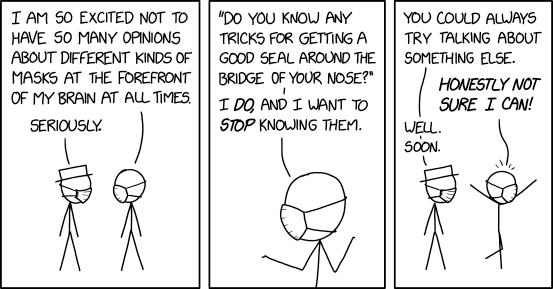
XKCD ‘Mask Opinions’
via the comic delivery system monikered Randall Munroe resident at XKCD!
*** This is a Security Bloggers Network syndicated blog from Infosecurity.US authored by Marc Handelman. Read the original post at: https://xkcd.com/2442/

