COVID-19 Shows the Importance of Protecting Availability
The ongoing effects of the coronavirus crisis are having a devastating impact on businesses worldwide. Whereas some industries are on the verge of collapse, other industries are experiencing sudden and exponential growth in demand for their services – and in turn, from their computing infrastructure.

If you’ve tried to use video conferencing, consult with your doctor remotely, or fill-out a government online application, you’ll know exactly what I’m talking about.
No Rest from the Wicked
Sadly, this difficult time offers no reprieve from cybercriminals, who are using this crisis as an opportunity to attack critical infrastructure.
Some examples from the past few weeks include:
- The US Department of Health and Human Service
(HHS) was hit
with a massive DDoS attack - Hospitals in France
and the Czech
Republic – including those responsible for COVID-19 testing – were attacked
by DDoS attacks which disrupted hospital systems - The Australian government announced its online
services portal – myGov – faced a significant
DDoS attack which prevented users from accessing it for several hours - A food delivery service in Germany faced
a bitcoin ransom attack which prevented it from providing food delivery
services to people unable to go out
[You may also like: How to Protect Your VPN: Lessons From a DDoS Attack Test]
At a time when customers, patients and citizens depend on the availability of critical services, attacks such as these emphasize the importance of safeguarding critical infrastructure, and in particular, guaranteeing availability during times of crisis.
Protecting Against DDoS Without Blocking Customers
One of the key tenets in guaranteeing service availability
is protecting against distributed denial of service (DDoS) attacks, such as the
ones mentioned above.
The challenge, however, is that DDoS protection requires answering a fundamental question: How do you block malicious traffic without blocking legitimate users?
Addressing this fundamental challenge is crucial, particularly in times such as the current crisis, when mission-critical applications are facing a surge of users who are in urgent need of their services.
[You may also like: Preserving Business Continuity During the Coronavirus Pandemic]
Smart DDoS Protection During COVID-19 Crisis
Behavioral detection
As the spikes in traffic for video conferencing software,
telemedicine services, and governmental websites demonstrate, organizations
need a way of distinguishing between malicious traffic and legitimate traffic
spikes.
The problem, however, is that looking just at raw traffic
rates doesn’t tell us whether that traffic is legitimate or malicious. For
example, the screenshot below compares a flash crows with a TCP RST Flood.
Using just a rate analysis, both requests look the same. However, a more detailed behavioral analysis of the packet behavior shows significant deviations of the malicious traffic from the established baseline of legitimate user behavior.
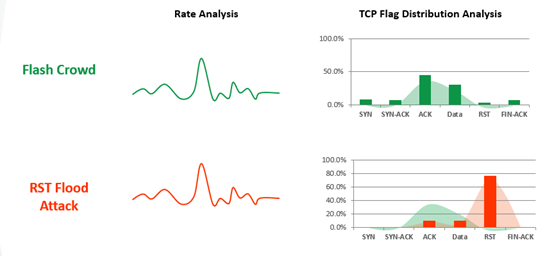
This is why it is crucial for anti-DDoS defenses to utilize not just volume-based detection, but also behavioral-based detection methods. In times of massive flash crowds, this is the only way of truly distinguishing between an attacker and a patient in need.
[You may also like: COVID-19: The Rise of the Telecommuter & the Impacts on Businesses]
Real-time signature
Albert Einstein said that “everything should be made as
simple as possible, but not simpler.” Paraphrasing that to the world of DDoS
protection, it means attack signatures should be tailored to the exact
characteristics of incoming attack traffic, but cover no more or less.
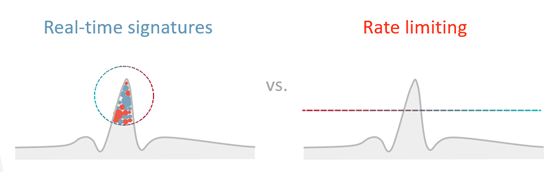
Apply a signature too narrowly, and it means that no attack traffic will be stopped; apply a signature that is too broad, and legitimate user traffic will be blocked, as well.
Traditional DDoS defenses are frequently based on rate limiting of incoming traffic, which reduces overall traffic volumes to a level that the service can withstand. The problem, however, is that rate limiting is a brute-force mechanism, which “caps off” traffic arbitrarily, but does not distinguish between legitimate and malicious traffic. This results in high degrees of false-positives, leading to legitimate users being blocked, while some malicious traffic still gets through.
A better approach uses real-time signature creation algorithms which are fine-tuned and optimized to the exact characteristics of attack patterns, meaning that malicious traffic – and only malicious traffic – will be blocked, while legitimate users, patients and customers will not be interrupted.
Encrypted attack protection
As more and more web traffic is encrypted, protection
against encrypted floods is a critical requirement for modern DDoS protection.
According to Google’s HTTPS Transparency Report, over 90% of web pages in
almost all major markets are now encrypted
by HTTPS.
This is especially applicable during the time of the coronavirus crisis, when many people are working remotely and share confidential financial details, work materials or patient data over secured connections.
Ironically, while HTTPS is crucial for data protection, it
also opens the door for a new breed of devastating DDoS attacks. HTTPS is a
highly asymmetric protocol, and the SSL handshake process may take as much as 15
times more resources from the target server than from the host making the
request. As a result, hackers can use HTTPS floods to create devastating
attacks with a relatively small number of requests.
This is why protection against encrypted DDoS floods is a critical requirement for modern DDoS protection.
Massive global capacity
Another critical requirement to safeguard the availability
of critical services is massive, dedicated DDoS mitigation capacity.
IoT botnets are constantly getting larger and more
sophisticated, and are capable of launching larger attacks than ever. For
example, a recent study by researchers at Ben Gurion University (BGU) in Israel
showed how a mid-sized botnet with as few as 6,000 nodes can bring down the
emergency 911 system of an average US state, and how 200,000 bots can
jeopardize the entire United States.
Naturally, such vulnerabilities are critical during a
massive public health emergency such as the COVID-19 crisis.
[You may also like: Coronavirus: Its Four Most Prevalent Cyber Threats]
The solution to that is relying on a globally-distributed DDoS scrubbing network with multi-terabit, dedicated capacity for DDoS mitigation, to guarantee you always have enough fallback capacity.
Managed security service
Finally, the last critical requirement for modern DDoS protection is a fully-managed security service. Staff shortages and the cybersecurity skill-gap are crucial problems on a routine basis, but these challenges are exacerbated during this time of crisis, when IT teams are overextended, many employees are working from home, and some might even be affected by lock downs, isolation, or hospitalization.
Using a fully-managed security service for DDoS protection helps
take the burden off your shoulders by relying on teams of experts for whom
network and application security is their expertise. This enables IT teams to
free-up their bandwidth to focus on their core tasks, and leave security
management to the experts.
*** This is a Security Bloggers Network syndicated blog from Radware Blog authored by Eyal Arazi. Read the original post at: https://blog.radware.com/security/ddos/2020/03/covid-19-shows-the-importance-of-protecting-availability/