NetworkMiner 2.3 Released!
The free and open source network forensics tool NetworkMiner now comes with improved extraction of files
and metadata from several protocols as well as a few GUI updates.
But the biggest improvements for version 2.3 are in the commercial tool NetworkMiner Professional,
which now supports VoIP call audio extraction and playback as well as OSINT lookups of file hashes,
IP addresses, domain names and URLs.
I’m happy to announce that NetworkMiner 2.3 now does an even better job than before at extracting files
and metadata from several protocols. Improvements have been made in the parsers for the following protocols:
HTTP, IEC-104, IPv4, Modbus, SIP, SMB, SMB2, SMTP and SSL/TLS.
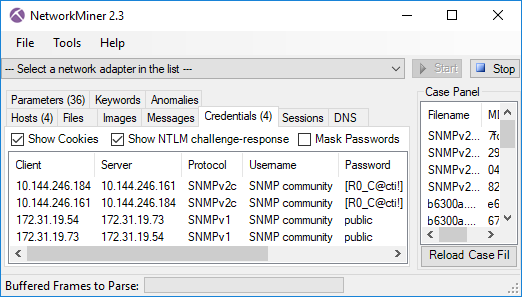
We have also added support for the SNMP protocol in NetworkMiner 2.3,
so that SNMP community strings can be extracted and displayed on the Parameters and Credentials tabs.
Another change is that timestamps are now displayed using the UTC time zone instead of using the local time zone.
We have also fixed a few GUI quirks in order to further improve the usability of the tool.
NetworkMiner Professional
The commercial version of NetworkMiner, i.e. NetworkMiner Professional,
comes with several additional improvements which are presented below.
VoIP Call Playback
NetworkMiner Professional has received a new tab called “VoIP”,
which enables audio playback of VoIP calls that are using SIP and RTP with G.711 μ-law or A-law encoding
(u-Law is primarily used in North America and Japan while A-law is used in Europe and most other parts of the world).
Video: Audio playback and extraction to WAV from the “SIP_CALL_RTP_G711” PCAP file in the
Wireshark Sample Captures.
The audio streams from the VoIP calls are also extracted to disk as .WAV files when codecs
G.729 or
G.711
(u-Law and A-Law) is used. NetworkMiner Professional also attempts to reassemble RTP streams encoded with
G.722 to .au files.
OSINT Lookups of IP Addresses, Domains, URLs and File Hashes
Right-clicking a network host in NetworkMiner Professional’s Hosts tab brings up a context menu with options for performing lookups of IP
and domain names using external sources. We refer to this method as open-source intelligence (OSINT) because the accessed data resides at
publicly available sources.
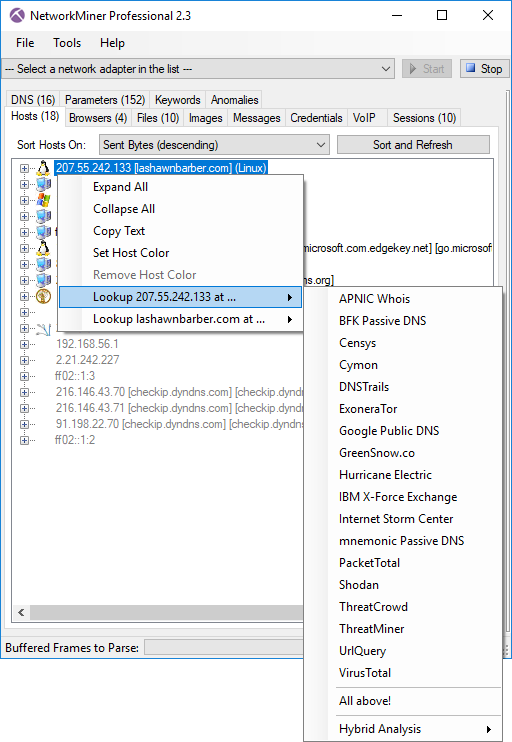
Clicking on an OSINT provider brings up a webpage with more detailed information about the selected IP address, such as
IBM X-Force,
mnemonic Passive DNS,
Shodan,
UrlQuery or
VT.
However, if you’re lazy like me, then you’ll probably click the “All above!” option instead,
which will bring up all of the sources in separate tabs in your browser.
The full list of OSINT providers available for IP lookups includes
APNIC Whois, BFK Passive DNS,
Censys,
Cymon,
DNSTrails,
ExoneraTor, Google Public DNS, GreenSnow.co, Hurricane Electric, IBM X-Force, Internet Storm Center, mnemonic Passive DNS,
PacketTotal,
Shodan,
ThreatCrowd,
ThreatMiner,
UrlQuery and VirusTotal.
The domain name lookup menu contains a similar set of providers:
BFK Passive DNS, Cymon,
DNSTrails, Google Public DNS, Google Safe Browsing,
Hybrid Analysis, IBM X-Force Exchange, mnemonic Passive DNS,
MXToolBox, MyWOT, Norton Safe Web,
PacketTotal,
ThreatCrowd,
ThreatMiner,
URL Void, UrlQuery, VirusTotal, Website Informer, Webutation and Whoisology.
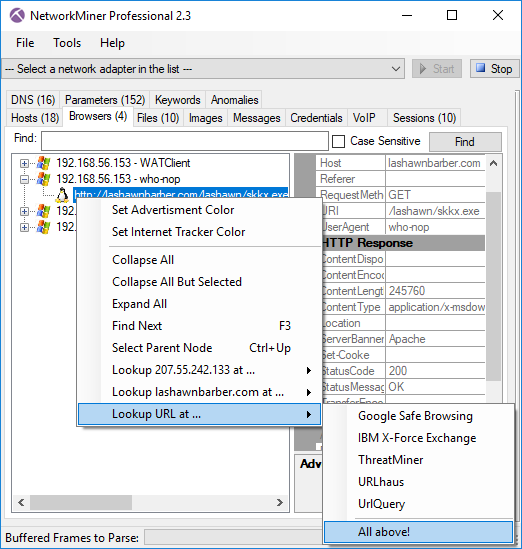
Right-clicking a URL in the Browsers tab brings up a similar context menu, which additionally includes the following services for URL lookups:
Google Safe Browsing, IBM X-Force,
ThreatMiner,
URLhaus and
UrlQuery.
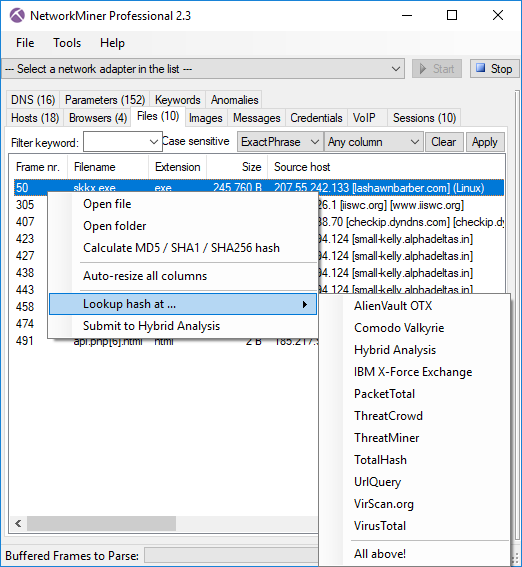
Finally, right-clicking on one of the files that NetworkMiner has extracted from a PCAP file brings up a menu for doing OSINT lookups based on
the MD5 or SHA256 hash of the file. The sources used for lookups of hashes include IBM X-Force,
PacketTotal,
ThreatCrowd,
TotalHash,
UrlQuery, VirScan.org, Comodo Valkyrie,
AlienVault OTX,
Hybrid Analysis,
ThreatMiner and VirusTotal.
Hybrid Analysis API Integration
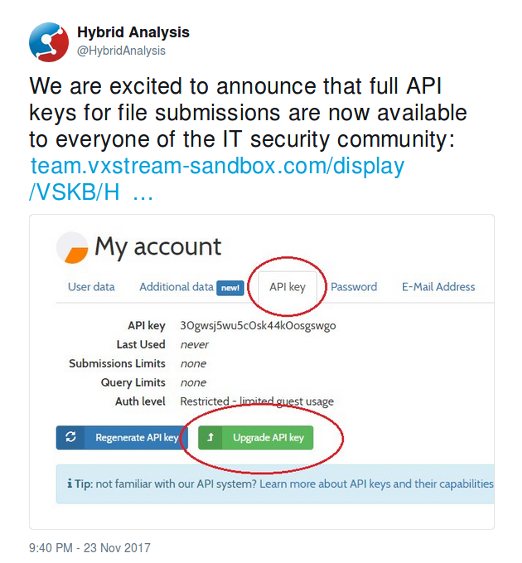
Did you know that the malware analysis service Hybrid Analysis provides free API keys to people in the IT security community?
This is a great move by the Hybrid Analysis team, and we’re happy to announce that we have leveraged their API in NetworkMiner Professional
in order to submit files for analysis directly from within the NetworkMiner GUI.
The API integration also enables you to query for an IP on Hybrid Analysis to see which previously submitted samples has communicated
with that particular IP address.
Here are the steps required to enable the Hybrid Analysis API integration:
- Create a HybridAnaysis account
- Create an API key
- Upgrade the API key by completing a vetting process
- Start NetworkMiner Pro, open the Tools > Settings menu and input your API key
Credits
I would like to thank
Chris Sistrunk, Mats Karlsson and Mikael Nilsson for suggesting several of the protocol and GUI improvements
that have been incorporated into this new release. I’d also like to thank Doug Green and Ahmad Nawawi for discovering and reporting a bugs in the
IP and SSL parser respectively.
Upgrading to Version 2.3
Users who have purchased a license for NetworkMiner Professional 2.x can download a free update to version 2.3 from our
customer portal.
Those who instead prefer to use the free and open source version can grab the latest version of NetworkMiner from the official
NetworkMiner page.
⛏ FOR GREAT JUSTICE! ⛏
 Share on Facebook
Share on Facebook  Tweet
Tweet  Submit to reddit.com
Submit to reddit.com
*** This is a Security Bloggers Network syndicated blog from NETRESEC Network Security Blog authored by Erik Hjelmvik. Read the original post at: http://www.netresec.com/?page=Blog&month=2018-04&post=NetworkMiner-2-3-Released