Home » Security Bloggers Network » Real-time Remediation Support Helps Developers Write Better Code
Real-time Remediation Support Helps Developers Write Better Code
Learning From Our Software Development Mistakes
Like anyone else, I hate making mistakes. When I do, I usually feel that I could have avoided it by learning more about the subject or maybe by asking for help. Good intentions aside, however, the reality is that we will still make mistakes. On that note, as software developers, we almost always create bugs while trying to meet a deadline or trying to provide functionality to delight users. Even the best software engineers make mistakes every day while writing code or configuring the technologies they use. Software is complex, so we can’t expect to get everything right all the time—especially when it comes to application security.
The old adage “you learn from your mistakes” is valid—trial and error is a fundamental aspect of the scientific method. Mistakes are really an opportunity to learn and get better at our craft. I wholeheartedly subscribe to this principle and so I’m delighted that Contrast Security has chosen to partner with Secure Code Warrior. Secure Code Warrior specializes in helping developers remediate application vulnerabilities and write secure code through hands-on exercises and video content. This partnership can benefit all Contrast users—and it is available today.
How Does the Contrast/Secure Code Warrior Joint Solution Work?
When the Contrast Application Security Platform detects a vulnerability, developers are notified in real time with detailed “how-to-fix” guidance to help them quickly find and fix the issue. This information is tailored specifically for developers, providing code examples based on the programming language and the libraries or frameworks used in the application. However, there are still instances when a developer might want a broader understanding of the vulnerability class—and this is where Secure Code Warrior adds real value. Contrast platform’s integration with Secure Code Warrior provides complementary contextual training content that further supports developers with their specific code remediation tasks.
For example, let’s say you’re working on an application programming interface (API) for an application that manages products for your company. A requirement of this API is to provide an option for suppliers to upload new products into your database. You write the code to import the products and then Contrast Assess assesses your API code for vulnerabilities in the background.
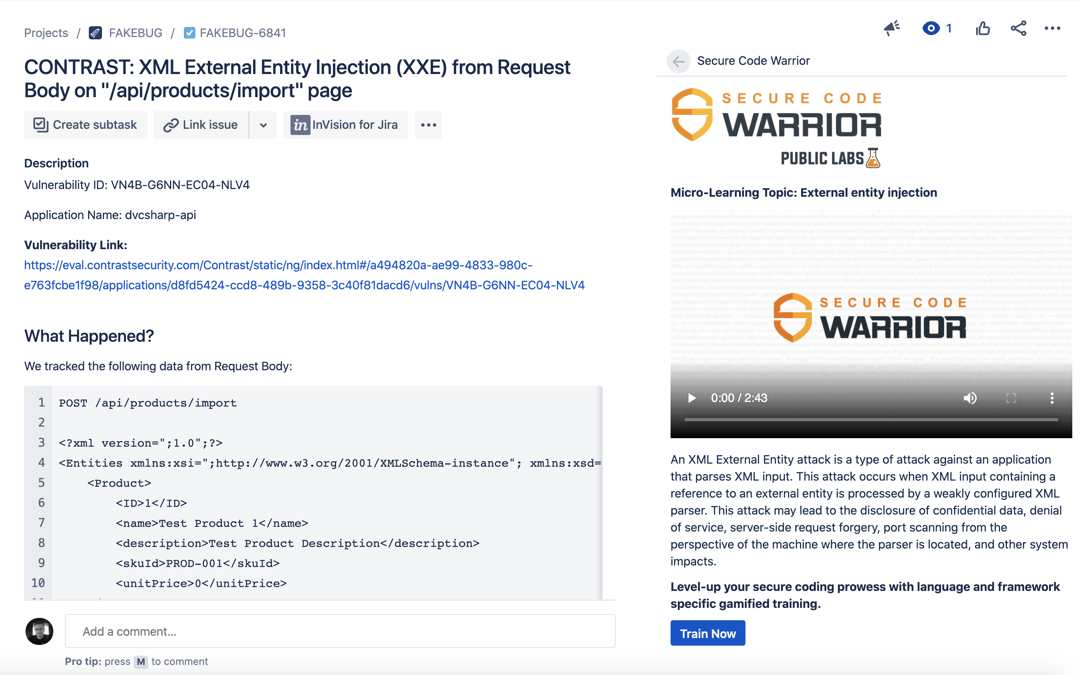
As you test the new API for the first time, you get a notification in Slack that you have introduced a vulnerability called XML External Entity Injection. Yikes! What’s that?
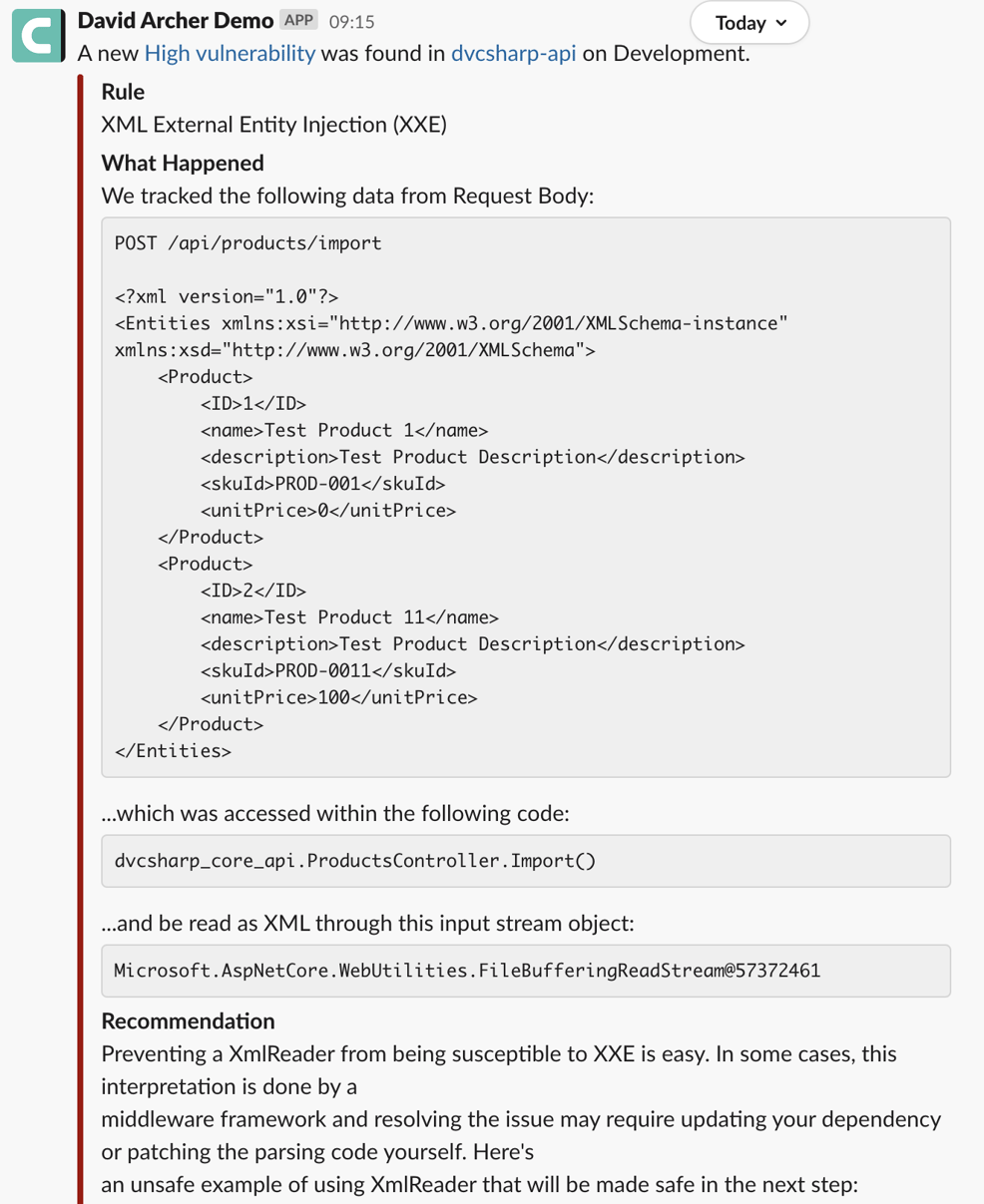
From the Slack notification, you open the vulnerability in Contrast. You can see from the description that it looks dangerous, but perhaps it’s also a bit mysterious.
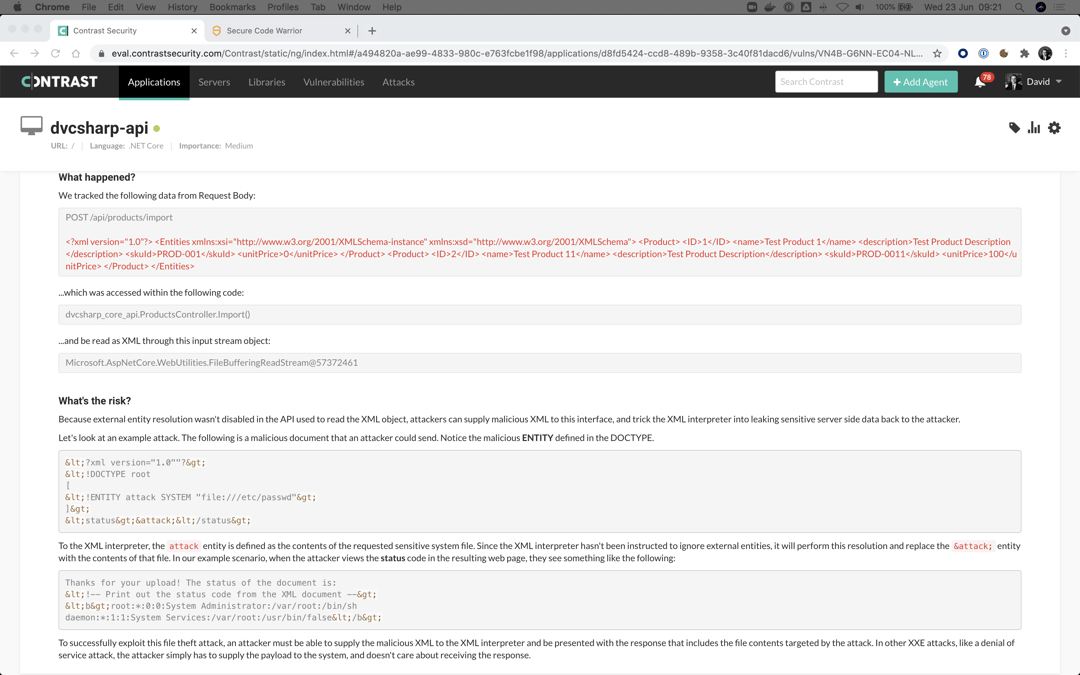
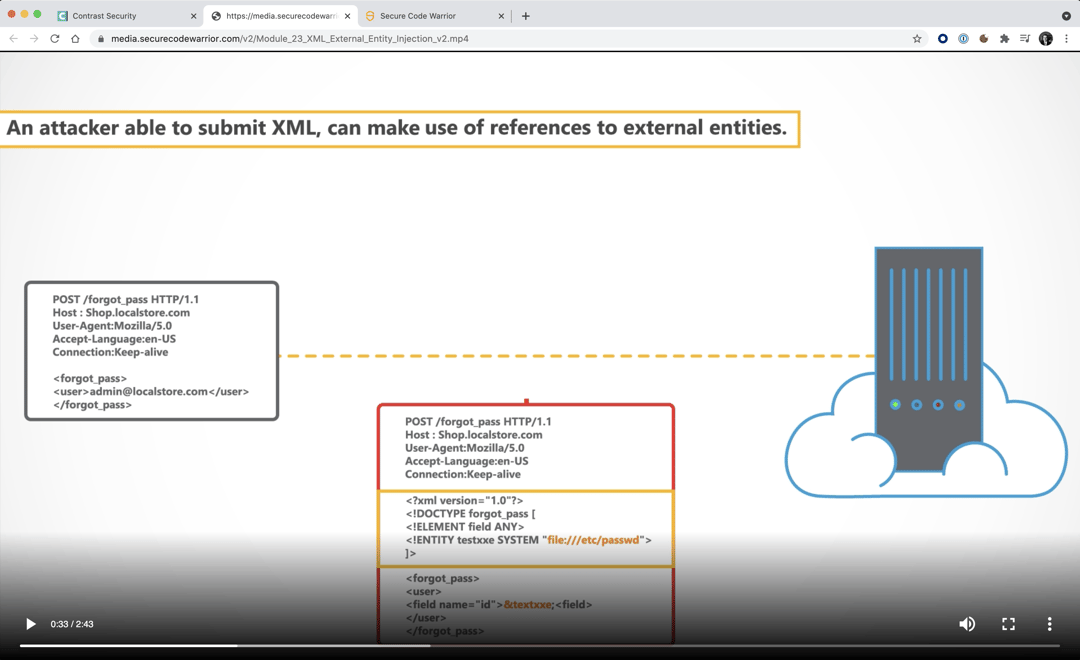
Before diving in to fix the problem, you need to understand the nature of the vulnerability in order to help you remediate it correctly on the first attempt (and maybe so you don’t repeat similar mistakes in the future). From the same “How-to-Fix” area in Contrast, you can follow a link to a Secure Code Warrior video that explains this vulnerability type in greater depth. It also includes a synopsis of the potential implications that could result if a malicious attack were to exploit the issue.
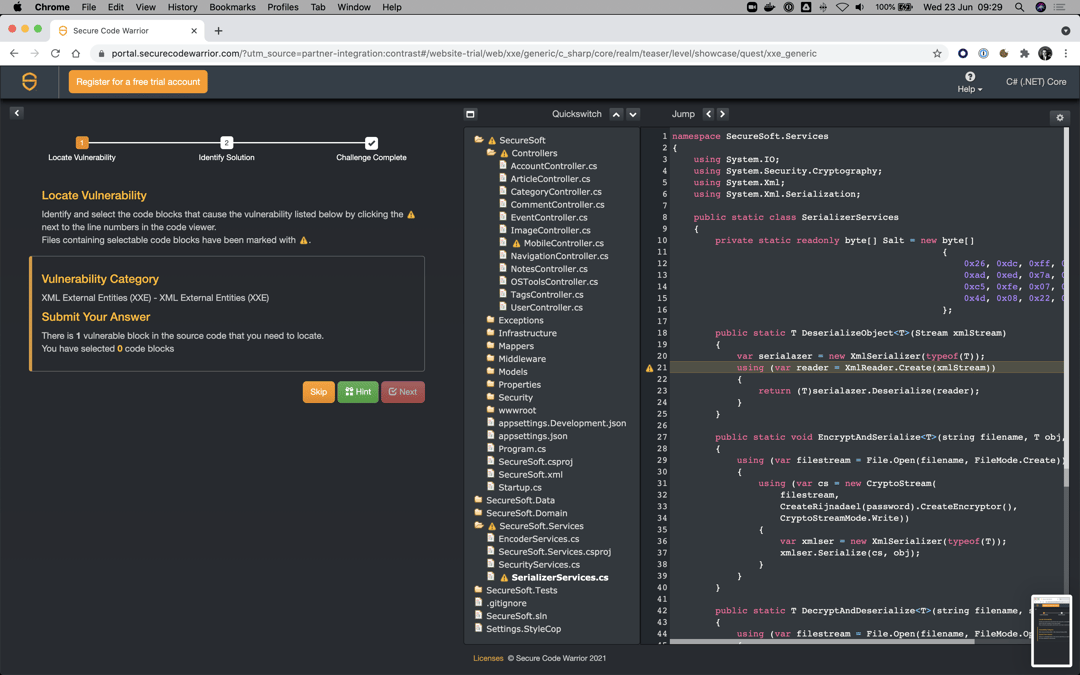
This kind of training helps you to understand the problem better. But maybe you don’t feel quite confident about solving it yet. Perhaps you’d like some practice first. The “How-to-Fix” guidance in Contrast links you directly to an exercise in Secure Code Warrior where you can see an example of this vulnerability and test your knowledge by identifying the correct solution from several options.
Finally, though not least, if you use Contrast’s integration with Jira to work on vulnerabilities, then there is also a Jira plugin available. The Jira plugin from Secure Code Warrior enables you to see video and training content embedded right in the ticket that was sent over from Contrast.
Working Together To Help Developers Write More Secure Code
The combined content from Contrast and Secure Code Warrior can help developers understand vulnerabilities to a much greater depth. The intent is that developers will use this just-in-time training approach and additional contextual guidance to avoid making the same coding mistake again.
For customers interested in adding Secure Code Warrior to your Contrast environment, you should get in touch with your Customer Success team that can guide you through a quick installation process. You may want to check out the solution brief on the joint solution—”Contrast Security and Secure Code Warrior: Just-in-Time Training for Developers.”
*** This is a Security Bloggers Network syndicated blog from AppSec Observer authored by David Archer. Read the original post at: https://www.contrastsecurity.com/security-influencers/real-time-remediation-support-helps-developers-write-better-code





