Document Analysis – 2018-newsletters.xls
Today I received what was clearly a malicious document in my email, so to celebrate the publishing of my second PluralSight course – Performing Malware Analysis on Malicious Documents – I thought I’d go through the analysis of the document.
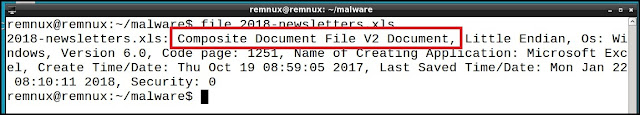
The document came in as an attachment in email and was named 2018-newsletters.xls.
MD5: 46fecfa6c32855c4fbf12d77b1dc761d
SHA1: c028bc46683617e7134aa9f3b7751117a38a177d
SHA256: 4e8449f84509f4d72b0b4baa4b8fd70571baaf9642f47523810ee933e972ebd9
You can download the file from here. The password is the last 8 characters of the filename, all lowercase.
To analyze it, I’m going to use REMNux, the malware analysis Linux distribution put together by Lenny Zeltser. This distro has all the tools we need to analyze the document.
The first thing I need to do is figure out what type of Office document we’re dealing with. By running the Linux file command on the document, it tells us we’re dealing with the composite file format, or structure storage format, of Office. Knowing this helps us figure out what tools we can use on the file.
Next, I want to see if there’s anything interesting inside of the document. There are lots of tools that can be used for this, but for now I’m just going to use Yara with the rules downloaded from the Yara Rules project.
Two yara rules get set off – Contains_VBA_macro_code and office_document_vba. Both rules indicate that the XLS contains VBA macro code. Macros are often used by attackers within documents to download additional malware or execute more code, such as PowerShell. If we didn’t think this spreadsheet was malicious before, this certainly raises our suspicions.
Next, I’ll try and extract the macro code. My favorite tool for doing this is olevba, which is part of the oletools by decalage. When I run it, I use the –deobf and –decode options to allow olevba to attempt to deobfuscate and decode any strings it can.
The resulting file is an excellent example of the obfuscation that attackers will go to in order to try and hide what they are doing from analysts. Lets look at a few of the functions and obfuscation performed.
 In the example to the right, the first function that is executed by the XLS is Workbook_Open(). This function calls the VBA Shell() function; Shell() is used to execute operating system commands. The parameters to the Shell() function are other functions, which lead to other functions, which lead to obfuscated strings.
In the example to the right, the first function that is executed by the XLS is Workbook_Open(). This function calls the VBA Shell() function; Shell() is used to execute operating system commands. The parameters to the Shell() function are other functions, which lead to other functions, which lead to obfuscated strings.
We can manually trace through the code to figure out what this is doing.
- The first parameter to Shell() is a function call to a function named tabretable().
- tabretable() calls 3 different functions, one of them being sunafeelo().
- sunafeelo() has 4 lines in it.
- The first line sets a variable to the string “external hard”.
- The second line sets a variable to the string “cM” using the Chr() function. Chr() returns the ASCII equivalent of the number given to it. This is a technique that is often used by attackers to obfuscate strings.
- The third line creates the string “D.ex” by combining Chr(), a period, and the results from the Left() function. In this case, the Left() function returns the first 2 letters from the left side of the string “external hard”, or “ex”.
- The last line combines all of these together, along with the results from the Right() function. Here, Right() returns the right-most two characters from the string “free “, which are “e ” (e plus a space).
The result from the first parameter to Shell() is “cMD.exe /c “, so we know its creating a command to execute on the system. I could go through all of the rest of the code to figure it out, but why should I if there are tools that will do it for me?
To do this, I’ll use Lazy Office Analyzer (LOA). LOA works by setting breakpoints on various APIs and recording their parameters. This allows us to watch when the malicious document writes files, connects to URLS, and most importantly, executes commands.
In the image above (click to enlarge), you can see how I ran LAO. In the end, the document executes obfuscated PowerShell that we could go in and deobfuscate some more. However, we see the URL hxxps://softarez[.]cf/mkeyb[.]gif in the code, which we can infer means that it will be downloading and executing whatever is returned.
This site was not up at the time I analyzed it, but fortunately it was analyzed by someone on hybrid-analysis, and shows that the downloaded files is a Windows executable, which VirusTotal indicates is a Zbot variant.
However, with regards to analyzing the malicious Excel file, we’re done. Since documents are typically used as the first stage of a malware compromise – in other words, they download or drop more malware to execute – we’ve figured out it does. The malicious document downloads an executable and runs it.
From here, we can start looking on our network for anyone accessing this site, as they will most likely have opened this document.
As I stated in the beginning of this post, my second PluralSight course was published and teaches how to analyze malicious documents. If you want to learn how to do everything I discussed here, plus a lot more, go check out the course. I welcome any feedback on it – good or bad – and any new courses you’d like to see from me.
IOCs
2018-newslettes.xls
MD5: 46fecfa6c32855c4fbf12d77b1dc761d
SHA1: c028bc46683617e7134aa9f3b7751117a38a177d
SHA256: 4e8449f84509f4d72b0b4baa4b8fd70571baaf9642f47523810ee933e972ebd9
URLs
- hxxps://softarez[.]cf/mkeyb[.]gi
*** This is a Security Bloggers Network syndicated blog from The Security Shoggoth authored by Tyler. Read the original post at: http://secshoggoth.blogspot.com/2018/01/document-analysis-2018-newslettersxls.html