Idaptive Release 20.2 is Now Available
Release 20.2 adds support for extended policy configuration for RADIUS MFA, enhancements to Windows and Mac Cloud Agents, and various UI and operational improvements.
With release 20.2, Idaptive now supports the following features:
Multi-Factor Authentication
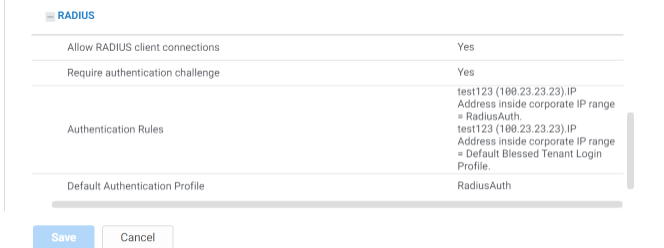
Extended Policy Configuration for RADIUS MFA
Idaptive can be configured with your RADIUS clients to provide the MFA authentication layer. Previously, secondary authentication requirements set in the authentication policies were enforced for all access requests to RADIUS clients. Now, you can define specific conditions, such as IP range, date, and time of the request when secondary authentication is required. For example, if your VPN service uses RADIUS for authentication, you can configure push notifications as a secondary authentication method for all requests coming from inside your corporate IP range. However, if access requests originate outside of your corporate network, a hardware token must be used to pass the secondary authentication challenge.
Device Security Management
Windows Cloud Agent Improvements
With this release, the new Windows Cloud Agent (WCA) supports the following capabilities:

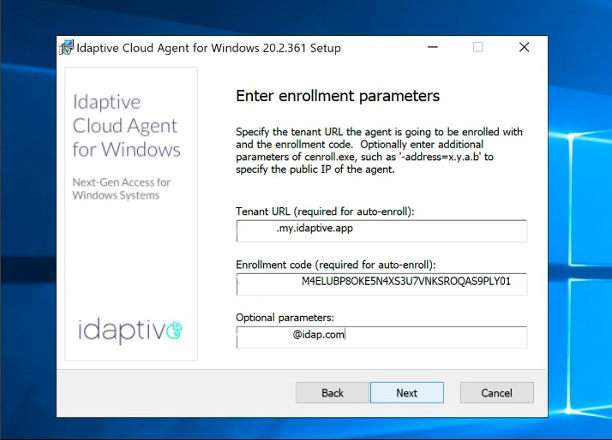
Deployment on non-domain joined endpoints
You can now deploy Windows Cloud Agent on non-domain joined endpoints, such as laptops, workstations, and servers. Previously, you could only deploy WCA on endpoints that have been joined to a domain or were actively connected to the corporate network. Now, you can deploy WCA on Windows endpoints without establishing a VPN connection or joining the domain. This eliminates the need for IT to set up endpoint devices prior to providing them to end-users and streamlines Single Sign-On and Multi-Factor Authentication setup for remote employees. For example, your employees who can’t come to the office or do not need domain-joined devices to perform their work can simply download and install the WCA agent on their laptops. Once installed, WCA enrolls the device into the Idaptive platform and enables them to log in to their devices with their Active Directory credentials after passing secondary authentication challenges.
Deployment on domain controllers
With this release, you can now deploy WCA on your domain controllers. This enables you to enroll your domain controllers into the Idaptive platform and enforce Multi-Factor Authentication requirements during the login process.
MFA on RDP/RDS connection for Windows workstations and servers
Remote Desktop Services (RDP) protocol and Remote Desktop Services (RDS) enable users to remotely connect to workstations and servers on your network. With WCA, you can now enroll workstations and servers into the Idaptive platform, setup RDP or RDS connection to them, enable RDP and RDS users with AD accounts to change their passwords or unlock their accounts, and enforce adaptive Multi-Factor Authentication at login.
Deployment of Zero Sign-On certificates
You can now deploy Zero Sign-On (ZSO) certificates on your Windows endpoints with Windows Cloud Agent. ZSO is a certificate-based authentication method that enables users to seamlessly login to their assigned applications and services without additional authentication once their devices are verified. This enables you to configure passwordless, conditional access rules based on the presence of ZSO certificates on devices. For example, you can configure a policy to bypass application authentication challenges on devices with a valid ZSO certificate and require multiple challenges for access requests from devices without a valid certificate.
Mac Cloud Agent Improvements
With this release, the new Mac Cloud Agent (MCA) supports the following capabilities:
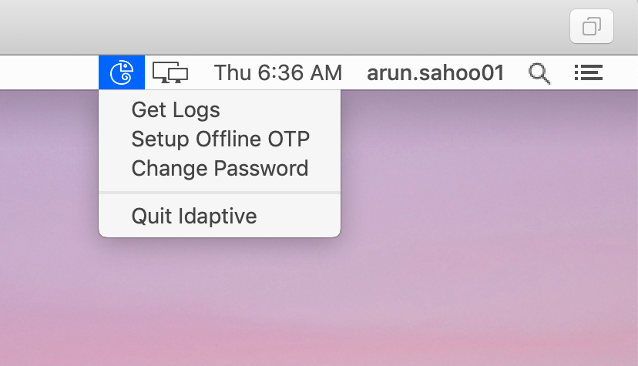
Streamlined password change
You can now enable users to easily change their passwords using an option in the Idaptive menu shown in the taskbar. With MCA deployed, users will now see the “change password” option, which allows them to change their directory password, keychain password, and Filevault password together. To add an extra layer of protection, administrators can require users to pass MFA challenges to proceed with password changes.
Additional features and improvements in the 20.2 release:
- Set a default background image for portal login: You can set a custom background image for your portal login screen.
- Microsoft Edge Idaptive Browser Extension: You can now enable SSO for username and password-based apps on the Edge Browser.
- Ability to resolve username conflicts in AD: You can now check if a user ID generated from the inbound provisioning attribute mapping script already exists in your target directory.
- Deploy custom iOS apps: You can now deploy custom iOS apps that are privately purchased and distributed using Apple’s Volume Purchase Program (VPP).
- Password expiration alerts: You can now enable email notifications of upcoming password expiration.
- Security event notifications: You can now automatically send email alerts to users when security events associated with their accounts are detected.
- Account lock after unsuccessful MFA authentication: You can now define the number of consecutive failed MFA challenge attempts, after which user accounts get locked.
- Support for multiple YubiKey for HOTP MFA: You can now allow users to use multiple YubiKeys for HOTP MFA authentication.
*** This is a Security Bloggers Network syndicated blog from Articles authored by Stas Neyman. Read the original post at: https://www.idaptive.com/blog/20-2-release-now-available/


