OpenSSL 3.0 will have significant changes in architecture, will include FIPS module and more
On 13th February, the OpenSSL team released a blog post outlining the changes that users can expect in the OpenSSL 3.0 architecture and plans for including a new FIPS module.
Architecture changes in OpenSSL 3.0
- ‘Providers’ will be introduced in this release which will be a possible replacement for the existing ENGINE interface to enable more flexibility for implementers. There will be three types of Providers: the “default” Provider will implement all of the most commonly used algorithms available in OpenSSL. The “legacy” Provider will implement legacy cryptographic algorithms and the “FIPS” Provider will implement FIPS validated algorithms.
- Existing engines will have to be recompiled to work normally and will be made available via both the old ENGINE APIs as well as a Provider compatibility layer.
- The architecture will include Core Services that will form the building blocks usable by applications and providers.
- Providers in the new architecture will implement cryptographic algorithms and supporting services. It will have implementations of one or more of the following:
- The cryptographic primitives (encrypt/decrypt/sign/hash etc) for an algorithm
- Serialisation for an algorithm
- Store loader back ends
- A Provider may be entirely self-contained or it may use services provided by different providers or the Core Services.
- Protocol implementations, for instance TLS, DTLS.
- New EVP APIs will be provided in order to find the implementation of an algorithm in the Core to be used for any given EVP call.
- Implementation agnostic way will be used to pass information between the core library and the providers.
- Legacy APIs that do not go via the EVP layer will be deprecated.
- The OpenSSL FIPS Cryptographic Module will be self-contained and implemented as a dynamically loaded provider.
- Other interfaces may also be transitioned to use the Core over time
- A majority of existing well-behaved applications will just need to be recompiled. No deprecated APIs will be removed in this release
You can head over to the draft documentation to know more about the features in the upgraded architecture.
FIPS module in OpenSSL 3.0
- The updated architecture incorporates the FIPS module into main line OpenSSL. The module is dynamically loadable and will no longer be a separate download and support periods will also be aligned.
- He module is a FIPS 140-2 validated cryptographic module that contains FIPS validated/approved cryptographic algorithms only.
- The FIPS module version number will be aligned with the main OpenSSL version number.
- New APIs will give applications greater flexibility in the selection of algorithm implementations.
- The FIPS Provider will implement a set of services that are FIPS validated and made available to the Core. This includes:
- POST: Power On Self Test
- KAT: Known Answer Tests
- Integrity Check
- Low Level Implementations
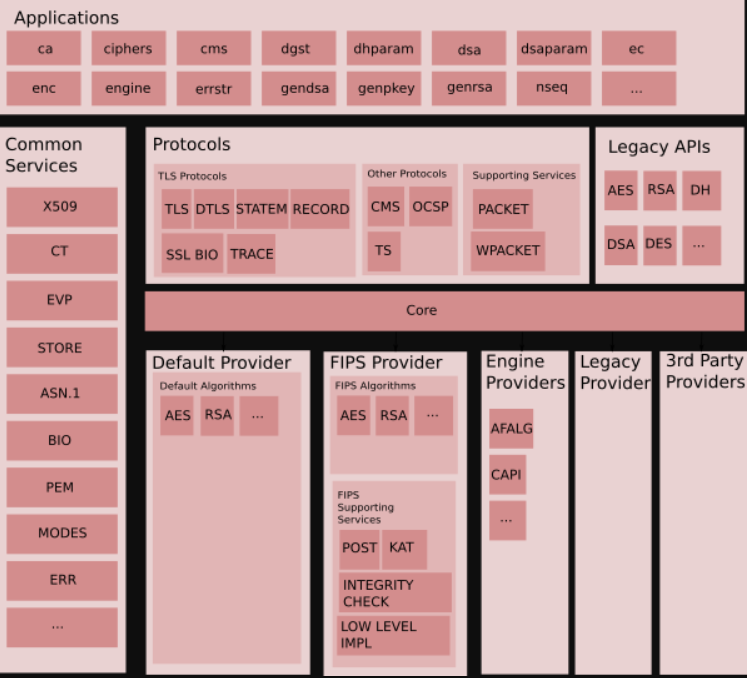
Conceptual Component View of OpenSSL 3.0
Read the draft documentation to know more about the FIPS module in the upgraded architecture.
Read Next
Baidu Security Lab’s MesaLink, a cryptographic memory safe library alternative to OpenSSL
OpenSSL 1.1.1 released with support for TLS 1.3, improved side channel security
Transformer-XL: A Google architecture with 80% longer dependency than RNNs
*** This is a Security Bloggers Network syndicated blog from Security News – Packt Hub authored by Melisha Dsouza. Read the original post at: https://hub.packtpub.com/openssl-3-0-will-have-significant-changes-in-architecture-will-include-fips-module-and-more/

