Planning Ahead for Post-Quantum Cybersecurity
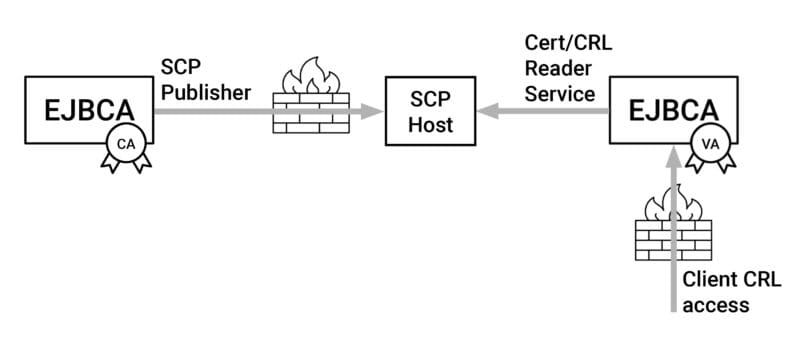
In a secure setup, where CAs and VAs are separated in different network zones, the secure copy protocol (SCP) can be used to synchronize data between CAs and VAs. The EJBCA SCP Publisher is available in EJBCA Community 7.11.
In a security-aware network setup, you want to minimize incoming traffic to your Certificate Authority (CA). One of the ways EJBCA supports such security awareness is by allowing you to use specific instances of EJBCA as CA and others as Validation Authority (VA).
The VAs are typically deployed in a different network zone than the CAs, where the CA network zone has higher protection. For the VAs to serve their purpose of distributing information about certificate status, OCSP, Certificate Revocation Lists, etc, there is a need for data synchronization between the CAs and the VAs.
How the EJBCA SCP Publisher works
The EJBCA SCP Publisher can be configured on the CA to publish information on certificate status and CRLs to a remote host using SCP. This requires no incoming traffic to the CA. Combining the SCP Publisher on the CA with the EJBCA Certificate and CRL reader service on the VA is a secure way to update the certificate and CRL data in your VA on a regular basis.
Since version 7.11, SCP Publisher along with Certificate and CRL Reader service is available in EJBCA Community. Read more in the release notes.
EJBCA Enterprise Edition includes a more advanced mechanism for integrating your CA with your VAs and the RAs, namely the Peer Systems concept.
Get Started with SCP Publisher
Do you want to try the SCP Publisher with EJBCA? Here is how to get started:
- Deploy EJBCA Community, see Quick Start Guide – Start EJBCA Container with Unauthenticated Network Access.
- Configure the SCP Publisher on your CA. See SCP Publisher.
- Configure the Certificate and CRL Reader on your VA. See Certificate and CRL Reader Service.
The post Integrate your VAs with your CA using Secure copy protocol (SCP) appeared first on Keyfactor.
*** This is a Security Bloggers Network syndicated blog from Blog Archive – Keyfactor authored by Karolin Hemmingsson. Read the original post at: https://www.keyfactor.com/blog/planning-ahead-for-post-quantum-cybersecurity/





