Reverse Engineering Proprietary ICS Protocols
One of the highlights at this year’s
SEC-T conference in Stockholm was
Steve Miller’s talk titled
“Reversing the TriStation Network Protocol“.
In this talk Steve covered his quest to better understand the TRITON malware,
which had been used in a targeted attack of an industrial control system (ICS).
Steve didn’t disclose the type or location of the plant, saying “Don’t ask me who it was, ‘cause I can’t say”
when the Q&A started. However, an
article in the Wall Street Journal
points out that it was a petrochemical plant in Saudi Arabia that had been hacked.
Targeting Safety Instrumented System
The TRITON malware (also called TRISIS) was used to target a safety instrumented system (SIS)
from Schneider Electric called Triconex. A SIS is typically not used to control the process of a plant,
but rather to detect abnormal operating conditions and safely shut down the industrial process if needed.
I could elaborate a lot regarding the consequences of attacking the SIS, but the good guys from Dragos have already
done a great job explaining this in their
“TRISIS Malware” report.
Reverse Engineering the ICS Protocol
The communication protocol used by the Triconex controllers is called TriStation, which is a proprietary protocol.
This means that there were no publicly available specifications available for the protocol at that time.
There was also no Wireshark dissector that could parse TriStation traffic. Nevertheless, Steve’s initial reaction
to this was “Awesome, undocumented things are my favorite things!”

Unfortunately Steve wasn’t able to get hold of a single PCAP file with the TriStation network protocol,
which made it really difficult to reverse engineer the protocol implementation in the TRITON malware.
The only piece of actual TriStation network traffic he was able to get hold of was a hex dump of a TriStation packet in an
academic paper.
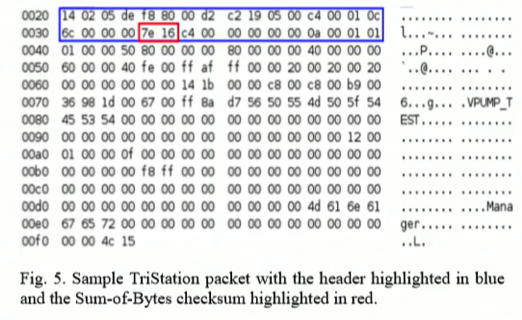
Armed with only the hexdump and Wireshark’s
text2pcap Steve managed to piece together an
actual PCAP file containing a single frame with a TriStation packet inside.
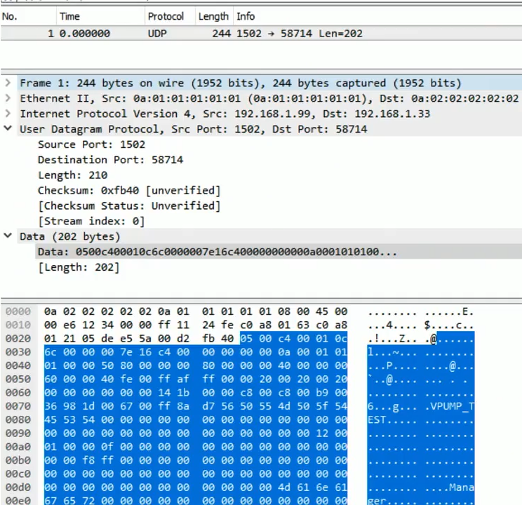
As you can see in the image above, Wireshark doesn’t decode any of the application layer data coming from
TCP port 1502 (which TriStation uses). He therefore implemented a Wireshark
Lua dissector for the TriStation protocol.
And some time later the people from Nozomi Networks even implemented a proper
Wireshark dissector for the TriStation protocol.
BSI’s ICS-SEC team have now also created
Snort IDS rules specifically for the TriStation protocol.
These IDS rules trigger on events like:
- Packets sent to the controller from an unauthorized host
- Malicious commands used by the TRITON malware to read and write to the RAM of the SIS controller as well as to execute code
The Importance of Sniffing ICS Traffic
I’ve been trying to convince asset owners, who use ICS in their power plants, factories,
water treatment facilities etc, to start
capturing the network traffic and storing it as PCAP files
for many years now. However, asset owners sometimes try to argue that there is no point in capturing their traffic since
it is using a proprietary protocol. Even Ralph Langner has opposed to the idea of capturing ICS network traffic in
a blog post,
which I have criticized.
So, how difficult is it to write a parser for a proprietary protocol?
I have personally implemented support for over 30 application layer protocols in
NetworkMiner,
but unlike Steve I’ve always had access to at least one PCAP file and some form of documentation of the protocol.
However, I’ve found that many real-world protocol implementations don’t follow specifications properly.
In these cases I’ve found that having access to PCAP files with real-world network traffic is more
important than having a full protocol specification.
Even complex proprietary protocols like the old proprietary Skype protocol
has been reverse engineered,
so with access to network traffic of a protocol combined with a binary that uses this protocol I’d say that
pretty much any network protocol can be reverse engineered.
Steve’s SEC-T talk also proves that ICS protocols are no different,
since they too can be reverse engineered without having a protocol specification or RFC.
Capturing network traffic in ICS networks is never wrong. There might not be parsers available today for
all the protocols you’re using. But once a parser or IDS signature becomes available for the protocol you’re using,
you can simply use that to analyze previously captured network traffic from your ICS network.
Also, in the wake of an incident you might actually end up writing a parser (as in the TRITON case)
or a custom IDS rule, in which case having historical network traffic from your plant in invaluable!
For more information on this topic I’d suggest reading my blog post titled
“Monitor those Control System Networks!” from 2011,
which still is highly relevant.
I’m also happy to announce that two PCAP files containing TriStation network traffic have been linked from our
list of publicly accessible PCAP files today
(see the “SCADA/ICS Network Captures” section).
And remember: PCAP or it didn’t happen!
 Share on Facebook
Share on Facebook  Tweet
Tweet  Submit to reddit.com
Submit to reddit.com
*** This is a Security Bloggers Network syndicated blog from NETRESEC Network Security Blog authored by Erik Hjelmvik. Read the original post at: http://www.netresec.com/?page=Blog&month=2018-09&post=Reverse-Engineering-Proprietary-ICS-Protocols

