Live from Black Hat: Healthscare – An Insider’s Biopsy of Healthcare Application Security with Seth Fogie

Healthcare providers heavily leverage technology.ツ?In his talk, Seth Fogie,ツ?informationツ?security director at Penn Medicine takes apart different vendor systemsツ?at the ???fictitious??? Black Hat Clinic. Fogie gives a lot of examples and drives home the point that you shouldn???t just look at network security ??ヲ you have to dig deep into the applications to ensure the security of your data.
Following the patient???s journey.
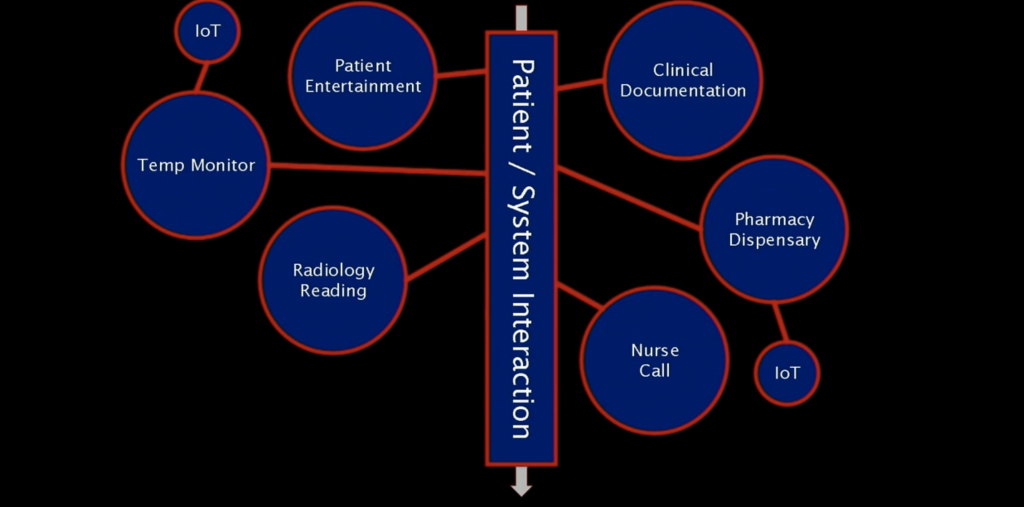
Fogie followsツ?the patient???s journey of now geriatric Alice and Bob, our quintessential victims in the security realm. Taking on the perspective of Mallory, the malicious attacker, he goesツ?to town taking apart one system after another.
For example, patient entertainment systems not only let you watch television but also give access to patient data.ツ?The first system he looks at providesツ?access to patient health information without authentication and usesツ?client-side authentication for PINsツ?that are easilyツ?overcome whenツ?using a proxy server between the client and the server.ツ?ツ?
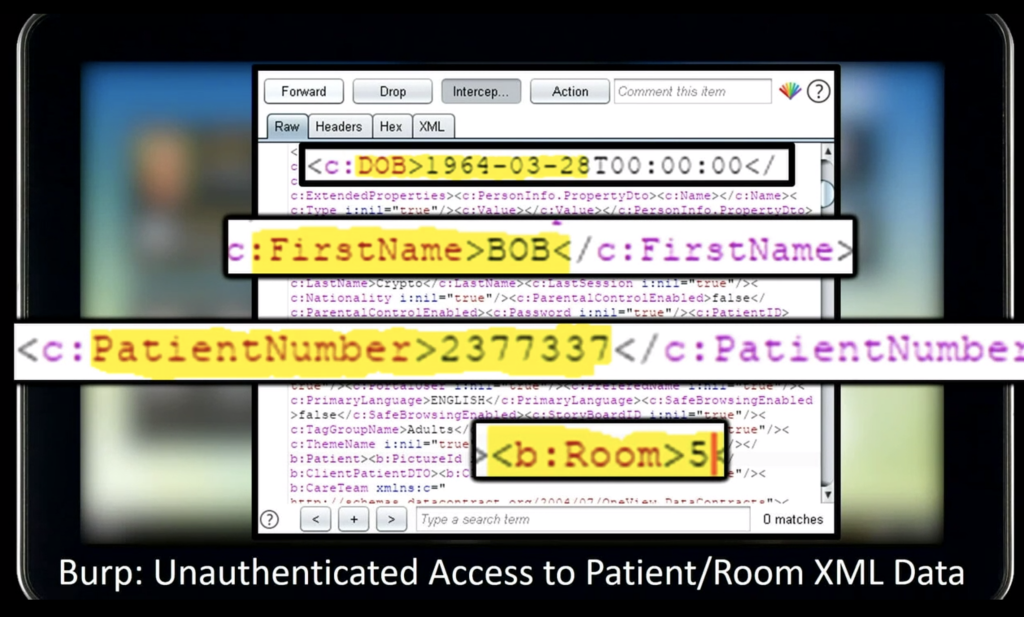
A different system, a clinical productivity system, hasツ?a backdoor with a daily password that is generated with a pre-determined algorithm.ツ?ツ?
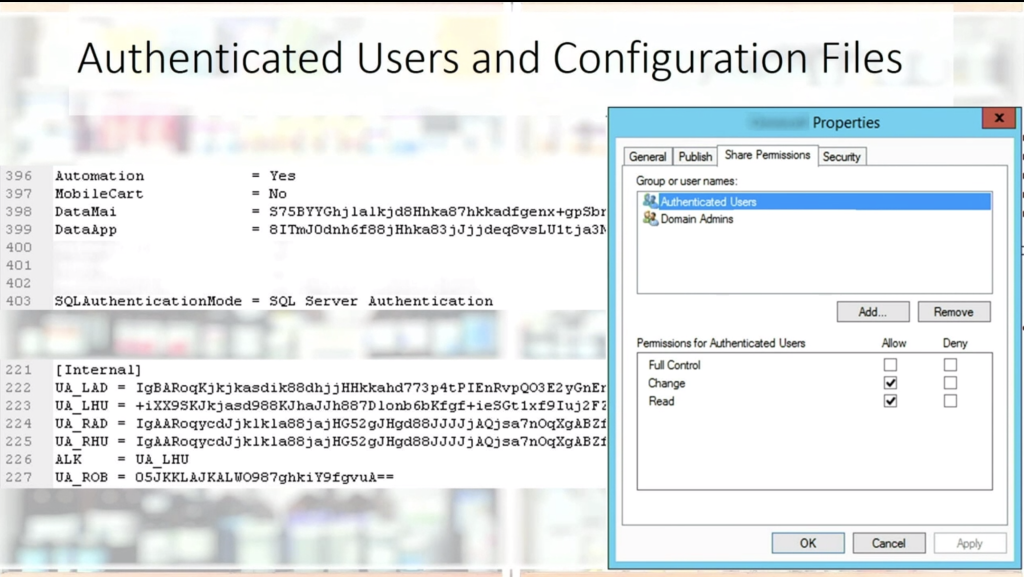
Next, he looksツ?at the drug dispensary system, which hasツ?an unauthenticated network share. Investigating the binaries, he findsツ?the SQL decryptionツ?key.ツ?This leads to full system access of the server, which providesツ?access not only to user data but a full table of encrypted passwords that they were able to decrypt using the same decryption key.ツ?ツ?ツ?
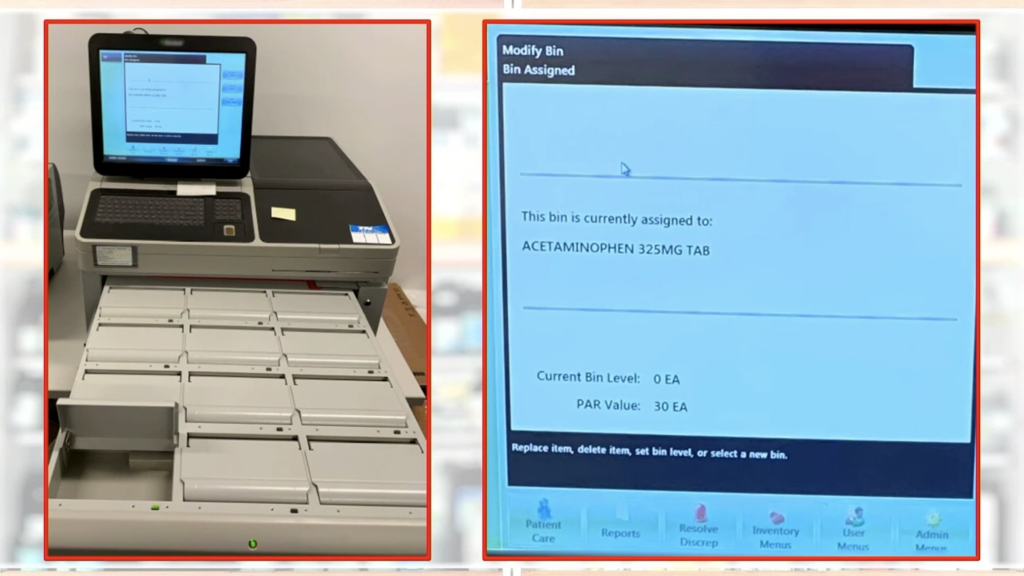
Fogie then looksツ?at the temperature monitoring system that is used to chill blood bags, insulin, and other drugs. Usingツ?WireShark, heツ?findsツ?a few authentication codes and passwords.ツ?(Around this point my head and keyboard startツ?to smoke as Fogie speedsツ?through his results faster than I canツ?screenshot.)
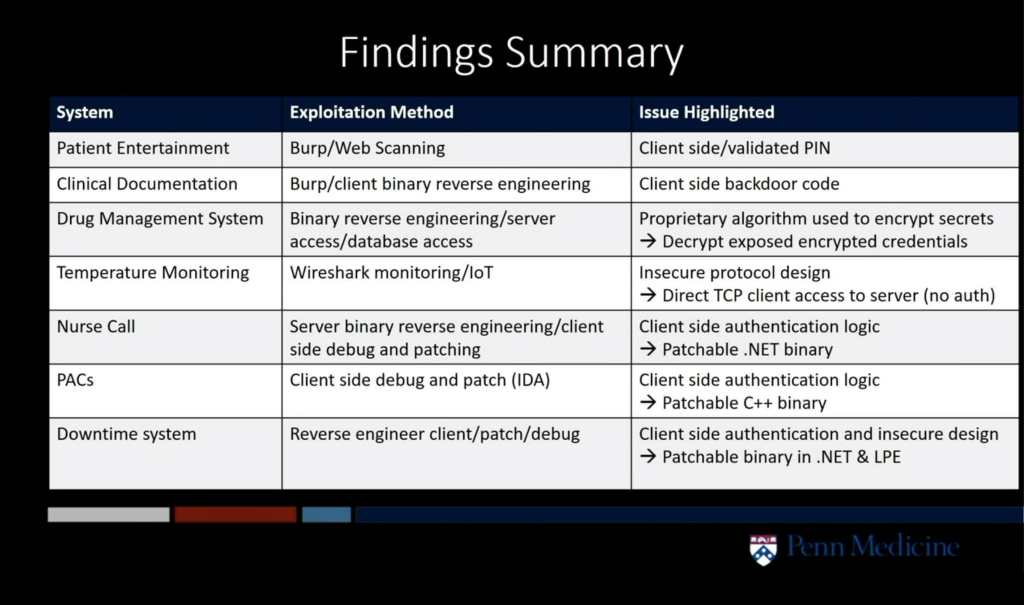
In the end, he compromisesツ?all seven systems, mostly through the use of clientツ?software. No vendors areツ?harmed in this presentation as Fogie blurred out all screens.ツ?He also worked with vendors to notify them of the security issues. Where software was no longer maintained, he patched the client software himself by setting a unique and complex password for a backdoor he found.ツ?ツ?
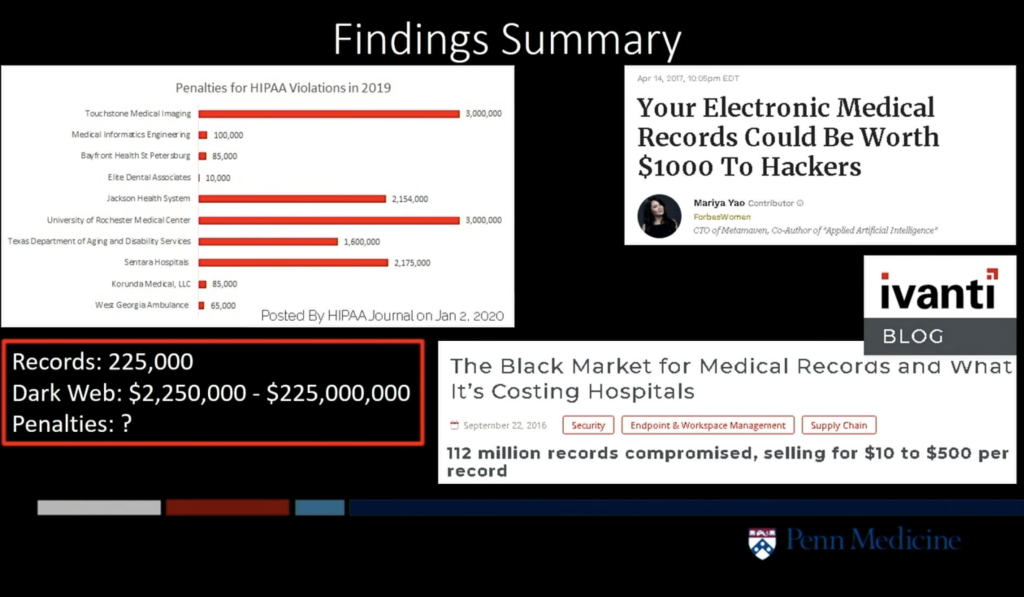
Managing 225,000 patient records, Black Hat Clinic could have been on the hook for millions of dollars in fines. Healthcare records are particularly popular on the dark web because they often contain a lot of information that helps fraudsters steal the identity of their victims andツ?use their credit.
Red flags to keep in mind:ツ?
- Default credentials
- Plaintext credentials
- Lack of hashed credentials in database
- Exposed ???secrets??? via client-side file review
- Client/server protocol design errors
- OWASP 101 including APIs
- Client-side binary review issues (e.g. ???backdoor???, decrypt, keys, etc.)
- Client-side authentication (e.g. debug/patchable authentication)
Don???t just try to get to DC,ツ?pentestツ?your apps.
Fogie???s advice is to not only conduct aツ?pentestツ?that is trying to get to the domain controller to take over the network but also to dig deep into the applications that hold your data. At Penn Med, they do a ???Lite???ツ?pentestツ?of all new products. For fellow practitioners in the healthcare space, he recommendsツ?participating in H-ISAC.ツ?ツ?
Plea to healthcare application vendors: ???Pleaseツ?don???t make our jobs harder.???ツ?
Fogie is asking healthcare application vendors toツ?run security testing onツ?their applicationsツ?prior to release. Of course, being an employee of application security testing vendor Veracode, I completely agree. At Veracode, we???re also seeing the market shift.ツ?Application vendors are telling us that their customers are putting more pressure on them to develop secure software than the regulators.ツ?ツ?
As an educated software buyer, ask your application vendor about their secure development practices.ツ?Rather than picking a vendor that has had a single point-in-time penetration test, look for vendors that follow a secure development process to ensure that they are continually trying to reduce risk and are more responsive to security issues.ツ?Some vendors may alsoツ?have theツ?Veracode Verifiedツ?seal, an attestation Veracode provides to organizations that follow specific security protocols in their application development.ツ?ツ?
If you don???t have the resources in house to run the type of tests that Fogie did in his presentation, please reach out to us to have a conversation. Our automated testing can beツ?plugged into anyツ?DevSecOpsツ?process, plus we help you with your program management to bring your stakeholders on board and advise your development team on how to fix flaws.ツ?We also do manual penetration tests if that???s what you need.ツ?ツ?
If you???d like to take your first step in your application security journey, we recommend you download our Ultimate Guide to Getting Started with Application Security. ツ?
ツ?
*** This is a Security Bloggers Network syndicated blog from Application Security Research, News, and Education Blog authored by [email protected] (ckirsch). Read the original post at: https://www.veracode.com/blog/intro-appsec/live-black-hat-healthscare-insiders-biopsy-healthcare-application-security-seth

