Cloud Security: What’s Good for Fintech Is Good for… All Our Clients
“Even after our major access risk cleanup, the Ermetic platform still ‘complains’ that we’re not perfect — which is fantastic. Security is never a binary outcome — it’s a sort of striving for perfection.” Senior engineer, MOHARA
***
Software solutions developer and integrator MOHARA, based in the UK, began using Ermetic to build cloud infrastructure security into client projects about a year ago, starting with an important Fintech customer. Mohara recently spoke with Ermetic about their use of the platform to help keep things secure and management-sane inside a cloud software development shop.
Discussion participants — MOHARA: Ben Blomerley, COO and co founder; Etienne Smith, CTO; Leo Thesen, Senior engineer; Louis Botes, Management engineer. Ermetic: Team members.
***
Calling card
MOHARA is a global technology product developer that partners with startups and larger corporations to build technology products that bring innovative ideas to life. As a technology innovator, MOHARA seeks to bring their startup clients the benefit of the best practices of their corporate clients, and vice versa. MOHARA has successfully delivered 100+ products; their diverse client base includes blue chip companies like Disney and the British Council, alongside a rich startup portfolio.
The penetration test challenge
The MOHARA team works on multiple software development initiatives simultaneously, supporting diverse clients, projects and environments. A new project came in: developing a cloud-native software solution for a third-party open banking partner in the UK. As a Fintech, the client demanded high cloud security requirements. To pass the client’s rigorous penetration testing stage, MOHARA needed deep visibility into IAM permissions, configurations and resources — and a process-integrative way to remediate detected risk.
Why did you start using Ermetic?
Our Fintech project initially rolled out as a high-stakes trial — a do-or-die milestone for us. We deployed Ermetic to ensure we would meet the required cloud security benchmark — and passed our first penetration test with flying colors including both the identity and entitlements and in the network sphere. Going into a penetration test can be intimidating. The results came back pretty conclusive that the system was secure. So we are using Ermetic to manage our security profile for this ongoing massive effort — and we came to realize that we could use Ermetic for other clients.
Frame the problem – why is it so hard to manage IAM risk in the cloud?
In engineering, we say, “I’ll clean up IAM later,” but no one ever does. In reality, enterprises have tens of thousands of policies — the moment it becomes a tad unmanageable, with excessive permissions, it becomes impossible to deal with. It’s just too hard to start refactoring those excessive permissions one by one. Yet that’s where your risk lies. So we’re using Ermetic to nip excessive permissions in the bud. Ermetic is also helping us meet our multi cloud needs. Our clients use different clouds — but it’s not practical for our team to learn the IAM mechanisms of each cloud — learning even one cloud’s access and entitlement scheme is very complicated, learning that of multiple clouds is insurmountable. With Ermetic, we don’t need deep IAM knowledge to have deep insight across multiple clouds.
Please describe your everyday use
We are pretty much using Ermetic extensively: starting our day with the dashboard and inventory analytics. I look at what Ermetic parses to be critical and high priority issues; we solve the big ones first and work our way down. We’ve also built Ermetic into every sprint, dedicating about an hour to our Ermetic review and action list — it’s been fantastic. Whether refactoring IAM user roles or people that have left the team to work on other projects, or tending to pipelines with excess permissions all the way to underused S3 buckets, Ermetic is a huge help. We also have a MOHARA-Ermetic Slack channel for capturing issues on the fly. We put those and the Ermetic findings into Jira, and add those actions to our sprint cycle.
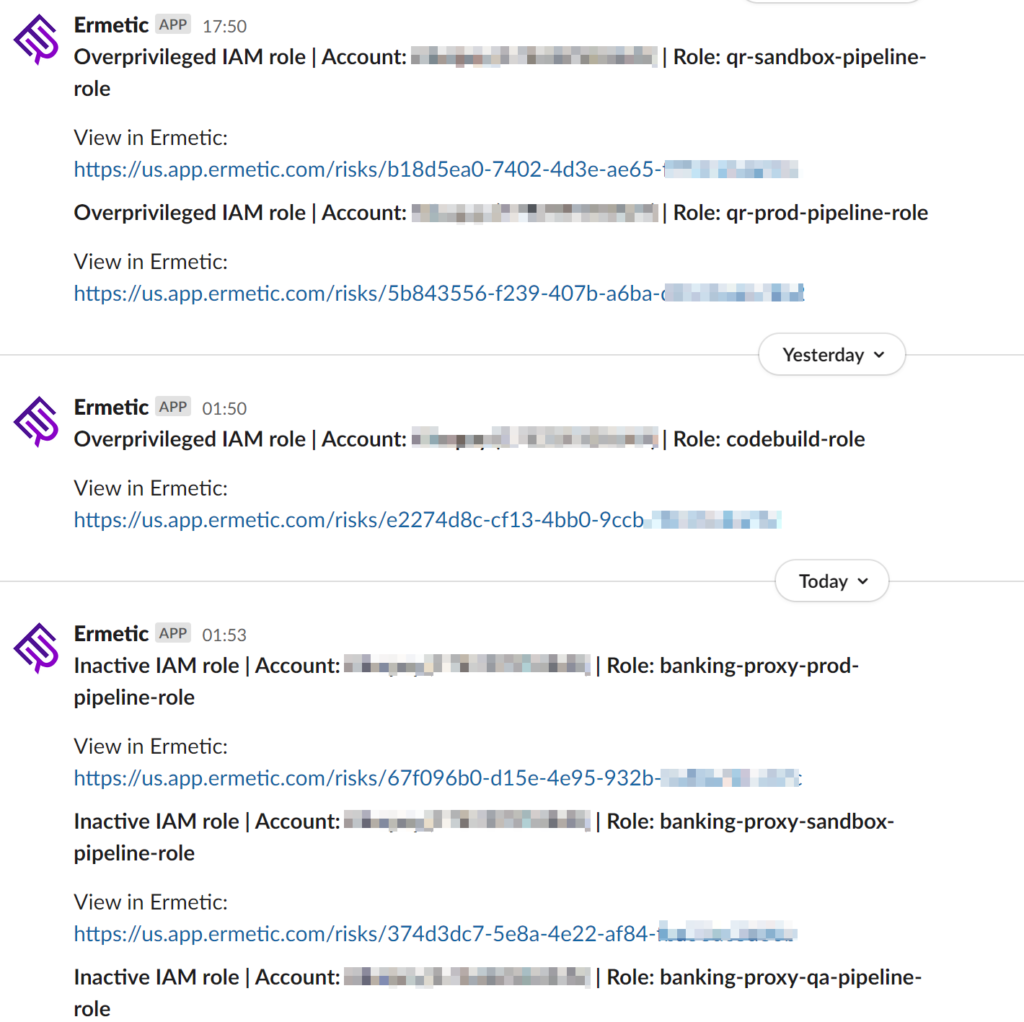
MOHARA’s Ermetic risk findings in Slack for sprint actioning
Our Git repository in Terraform is our source of truth. We plug Ermetic least privilege code snippets into our pipeline for code review. This aligns with our process of getting as many eyes on everything as possible, especially infrastructure changes.
Development on speed, with oversight
Don’t get me wrong, while cloud security is important to us, IAM discipline doesn’t always come first. Sometimes we need to push features forward immediately — at the expense of IAM policies. Having Ermetic gives us that flexibility: we focus on building the new features knowing we can go back and resolve the risk with Ermetic’s help.
Our strategy is to use a lot of IaC and IaS, to set things up quickly. We can do things faster for our clients by avoiding doing all kinds of configurations: we just roll it out. But this approach requires many user roles and the like that we often alternate between — engineers wear different hats — which adds to the complexity of the infrastructure. Ermetic enables us to work like this because it monitors the security and lets us do things in parallel.
What else? You mentioned “spam”-y links, minor hacks
While we’re busy focusing on avoiding catastrophic data breaches, with millions of records, there are, in fact, lots of minor hacks — security risks — that you might otherwise put up with. Minor irritations that can be easily fixed, like an open repository or instance that someone or something has access to. But such risks can add up. Ermetic helps us push back on these high instance, low impact risks, keeping our security posture clean.
Please talk about distributed responsibility
That’s our vision: to distribute ownership through IaC and use Ermetic to standardize the infrastructure with reusable modules that we know are secure. We aim to ensure that all MOHARA projects are at a consistent and repeatable level of quality — especially from an infrastructure and security point of view. We achieve this by using Ermetic to continuously review all projects. That is, we use Ermetic to ensure that if vulnerabilities have been introduced or exposed you can rectify them across all projects.
It’s quite an arduous task if you have to log into each module and check each project. Ermetic lets us standardize our security knowledge approach by reviewing our different client projects on a regular basis. So, for example, we can take a big security mindset to the Fintech client we mentioned but — and this is the amazing cost benefit/high customer value thing: we can do the same with another outfit, giving the security lens the same amount of attention.
Regarding distributed responsibility, we believe and practice that if you can start left — not shift left, start left — in a way that is cost effective and efficient for the build, why not? Because having that discipline takes away risk. You don’t have to think: Do I have a lot of risk balancing on this? Rather, it’s: Why not? Start left is good practice and doesn’t impact our overall trajectory. Our distributed responsibility strategy is across the board, not just for DevOps teams.
A few words about your security review team?
With pleasure. It’s been such an interesting finding that using Ermetic we’ve enabled a few key people across domains — IAM, our CTO, our principal engineer — to have visibility over the state of many IAM configurations and multiple projects. That is, Ermetic has allowed us to accelerate creation of a central review team that can move from project to project and raise issues quickly and share best practices. It helps elevate the quality of execution of each project.
What does Ermetic do for you?
It’s more than managing our cloud infrastructure permissions and risks. We see Ermetic as a strategic cloud security solution that enables our philosophy; it goes beyond, scans for things we don’t look for or are aware of. Ermetic does two key things for us:
- Reduces our reliance on a centralized function between different customer projects
- When a centralized role does exist, allows a quick and efficient way to keep tabs on multiple products at once. It prevents us from waiting until something goes wrong; rather, lets us proactively manage what’s going on — even if someone doesn’t have the IAM experience with a given cloud platform.
Even after our major access risk cleanup, the Ermetic platform still ‘complains’ that we’re not perfect — which is fantastic. Security is never a binary outcome – it’s a sort of striving for perfection.
The post Cloud Security: What’s Good for Fintech Is Good for… All Our Clients appeared first on Ermetic.
*** This is a Security Bloggers Network syndicated blog from Ermetic authored by Ermetic Team. Read the original post at: https://ermetic.com/whats-new/blog/cloud-security/whats-good-for-fintech-is-good-for-all-our-clients/

