Spear-Phishing: The Smart Malware
Protecting your organization from phishing has never been more important. In this blog, I examine a particularly smart phishing mechanism called spear-phishing, which is increasingly becoming popular, mainly because it’s irresistibly clickable. And that is because it is expertly fine-tuned to target “you.” [Read my earlier blog — Gone Phishing: Everything You Need to Know About the Ever Present Threat to Your Data — for practical advice on how to protect your organization from being another phish in the sea.]
Rationale Behind Spear-Phishing
Using sophisticated background research, hackers craft the phishing email to hone in on (or spear) specific individuals within an organization. With its advanced bait, hackers take the phish many notches higher, and are consequently looking for a larger return.. They go to great lengths to personalize the message — a complaint from the Better Business Bureau, a vendor cancelling a shipment, a “we’re being sued” email from the legal department, or even a note from the CEO. All designed to encourage the employee to make the fatal click to steal their identity, or worse still to worm its way into the organization’s network to either install malware or to deceive employees to wire funds to the hacker’s account.
Examples of Spear-Phishing Hurting the Organization
The 2018 Phishing Trends & Intelligence Report warns that hackers are “switching from primarily targeting individuals to targeting organizations.” And spear-phishing makes for the perfect vector. Here are some examples, that showcase how intelligent “social engineering” can make even highly-secure organizations susceptible to spear-phishing.
- Spear-phishing attacks against organizations have become common enough for the FBI to release a public service announcement warning against Business Email Compromise. This was back in 2015, when tech firm Ubiquiti suffered a $46M Cyberheist that was triggered by spear-phishing — “employee impersonation and fraudulent requests from an outside entity targeting the Company’s finance department.”
- This spear-phish attack cleverly intercepted chat messages with highly customized messages, so the targets were tricked into believing that they were still chatting with their original contact. Once in the network, the hackers infiltrated several organizations; including a Middle Eastern bank, an European intellectual services firms, and an international sporting organization.
- The federal indictment for the 2017 WannaCry ransomware attack and the attack on Sony Pictures Entertainment, called out “spear-phishing” as the main mode of attack. The hackers used “online reconnaissance” to craft ingenious emails that impersonated recruiters at competing defense contractors, connected with targets on their social media accounts and fraudulently authenticated SWIFT interbank messaging platform messages to transfer $81 million from a Bangladeshi bank, amongst other hacks.
Safeguarding the Organization Against Spear-Phishing
Common safeguards against phishing, like spam traps, may not be effective against spear-phishing as they are not mass e-mailed. Furthermore, spear-phishing attacks like the “Business Email Compromise,” dodge banking security checks for account takeovers, as attackers are not interacting with the bank, rather it is the very employee that has been swindled. Educating and training the employee is at the core of safeguarding the organization against such attacks.
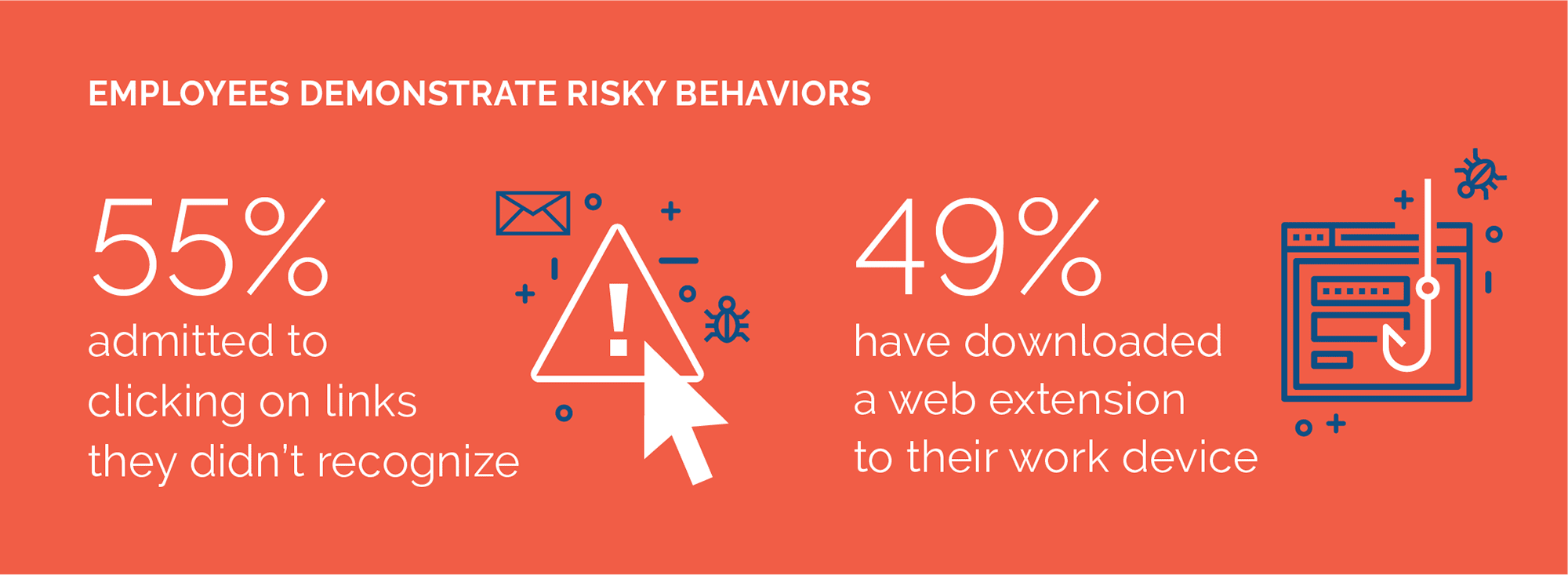
Glaring examples of top tech companies and government organizations, that have all the technical security measures in place, being made victims of phishing scams underscore that hi-tech security solutions can only do this much. Ultimately the employee can either be the weakest or strongest link in protecting your organization. Here are the top four things you should do now to protect your organization from spear-fishing:
- Train all Employees, Including the C-Suite, About Email Red Flags: Train employees to sniff out signs of fraudulent emails — check the sender’s email (not just the name), verify the URL link and call/email the sender’s directly if the email demands an urgent response or requests personal information. Only 36% of all employees polled, correctly identified a suspicious link as being the key indicator of a phishing email in a recent report by Spanning, Trends in U.S. Worker Cyber Risk-Aversion and Threat Preparedness.
- Encourage High-level Executives to Not Give Out Personal Information: Use regular awareness training to remind executives to be extremely vigilant about sharing personal information online, especially on social media. LinkedIn profiles are particularly fertile ground for hackers to get valuable spear-phishing information.
- Formulate a Phishing Response Procedure: Curbing an attack at the earliest will prove critical to reducing its damage and getting your organization back on its feet. Urge employees to report an attack and have an immediate action plan to stem the tide — reset passwords, scan the network, notify employees, customers, etc.
- Backup Your Data for Easy Data Recovery: Backing up your data reliably, including SaaS data like Office 365 and G Suite, so that you can recover data quickly and accurately post an attack helps ensure Business Continuity — an important aspect of organizational recovery. Attacks can lose their sting with the safety net of a solid backup and recovery solution that restores your data just as it was before.
Learn Why You Need to Backup Your SaaS Data
*** This is a Security Bloggers Network syndicated blog from Spanning authored by Brian Rutledge. Read the original post at: https://spanning.com/blog/spear-phishing-smart-malware/

