Insider Threats are on the Rise
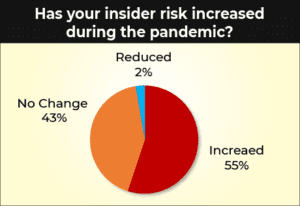
Insider threats are on the rise. The global pandemic has seen an exponential growth of cyberattacks targeting remote workers. This has dramatically impacted organizations worldwide as they struggle to maintain a secure working environment. With COVID-19, we have seen a dramatic increase in insider threats across the board, including malicious employees, accidental negligence, third party contractor or vendor misuse, and account compromise attacks. We’ve seen layoffs and reductions in work hours resulting in job dissatisfaction. Disgruntled employees can quickly turn into malicious actors looking for financial gain. The statistics aren’t encouraging. We need a better way to fight the rise of insider threats.
WSJ Survey Found 67% Of Companies Worry About Malicious Employees
In a recent Wall Street Journal Pro Research Survey of cybersecurity executives at nearly 400 companies, 67% said they were concerned about malicious employees. The results were published on Monday, June 22, 2020. The larger the company, the greater the concern about malicious insiders. Further, concern over the rise of insider threats grows to a greater degree than concern about other cybersecurity threats.
Percentage of respondents who consider the following actors to be cybersecurity threats:
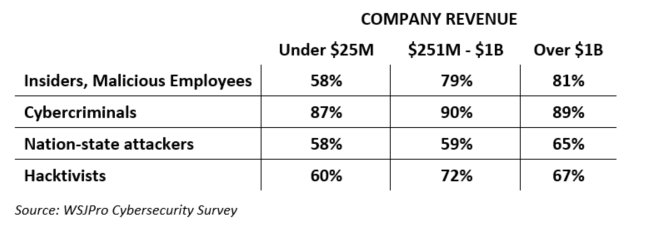
The publication also points out that companies are struggling with solutions to address the rise of insider threats. It is not easy to detect malicious employees before they exfiltrate data or IP. Behavioral analytics is one of the most successful technologies to proactively identify in real-time when an employee’s behavior differs enough to be suspect – to then be reviewed for corrective action.
DHS Expands Insider Threat Program
In other news, the Department of Homeland Security announced on June 16, 2020 that the agency is expanding its Insider Threat Program (ITP). The program will expand from those having access to classified materials to encompass, “all those with past or current access to DHS facilities, information, equipment, networks, or systems.”
Why do you think that is? As we’ve seen time and time again, the insider threat includes employees, partners, vendors, and contractors – past and present. The DHS found that the behavioral indicators it had been using to flag cases for additional analysis were created for a smaller population. They did not account for the expanded scope of the ITP. The historical trends and specific conduct missed critical insider access beyond the scope of the original ITP. This just proves the point that coverage is critical when it comes to predicting, detecting, and stopping the insider threat. The Edward Snowden case is an unforgettable reminder that organizations must include third party vendors and subcontractors in their insider threat programs. To combat the rise of insider threats, you need to implement comprehensive coverage to include the extended workforce and partner community.
The Enemy Within: How Insider Threats Are Changing
Gurucul was fortunate to participate on a recent Threatpost Webinar entitled, “The Enemy Within: How Insider Threats Are Changing.” During the webinar, the panelists discussed how to detect and prevent today’s insider-based malicious activity. With the rise in work from home cyberattacks, the conversation turned to how to address phishing scams, business email compromise, spoofing, and impersonation attacks.
Employee training and awareness is critical to overcoming the cybersecurity gaps heightened by the porous remote work perimeter. Technology plays a huge part as well. Once again, behavioral analytics takes center stage as a crucial weapon in the fight against insider threats. Behavior is the leading threat indicator when it comes to detecting malicious insider activity. Machine learning based behavior analytics has proven to successfully and continuously predict and stop insider threats in real-time.
Where Do We Go from Here?
There’s no doubt we will continue to see the rise of insider threats during this global pandemic. Best practices dictate we all need to pay closer attention to what we’re doing online with company data on personal devices, over WiFI networks. We also need to implement the right tools and technologies to bridge the gap between what we can and can’t control. We can’t control cybercriminals and they are incessantly leveraging COVID-19 in their account compromise, BEC and impersonation attacks.
Gurucul can help. We work with the Carnegie Mellon University CERT team on best practices for using threat intelligence to identify insider threat behavior patterns. Contact us for details.
The post Insider Threats are on the Rise appeared first on Gurucul.
*** This is a Security Bloggers Network syndicated blog from Blog – Gurucul authored by Jane Grafton. Read the original post at: https://gurucul.com/blog/insider-threats-are-on-the-rise