Weekly Cyber Risk Roundup: Russia Sanctions, Mossack Fonseca Shutdown, Equifax Insider Trading
On Thursday, the U.S. government imposed sanctions against five entities and 19 individuals for their role in “destabilizing activities” ranging from interfering in the 2016 U.S. presidential election to carrying out destructive cyber-attacks such as NotPetya, an event that the Treasury department said is the most destructive and costly cyber-attack in history.
“These targeted sanctions are a part of a broader effort to address the ongoing nefarious attacks emanating from Russia,” said Treasury Secretary Steven T. Mnuchin in a press release. “Treasury intends to impose additional CAATSA [Countering America’s Adversaries Through Sanctions Act] sanctions, informed by our intelligence community, to hold Russian government officials and oligarchs accountable for their destabilizing activities by severing their access to the U.S. financial system.”
Nine of the 24 entities and individuals named on Thursday had already received previous sanctions from either President Obama or President Trump for unrelated reasons, The New York Times reported.
In addition to the sanctions, the Department of Homeland Security and the FBI issued a joint alert warning that the Russian government is targeting government entities as well as organizations in the energy, nuclear, commercial facilities, water, aviation, and critical manufacturing sectors.
According to the alert, Russian government cyber actors targeted small commercial facilities’ networks with a multi-stage intrusion campaign that staged malware, conducted spear phishing attacks, and gained remote access into energy sector networks. The actors then used their access to conduct network reconnaissance, move laterally, and collect information pertaining to Industrial Control Systems.
Other trending cybercrime events from the week include:
- Sensitive data exposed: Researchers discovered a publicly accessible Amazon S3 bucket belonging to the Chicago-based jewelry company MBM Company Inc. that exposed the personal information of more than 1.3 million people. About 3,000 South Carolina recipients of the Palmetto Fellows scholarship had their personal information exposed online for over a year due to a glitch when switching programs. The Dutch Data Protection Authority accidentally leaked the names of some of its employees due to not removing metadata from more than 800 public documents.
- State data breach notifications: ABM Industries is notifying clients of a phishing incident that may have compromised their personal information. Chopra Enterprises is notifying customers that payment cards used on its ecommerce site may have been compromised. Neil D. DiLorenzo CPA is notifying clients of unauthorized access to a system that contained files related to tax returns, and several clients have reported fraudulent activity related to their tax returns. NetCredit is warning a small percentage of customers that an unauthorized party used their credentials to access their accounts.
- Other data breaches: A misconfiguration at Florida Virtual School led to the personal information of 368,000 students as well as thousands of former and current Leon County Schools employees being compromised. Okaloosa County Water and Sewer said that individuals may have had their payment card information stolen due to a breach involving external vendors that process credit and debit card payments. The Nampa School District said that an email account compromise may have compromised the personal information of 3,983 current and past employees. A cyber-attack at the Port of Longview may have exposed the personal information of 370 current and former employees as well as 47 vendors.
- Arrests and legal actions: A Maryland Man was sentenced to 12 years in prison for his role in a multi-million dollar identity theft scheme that claimed fraudulent tax refunds over a seven-year period. The owner of Smokin’ Joe’s BBQ in Missouri has been charged with various counts related to the use of stolen credit cards. Svitzer said that 500 employees are impacted by the discovery of three employee email accounts in finance, payroll, and operations were auto-forwarding emails outside of the company for nearly 11 months without the company’s knowledge.
- Other notable events: Up to 450 people who filed reports with Gwent Police over a two-year period had their data exposed due to security flaws in the online tool, and those people were never notified that their data may have been compromised. A security flaw on a Luxembourg public radio station may have exposed non-public information.
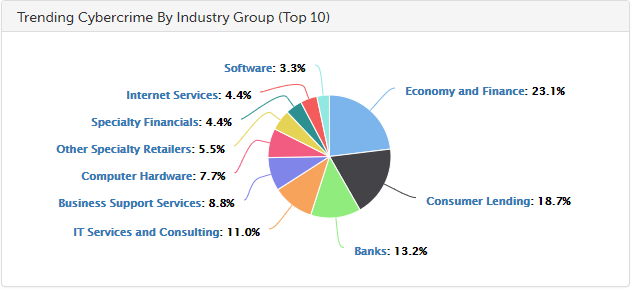
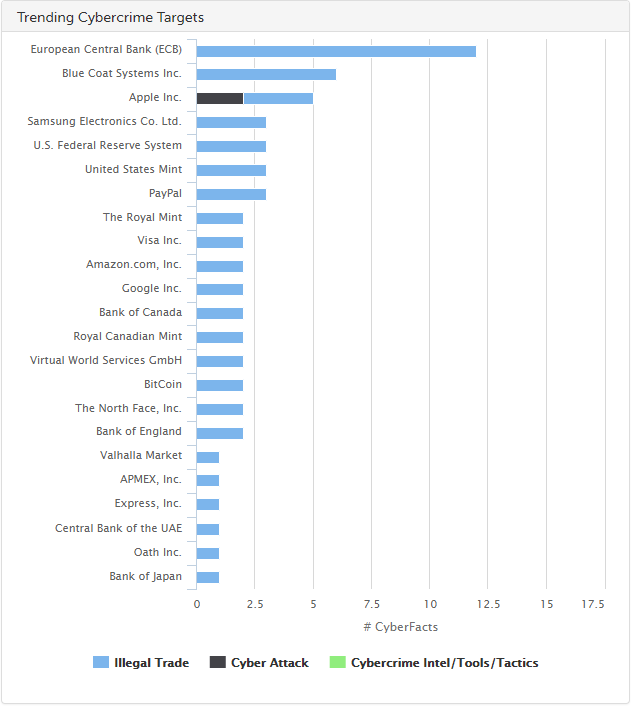
SurfWatch Labs collected data on many different companies tied to cybercrime over the past week. Some of the top trending targets are shown in the chart below.
Cyber Risk Trends From the Past Week
 Two of the largest data breaches of recent memory were back in the news this week due to Mossack Fonseca announcing that it is shutting down following the fallout from the Panama Papers breach as well as a former Equifax employee being charged with insider trading related to its massive breach.
Two of the largest data breaches of recent memory were back in the news this week due to Mossack Fonseca announcing that it is shutting down following the fallout from the Panama Papers breach as well as a former Equifax employee being charged with insider trading related to its massive breach.
Documents stolen from the Panamanian law firm Mossack Fonseca and leaked to the media in April 2016 were at the center of the scandal known as the Panama Papers, which largely revealed how rich individuals around the world were able to evade taxes in various countries.
“The reputational deterioration, the media campaign, the financial circus and the unusual actions by certain Panamanian authorities, have occasioned an irreversible damage that necessitates the obligatory ceasing of public operations at the end of the current month,” Mossack Fonseca wrote in a statement.
While Mossack Fonseca’s data breach appears to have finally led to the organization shutting down, Equifax’s massive breach announcement in September 2017 has since sparked a variety of regulatory questions, as well as criticism of the company’s leadership and allegations of insider trading.
Last week the SEC officially filed a complaint that alleges that Jun Ying, who was next in line to be the company’s global CIO, conducted insider trading by using confidential information entrusted to him by the company to conclude Equifax had suffered a serious breach, and Ying then exercised all of his vested Equifax stock options and sold the shares in the days before the breach was publicly disclosed.
“According to the complaint, by selling before public disclosure of the data breach, Ying avoided more than $117,000 in losses,” the SEC wrote in a press release.
Ying also faces criminal charges from the U.S. Attorney’s Office for the Northern District of Georgia.
*** This is a Security Bloggers Network syndicated blog from SurfWatch Labs, Inc. authored by Jeff Peters. Read the original post at: https://blog.surfwatchlabs.com/2018/03/17/weekly-cyber-risk-roundup-russia-sanctions-mossack-fonseca-shutdown-equifax-insider-trading/

