Juniper Networks: Cryptomining Exploit Targeting Docker Containers
Juniper Networks revealed today cybercriminals are now employing Docker containers to surreptitiously run cryptomining malware on public clouds.
Researchers at Juniper Threat Labs have discovered an infection in the wild that hunts for misconfigured publicly exposed Docker services in the cloud, which it then infects with containers running Monero miners.
Mounir Hahad, head of Juniper Threat Labs, said cybercriminals are trying to take advantage of lax authentication to use a cloud service to generate digital currency that winds up getting billed to the IT organization that contracted the public cloud service.
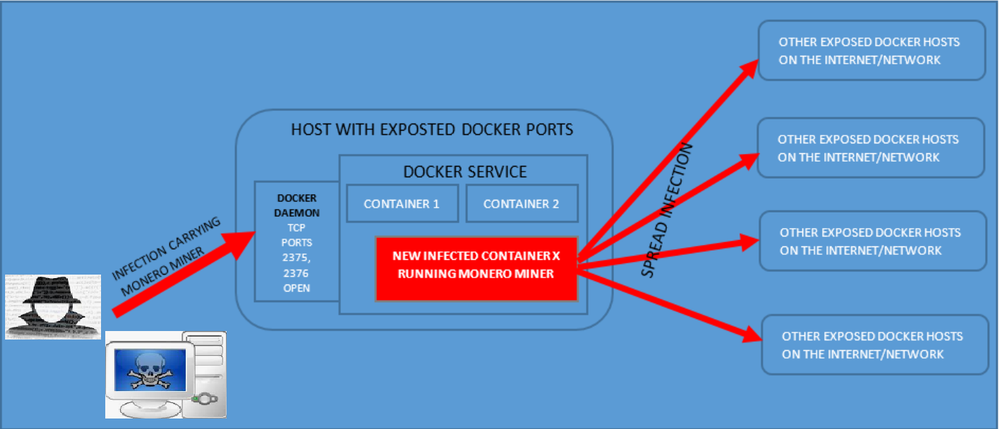
Hahad said the infection his team discovered spreads across hosts using misconfigured or loosely configured Docker services that expose its REST Management application programming interfaces (APIs) through open and unauthenticated TCP ports 2375 and 2376 on the internet. Each new infection continues to spread the infection to other new hosts by scanning for the presence of other misconfigured Docker hosts on the network.
Docker provides REST APIs for management of its service, including the ability to create and start/stop containers. By default, Docker only enables Unix socket access to its REST APIs. To enable remote access to the Docker service’s REST APIs, there is a need to configure Docker to listen on TCP ports. The conventional ports used by Docker are 2375 and 2376, which by default provide unencrypted and unauthenticated access to the docker REST APIs.
Juniper reports the entire infection chain is largely script-based and makes use of well-known utilities to spread the infection, including Docker, Wget, cURL, Bash, iproute2, MASSCAN, apt-get, yum, up2date, pacman, dpkg-query and systemd.
Hahad said Juniper Networks expects to see more organizations become victimized by these attacks because cloud services are often spun up with little to no oversight by an internal IT organization. Many developers don’t realize that the Docker containers they are spinning up are exposed via an external network; they assume that application they spun up is only visible on an internal network, he said.
As use of Docker containers continues to increase, it’s clear they are now on the radar screens of cybersecurity. In fact, Hadad noted that almost every emerging technology goes through a cycle during which cybercriminals learn to exploit it until enterprise IT organizations become savvy enough to eliminate the vulnerability to the point at which hackers lose interest in that exploit.
Of course, authentication issues on public clouds is not anything new. Too many developers still assume the cloud service provider is protecting their application. Cloud service providers are committed to securing their own infrastructure. But customers are on their own when it comes to securing their cloud applications. The challenge many of them will face as they embrace containers is that the number of things that need to be secured increases exponentially when thousands of containers that make up an application based on microservices get deployed. Previously, organizations were finding it hard enough to secure monolithic applications in the cloud.
In the meantime, cybersecurity issues are not likely to discourage developers from employing containers to build and deploy applications. But as reports of cloud services being compromised by containers increase, they hopefully will learn to invoke cloud services with greater care.