as CVE-2021-41338 , CVE-2021-40469 , CVE-2021-41335 and CVE-2021-40449 which is being actively exploited.
Zero-day vulnerabilities are those that have been publicly disclosed but don’t yet have a patch. Hence, they pose a greater security risk since your vulnerable systems are exposed until a patch becomes available. You should act quickly to apply the patches to the zero-days in this month’s release.
The tools affected by this month’s vulnerabilities include Windows, Microsoft Office, Active Directory Federation Services and Microsoft Visual Studio.
The critical bugs in this month’s Patch Tuesday release are:
| ID | Affected Product(s) | Impact | Rating |
|---|---|---|---|
| CVE-2021-40486 | Microsoft Office Word | Remote Code Execution | Critical |
| CVE-2021-40461 | Role: Windows Hyper-V | Remote Code Execution | Critical |
| CVE-2021-38672 | Role: Windows Hyper-V | Remote Code Execution | Critical |
The October 2021 Security Update Release Notes can be found here.
Patch Tuesday: September 2021 Updates
On Tuesday, September 14, 2021, Microsoft released its monthly set of software security patches. This month, Microsoft has patched 60 software vulnerabilities in total, out of which four are critical vulnerabilities and one is a zero-day vulnerability.
The zero-day vulnerability CVE-2021-40444 was found in Microsoft’s MSHTML (Trident) engine that was exploited in the wild in limited, targeted attacks.
Zero-day vulnerabilities are those that have been publicly disclosed but don’t yet have a patch. Hence, they pose a greater security risk since your vulnerable systems are exposed until a patch becomes available. You should act quickly to apply the patches to the zero-days in this month’s release.
The tools affected by this month’s vulnerabilities include Windows, Azure, Microsoft Office, Microsoft Sharepoint and Microsoft Visual Studio.
The critical bugs in this month’s Patch Tuesday release are:
| ID | Affected Product(s) | Impact | Rating |
|---|---|---|---|
| CVE-2021-40444 | Microsoft’s MSHTML (Trident) engine | Remote Code Execution | Critical |
| CVE-2021-26435 | Windows Server 2012 R2 (Server Core installation) | Elevation of Privilege | Critical |
| CVE-2021-38647 | Azure Open Management Infrastructure | Elevation of Privilege | Critical |
| CVE-2021-36965 | Windows Server 2012 R2 (Server Core installation) | Remote Code Execution | Critical |
The September 2021 Security Update Release Notes can be found here.
Patch Tuesday: August 2021 Updates
On Tuesday, August 10, 2021, Microsoft released its monthly set of software security patches. This month, Microsoft has patched 44 software vulnerabilities in total, out of which seven are critical vulnerabilities and three are zero-day vulnerabilities.
Zero-day vulnerabilities are those that have been publicly disclosed but don’t yet have a patch. So, they pose a greater security risk since your vulnerable systems are exposed until a patch becomes available. You should act quickly to apply the patches to the zero-days in this month’s release.
The tools affected by this month’s vulnerabilities include Windows Update, Azure, Microsoft Office, Microsoft Dynamics, Windows Print Spooler Components, ASP.NET Core & Visual Studio, and Remote Desktop Client.
Seven of the vulnerabilities being patched are critical, remote code execution (RCE) bugs that could allow cybercriminals to gain control over systems without any user involvement.
The critical bugs in this month’s Patch Tuesday release are:
| ID | Affected Product(s) | Impact | Rating |
|---|---|---|---|
| CVE-2021-36936 | Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) | Remote Code Execution | Critical |
| CVE-2021-26424 | Windows 10 Version 20H2 for x64-based Systems | Remote Code Execution | Critical |
| CVE-2021-34480 | Windows 10 Version 21H1 for 32-bit Systems | Remote Code Execution | Critical |
| CVE-2021-34534 | Windows MSHTML Platform | Remote Code Execution | Critical |
| CVE-2021-34535 | Remote Desktop Client | Remote Code Execution | Critical |
| CVE-2021-26432 | Windows Services for NFS ONCRPC XDR Driver | Remote Code Execution | Critical |
| CVE-2021-34530 | Microsoft Graphics Component | Remote Code Execution | Critical |
The August 2021 Security Update Release Notes can be found here.
Patch Tuesday: July 2021 Updates
On Tuesday, July 13, 2021, Microsoft released its monthly set of software security patches. This month, Microsoft has patched 117 software vulnerabilities in its Windows Kernal, Microsoft Office, SharePoint, Exchange Server, Visual Studio, and other products.
Thirteen of the vulnerabilities that have been patched in this month’s release are rated critical and nine are zero-days, out of which four are actively being exploited in the wild.
Zero-day vulnerabilities are those that have been publicly disclosed but don’t yet have a patch. So, they pose a greater security risk since your vulnerable systems are exposed until a patch becomes available. You should act quickly to apply the patches to the zero-days in this month’s release.
The four exploited zero-days patched in this release are: CVE-2021-34527 (PrintNightmare), CVE-2021-34448, CVE-2021-31979, and CVE-2021-33771.
Just a week prior to the latest Patch Tuesday release, Microsoft issued an emergency “out of band” patch to fix the “PrintNightmare” vulnerability (CVE-2021-34527). But that patch did not fully remediate the issue.
Twelve of the vulnerabilities being patched are critical, remote code execution (RCE) bugs that could allow cybercriminals to gain control over systems without any user involvement.
The critical bugs in this month’s Patch Tuesday release are:
| ID | Affected Product(s) | Impact | Rating |
|---|---|---|---|
| CVE-2021-34448 | Windows Server 2012 R2 | Remote Code Execution | Critical |
| CVE-2021-34497 | Windows 10 Version 1809 for 32-bit Systems | Remote Code Execution | Critical |
| CVE-2021-34494 | Windows Server 2016 | Remote Code Execution | Critical |
| CV E-2021-34464 | Microsoft Malware Protection Engine | Remote Code Execution | Critical |
| CVE-2021-34473 | Microsoft Exchange Server 2019 Cumulative Update 9 | Remote Code Execution | Critical |
| CVE-2021-34450 | Windows Server, version 20H2 (Server Core Installation) | Remote Code Execution | Critical |
| CVE-2021-34522 | Microsoft Malware Protection Engine | Remote Code Execution | Critical |
| CVE-2021-34474 | Microsoft Dynamics 365 Business Central 2021 Release Wave 1 – Update 18.3 | Remote Code Execution | Critical |
| CVE-2021-34458 | Windows Server 2016 (Server Core installation) | Remote Code Execution | Critical |
| CVE-2021-34503 | Windows 10 Version 1909 for ARM64-based Systems | Remote Code Execution | Critical |
| CVE-2021-34439 | Windows Server 2016 (Server Core installation) | Remote Code Execution | Critical |
| CVE-2021-33740 | Windows 10 for x64-based Systems | Remote Code Execution | Critical |
The June 2021 Security Update Release Notes can be found here.
Patch Tuesday: June 2021 Updates
On Tuesday, June 8, 2021, Microsoft released its monthly set of software security patches. This month, Microsoft has patched 49 software vulnerabilities in its Windows, Windows Server, Microsoft Office, SharePoint Server, Visual Studio, and other products.
Six of the vulnerabilities that have been patched in this month’s release are zero-days that are actively being exploited in targeted attacks:
- CVE-2021-33742, a remote code execution bug in a Windows HTML component, CVSS 7.5
- CVE-2021-31955, an information disclosure bug in the Windows Kernel, CVSS 5.5
- CVE-2021-31956, an elevation of privilege flaw in Windows NTFS, CVSS 7.8
- CVE-2021-33739, an elevation of privilege flaw in the Microsoft Desktop Window Manager, CVSS 8.4
- CVE-2021-31201, an elevation of privilege flaw in the Microsoft Enhanced Cryptographic Provider, CVSS 5.2
- CVE-2021-31199, an elevation of privilege flaw in the Microsoft Enhanced Cryptographic Provider, CVSS 5.2
Zero-day vulnerabilities are those that have been publicly disclosed but don’t yet have a patch. So, they pose a greater security risk since your vulnerable systems are exposed until a patch becomes available. All of the above zero-days have already been exploited, so you should act quickly to apply these patches.
Five of the vulnerabilities being patched are critical, remote code execution (RCE) bugs that could allow cyber criminals to gain control over systems without any user involvement. The critical bugs in this month’s Patch Tuesday release are:
| ID | Affected Product(s) | Impact | Rating |
|---|---|---|---|
| CVE-2021-31985 | Microsoft Defender Malware Protection Engine | Remote Code Execution | Critical |
| CVE-2021-31959 | Windows RT 8.1, Windows 7, Windows 10, Windows Server 2008 R2, 2012, 2016, 2019 | Remote Code Execution | Critical |
| CVE-2021-31967 | VP9 Video Extensions | Remote Code Execution | Critical |
| CVE-2021-31963 | Microsoft SharePoint Server | Remote Code Execution | Critical |
| CVE-2021-33742 | Windows RT 8.1, Windows 7, Windows 10, Windows Server 2008, 2008 R2, 2012, 2012 R2, 2016, 2019 | Remote Code Execution | Critical |
The June 2021 Security Update Release Notes can be found here.
Patch Tuesday: May 2021 Updates
For the May 11, 2021 Patch Tuesday, Microsoft has patched 55 software vulnerabilities in its Windows, Windows Server, Internet Explorer, Microsoft Office, Exchange Server and other products. Four of the vulnerabilities being patched are critical remote code execution (RCE) bugs that could allow cyber criminals to gain control over systems without any user involvement. Microsoft has said that none of these critical vulnerabilities are being actively exploited in the wild.
The highest priority vulnerability is CVE-2021-31166, a Windows 10 and Windows Server bug that has a CVSS rating of 9.8 out of 10. This bug has been described as “wormable” meaning that it could be used to self-replicate across the internal network and affect internal services that may not have been exposed, according to Microsoft.
The critical bugs in this month’s Patch Tuesday release are:
| ID | Title | Rating |
|---|---|---|
| CVE-2021-31166 | HTTP Protocol Stack Remote Code Execution Vulnerability: A wormable HTTP protocol-stack issue in Windows 10 and some versions of Windows Server allowing remote code-execution (RCE) | Critical |
| CVE-2021-26419 | Scripting Engine Memory Corruption Vulnerability: A scripting-engine memory corruption vulnerability in Internet Explorer 11 and 9 allowing RCE | Critical |
| CVE-2021-31194 | OLE Automation Remote Code Execution Vulnerability: An RCE bug in Microsoft Windows Object Linking and Embedding (OLE) Automation | Critical |
| CVE-2021-28476 | Hyper-V Remote Code Execution Vulnerability: An RCE vulnerability in Microsoft Windows Hyper-V | Critical |
The May 2021 Security Update Release Notes can be found here.
We recommend that all critical patches be deployed within 30 days of release. For detailed information on all 55 vulnerabilities, please visit Microsoft’s Security Update Guide page.
Patch Tuesday: April 2021 Updates
On Tuesday, April 13, 2020, Microsoft released its monthly set of software security patches. This month, 108 software vulnerabilities have been remediated with 19 of them being rated “critical” and 88 being rated as “important” and one as “moderate” in severity.
The list includes patches for four new critical vulnerabilities in Microsoft Exchange Server with CVE IDs CVE-2021-28480, CVE-2021-28481, CVE-2021-28482, CVE-2021-28483. As noted in Microsoft’s blog, they recommend that customers prioritize (i.e. update as soon as possible) patches for critical vulnerabilities, including patches for these new vulnerabilities in on-premises Exchange Servers.
Microsoft had previously released emergency, out-of-band patches for four zero-day vulnerabilities in Exchange Server on March 2, 2021. For more details on these earlier vulnerabilities, see this ZDNet article. Microsoft also published a mitigation guide and made available a one-click mitigation tool for these vulnerabilities. Microsoft strongly recommended that customers investigate their Exchange Server deployments to be sure that they haven’t been compromised.
As always, make sure that you have backed up your systems before you apply updates to your software.
The CVE details of the April critical vulnerabilities are listed below:
| ID | Title | Rating |
|---|---|---|
| CVE-2021-27095 | Windows Media Video Decoder Remote Code Execution Vulnerability | Critical |
| CVE-2021-28315 | Windows Media Video Decoder Remote Code Execution Vulnerability | Critical |
| CVE-2021-28329 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28330 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28331 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28332 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28333 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28334 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28335 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28336 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28337 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28338 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28339 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28343 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-28460 | Azure Sphere Unsigned Code Execution Vulnerability | Critical |
| CVE-2021-28480 | Microsoft Exchange Server Remote Code Execution Vulnerability | Critical |
| CVE-2021-28481 | Microsoft Exchange Server Remote Code Execution Vulnerability | Critical |
| CVE-2021-28482 | Microsoft Exchange Server Remote Code Execution Vulnerability | Critical |
| CVE-2021-28483 | Microsoft Exchange Server Remote Code Execution Vulnerability | Critical |
Here are the release notes for the April 2021 security updates.
Patch Tuesday: March 2021 Updates
This month’s Patch Tuesday security updates are here. In the March release, Microsoft has rolled out 82 security patches for Windows and other supported software. 10 out of these patches are deemed “Critical” in severity. The Internet Explorer vulnerability CVE-2021-26411 has seen active exploitation. An attacker could host a specially crafted website designed to exploit the vulnerability through Internet Explorer and then convince a user to view the website. Below are the details of the critical patches.
| ID | Title | Rating |
|---|---|---|
| CVE-2021-21300 | Git for Visual Studio Remote Code Execution Vulnerability | Critical |
| CVE-2021-24089 | HEVC Video Extensions Remote Code Execution Vulnerability | Critical |
| CVE-2021-26411 | Internet Explorer Memory Corruption Vulnerability | Critical |
| CVE-2021-26867 | Windows Hyper-V Remote Code Execution Vulnerability | Critical |
| CVE-2021-26876 | OpenType Font Parsing Remote Code Execution Vulnerability | Critical |
| CVE-2021-26897 | Windows DNS Server Remote Code Execution Vulnerability | Critical |
| CVE-2021-26902 | HEVC Video Extensions Remote Code Execution Vulnerability | Critical |
| CVE-2021-27061 | HEVC Video Extensions Remote Code Execution Vulnerability | Critical |
| CVE-2021-27074 | Azure Sphere Unsigned Code Execution Vulnerability | Critical |
| CVE-2021-27080 | Azure Sphere Unsigned Code Execution Vulnerability | Critical |
Here are the release notes for the March 2021 security updates.
Patch Tuesday: February 2021 Updates
Patch Tuesday is here. In this February 2021 release, Microsoft rolled out updates for 56 security vulnerabilities across Windows OS, Windows Server, Windows Defender, Windows PowerShell, Azure, Microsoft Edge and more.
11 of these 56 updates are deemed to be “critical”, and allow remote code execution, meaning these require special attention and should be patched as soon as possible.
The updates included a “zero-day” vulnerability CVE-2021-1732, an elevation of privilege bug that affects Windows Server 2019, Windows Server 20H2 and Windows 10. This “important” vulnerability has already been exploited in the wild.
As noted in Krebs on Security, there are two critical vulnerabilities in Microsoft’s .NET Framework that are a concern because .NET is “a component required by many third-party applications (most Windows users will have some version of .NET installed).”
Further, Krebs says, “Windows 10 users should note that while the operating system installs all monthly patch roll-ups in one go, that rollup does not typically include .NET updates, which are installed on their own. So when you’ve backed up your system and installed this month’s patches, you may want to check Windows Update again to see if there are any .NET updates pending.”
CVE-2021-24078 is a Windows DNS Server Remote Code Execution Vulnerability that has a CVSS score of 9.8, which is extremely high. According to Kev Breen of Immersive Labs, this vulnerability could be exploited to let an attacker “steal a lot of data by essentially altering the destination for organizational traffic; for example, by pointing internal appliances or Outlook Web Access at a malicious server.”
The details of the critical vulnerabilities are as below:
| ID | Title | Rating |
|---|---|---|
| CVE-2021-1722 | Windows Fax Service Remote Code Execution Vulnerability | Critical |
| CVE-2021-24074 | Windows TCP/IP Remote Code Execution Vulnerability | Critical |
| CVE-2021-24077 | Windows Fax Service Remote Code Execution Vulnerability | Critical |
| CVE-2021-24078 | Windows DNS Server Remote Code Execution Vulnerability | Critical |
| CVE-2021-24081 | Microsoft Windows Codecs Library Remote Code Execution Vulnerability | Critical |
| CVE-2021-24088 | Windows Local Spooler Remote Code Execution Vulnerability | Critical |
| CVE-2021-24091 | Windows Camera Codec Pack Remote Code Execution Vulnerability | Critical |
| CVE-2021-24093 | Windows Graphics Component Remote Code Execution Vulnerability | Critical |
| CVE-2021-24094 | Windows TCP/IP Remote Code Execution Vulnerability | Critical |
| CVE-2021-24112 | .NET Core Remote Code Execution Vulnerability | Critical |
| CVE-2021-26701 | .NET Core Remote Code Execution Vulnerability | Critical |
Here are the release notes for the February 2021 security updates.
Patch Tuesday: January 2021 Updates
The first Patch Tuesday of the year is here. In this January 2021 release, Microsoft rolled out updates for 83 security vulnerabilities across Windows OS, Windows Server, Windows Defender, Azure, Microsoft Edge and more.
Nine of these 83 updates are deemed to be “critical”, and allow remote code execution, meaning these require special attention and should be patched as soon as possible.
One of the most critical vulnerabilities is the Microsoft Defender Remote Code Execution Vulnerability – CVE-2021-1647 – a zero-day vulnerability that is known to be actively exploited. Typically, the Microsoft Malware Protection Engine will be updated automatically. As discussed in the Microsoft Update Guide, “best practices recommend that customers regularly verify whether software distribution, such as the automatic deployment of Microsoft Malware Protection Engine updates and malware definitions, is working as expected in their environment.”
The details of the critical vulnerabilities are as below:
| ID | Title | Rating |
|---|---|---|
| CVE-2021-1643 | HEVC Video Extensions Remote Code Execution Vulnerability | Critical |
| CVE-2021-1647 | Microsoft Defender Remote Code Execution Vulnerability | Critical |
| CVE-2021-1658 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-1660 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-1665 | GDI+ Remote Code Execution Vulnerability | Critical |
| CVE-2021-1666 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-1667 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | Critical |
| CVE-2021-1668 | Microsoft DTV-DVD Video Decoder Remote Code Execution Vulnerability | Critical |
| CVE-021-1673 | Microsoft DTV-DVD Video Decoder Remote Code Execution Vulnerability | Critical |
Here are the release notes for the January 2021 security updates.
Patch Tuesday: December 2020 Updates
The second Tuesday of the month has arrived. We all know what that means. We are back today with the Microsoft Patch Tuesday updates for December 2020.
This month, Microsoft has fixed 58 vulnerabilities of which 22 are classified as remote code execution (RCE) vulnerabilities. These RCE vulnerabilities are the ones that should be addressed as soon as possible since they could be exploited via the internet without user interaction. Pay particular attention to the RCE bugs that affect Microsoft Exchange, SharePoint and Hyper-V.
When it comes to severity, 9 of the vulnerabilities are “Critical” affecting Microsoft Exchange Server (2013, 2016, 2019), Microsoft SharePoint, Dynamics 365 for Finance and Operations, Windows Server (2016 and 2019), Windows 10, ChakraCore and Microsoft Edge.
48 of the vulnerabilities are classified as “Important” and two others as “Moderate”. The December Patch Tuesday patches do not remediate any zero-day vulnerabilities. The CVE details for the critical vulnerabilities are listed below:
| ID | Title | Rating |
|---|---|---|
| CVE-2020-17095 | Hyper-V Remote Code Execution Vulnerability | Critical |
| CVE-2020-17117 | Microsoft Exchange Remote Code Execution Vulnerability | Critical |
| CVE-2020-17118 | Microsoft SharePoint Remote Code Execution Vulnerability | Critical |
| CVE-2020-17121 | Microsoft SharePoint Remote Code Execution Vulnerability | Critical |
| CVE-2020-17131 | Chakra Scripting Engine Memory Corruption Vulnerability | Critical |
| CVE-2020-17132 | Microsoft Exchange Remote Code Execution Vulnerability | Critical |
| CVE-2020-17142 | Microsoft Exchange Remote Code Execution Vulnerability | Critical |
| CVE-2020-17152 | Microsoft Dynamics 365 for Finance and Operations (on-premises) Remote Code Execution Vulnerability | Critical |
| CVE-2020-17158 | Microsoft Dynamics 365 for Finance and Operations (on-premises) Remote Code Execution Vulnerability | Critical |
Here are the release notes for the December 2020 security updates.
Patch Tuesday: November 2020 Updates
On Tuesday, November 10, 2020, Microsoft released its monthly set of software security patches. This month, they have remediated 112 software vulnerabilities. Among these, Microsoft provided a patch for a zero-day vulnerability, CVE-2020-17087, Windows Kernel Local Elevation of Privilege Vulnerability, which has already been exploited “in the wild.” The exploit works in conjunction with a Google Chrome zero-day vulnerability, as described in this ZDNet article.
The Chrome zero-day vulnerability has been patched in Chrome version 86.0.4240.111. The Windows vulnerability affects all currently supported versions of Windows, including Windows 10 and Windows Server.
Out of the 112 vulnerabilities, there are 24 that can allow remote code execution (RCE) exploits in a number of different Microsoft products, and 17 are rated “critical,” impacting the following:
- Windows Server, Version 20H2 (Server Core Installation)
- Raw Image Extension
- Microsoft Edge (EdgeHTML-based)
- Internet Explorer 11
- HEVC Video Extensions
- HEIF Image Extension
- Azure Sphere and
- AV1 Video Extension
The CVE details of the critical vulnerabilities are listed below:
Here are the release notes for the November 2020 security updates.
Patch Tuesday: October 2020 Updates
Microsoft provides Patch Tuesday updates in its Security Update Guide portal. Each update also comes with a set of release notes. (See this month’s release notes at the bottom of this blog.)
The Common Vulnerabilities and Exposure (CVE) ID is a format in which each vulnerability is disclosed and cataloged in the National Vulnerability Database (NVD). Vulnerabilities in the NVD have a criticality rating ranging from 1 (lowest) to 10 (highest).
For the October 2020 Patch Tuesday, a total of 87 CVEs were released, with 11 of them rated “Critical.” The October security updates are for the following Microsoft software:
- Microsoft Windows
- Microsoft Office and Microsoft Office Services and Web Apps
- Microsoft JET Database Engine
- Azure Functions
- Open Source Software
- Microsoft Exchange Server
- Visual Studio
- PowerShellGet
- Microsoft .NET Framework
- Microsoft Dynamics
- Adobe Flash Player
- Microsoft Windows Codecs Library
Below are the CVE details of the “Critical” vulnerabilities in this month’s update.
| ID | Title | Rating | Description |
|---|---|---|---|
| CVE-2020-16891 | Windows Hyper-V Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists when Windows Hyper-V on a host server fails to properly validate input from an authenticated user on a guest operating system. |
| CVE-2020-16898 | Windows TCP/IP Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists when the Windows TCP/IP stack improperly handles ICMPv6 Router Advertisement packets. |
| CVE-2020-16911 | GDI+ Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists in the way that the Windows Graphics Device Interface (GDI) handles objects in memory. |
| CVE-2020-16915 | Media Foundation Memory Corruption Vulnerability | Critical | A memory corruption vulnerability exists when Windows Media Foundation improperly handles objects in memory. |
| CVE-2020-16923 | Microsoft Graphics Components Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists in the way that Microsoft Graphics Components handle objects in memory. |
| CVE-2020-16947 | Microsoft Outlook Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists in Microsoft Outlook software when the software fails to properly handle objects in memory. |
| CVE-2020-16951 | Microsoft SharePoint Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists in Microsoft SharePoint when the software fails to check the source markup of an application package. |
| CVE-2020-16952 | Microsoft SharePoint Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists in Microsoft SharePoint when the software fails to check the source markup of an application package. |
| CVE-2020-16967 | Windows Camera Codec Pack Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists when the Windows Camera Codec Pack improperly handles objects in memory. |
| CVE-2020-16968 | Windows Camera Codec Pack Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists when the Windows Camera Codec Pack improperly handles objects in memory. |
| CVE-2020-17003 | Base3D Remote Code Execution Vulnerability | Critical | A remote code execution vulnerability exists when the Base3D rendering engine improperly handles memory. |
The complete details of all 87 October 2020 security updates can be found on the Microsoft’s Security Update Guide page. The release notes can be found here as well.
We highly recommend that you apply these patches at the earliest, within 30 days of release at the latest.
Learn more about patching in Kaseya VSA here.
The post Patch Tuesday: December 2021 appeared first on Kaseya.
*** This is a Security Bloggers Network syndicated blog from Blog – Kaseya authored by John Emmitt. Read the original post at: https://www.kaseya.com/blog/2021/12/01/patch-tuesday/

