Home » Cybersecurity » Threats & Breaches » Vulnerabilities » Sonatype Spots 150+ Malicious npm Packages Copying Recent Software Supply Chain Attacks that Hit 35 Organizations
Sonatype Spots 150+ Malicious npm Packages Copying Recent Software Supply Chain Attacks that Hit 35 Organizations
Just three days ago on February 9th, Sonatype released our findings on Alex Birsan’s research in which he used the “dependency or namespace confusion” technique to push his malicious proof-of-concept (PoC) code to internal development builds of over 35 major tech organizations including Microsoft, Apple, Tesla, Uber and others.
For his ethical research efforts, the researcher also made over $130,000 in bug bounties.
With the news making headlines, it didn’t take long for other researchers to start imitating Birsan’s open source software supply chain attack research.
Within 48 hours of the news reports, Sonatype’s automated malware detection systems, part of Nexus Intelligence, began flagging over 150 copycat npm packages published by different authors that imitate Alex Birsan’s proof-of-concept (PoC) research. We are actively seeing more of these packages coming in every few hours.
Sonatype has exclusively spotted these npm packages from multiple, pseudonymous authors claiming these are for “security research purposes only,” in the style of Birsan.
But, it is important to note, any adversary could be publishing outright nefarious packages to public open source repositories and disguising them as having been published for “research purposes.”
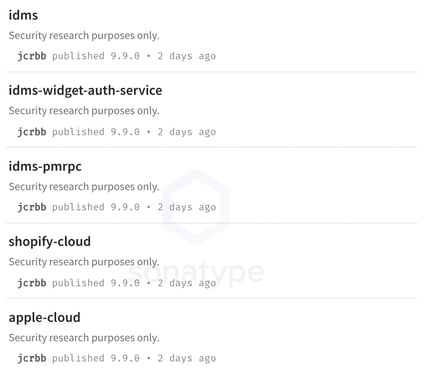
Image: new npm copycat packages have emerged imitating Birsan’s research
Not only do most of these packages contain identical code that makes callbacks to the researcher’s server over DNS, they have the exact same structure, version numbering, code comments and “research purposes only” disclaimers.
Another noteworthy observation is that some of these npm packages are named after the RubyGems packages that Birsan had published in his PoC attack. For example, the “shopify-cloud” npm package by this new author copies the “shopify-cloud” gem that had earned the researcher a $30,000 bug bounty.
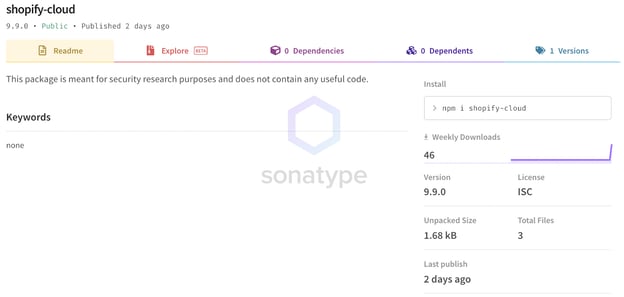
Image: A “shopify-cloud” npm component published by a different author imitates Birsan’s (Read more...)
*** This is a Security Bloggers Network syndicated blog from Sonatype Blog authored by Ax Sharma. Read the original post at: https://blog.sonatype.com/sonatype-spots-150-malicious-npm-packages-copying-recent-software-supply-chain-attacks





