What You Need to Know About the Latest KEV Updates
In June of last year, we published our first review of the vulnerabilities in CISA’s Known Exploited Vulnerabilities (KEV) Catalog. Of course, security never stands still, and the KEV has steadily been updated as adversaries have shifted their tactics to exploit new vulnerabilities. In this blog, we will take a look at how things have changed over the past several months, and what KEV can tell us about where security teams should be focusing their efforts.
A Brief Background of KEV
KEV is a relatively new project, first being published by CISA in 2021. As the name suggests, KEV focuses on the vulnerabilities that are actively exploited in the wild by adversaries. This is important for two reasons. First, and most obviously, these vulnerabilities carry much higher risk to organizations because they are the most likely to be exploited in an actual attack. Secondly, it enables organizations to easily distill and prioritize what has become an overwhelming number of known CVEs. The rate of new vulnerability discovery has exploded in recent years and shows no signs of slowing down. The table below from CVE.org shows the scope of the problem. 25,059 new CVEs were identified in 2022 alone, and 97,415 in the past five years. By contrast, the KEV catalog hones in on the 886 vulnerabilities (<.01%) that are known to be exploited. Additionally, all the CVEs in the KEV database have published remediations such as updates or fixes. This gives organizations a highly-focused set of vulnerabilities that they can and should be addressing.
| Year | 2022 | 2021 | 2020 | 2019 | 2018 | 2017 | 2016 | 2015 |
| Quarter 4 | 6,231 | 5,200 | 4,387 | 4,822 | 3,614 | 3,570 | 1,590 | 1,652 |
| Quarter 3 | 6,448 | 5,541 | 4,170 | 5,150 | 4,350 | 4,037 | 1,713 | 1,747 |
| Quarter 2 | 6,365 | 5,005 | 5,011 | 4,091 | 4,613 | 3,612 | 1,775 | 1,443 |
| Quarter 1 | 6,015 | 4,415 | 5,807 | 3,245 | 3,935 | 3,426 | 1,379 | 1,652 |
| Total | 25,059 | 20,161 | 18,375 | 17,308 | 16,512 | 14,645 | 6,457 | 6,494 |
What Changed and What Stayed the Same?
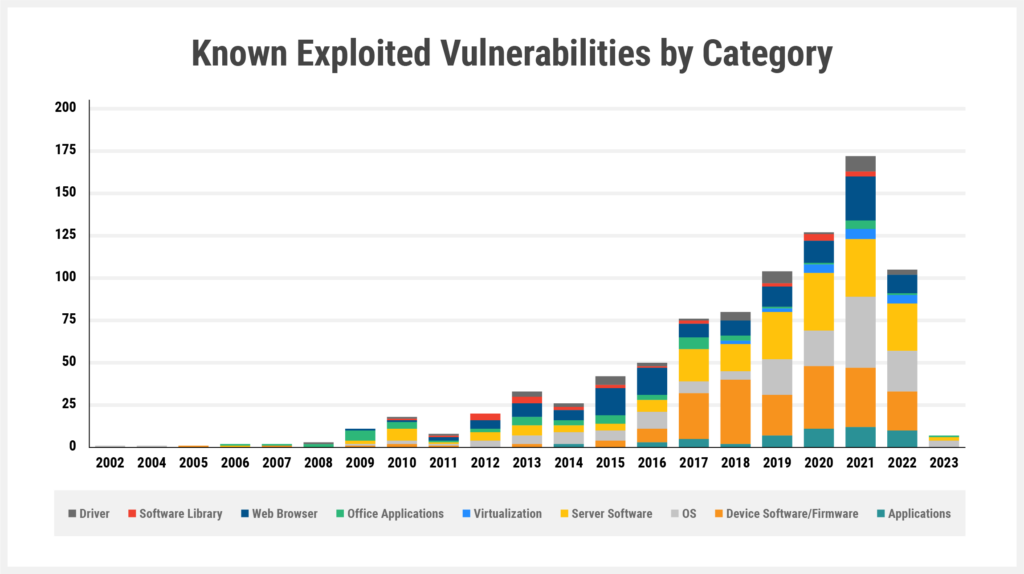
When we first published in June of 2022, the KEV included 778 actively exploited CVEs. As of March 6, 2023, the list has added 111 CVEs for a total of 889. The chart below breaks out these 889 vulnerabilities in terms of the year they were discovered and the category of vulnerability. As noted in our prior analysis, CISA itself does not yet categorize the vulnerabilities, so we assigned categories to each vulnerability based on the type of asset as follows:
- Firmware (e.g. Intel AMT, Cisco, F5 Networks)
- Server Software (e.g. Apache, Microsoft Exchange)
- Operating Systems (e.g. Windows, Android)
- Web Browser (e.g. Google Chrome, Internet Explorer)
- Office applications (e.g.. Microsoft Word, Excel)
- Applications (e.g. WinRAR, WhatsApp)
- Software library (e.g. OpenSSL)
- Virtualization (e.g. Docker, VMWare)
Firmware Continues to Lead the Pack
If we compare the current state of the KEV with that of nine months ago, we can see a few changes and the continuation of some trends that were noted during our previous analysis. Overall, firmware remains the most common category of vulnerability with 204 CVEs followed closely by server software (198), operating systems (162), and web browsers (134). The overall ranking of categories remained unchanged other than the “applications” category pulling into a tie with “office applications”.
| Category | Count of CVEs |
| Firmware | 204 |
| Server Software | 198 |
| OS | 162 |
| Web Browser | 134 |
| Applications | 52 |
| Office Applications | 52 |
| Driver | 41 |
| Software Library | 26 |
| Virtualization | 20 |
What’s New: More Server CVEs, Firmware is Evergreen
If we focus on just the 111 CVEs added since June, the chart looks like this:
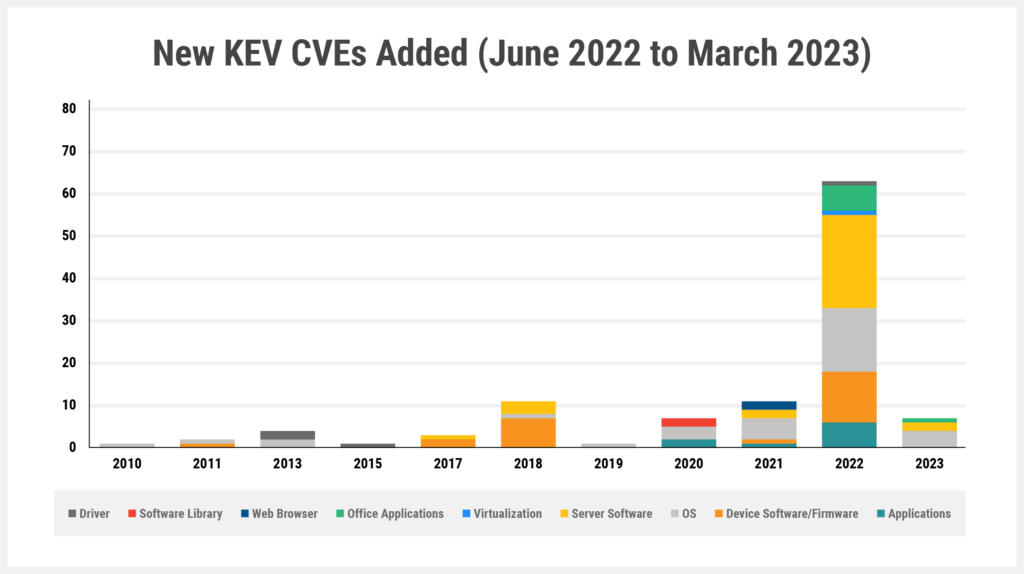
We can see that the second half of 2022 was dominated by CVEs discovered in 2022 including 63 CVEs total. However, older CVEs were still being added to the KEV in significant numbers including CVEs that were more than a decade old.
And while firmware, server, and OS vulnerabilities remained the most common categories, there were some interesting differences. Operating systems had the most CVEs with 33, followed by server software (30) and firmware (23).
Naturally, we should probably not infer too much from this data based on its relatively small sample size, but there are some interesting points to consider particularly in the context of firmware vulnerabilities. When looking at these updates, most of the categories were heavily weighted toward recently discovered vulnerabilities. However, firmware vulnerabilities were almost equally split between new and old CVEs. 13 firmware CVEs were from 2022 or 2021, while 10 were from 2018 or earlier. Even when only looking at these most recent updates, it is clear that adversaries recognize that firmware vulnerabilities and exploits have a longer shelf-life. And the biggest reason for this is that many organizations continue to lag when it comes to scanning and updating the firmware in their devices.
CVEs by Vendor
The 111 CVEs were spread across 45 different vendors or open-source projects. Microsoft and Apple had the most vulnerabilities with 21 and 13 CVEs respectively, mostly tied to OS vulnerabilities. Google had 6 CVEs with all of them tied to the Chrome web browser.
The list also included a variety of CVEs that could affect enterprise infrastructure. This included firmware vulnerabilities within Citrix ADC as well as network security infrastructure from Cisco, Fortinet, Palo Alto Networks, and Sophos. Server software vulnerabilities included CVEs tied to Apache (Spark, Couch DB), Atlassian, Grafana, Microsoft (Exchange Server, Active Directory), Oracle, Zimbra Collaboration, and Zoho ManageEngine.
The 2022 Year In Review
Since our previous analysis only included the first half of 2022, we wanted to go back and do an analysis of 2022 now that we have a full set of data. And 2022 was certainly a busy year for the KEV. Some of this can be attributed to adversaries being particularly active in the wild, but we also have to remember that the KEV was only first introduced in November of 2021. Given that 2022 was the first full year of the KEV’s existence, it should be no surprise that many of the updates likewise were added in 2022.
To put it in more concrete terms, of the 889 CVEs listed in the KEV, 556 of them (62.5%) were added to the list in 2022. However, it is important to distinguish between the year a CVE was discovered and the year it was added to the KEV. For example, CVE-2017-15944 affecting the firmware of Palo Alto Networks devices was first discovered in 2017 but only added to the KEV in August of 2022. In fact, as the chart below illustrates, the KEV updates covered CVEs from a wide range of years, with the oldest coming from 2002.
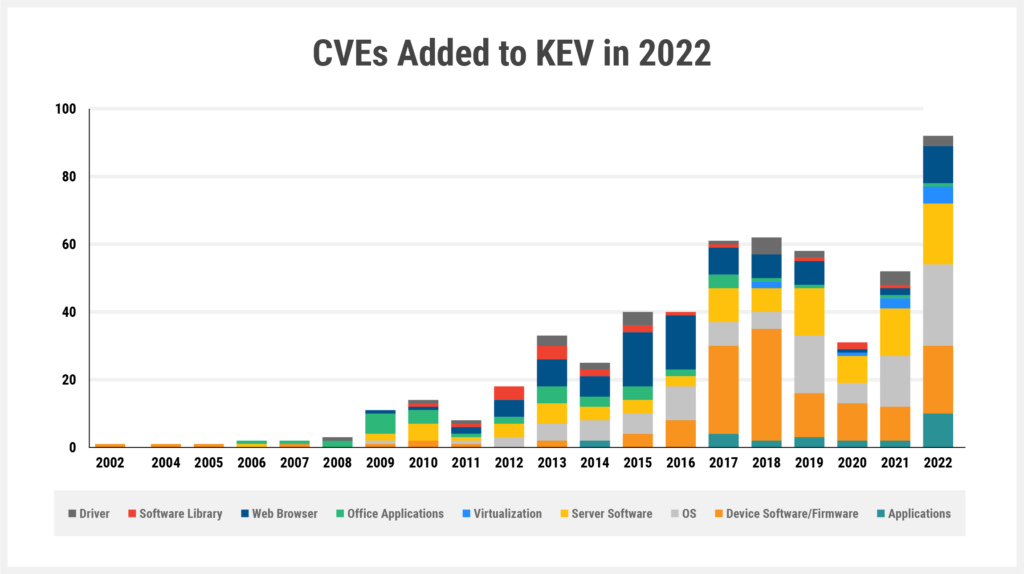
There are a few important takeaways as we look deeper into the 2022 additions. First, 92 CVEs were from 2022 (i.e. CVE-2022-XXXX), and this was the largest number for any single year. This shows that adversaries are certainly attacking newly-discovered CVEs.
However, the other side of that coin is that 464 or 83.5% of newly added CVEs were not from 2022. In fact, after 2022, most CVEs came from 2018, 2017, and 2019 respectively. This shows that adversaries aren’t just going after new or 0-day vulns, they are also feasting on the vulns that remain unpatched.
The 2022 additions reflect many of the same trends that we have seen before. Firmware, OS, and server vulnerabilities make up the “big 3” with 133, 110, and 100 CVEs respectively. And once again, we see both old and new firmware vulnerabilities being attacked in the wild. However, this should probably not be surprising – unlike OS vulnerabilities which are often quickly patched, firmware weaknesses can go unpatched for years. This will be a very interesting area to monitor over time as additional CVEs are added to the KEV database. Do firmware vulnerabilities continue to be the attacker’s choice for evergreen vulnerabilities or will better firmware and supply chain security begin to turn the tide?
The post What You Need to Know About the Latest KEV Updates appeared first on Eclypsium | Supply Chain Security for the Modern Enterprise.
*** This is a Security Bloggers Network syndicated blog from Eclypsium | Supply Chain Security for the Modern Enterprise authored by Stephanie Choi. Read the original post at: https://eclypsium.com/blog/what-you-need-to-know-about-the-latest-kev-updates/

