OWASP API Security Top 10: A Framework for Improving Your API Security Efforts
During a recent API Security conversation with a customer, I asked if they had seen the OWASP API Security Top 10 list. They had not heard about it yet, a response that is consistent with other customers as well as from industry analysts including Gartner, Forrester and the Aite Group. Like the preceding Web App Security Top 10 list, the OWASP API Security Top 10 is a great addition to your API programs and initiatives, acting as a set of guidelines for both security and development teams alike.
APIs have long been the vehicle of choice for automated bots – it’s far easier to target the API for a shopping cart, a login or registration endpoint than it is to script a web form fill. However, a long list of API security incidents in 2020 shows that APIs are increasingly targeted for data theft due to security gaps like weak authentication or verbose error messages. Clearly, the explosive use of APIs has exposed security gaps within both the development and security teams, as highlighted in our API Security Risks webinar with the Aite Group.
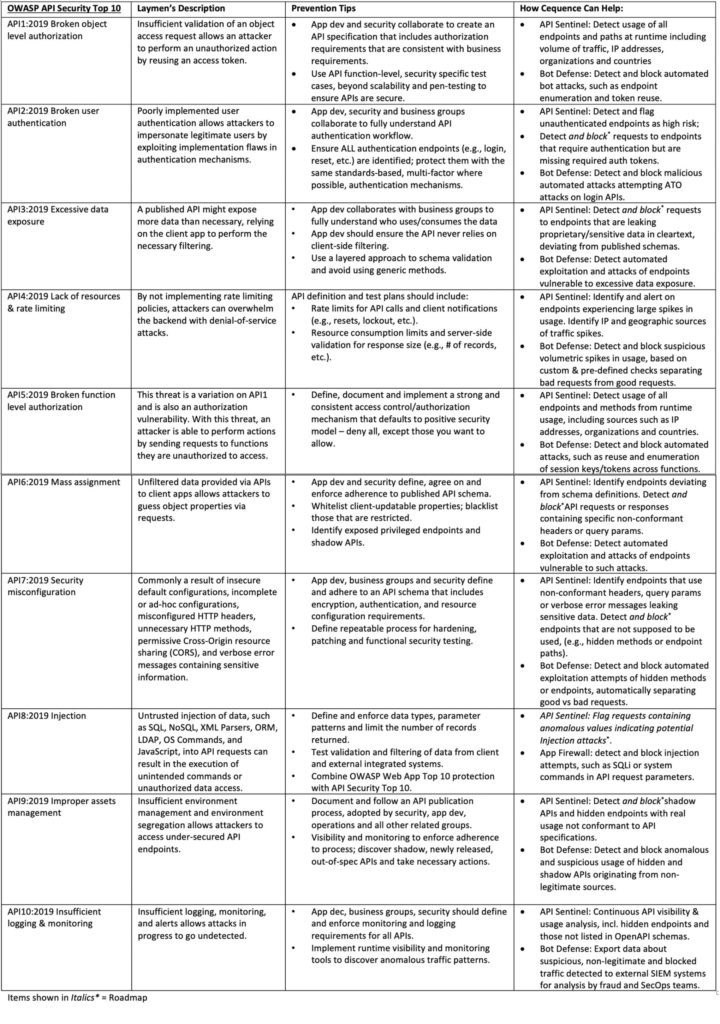
Improving your API security posture is best done using a combination of documented best practices and technology to monitor and enforce policies. To that end, we recently held an educational webinar, Demystifying the OWASP API Security Top 10, where we took a threat actor (Jason Kent, our Hacker in Residence) vs. protector (Subbu Iyer, VP of Products) approach of defining each of the attacks on the list, discussing the ways threat actors will use the security weakness, prevention tips, and how the Cequence Application Security Platform can augment your API coding best practices. You can see the webinar here, and a summary is shown in the table below.
The post OWASP API Security Top 10: A Framework for Improving Your API Security Efforts appeared first on Cequence.
*** This is a Security Bloggers Network syndicated blog from Cequence authored by Matt Keil. Read the original post at: https://www.cequence.ai/blog/owasp-api-security-top-10-a-framework-for-improving-your-api-security-efforts/





