Meeting NERC CIP Standards with Private Cellular Networks
Cyberattacks on critical power grid infrastructure are no longer a matter of speculative concern. In recent years, both the capability and the willingness to attack bulk power system assets have been demonstrated by resourceful malefactors and state-sponsored cyberterrorists.
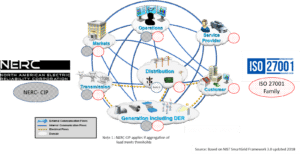
This has drawn the attention of both the U.S. government and the regulatory bodies that oversee utility systems, leading to tightening standards and increased awareness of the importance of following up-to-date security frameworks. In the energy sector, compliance with the North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) requirements is vital—and enforcement is only likely to increase.
One of the first confirmed cyberattacks on a power grid system occurred in Ukraine in December 2015. Hackers were able to deploy malware that allowed them to take 30 substations offline, cutting off power for more than 230,000 residents for several hours. With significant portions of domestic energy infrastructure dependent on legacy systems designed long before cyberwarfare became a reality? This event served as notice that rigorous new security standards were badly needed.
In July 2020, the new standard NERC CIP-013 went into effect to address risks in the vendor supply chain related to energy contracts. NERC is at the forefront of establishing the framework and standards that critical infrastructure companies and their cybersecurity providers need to follow. Avoiding loss and outages by adhering to these standards is of the utmost importance for any endeavor intended to protect and maintain cybersecurity for power grid systems and other utilities.
As old legacy systems give way to smarter, more interconnected networks and operational technology, private cellular networks have risen to the fore as a more defensible communications option. While these systems offer many advantages over public networks, care must be taken to ensure that NERC CIP compliance is maintained.
What are NERC Critical Infrastructure Protection Standards?
NERC is a nonprofit corporation based in Georgia that works to ensure the reliability of the bulk power system across North America. In 2008, they developed the CIP standards to establish a compliance framework for preventing cyberattacks on the power grid. Compliance with NERC standards is enforceable (via financial penalty) in the U.S. and some Canadian provinces.
The CIP standards are categorized as follows:
- CIP-002 – Identification, and categorization of systems and assets to support adequate security protocols to protect them.
- CIP-003 – Establishing security management controls that provide accountability.
- CIP-004 – Training personnel to understand security awareness and risk assessment.
- CIP-005 – Providing electronic security perimeters to control outside access to critical systems.
- CIP-006 – Managing physical security for assets that could be compromised.
- CIP-007 – Maintaining the technology, operations, and processes that allow for secure systems management.
- CIP-008 – Incident reporting and response planning following a cyberattack or breach.
- CIP-009 – Recovery plans for critical assets involved in an incident.
- CIP-010 – Preventing and detecting unauthorized changes to the system through vulnerability assessments and configuration change management processes.
- CIP-011 – Specifications for information protection requirements at the endpoint level.
- CIP-013 – Establishing security controls to minimize risks coming through the supply chain.
- CIP-014 – Managing physical security for transmission stations and substations.
Elements of all of the above standards are already subject to enforcement. All standards are subject to enforcement in the future and stakeholders should be proactive about meeting the requirements.
Enforcement
NERC guidelines allow them to fine violators up to $1 million per day, but penalties have yet to be assessed at this extreme level. The enforcement penalties typically levied by NERC vary according to the number and severity of the violations. In 2019, a record-setting $10 million fine was assessed to Duke Energy Corporation for multiple CIP violations that posed a risk to the cybersecurity of the bulk energy systems they oversee.
In anticipation of increased enforcement and more severe penalties reflecting the growing threat of cyberwarfare to critical power infrastructure, utility companies should be looking to leverage technologies that support a forward-thinking approach to the cybersecurity challenges of the current era.
How to Meet NERC CIP Requirements with Private Cellular Networks
Cellular connectivity is widely seen as the future of connectivity for smart utilities and infrastructure—specifically, private LTE networks, which offer significant advantages in the form of speed, clarity, and standardization, allowing a greater degree of flexibility and freeing utilities from dependence on specialized vendor-based communication systems. Private networks also present opportunities for enhanced cybersecurity measures that can facilitate compliance with NERC CIP standards, but smart connectivity brings its own set of security and implementation concerns.
When considering the networking and communication needs of a bulk energy system or similar enterprise, meeting NERC CIP standards should be of primary concern. While private cellular networks improve upon many of the shortcomings of previous communication technologies and can make it easier to meet the standards, it’s worth considering these benefits against the challenges that come with cellular connectivity.
Benefits of Private Cellular Networks
Private cellular networks bring the speed and accessibility of cellular connectivity in a form that allows precise deployment and a high degree of control, ideal for maintaining exacting security standards and for other applications. With utility systems interconnected on a high-speed broadband network, predictive maintenance and analysis are instantly available, allowing quicker responses to changes and errors that may be indicative of a cyberattack.
Smart devices are becoming an increasingly widespread part of public and private infrastructure, and utilities are at an advantage when they have the means to natively interface and communicate with these devices. However, the nature of cellular connectivity offers a wider range of endpoints that bad actors can use to attempt to gain entry to private networks. Private cellular networks offer plenty of opportunities to improve and expand on security and maintain the strictest regulatory compliance, but it’s absolutely essential to understand and account for the new vulnerabilities that may be created.
Challenges of Private Cellular Networks
Unfortunately, the desire for greater connectivity and smarter devices is at odds with the need for enhanced cybersecurity. The increased co-presence of critical operational technology and Internet of Things devices on electrical grids provides hackers with a wider range of wireless attack vectors than ever before. A single device, compromised by a phishing attack or left with a default password, can provide a point of entry from which the entire network can be damaged.
From a security and compliance standpoint, private cellular networks make sense, but the challenge of taking on endpoint security cannot be sidelined. Despite the impulse to break down barriers in the name of smart connectivity, the concept of a security perimeter remains essential and in the context of a utility-wide private cellular network, that means providing sufficient security for attached and networked devices.
Protecting Private Cellular Networks for NERC CIP Compliance
For utilities, the private cellular network option is a recent one, prompted by recent rule changes at the FCC that repurposed a portion of the wireless spectrum for their use. One utility that adopted private LTE early on is the New York Power Authority, which specifically cited cybersecurity as a major factor. With the framework provided by NERC CIP as a minimum baseline of security, private cellular networks offer a high level of control over the protections they choose to implement, allowing cybersecurity experts to build highly robust and customized defenses.
Bulk energy systems and other critical infrastructure will always draw the attention of high-profile attackers, and their defenses are constantly being tested. Staying within the NERC CIP guidelines means you’re doing the minimum necessary to protect the assets under your watch from the financial and reputational damage of a successful cyberattack, but true protection for private cellular networks necessitates a thorough threat assessment and a comprehensive approach to endpoint security.
Meeting NERC standards is not enough.
The FirstPoint team is here to help secure your cellular threat landscape.
The post Meeting NERC CIP Standards </br>with Private Cellular Networks appeared first on FirstPoint.
*** This is a Security Bloggers Network syndicated blog from Blog – FirstPoint authored by Adam Weinberg. Read the original post at: https://www.firstpoint-mg.com/blog/meeting-nerc-cip-standards-with-private-cellular-networks/