BlueLeaks: Putting Out an APB for Appropriate Password Policies
 In yet another blow to law enforcement, data belonging to over 200 police departments, some of which is highly sensitive, has been leaked online in the so-called BlueLeaks collection. The BlueLeaks data amounted to more than 270GB of information, and includes highly sensitive information including routing and bank account numbers, personally identifiable information, and even images of suspects.
In yet another blow to law enforcement, data belonging to over 200 police departments, some of which is highly sensitive, has been leaked online in the so-called BlueLeaks collection. The BlueLeaks data amounted to more than 270GB of information, and includes highly sensitive information including routing and bank account numbers, personally identifiable information, and even images of suspects.
The leak stems from a hack of NetSential, a web developer that works with multiple law enforcement agencies and “fusion centers,” which, according to the Department of Homeland Security, “are state-owned and operated centers that serve as focal points in states and major urban areas for the receipt, analysis, gathering and sharing of threat-related information between State, Local, Tribal and Territorial (SLTT), federal and private sector partners.”
NetSential’s web site is very outdated. Not necessarily a smoking gun in this case, but certainly cause for additional investigation of capabilities before engaging with such a vendor:
According to the National Fusion Center Association, Netsential has confirmed that this breach resulted from a compromised customer account. From that compromised account, the attackers used upload features in the platform to upload malicious content, which was how they were able to exfiltrate sensitive data from across Netsential’s customer base.
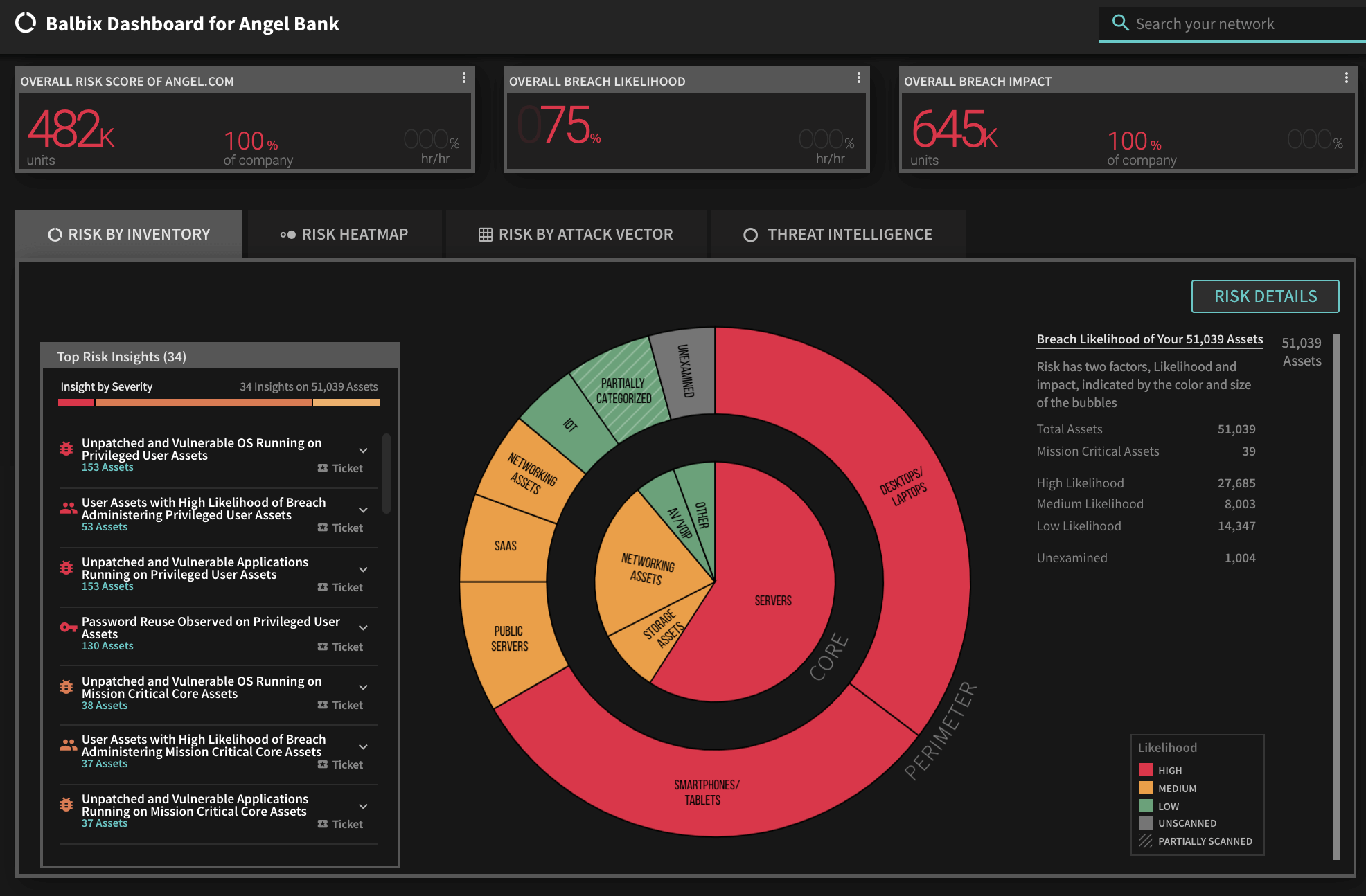
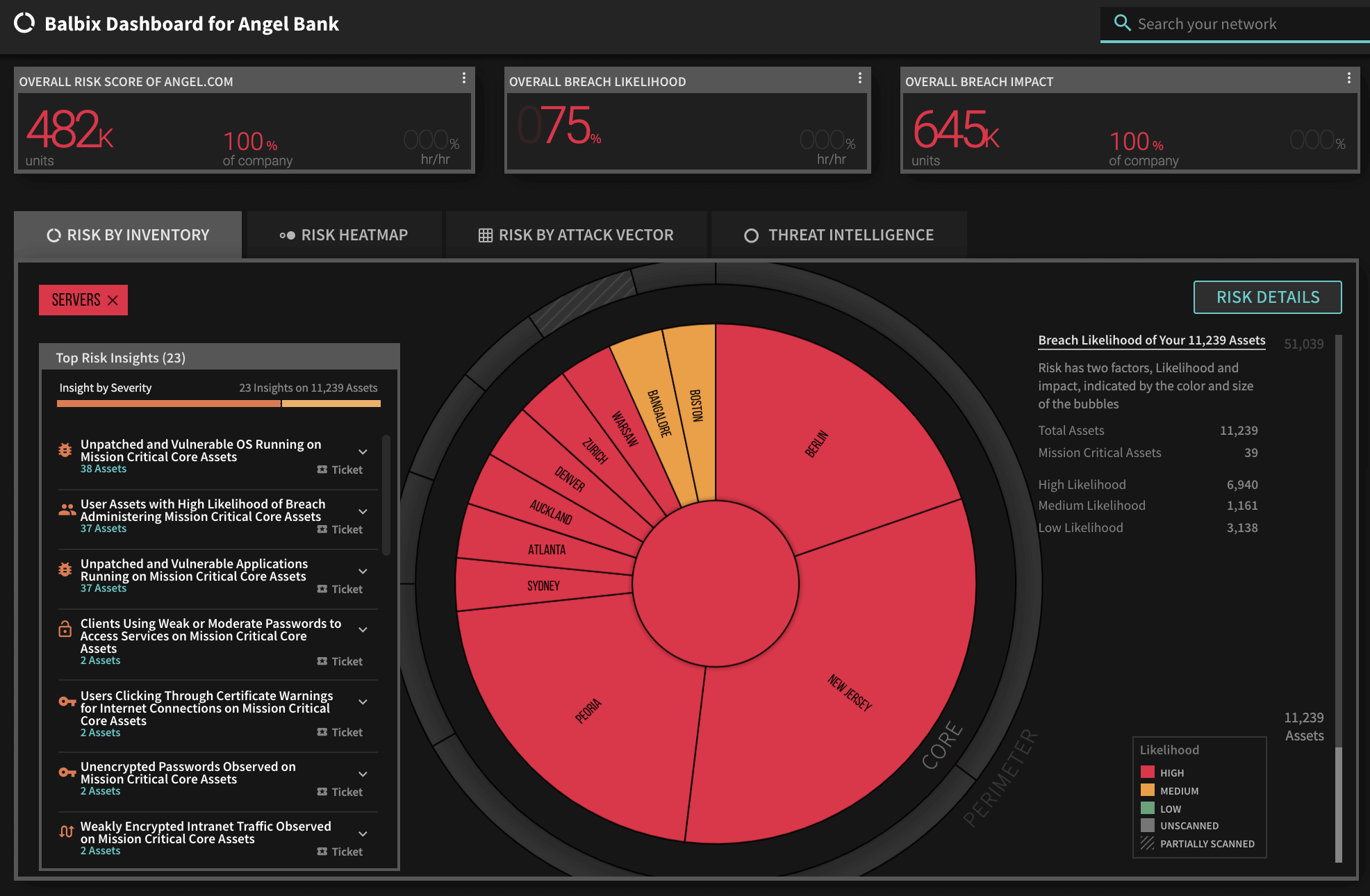
According to Vinay Sridhara, CTO of Balbix:
“While most police departments don’t have the internal expertise and resources to develop and maintain their own websites, this does speak to the importance of thoroughly vetting third party contractors, especially those handling sensitive data. In this case, basic, commonly accepted identity best practices could have thwarted the attack in question.
On average, every single password is shared across 2.7 accounts, and more than 99% of users reuse passwords across work and personal accounts. Sites handling such sensitive information must require multifactor authentication, amongst other measures to help reduce password reuse, such as requiring use of a password manager. In this case, both the individual departments and NetSential both failed to take such basic best practices into account, resulting in an embarrassing and harmful leak of sensitive data.”
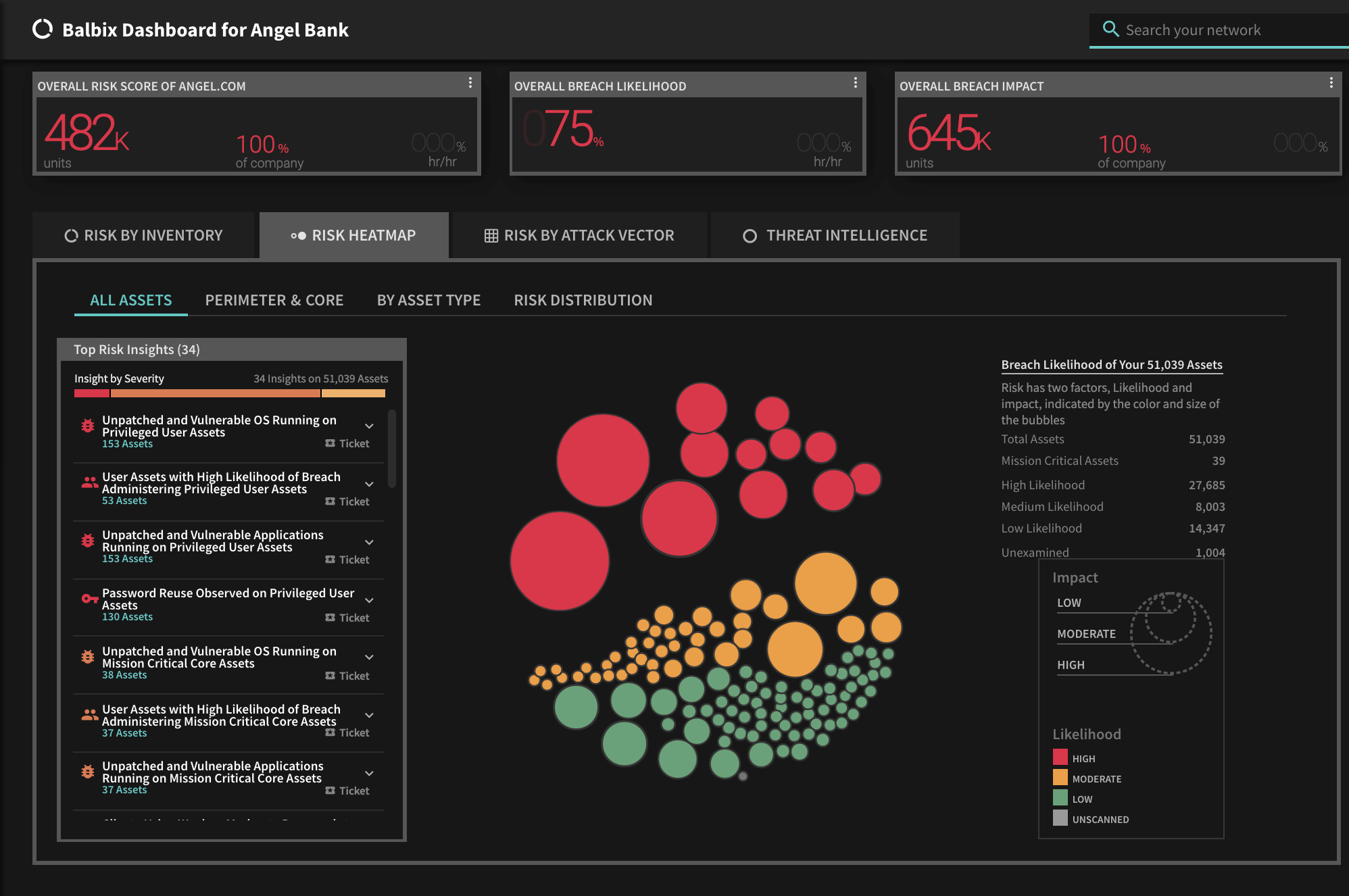
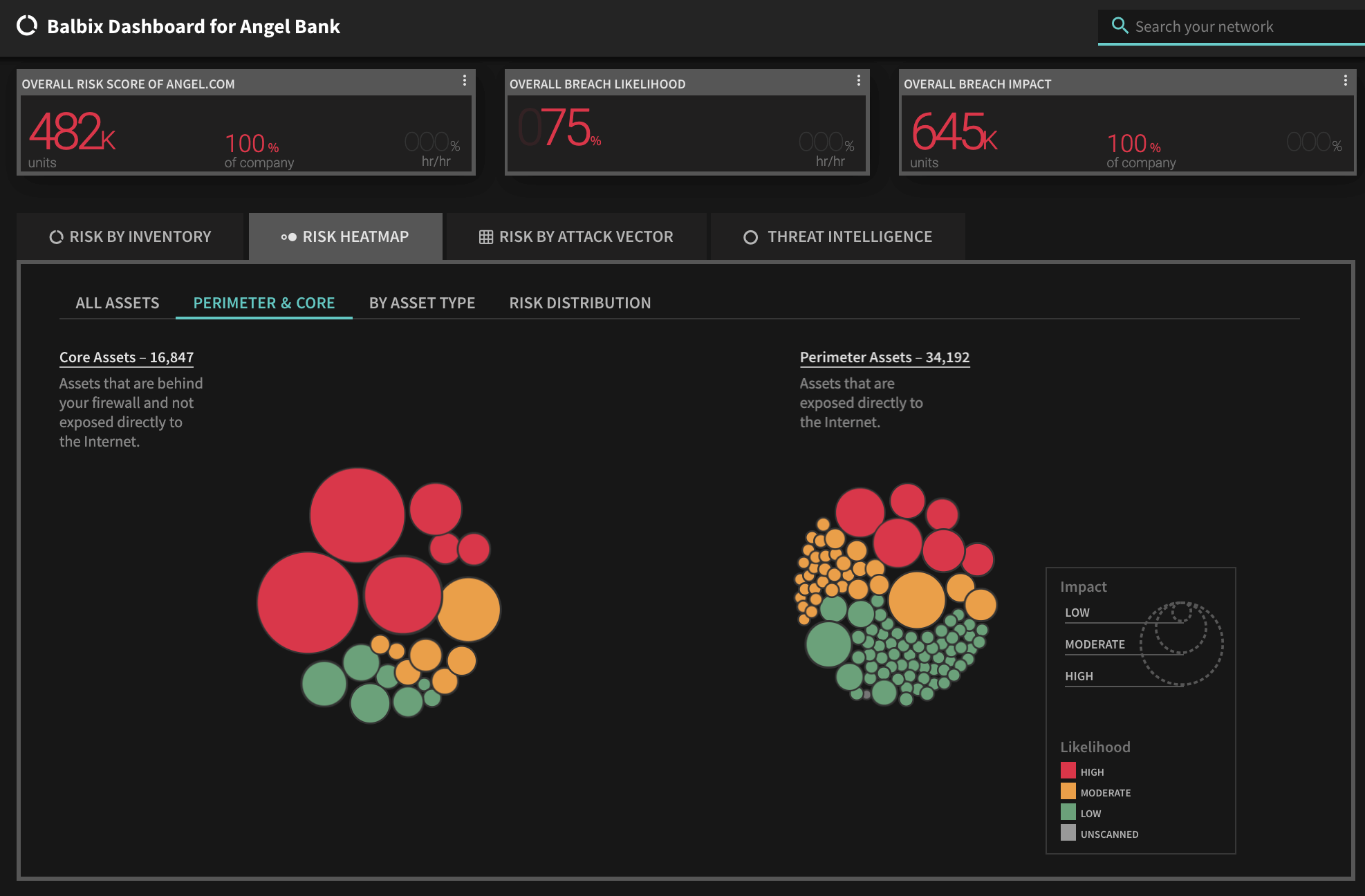
See Balbix Live
*** This is a Security Bloggers Network syndicated blog from Blog – Balbix authored by Rich Campagna. Read the original post at: https://www.balbix.com/blog/blueleaks-putting-out-an-apb-for-appropriate-password-policies/


