Nations come together to condemn China: APT31 and APT40
On Monday (19JUL2021) President Biden announced that the US and its allies were joining together to condemn and expose that China was behind a set of unprecedented attacks exploiting vulnerabilities in Microsoft Exchange servers conducted earlier this year. The White House press release was titled: “The United States, Joined by Allies and Partners, Attributes Malicious Cyber Activity and Irresponsible State Behavior to the People’s Republic of China.”
After praising recent actions by world governments to condemn Russian ransomware attacks, today’s memo goes on the offensive against China, reminding the world that the PRC intelligence enterprise hires contract hackers who operate both for the state and for their own profits. Biden reminds us of charges brought against PRC Ministry of State Security (MSS) hackers in October 2018, July 2020, and September 2020 and says they have “engaged in ransomware attacks, cyber enabled extortion, crypto-jacking, and rank theft.” Today additional charges were brought against additional MSS hackers.
While many court cases, agreements and foreign government statement were mentioned in the article, we thought it would be helpful to have all the links in one place. In this article, we share links to the mentioned charges against MSS-sponsored hackers, indicators and characteristics of the APT40 attacks, including advisories from CISA and NSA, links to foreign government statements joining in condemning China’s cyber attacks, and lastly, policy statements from G7, NATO, and EU supporting new Ransomware policy initiatives.
Justice.gov Previous Charges Against Chinese MSS-supported Hackers
The previous incidents referred to by the White House can be found on the Justice.gov website at the links below:
Zha Rong and Chai Meng were intelligence officers in the Jiangsu Province office of the Ministry of State Security (MSS). Their hacking team included Zhang Zhang-Gui, Liu Chunliang, Gao Hong Kun, Zhuang Xiaowei, and Ma Zhiqi and insiders of a French aviation company, Gu Gen and Tian Xi. Their cyber attacks went back to at least 08JAN2010. The indictment of these Chinese hackers which provides several aliases including leanov, Cobain, sxpdlcl, Fangshou, mer4en7y, jpxxav, zhuan86, and Sam Gu is available.
LI Xiaoyu (李啸宇)and DONG Jiazhi (董家志). The 27-page indictment of these Chinese hackers, which reveals Li’s hacker handle of “Oro0lxy” and the fact they worked for Guangdong State Security Department, is also available from DOJ.
Jiang Lizhi (蒋立志), Qian Chuan (钱川), and Fu Qiang (付强) operated Chengdu 404 Network Technology. Zhang Haoran (张浩然) and Tan Dailin (谭戴林) of China were part of a conspiracy targeting the video gaming industry, along with Wong Ong Hua and Ling Yang Ching of Malaysia who operated through Sea Gamer Mall. A transcript of the press conference about these three indictments of Chinese hackers is available.
Justice.gov Newly revealed Charges
The current case charges that the Hainan state Security Department set up a shell company, Hainan Xiandun Technology Development Company (海南仙盾). Three HSSD Intelligence officers, Ding Xiaoyang (丁晓阳), Cheng Qingmin (程庆民) and Zhu Yunmin (朱允敏), interacted with a lead hacker at Hainan Xiandun, Wu Shurong (吴淑荣). Working with his team, Wu and his hackers attacked universities and research facilities across the United States and the world, planting malware and stealing intellectual property. The indictment against Ding, Cheng, Zhu, and Wu, which also uses the aliases Ding Hao, Manager Chen, Manager Cheng, Zhu Rong, and gives Wu Shurong’s hacker aliases as goodperson and ha0r3n is available from justice.gov.
Many research groups have referred to them and their malware by a variety of names, including APT40, Bronze, Mohawk, Feverdream, Goo65, Gadolinium, GreenCrash, Hellsing, Kryptonite Panda, Leviathan, Mudcarp, Periscope, Temp.Periscope, and Temp.Jumper. A few reports on these would include:
- FireEye – “APT40 Examining a China Nexus Espionage Actor”
- Malpedia (at Fraunhofer.de) – “Leviathan”
- Crowdstrike – “Two Birds One Stone Panda” – which also includes discussions of how MSS Technology/13th Bureau uses source code review to reveal Microsoft vulnerabilities to their hackers, such as APT40, prior to their public disclosure by Microsoft!
- MITRE – Leviathan Group Report
CISA.gov has released an APT40 TTP Advisory, available as “Alert (AA21-200A) Tactics, Techniques, and Procedures of Indicted APT40 Actors Associated with China’s MSS Hainan State Security Department”
The Malware families and malicious tools named in the CISA advisory (with links to MITRE tool description pages) are:
- BADFLICK/Greencrash
- China Chopper [S0020]
- Cobalt Strike [S0154]
- Derusbi/PHOTO [S0021]
- Gh0stRAT [S0032]
- GreenRAT
- jjdoor/Transporter
- jumpkick
- Murkytop (mt.exe) [S0233]
- NanHaiShu [S0228]
- Orz/AirBreak [S0229]
- PowerShell Empire [S0363]
- PowerSploit [S0194]
- Server software component: Web Shell [TA1505.003]
NSA Advisory on Chinese State-Sponsored Cyber Operations
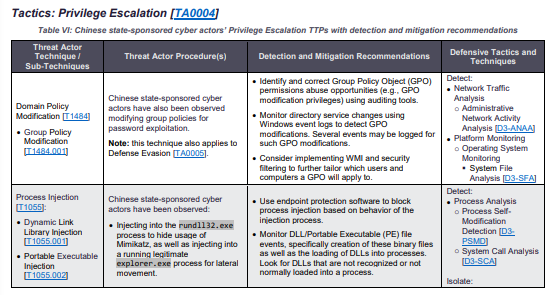
The National Security Agency, working with CISA.gov and the FBI, also released an advisory today, detailing in 31 pages more details about observed Tactics, Techniques, and Procedures (TTPs) used by Chinese hacking groups. Their description, provides Tactics, Threat Actor Techniques, Threat Actor Procedures, and Defensive Tactics and Techniques using the MITRE ATT&CK and D3FEND models. Detailed Detection and Mitigation Recommendations are also shared for each tactic.
Just to share one example … here is the way “TA0004” is described in the report.
That level of detailed explanation goes on for 14 pages of the report! Please see the full report for more details by visiting “CSA Chinese State-Sponsored Cyber TTPs.”
International Coalition Joining In
NATO Press Release: Statement by the North Atlantic Council in solidarity with those affected by recent malicious cyber activities including the Microsoft Exchange Server compromise
Previous Ransomware Actions
The White House memo makes reference to three recent advances in international communications about cyber security, from the G7, NATO, and the EU.
In June, the G7 Summit Communique specifically called out Russia’s inattention to Ransomware issues:
51. We reiterate our interest in stable and predictable relations with Russia, and will continue to engage where there are areas of mutual interest. We reaffirm our call on Russia to stop its destabilising behaviour and malign activities, including its interference in other countries’ democratic systems, and to fulfil its international human rights obligations and commitments. In particular, we call on Russia to urgently investigate and credibly explain the use of a chemical weapon on its soil, to end its systematic crackdown on independent civil society and media, and to identify, disrupt, and hold to account those within its borders who conduct ransomware attacks, abuse virtual currency to launder ransoms, and other cybercrimes.
Also in June, the NATO Brussels Summit Communique reaffirmed the NATO Cyber Defence Pledge and again called out Russia’s behavior:
12. In addition to its military activities, Russia has also intensified its hybrid actions against NATO Allies and partners, including through proxies. This includes attempted interference in Allied elections and democratic processes; political and economic pressure and intimidation; widespread disinformation campaigns; malicious cyber activities; and turning a blind eye to cyber criminals operating from its territory, including those who target and disrupt critical infrastructure in NATO countries. It also includes illegal and destructive activities by Russian Intelligence Services on Allied territory, some of which have claimed lives of citizens and caused widespread material damage. We stand in full solidarity with the Czech Republic and other Allies that have been affected in this way.
32. Cyber threats to the security of the Alliance are complex, destructive, coercive, and becoming ever more frequent. This has been recently illustrated by ransomware incidents and other malicious cyber activity targeting our critical infrastructure and democratic institutions, which might have systemic effects and cause significant harm. To face this evolving challenge, we have today endorsed NATO’s Comprehensive Cyber Defence Policy, which will support NATO’s three core tasks and overall deterrence and defence posture, and further enhance our resilience. Reaffirming NATO’s defensive mandate, the Alliance is determined to employ the full range of capabilities at all times to actively deter, defend against, and counter the full spectrum of cyber threats, including those conducted as part of hybrid campaigns, in accordance with international law. We reaffirm that a decision as to when a cyber attack would lead to the invocation of Article 5 would be taken by the North Atlantic Council on a case-by-case basis. Allies recognise that the impact of significant malicious cumulative cyber activities might, in certain circumstances, be considered as amounting to an armed attack. ( … ) If necessary, we will impose costs on those who harm us. Our response need not be restricted to the cyber domain. We will enhance our situational awareness to support NATO’s decision-making. Resilience and the ability to detect, prevent, mitigate, and respond to vulnerabilities and intrusions is critical, as demonstrated by malicious cyber actors’ exploitation of the COVID-19 pandemic. NATO as an organisation will therefore continue to adapt and improve its cyber defences. …
The European Union held their US-EU Justice and Home Affairs summit on 21-22JUN2021. European Commissioner Ylva Johansson, and US Secretary of Homeland Security Alejandro Mayorkas met along with the European External Actions Service, Europol, Eurojust, and others agreed to create a new U.S.-EU working group dedicated to fighting against ransomware. DHS reporting of the event can be found as “Readout of Secretary Mayorkas’s Trip to Portugal.” The EU’s reporting of the same event can be found as “Joint EU-US statement following the EU-US Justice and Home Affairs Ministerial Meeting.”
6. The United States and the European Union acknowledged the need to cooperate and shape a digital future based on our shared democratic values. The United States and the European Union acknowledged the potential benefits and risks of using Artificial Intelligence technologies for law enforcement and the judiciary. They also reaffirmed their dedication to develop and use such technologies in a trustworthy manner in conformity with human rights obligations. They further exchanged views on current and upcoming European Union efforts on tackling illegal content online, including the need to improve the cooperation between the authorities and online platforms to detect ongoing criminal activity. The United States and the European Union commit to continue to work together on how law enforcement and judicial authorities can most effectively exercise their lawful powers to combat serious crime both online and offline. They agreed on the importance of together combating ransomware including through law enforcement action, raising public awareness on how to protect networks as well as the risk of paying the criminals responsible, and to encourage those states that turn a blind eye to this crime to arrest and extradite or effectively prosecute criminals on their territory.
*** This is a Security Bloggers Network syndicated blog from CyberCrime & Doing Time authored by Gary Warner. Read the original post at: http://garwarner.blogspot.com/2021/07/nations-come-together-to-condemn-china.html