Security researcher publicly releases second Steam zero-day after being banned from Valve’s bug bounty program
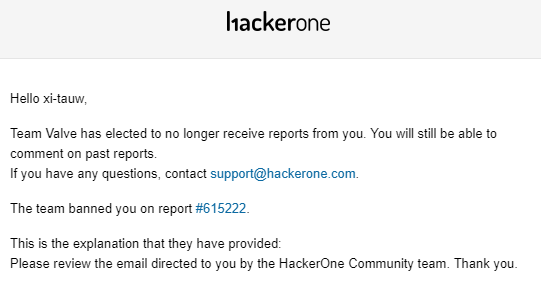
A Russian security researcher, Vasily Kravets, has found a second zero-day vulnerability in the Steam gaming platform, in a span of two weeks. The researcher said he reported the first Steam zero-day vulnerability earlier in August, to its parent company, Valve, and tried to have it fixed before public disclosure. However, “he said he couldn’t do the same with the second because the company banned him from submitting further bug reports via its public bug bounty program on the HackerOne platform,” ZDNet reports.
Source: amonitoring.ru
This first flaw was a “privilege-escalation vulnerability that can allow an attacker to level up and run any program with the highest possible rights on any Windows computer with Steam installed. It was released after Valve said it wouldn’t fix it (Valve then published a patch, that the same researcher said can be bypassed),” according to Threatpost.
Although Kravets was banned from the Hacker One platform, he disclosed the second flaw that enables a local privilege escalation in the Steam client on Tuesday and said that the flaw would be simple for any OS user to exploit. Kravets told Threatpost that he is not aware of a patch for the vulnerability.
“Any user on a PC could do all actions from exploit’s description (even ‘Guest’ I think, but I didn’t check this). So [the] only requirement is Steam,” Kravets told Threatpost. He also said, “It’s sad and simple — Valve keeps failing. The last patch, that should have solved the problem, can be easily bypassed so the vulnerability still exists. Yes, I’ve checked, it works like a charm.”
Another security researcher, Matt Nelson also said he had found the exact same bug as Kravets had, which “he too reported to Valve’s HackerOne program, only to go through a similar bad experience as Kravets,” ZDNet reports. He said both Valve and HackerOne took five days to acknowledge the bug and later refused to patch it. Further, they locked the bug report when Nelson wanted to disclose the bug publicly and warn users.
“Nelson later released proof-of-concept code for the first Steam zero-day, and also criticized Valve and HackerOne for their abysmal handling of his bug report”, ZDNet reports.
The company at fault here is Valve (Steam). Good luck reporting anything that doesn’t fit their crappy bounty scope. https://t.co/vLHmTQ0qmq
— Matt Nelson (@enigma0x3) July 8, 2019
“Despite any application itself could be harmful, achieving maximum privileges can lead to much more disastrous consequences. For example, disabling firewall and antivirus, rootkit installation, concealing of process-miner, theft any PC user’s private data — is just a small portion of what could be done,” said Kravets.
Kravets demonstrated the second Steam zero-day and also detailed the vulnerability on his website.
Per Threatpost, “Valve did not respond to a request for comment about the vulnerability, bug bounty incident and whether a patch is available. HackerOne did not have a comment.”
Other researchers who have participated in Valve’s bug bounty program are infuriated over Valve’s decision to not only block Kravets from submitting further bug reports, but also refusing to patch the flaw.
i am disappointed that valve does this kinda stuff https://t.co/z1JPKJmHhQ
— D̒͂̕ᵈăᵃn̕ᶰ Ť̾̾̓͐͒͠ᵗe͗̑́̋̂́͡ᵉn̅ᶰtᵗl̀̓͘ᶫe̓̒̂̚ᵉrʳ (@Viss) August 21, 2019
Researcher: Valve, there’s an EoP flaw, you should fix.
Valve: Not flaw, no patch
Researcher: Ok, fine, here’s a PoC world
Valve/HackerOne: Oh no, why’d you go and release a EoP flaw #BanHammer
Pretty disappointing behavior by @steam_games and @Hacker0x01 here. :/ https://t.co/TFyqqk5LEJ
— Scott the KamenRunner @ #HackerSummerCamp (@kamenrannaa) August 22, 2019
A user on Reddit writes, “If management isn’t going to take these issues seriously and respect a bug bounty program, then you need to bring about some change from within. Now they are just getting bug reports for free.”
To know more about this news in detail, read Kravets’ blog post. You could also check out Threatpost’s detailed coverage.
Read Next
Puppet launches Puppet Remediate, a vulnerability remediation solution for IT Ops
*** This is a Security Bloggers Network syndicated blog from Security News – Packt Hub authored by Savia Lobo. Read the original post at: https://hub.packtpub.com/security-researcher-publicly-releases-second-steam-zero-day-after-being-banned-from-valves-bug-bounty-program/


