Understanding NIST Cybersecurity Framework (NIST CSF) Functions
The NIST CSF is voluntary guidance aiming to help organizations better manage and reduce cybersecurity risk. It is based on existing standards, guidelines, and practices that have proven to be effective in improving cybersecurity posture. It can be used to help identify and prioritize actions for reducing cybersecurity risk, and it is a tool for aligning policy, business, and technological approaches to managing that risk.
The framework has a core set of cybersecurity activities organized at three levels:
- Functions
- Categories
- Subcategories
- Categories
The important distinction of Functions in NIST CSF
The three activities we have structured above are very unique and serve very specific purposes for taking charge of an organization’s cybersecurity posture. Sometimes these activities are used interchangeably in conversation, particularly by someone who has not had a chance to take a deeper dive into how the framework is organized. In this post we aim to explain the important distinction of functions in NIST CSF, and show how they can be utilized in an efficient and dynamic way for planning your cybersecurity program.
Those who wish to Functions organize basic cybersecurity activities at their highest level. These Functions are:
- Identify
- Protect
- Detect
- Respond
- Recover
Functions are meant to intuitively organize aspects of cybersecurity to support decision making, managing risk, addressing threats, and continually improving based on lessons learned. Functions address the steps to take prior to a cybersecurity event (Identify, Protect, Detect) as well what to do after a one occurs (Respond and Recover).
How NIST CSF Functions are structured in the framework
Each NIST CSF Function is subdivided into a number of Categories, each of which describes a group of outcomes that are recommended as part of the Function. Each Category is further subdivided into Subcategories. Each subcategory defines a specific recommended outcome. Informative References are existing standards, guidelines, and practices that are mapped to each subcategory.
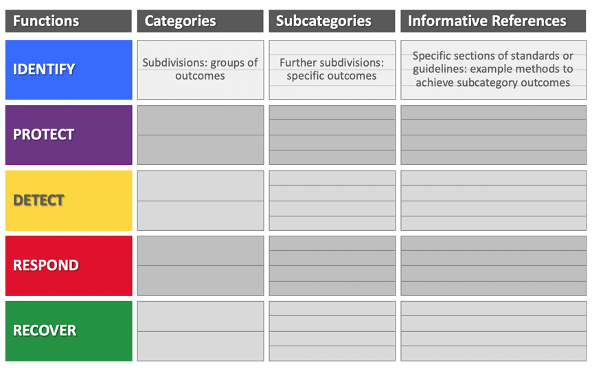
NIST CSF contains 5 Functions, 23 Categories, and 108 Subcategories
NIST CSF Functions communicate cyber risk clearly to all stakeholders
The NIST CSF Functions can be leveraged when communicating to both technical and non-technical audiences such as senior leadership and Boards of Directors because of the logical progression they describe. One of the great successes of the NIST CSF is that the world now commonly speaks of cybersecurity in terms of Identify, Protect, Detect, Respond, and Recover.
A closer look at the 5 Functions of NIST CSF
1. Identify
Develop the organizational understanding to manage cybersecurity risk to systems, assets, data, and capabilities.
The first Function, Identify, drives home the importance of understanding what cybersecurity risks the organization is susceptible to before going about putting protections in place.
Example outcomes for the Identify function include:
- Identifying physical and software assets to establish an asset management program
- Establishing cybersecurity roles, responsibilities, and policies to define a governance program
- Defining a risk management strategy and risk assessment processes for the organization
2. Protect
Develop and implement appropriate safeguards to ensure delivery of critical services.
Once the organization has a grasp of the systems, assets, data, and capabilities in its environment and their associated risks, the next Function, Protect, guides actions for deciding what specific steps to take to protect them.
Example outcomes for the Protect function include:
- Implementing controls to protect the confidentiality, integrity, and availability of data
- Managing protective technologies to ensure the security and resilience of systems and assets
- Empowering and enabling staff through awareness and training activities
3. Detect
Develop and implement appropriate activities to identify the occurrence of a cybersecurity event.
Third, organizations need to be able to effectively detect when a cybersecurity event may be occurring and know what to look for.
Example outcomes for the Detect function include:
- Implementing continuous monitoring to identify cybersecurity events and verify protections
- Ensuring that anomalies and events are detected, and their potential impact is understood
- Testing and maintaining detection processes to ensure awareness of anomalous events
4. Respond
Develop and implement appropriate activities to take action regarding a detected cybersecurity incident.
Fourth, no organization is immune from cybersecurity event no matter how proactive it has been, so it is important to prepare for the steps needed after a cybersecurity event takes place.
Example outcomes for the Respond function include:
- Ensuring response plans are executed during or after an incident
- Coordinating and managing communications inside and outside the organization during a response
- Analyzing effectiveness of response activities
5. Recover
Develop and implement appropriate activities to maintain plans for resilience and to restore any capabilities or services that were impaired due to a cybersecurity incident.
Lastly, organizations have to get back to normal operations after a cyber security event.
Example outcomes for the Recover function include:
- Ensuring the organization implements recovery planning processes and procedures
- Implementing improvements based on lessons learned
- Coordinating communications during recovery activities
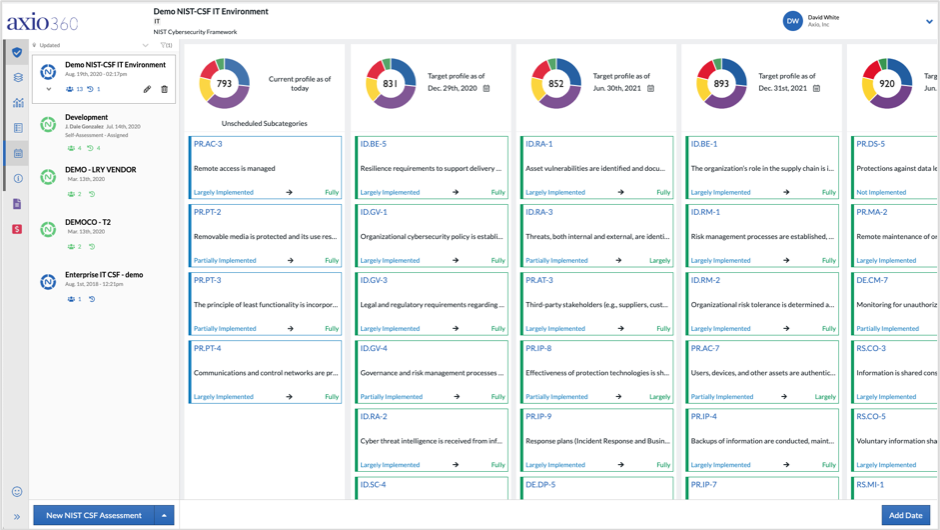
NIST CSF in the Axio360 platform
The 5 Functions in NIST CSF serve as the broadest starting point in completing an assessment of your cybersecurity program’s maturity. The Axio360 platform integrates the NIST CSF into its Cyber Program Assessment, Planning, and Management functionality.
Through Axio360 the NIST CSF can be used to:
- Manage and improve the health of your cyber program, with company-wide transparency.
- Benchmark your cybersecurity program to see how well it stacks up to peers.
- Create and manage a target profile and workplan for improvement.
- Continually share progress with company leadership and the Board with dynamic dashboards and generated reports.
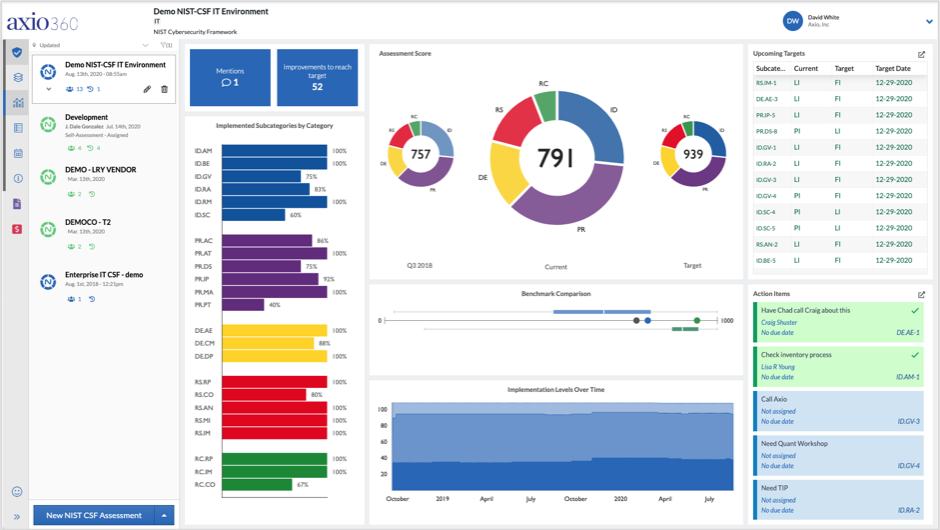 Axio360 NIST CSF Assessment Dashboard
Axio360 NIST CSF Assessment Dashboard
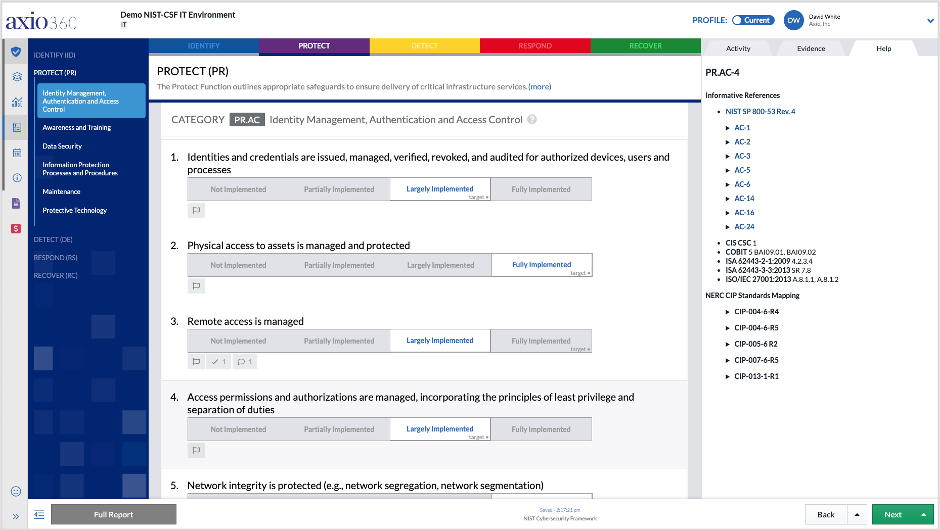 Axio360 NIST CSF Assessment and Target Profile Interface
Axio360 NIST CSF Assessment and Target Profile Interface
 Axio360 NIST CSF Roadmap Planning Tool
Axio360 NIST CSF Roadmap Planning Tool
How to get started with NIST CSF in the Axio360 platform
If you’d like to experience the complete functionality of NIST CSF and discuss your particular use case for the framework, are experts are standing by. You can book a demo.
About the author: Wassie Goushe is a senior cybersecurity engineer at Axio.
*** This is a Security Bloggers Network syndicated blog from Axio authored by Wassie Goushe. Read the original post at: https://axio.com/insights/understanding-nist-cybersecurity-framework-nist-csf-functions/

