SCADA Security in a Cellular World
SCADA systems have been around since the early 1970s, way back when networks were all closed systems and hacking them was the stuff of spy movies. All this changed in the early 2000s when those networks became exposed to the internet. The increased connectivity allowed for higher productivity, access, and simplicity of use. However, with higher connectivity came new security concerns, as well as industry standards for protecting critical SCADA networks.
With the rise of cellular communication for industrial applications and Industry 4.0? It was only a matter of time before the adoption became global. High speeds, low costs, and a solution for SCADA networks that need to cover large distances all make cellular an ideal connectivity choice. However, increased wireless connectivity introduced additional attack vectors threatening the operation and safety of the devices connected.
Are those attack vectors enough to slow down the adoption of cellular connectivity for SCADA networks?
What are SCADA networks?
(Source)
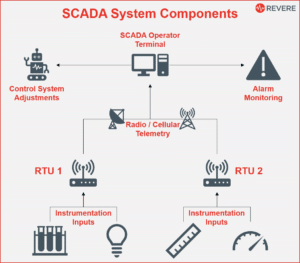
SCADA (Supervisory Control And Data Acquisition) is a general term for any system that can aggregate data from multiple industrial devices into a single location. Information from the SCADA network passes into a PLC (Programmable Logic Controller) or RTU (Remote Terminal Unit), which then provides information to an HMI (Human Machine Interface), where a human floor manager can interact with it.
SCADA interfaces can also allow for input, which means that the factory floor manager can not only get data but also make adjustments. In some cases, the SCADA system itself can make automated adjustments based on sensor data, saving many staff and managers’ work hours.
Wireless connectivity
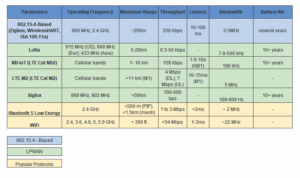
To this day UHF (Ultra High Frequency) Radio is the gold standard for safe and easy wireless connectivity. But it’s easy to see why it is being phased out as part of digital transformation of industrial networks. UHF is generally limited to a bandwidth of 19.6 kbps, which is more than enough to transfer commands to connected devices, but falls short when attempting to collect large amounts of DATA or even a single CCTV feed. Moreover, UHF radio is unreliable, relatively slow and prone to interference.
Alternatives to UHF radio for wireless connectivity for SCADA networks vary. A Wi-Fi router can replace UHF radio, but that won’t hold up along very large distances. Another older industrial connectivity solution are satellite connections. The problem with satellite connectivity is that it is very costly, and latency can become an issue with critical system controls.
Radio frequencies and Wi-Fi can suffice for some SCADA networks, especially when there is only a need for low-level diagnostics and basic commands. But when more data needs to be transferred, and scalability is a goal one solution stands tall above the rest — cellular connectivity.
(Source)
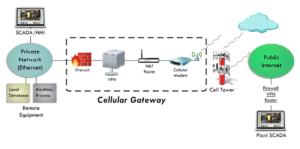
Private cellular networks in particular are a very affordable way to get long-distance connectivity as long as a cellular tower is in range. A public cellular network can offer a less reliable and secure option by connecting to the Internet, but offloads many related costs and maintenance concerns. In either case, you wouldn’t need much more than a cellular modem at every endpoint.
SCADA on IIoT
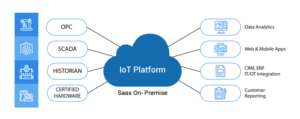
IIoT, the Industrial Internet of Things, is the collective name for devices connected to the Internet in industrial applications. Some devices have the built-in capability to connect to the Internet on their own through a built-in cellular modem component. Others use a local network as a gateway to the WAN (be it the Internet or an Intranet).
Generally speaking, anything that can connect to SCADA can connect to the Internet via a central computer. Connecting devices to the Internet allows managers to employ the power of cloud computing and big data processing to give a much deeper understanding of the systems connected.
(Source)
With the power of IIoT comes the vulnerability to external cyber-attacks. Where SCADA networks are a closed Intranet system by design, IIoT is exposed to the public Internet. Cybersecurity of devices connected to the Internet is a well-developed field, but SCADA brings its own set of vulnerabilities. That is, before we even mention the contribution of wireless connectivity to the overall attack surface of any industrial network.
What makes SCADA networks vulnerable?
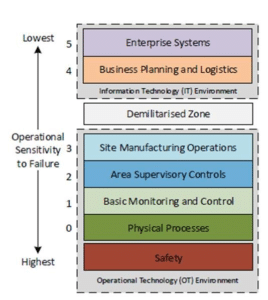
The devices connected to a SCADA network at the endpoints are all “dumb” devices. As such, they’re not afforded the protection of built-in firewalls or anti-malware software. Often a device connected to a SCADA network has nothing more than a control dial and an on/off switch. The vulnerability comes from the fact it is connected to a computer that can control it remotely. In this case, connectivity is vulnerability.
However, the more dangerous vulnerability of SCADA systems comes from the PLC, RTU, or HMI. Those devices that have oversight over the network must be secure. If not, malware that finds its way into the system can bring it down. A router suffering from a broadcast storm or even a latency in the system are all things that can cause major trouble.
(Source)
When it comes to cellular network connectivity, a slew of other vulnerabilities are introduced. A passive listener can pick up transmissions (and launch MiTM attacks), so the communication needs to be encrypted. Attacks can occur against devices through which communication is made, from the modem to the cellular towers.
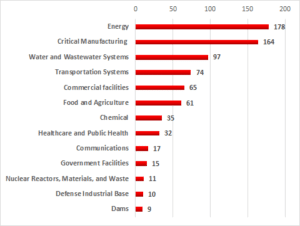
Why it’s critical to protect connected SCADA networks
SCADA networks are employed all over the world and not only in the private sector. As warfare and industrial sabotage move to the digital realm, so should protections. News headlines provide no shortage of examples.
One of the recently reported attacks on a public infrastructure SCADA network happened when allegedly Iranian hackers attacked Israeli water pumps. Authorities have not fully disclosed the scope of the attack or its effect, but it is believed that the attack was a malicious attempt to poison the water supply, and was enabled by bad password hygiene on endpoint devices.
This wasn’t the first time hackers affiliated with the Iranian state have dipped their toes the proverbial water. In 2013, a small utility called Bowman Dam in New York was under Iranian cyber attack. The SCADA network that controlled storm surges was connected to the Internet via a cellular modem. According to the US government, the only reason the hackers failed to do any damage was that they “did not have that capability because the sluice gate had been manually disconnected for maintenance at the time of the intrusion”.
Many companies in the private sector have also suffered attacks with high costs. In 2013, Target was under such an attack that aimed to steal credit card data. Following the resulting lawsuits, Target had to pay the 7 million affected customers a total of $309 million.
Perhaps one of the opening shots for international cyber-warfare was Stuxnet that has reportedly destroyed a fifth of Iran’s nuclear centrifuges that were used for nuclear fuel enrichment. Its malicious code has since been modified by others to attack similar SCADA networks.
(Source)
Even if it is unlikely your particular network will be under a direct attack, other malware can still affect it — especially if the network employs outdated or unpatched operating systems. Any OS-targeted malware can target these kinds of systems. Sometimes all it takes is one person plugging an infected USB key into the network to bring it down.
Achieving security at minimal latency
When people imagine security they often think of network attacks, but there are additional security concerns. SCADA networks must not only be encrypted, but they must also provide a reliable and continuous service. If all best practice protocols for security are to be implemented, then a UHF network would fail due to overload and latency.
(Source)
Cellular connectivity is found to be more secure than all radio frequencies, providing the necessary broadband to encrypt data and providing a reliable continuous connection with low latency.
According to research published by the International Society of Automation, the internal security protocols and standard security protocols (such as VPN, IPSec, and GRE) cause a traffic reduction of about 30%. Cellular networks can maintain broadband capabilities even with those security protocols in place.
Conclusion
The future of any SCADA network beyond the small factory floor is cellular connectivity. It is affordable, scalable, and potentially secure, which makes it the obvious choice going forward. While there are definitely valid concerns regarding SCADA networks’ vulnerability, many of them have already been solved by proper security protocols and industry standards.
Cellular connectivity might introduce additional attack vectors onto your system, but capable security options are out there for those that put in the effort. At the end of the day, cellular connectivity for industrial control systems is the most cost-effective path to secure digital transformation.
SCADA networks + Cellular = Unique attack surfaces.
The FirstPoint team is here to help analyze your cellular threat landscape.
The post SCADA Security </br> in a Cellular World appeared first on FirstPoint.
*** This is a Security Bloggers Network syndicated blog from Blog – FirstPoint authored by Noa Ouziel. Read the original post at: https://www.firstpoint-mg.com/blog/scada-security-in-a-cellular-world/