Transforming Your IT Risk Management from Reactive to Proactive in 5 Steps
As a seasoned IT risk management professional, you already know that staying on top of security is a constant battle. Cyber attackers are constantly evolving their methods, there are more stringent data privacy regulations in place than ever before, and technology buyers are highly sensitized to the fact that their software vendors and service providers’ security flaws can leave their valuable data exposed.You don’t need anyone to tell you how important it is to take a disciplined, proactive approach to managing IT risks.
You probably also know that managing IT risks proactively and consistently is incredibly difficult to do. In Hyperproof’s 2021 IT Benchmark Survey (completed by 1,029 IT security assurance/compliance professionals), we found that 65% of global tech companies are still managing IT risks in an ad-hoc way, in siloed departments, with disparate processes and multiple disconnected tools.
Overcoming the Operations Gap
In the survey, we specifically asked people, “When it comes to managing security and data privacy tasks arising from your internal environment, what tasks do you find to be tedious/take longer than you’d like?” And we found that many of the critical tasks around risk management are manual and time-intensive, such as:
- Keeping a risk register up-to-date
- Collecting the necessary data to test controls
- Finding risk-related information when it’s needed
- Figuring out how a control links back to a risk
- Switching back and forth between multiple systems throughout the risk management process
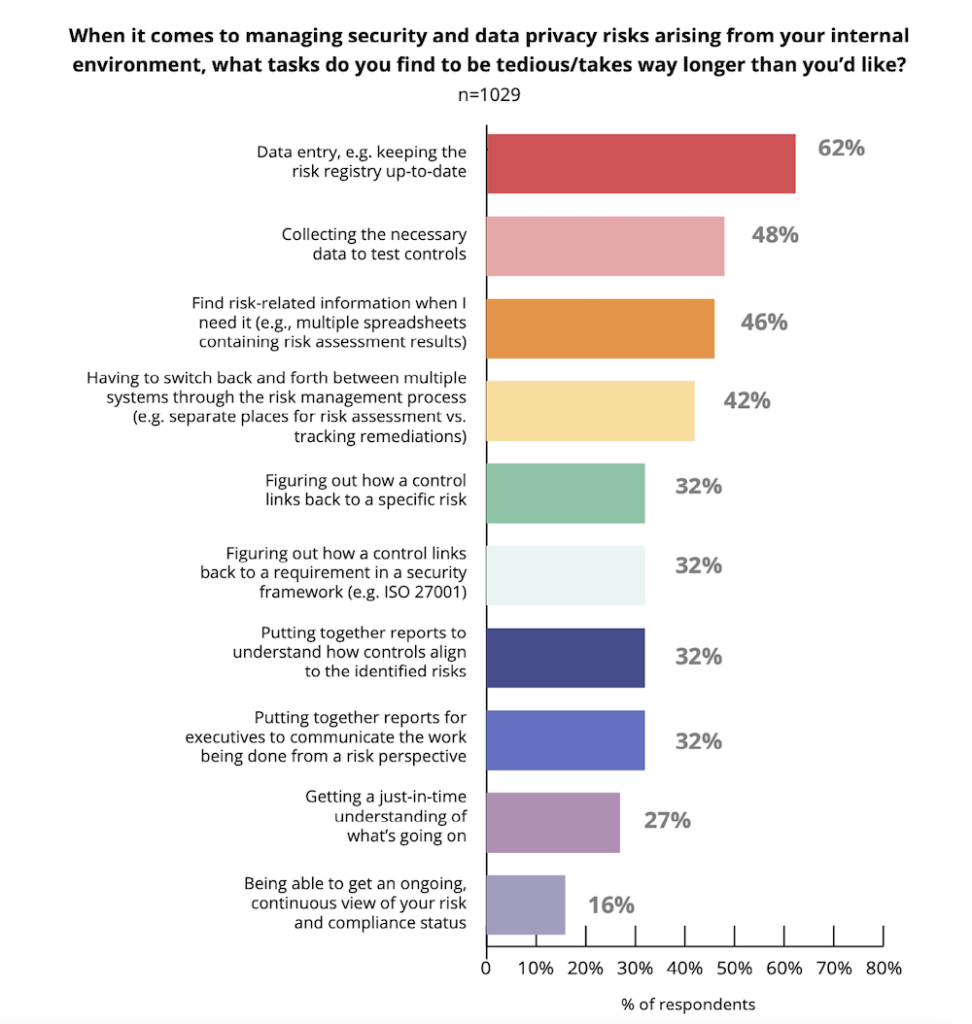
When organizations use multiple, disconnected tools throughout their risk management process, collecting critical risk and compliance information is both incredibly difficult and tedious.
As such, organizations often have a limited understanding of how well existing risks are managed and a limited capacity to detect when a control meant to mitigate a certain risk has failed or hasn’t been implemented effectively. In fact, close to 70% of surveyed IT security assurance professionals do not have a monitoring system in place to check whether controls designed around their organization’s specific risks are operating properly or not.
All of this ultimately results in unwanted risk exposure: 61% of all surveyed said their organization has experienced a data breach or a privacy violation in the last three years.
If these statistics resonate with you, and if you want to get a better handle on your information security compliance program, we’re here to help. In this article, we’ll tell you about a framework we’re calling “Compliance Operations” (or “ComOps” for short) you can use to get things into better shape.
What is Compliance Operations?

Compliance Operations is a business methodology that recognizes that managing information security compliance and security assurance programs consistently and on a day-to-day basis is a critical component of effective IT risk management. It operates on the understanding that cyber risks can change by the minute, regulatory volatility isn’t going away, and zero trust is now the default security (and B2B purchase) model. As such, compliance and security assurance professionals need to apply more rigor and discipline to their day-to-day activities. The Compliance Operations methodology provides a way for organizations to manage IT risks in a more disciplined, proactive manner and efficiently prove to their customers that they can keep sensitive customer data safe.
Five Compliance Operations Principles
1. Break down information silos across IT risk management processes
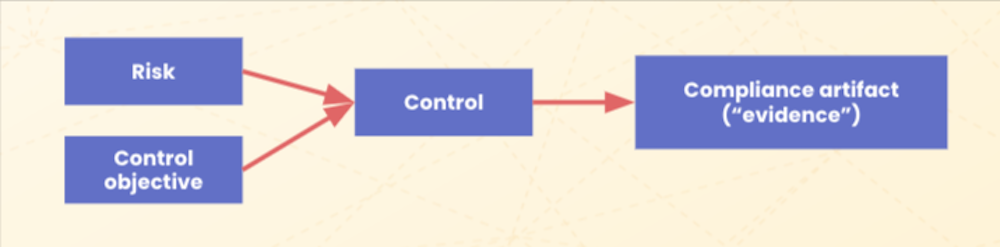
Connecting disparate information silos across the IT risk management processes– so risks, security requirements, and the state of existing internal controls are well understood — has to be the first step if an organization wants to manage IT risks in an agile, proactive way. All of your company’s risks, control objectives and requirements, controls, and compliance artifacts can be documented in Hyperproof and these information objects can be mapped.
2. Make the work visible and predictable
It’s hard to plan tasks and resources and manage workloads if you are not able to clearly see the full set of work that needs to be done to support security assurance and compliance objectives. The starting point has to be a disciplined approach to finding out what work needs to be done.
With that understanding, you can begin to estimate the workload and resources required to meet those objectives and design the allocation of key tasks within, and outside of, the security assurance and compliance function. Knowing the schedule, and being able to stay ahead of it, is key. What’s the cadence for internal and external audit activities? When do controls need to be implemented, reviewed, and tested? Who’s responsible for critical tasks and how do we monitor that? And finally, how can we quickly see if there’s a potential issue, like a control not being tested on schedule or if we failed to remediate a key finding?
3. Define a process for collecting and reviewing evidence

If you don’t have access to up-to-date evidence, you can’t assess whether controls you’ve implemented are functioning properly or not, which may leave a key IT system exposed. Additionally, in order to pass an independent audit, you’ll need to supply your auditors with the correct compliance artifacts. Lastly, collecting evidence tends to be so tedious and time-consuming that it holds security assurance professionals back from tackling more strategic tasks. Hyperproof’s 2021 IT Compliance Benchmark Survey found that half of the IT security compliance professionals surveyed spend 50% or more of their total time at work on repetitive administrative tasks around preparing for audits.
By having a clearly defined process for collecting and reviewing evidence, you can save a significant amount of time, money, and frustration and minimize the risk of control failures.
When defining your evidence collection process, it’s important to consider the following:
- Evidence should be mapped to controls
- What types of evidence are needed to test whether this control is functional?
- What’s the appropriate frequency for collecting that evidence?
- How long do I consider the evidence to be “fresh” or valid?
- What IT/business system does the evidence reside in?
- Who is responsible for submitting the evidence?
- Who needs to review that evidence?
By keeping all this contextual information alongside each piece of evidence in a system of record, you can easily reference this information for future audits, saving time and money.
4. Automate processes to make them more efficient (and support a more efficient operating environment for the entire organization)
When security compliance teams spend much of their time on manual repetitive tasks, they’re left with little time to focus on other important tasks aimed at improving security and resiliency (e.g., testing controls on high risk areas, talking to business units to understand what’s changing in the business and how those changes may create new risks or amplify existing risks). Manual, repetitive tasks, such as evidence collection, controls monitoring, and reporting, should be automated.
Further, at the controls level, it’s easy to become “over-controlled” as compliance professionals try to meet different but somewhat similar framework requirements. This issue has driven the move towards unified controls frameworks. Automation and good processes can help us get there and remain there in light of new or changing requirements.
5. Have a reporting and monitoring system in place to support ongoing improvements
Security assurance/IT compliance work is an iterative process. Controls can quickly become obsolete when a change occurs in an organization, such as when an existing IT system is retired and a new one is implemented. To achieve continuous compliance, every organization needs to have a reporting and monitoring system that provides real-time insight into the status of internal controls, risks, audits, and automatic flagging of issues that need attention. For instance, one report should help you identify which controls need review because evidence isn’t fresh anymore. You should have an easy way to see which security objectives aren’t met yet because controls haven’t been implemented or tested. There should be a way to track issues and tasks so that those involved in compliance know what they need to do next.
When you put these steps in place, it becomes possible to scale up your infosec compliance programs efficiently, without having to reinvent the wheel.
Advantages of Taking an Operational Approach to Compliance Activities

The advantages of taking an operational approach, as opposed to a traditional approach (e.g., rushing to check controls, collect evidence, and fix controls right before an audit) are three-fold.
First, by reviewing things on a cadence, you effectively minimize the chances of experiencing security and compliance lapses and of leaving risks unaddressed.
When your team can easily collect evidence on an ongoing basis, no one needs to scramble or go into fire-drill mode right before an audit, which helps keep your team’s stress levels down. When the team keeps track of all of their work in a single compliance operations platform, it becomes easy to prove to customers, auditors, and regulators that your organization has been operating in a secure and compliant way all along. When your organization is good at proving your compliance posture, you win and retain more business.
Put Compliance Operations Principles Into Practice with a Platform
While it might be possible to bring discipline and rigor to these processes using the same tools we use now, it will be close to impossible to keep it that way. This is intuitive when you look at how various business functions are operating today. Sales teams have Salesforce, HR has Workday, and Engineering has a variety of DevOp tools to efficiently execute their work. It’s time security assurance and compliance teams got their own platform for managing daily compliance operations — a place for making project plans, getting work done, tracking progress, and identifying areas for improvement.
Hyperproof’s compliance operations platform was built with these key principles of good operations in mind. Hyperproof is your assistant in creating a highly effective Compliance Operations function. It gives you the visibility, efficiency, and consistency you and your team need to stay on top of all your security assurance and compliance work.
To learn more about Hyperproof, sign up for a demo: https://hyperproof.io/request-a-demo/
The post Transforming Your IT Risk Management from Reactive to Proactive in 5 Steps appeared first on Hyperproof.
*** This is a Security Bloggers Network syndicated blog from Hyperproof authored by Jingcong Zhao. Read the original post at: https://hyperproof.io/resource/transforming-it-risk-management-5-steps/

